 10001100001011100000111001001101001011011100100110100101 1101000111100100100000011001000110000101110000011100100110100 101101110010011010010111010001111001001000000110010001100001011101000110 000101110000011100100110100101101110010011010010111010001111001001000000 11001000110000101110000011100100110100101101110010011010 0101110100011110010010000001100100011000010111000001110010011 010010110111001001101001011101000111100100100000011001000110000101110100 011000010111000001110010011010010110111001001101001011101000111100100100 00001100100011000010111000001110010011010010110111001001 1010010111010001111001001000000110010001100001011100000111001 00110100101101110010011010010111010001111001001000000110010001100001011100000111001001101001011011100100110100101110100011110010 01000000110010001100001011100000111001001101001011011100 1001101001011101000111100100100000011001000110000101110000011 100100110100101101110010011010010111010001111001001000000110010001100001 011101000110000101110000011100100110100101101110010011010010111010001111 0010010000001100100011000010111000001110010011010010110111101 1100100110100101110100011110010010000001100100011000010111000 By 001110010011010010110111001001101001011101000111100100100000011001000110 000101110100011000010111000001110010011010010110111001001101001011101000 1111001001000000110010001100001011100000111001001101001011011100100110100101110100011110010010000001100100011000010111010001100001011 100000111001001101001011011100100110100101110100011110010010000001100100 011000010111010001100001011100000111001001101001011011100100110100101110 1000111100100100000011001000110000101110000011100100110100101 Cyber Security Top Threats and What You Can Do About Them
10001100001011100000111001001101001011011100100110100101 1101000111100100100000011001000110000101110000011100100110100 101101110010011010010111010001111001001000000110010001100001011101000110 000101110000011100100110100101101110010011010010111010001111001001000000 11001000110000101110000011100100110100101101110010011010 0101110100011110010010000001100100011000010111000001110010011 010010110111001001101001011101000111100100100000011001000110000101110100 011000010111000001110010011010010110111001001101001011101000111100100100 00001100100011000010111000001110010011010010110111001001 1010010111010001111001001000000110010001100001011100000111001 00110100101101110010011010010111010001111001001000000110010001100001011100000111001001101001011011100100110100101110100011110010 01000000110010001100001011100000111001001101001011011100 1001101001011101000111100100100000011001000110000101110000011 100100110100101101110010011010010111010001111001001000000110010001100001 011101000110000101110000011100100110100101101110010011010010111010001111 0010010000001100100011000010111000001110010011010010110111101 1100100110100101110100011110010010000001100100011000010111000 By 001110010011010010110111001001101001011101000111100100100000011001000110 000101110100011000010111000001110010011010010110111001001101001011101000 1111001001000000110010001100001011100000111001001101001011011100100110100101110100011110010010000001100100011000010111010001100001011 100000111001001101001011011100100110100101110100011110010010000001100100 011000010111010001100001011100000111001001101001011011100100110100101110 1000111100100100000011001000110000101110000011100100110100101 Cyber Security Top Threats and What You Can Do About Them
 Hackers
Hackers
 Cyber Warfare
Cyber Warfare
 Dictators
Dictators
 Your Employees
Your Employees
 The Bad News • For Cyber Criminals size doesn’t matter – Successful attacks on small-midsize businesses grew by 64% in 2014 – Smaller companies are low hanging fruit
The Bad News • For Cyber Criminals size doesn’t matter – Successful attacks on small-midsize businesses grew by 64% in 2014 – Smaller companies are low hanging fruit
 More Bad News – Automated attacks mean criminals can hit thousands of businesses
More Bad News – Automated attacks mean criminals can hit thousands of businesses
 The Really Bad News 60 % of small businesses that suffer an attack shut down after 6 months
The Really Bad News 60 % of small businesses that suffer an attack shut down after 6 months
 Small Business Security Threats • Social Engineering – Phishing • Malware – – Viruses Worms Trojan horses Ransomware
Small Business Security Threats • Social Engineering – Phishing • Malware – – Viruses Worms Trojan horses Ransomware
 Social Engineering • Psychological manipulation of people into performing actions or divulging confidential information.
Social Engineering • Psychological manipulation of people into performing actions or divulging confidential information.
 Phishing • The attempt to acquire sensitive information such as usernames, passwords, and credit card details (and sometimes, indirectly, money), often for malicious reasons, by masquerading as a trustworthy entity in an electronic communication.
Phishing • The attempt to acquire sensitive information such as usernames, passwords, and credit card details (and sometimes, indirectly, money), often for malicious reasons, by masquerading as a trustworthy entity in an electronic communication.
