7df58a3cf633969cce3d928bfa883eee.ppt
- Количество слайдов: 153

通信与网络安全基础

议题 1. OSI模型和TCP/IP协议簇 2. 通信和网络技术 3. 互联网技术与服务 4. 主要网络安全协议和机制

一、OSI模型和TCP/IP协议簇
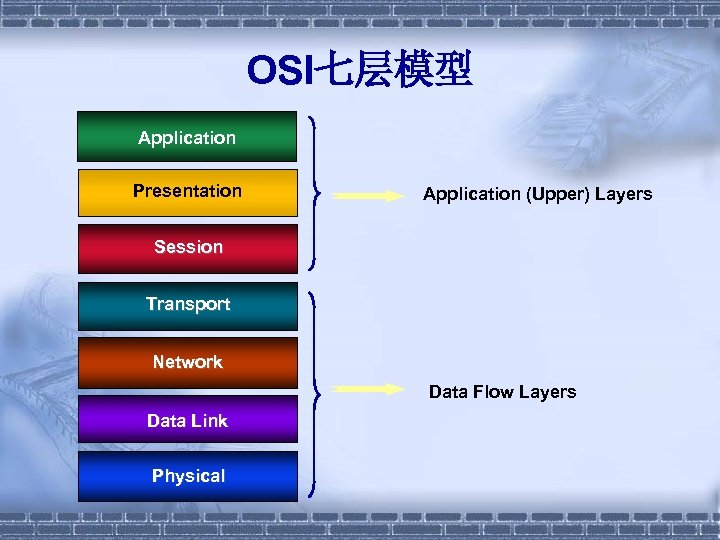
OSI七层模型 Application Presentation Application (Upper) Layers Session Transport Network Data Flow Layers Data Link Physical
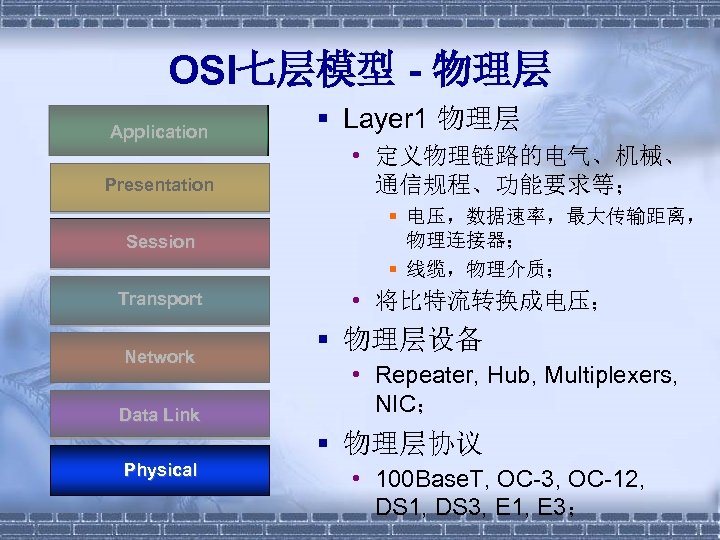
OSI七层模型 - 物理层 Application Presentation Session Transport Network Data Link § Layer 1 物理层 • 定义物理链路的电气、机械、 通信规程、功能要求等; § 电压,数据速率,最大传输距离, 物理连接器; § 线缆,物理介质; • 将比特流转换成电压; § 物理层设备 • Repeater, Hub, Multiplexers, NIC; § 物理层协议 Physical • 100 Base. T, OC-3, OC-12, DS 1, DS 3, E 1, E 3;