 Phishing Example A (Hello Dearest) • • • • Hello Dearest, Compliments of the day. I came across your contact address while searching for someone to help me, I lost my parents and want you to stand as my foreign trustee to retrive and invest USD$6. 5 Million which I inherited from my late parent. I tried to get this money out from the bank , but the management refused because of my age. I am ready to give you 25% of the whole money at the completion of the transaction, write me back for more details. Regards, Miss. Mary Anderson
Phishing Example A (Hello Dearest) • • • • Hello Dearest, Compliments of the day. I came across your contact address while searching for someone to help me, I lost my parents and want you to stand as my foreign trustee to retrive and invest USD$6. 5 Million which I inherited from my late parent. I tried to get this money out from the bank , but the management refused because of my age. I am ready to give you 25% of the whole money at the completion of the transaction, write me back for more details. Regards, Miss. Mary Anderson
 Phishing Example B (Mr. Leon) • 1, 500, 000 USD A Personal Donation to you from Mr. Leon hirtle, Contact Mr. Leon hirtle • On: mrleonhirtle 2@gmail. com. for more details. • Greetings!!! I'm Mr Juan Colombás from Lloyds banking Group United Kingdom. I saw your profile and I want to have a Joint Venture with you. You can view my website and contact me for more details http: //www. lloydsbankinggroup. com/about_us /directors/board_directors. asp Mr. Juan Colombás. Email: lloydsbanksb@yahoo. co. uk Mobile: +447872219425 www. lloydsbankinggroup. com
Phishing Example B (Mr. Leon) • 1, 500, 000 USD A Personal Donation to you from Mr. Leon hirtle, Contact Mr. Leon hirtle • On: mrleonhirtle 2@gmail. com. for more details. • Greetings!!! I'm Mr Juan Colombás from Lloyds banking Group United Kingdom. I saw your profile and I want to have a Joint Venture with you. You can view my website and contact me for more details http: //www. lloydsbankinggroup. com/about_us /directors/board_directors. asp Mr. Juan Colombás. Email: lloydsbanksb@yahoo. co. uk Mobile: +447872219425 www. lloydsbankinggroup. com
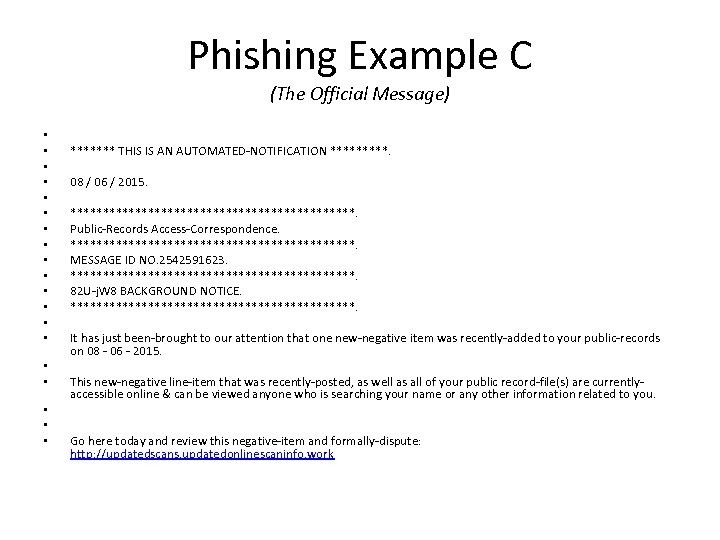 Phishing Example C (The Official Message) • • • • • ******* THIS IS AN AUTOMATED-NOTIFICATION *****. 08 / 06 / 2015. **********************. Public-Records Access-Correspondence. **********************. MESSAGE ID NO. 2542591623. **********************. 82 U-j. W 8 BACKGROUND NOTICE. **********************. It has just been-brought to our attention that one new-negative item was recently-added to your public-records on 08 - 06 - 2015. This new-negative line-item that was recently-posted, as well as all of your public record-file(s) are currentlyaccessible online & can be viewed anyone who is searching your name or any other information related to you. Go here today and review this negative-item and formally-dispute: http: //updatedscans. updatedonlinescaninfo. work
Phishing Example C (The Official Message) • • • • • ******* THIS IS AN AUTOMATED-NOTIFICATION *****. 08 / 06 / 2015. **********************. Public-Records Access-Correspondence. **********************. MESSAGE ID NO. 2542591623. **********************. 82 U-j. W 8 BACKGROUND NOTICE. **********************. It has just been-brought to our attention that one new-negative item was recently-added to your public-records on 08 - 06 - 2015. This new-negative line-item that was recently-posted, as well as all of your public record-file(s) are currentlyaccessible online & can be viewed anyone who is searching your name or any other information related to you. Go here today and review this negative-item and formally-dispute: http: //updatedscans. updatedonlinescaninfo. work
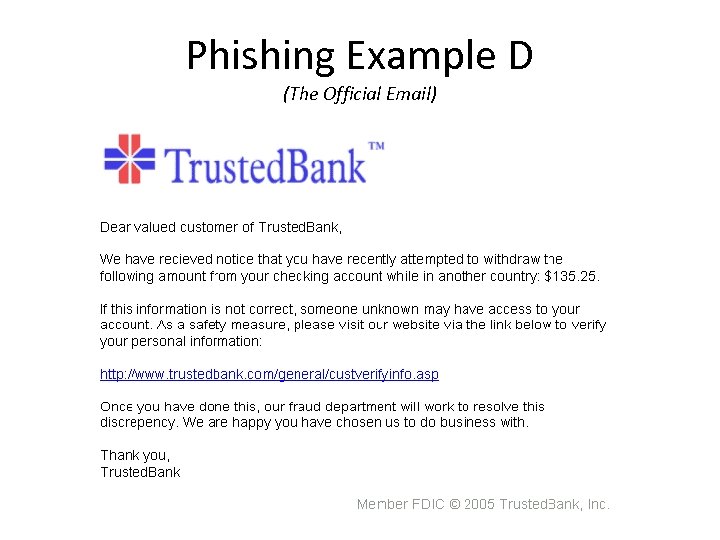 Phishing Example D (The Official Email)
Phishing Example D (The Official Email)
 Malware • Malware= short for malicious software, is any software used to disrupt computer operation, gather sensitive information, or gain access to private computer systems.
Malware • Malware= short for malicious software, is any software used to disrupt computer operation, gather sensitive information, or gain access to private computer systems.
 Ransomware • A type of malware that restricts access to a computer system that it infects in some way, and demands that the user pay a ransom to the operators of the malware to remove the restriction.
Ransomware • A type of malware that restricts access to a computer system that it infects in some way, and demands that the user pay a ransom to the operators of the malware to remove the restriction.
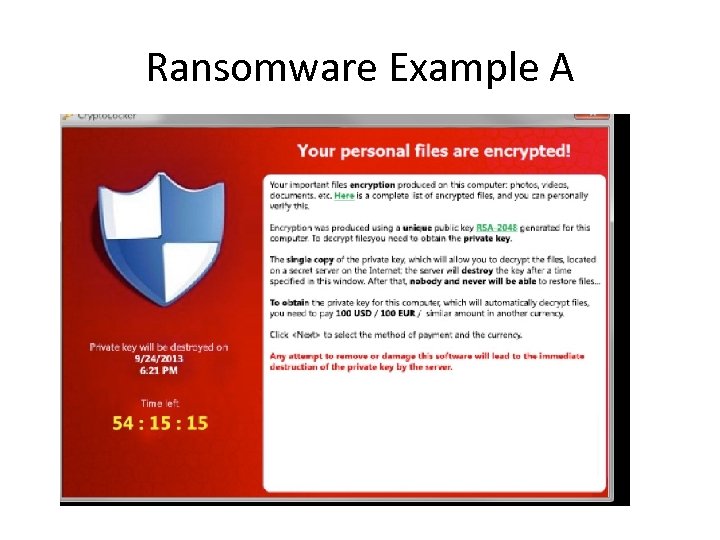 Ransomware Example A
Ransomware Example A
 Things To Consider • Fake Wireless Access Points • Browser cookies that save passwords • Malicious Apps
Things To Consider • Fake Wireless Access Points • Browser cookies that save passwords • Malicious Apps
 The Good News! You don’t need to be an expert to protect yourself like an expert
The Good News! You don’t need to be an expert to protect yourself like an expert
 More Good News • Cyber Security experts What are the 3 most important things you do to protect your security online?
More Good News • Cyber Security experts What are the 3 most important things you do to protect your security online?
 The Top 5 Responses • • • Installing software updates Using unique passwords Using strong passwords Using two factor authentication Using a password manager
The Top 5 Responses • • • Installing software updates Using unique passwords Using strong passwords Using two factor authentication Using a password manager
 Anti-Phishing Tips • Beware of emails that try to get you to click a link in order to change your account information. • Do not follow any links via email to change your sensitive information. • Only visit sites from known sources and always confirm suspicious information via telephone.
Anti-Phishing Tips • Beware of emails that try to get you to click a link in order to change your account information. • Do not follow any links via email to change your sensitive information. • Only visit sites from known sources and always confirm suspicious information via telephone.
 Anti-Phishing Tips • Always use updated anti-virus software with a special antiphishing filter. • Always be very skeptical about sending any of your personal or sensitive information over the Internet. • Keep informed about Phishing techniques (phishme. com) • Keep link clicking to a minimum • Keep your browser up to date
Anti-Phishing Tips • Always use updated anti-virus software with a special antiphishing filter. • Always be very skeptical about sending any of your personal or sensitive information over the Internet. • Keep informed about Phishing techniques (phishme. com) • Keep link clicking to a minimum • Keep your browser up to date
 Anti-Phishing Tips • Everyone has their own passwords! • Change passwords every 3 months • Backup your data
Anti-Phishing Tips • Everyone has their own passwords! • Change passwords every 3 months • Backup your data
 The Good News • Employee Education • Have a Cyber Security office policy • https: //www. fcc. gov/cyberforsmallbiz
The Good News • Employee Education • Have a Cyber Security office policy • https: //www. fcc. gov/cyberforsmallbiz
 The Future • No more passwords
The Future • No more passwords
 Moving to the Cloud
Moving to the Cloud
 The Future • Moving to the Cloud – A worldwide growth rate of 36% – Market size = $19. 6 billion by 2016
The Future • Moving to the Cloud – A worldwide growth rate of 36% – Market size = $19. 6 billion by 2016
 Security in the Cloud • Transfer the worry to your vendor • Technicians whose only job is data security • Multiple technicians employing the latest technology watching your data • Your data is backed up for you • Built in Disaster Recovery
Security in the Cloud • Transfer the worry to your vendor • Technicians whose only job is data security • Multiple technicians employing the latest technology watching your data • Your data is backed up for you • Built in Disaster Recovery
 • “Security is actually increased when using cloud solutions due to strict ISO security standards that cloud providers must adhere to, in addition to the regular security audits. ”
• “Security is actually increased when using cloud solutions due to strict ISO security standards that cloud providers must adhere to, in addition to the regular security audits. ”
 10001100001011100000111001001101001011011100100110100101 1101000111100100100000011001000110000101110000011100100110100 101101110010011010010111010001111001001000000110010001100001011101000110 000101110000011100100110100101101110010011010010111010001111001001000000 11001000110000101110000011100100110100101101110010011010 0101110100011110010010000001100100011000010111000001110010011 010010110111001001101001011101000111100100100000011001000110000101110100 011000010111000001110010011010010110111001001101001011101000111100100100 00001100100011000010111000001110010011010010110111001001 1010010111010001111001001000000110010001100001011100000111001 00110100101101110010011010010111010001111001001000000110010001100001011100000111001001101001011011100100110100101110100011110010 01000000110010001100001011100000111001001101001011011100 1001101001011101000111100100100000011001000110000101110000011 100100110100101101110010011010010111010001111001001000000110010001100001 011101000110000101110000011100100110100101101110010011010010111010001111 0010010000001100100011000010111000001110010011010010110111101 1100100110100101110100011110010010000001100100011000010111000 001110010011010010110111001001101001011101000111100100100000011001000110 000101110100011000010111000001110010011010010110111001001101001011101000 1111001001000000110010001100001011100000111001001101001011011100100110100101110100011110010010000001100100011000010111010001100001011 100000111001001101001011011100100110100101110100011110010010000001100100 011000010111010001100001011100000111001001101001011011100100110100101110 1000111100100100000011001000110000101110000011100100110100101 Thank You
10001100001011100000111001001101001011011100100110100101 1101000111100100100000011001000110000101110000011100100110100 101101110010011010010111010001111001001000000110010001100001011101000110 000101110000011100100110100101101110010011010010111010001111001001000000 11001000110000101110000011100100110100101101110010011010 0101110100011110010010000001100100011000010111000001110010011 010010110111001001101001011101000111100100100000011001000110000101110100 011000010111000001110010011010010110111001001101001011101000111100100100 00001100100011000010111000001110010011010010110111001001 1010010111010001111001001000000110010001100001011100000111001 00110100101101110010011010010111010001111001001000000110010001100001011100000111001001101001011011100100110100101110100011110010 01000000110010001100001011100000111001001101001011011100 1001101001011101000111100100100000011001000110000101110000011 100100110100101101110010011010010111010001111001001000000110010001100001 011101000110000101110000011100100110100101101110010011010010111010001111 0010010000001100100011000010111000001110010011010010110111101 1100100110100101110100011110010010000001100100011000010111000 001110010011010010110111001001101001011101000111100100100000011001000110 000101110100011000010111000001110010011010010110111001001101001011101000 1111001001000000110010001100001011100000111001001101001011011100100110100101110100011110010010000001100100011000010111010001100001011 100000111001001101001011011100100110100101110100011110010010000001100100 011000010111010001100001011100000111001001101001011011100100110100101110 1000111100100100000011001000110000101110000011100100110100101 Thank You


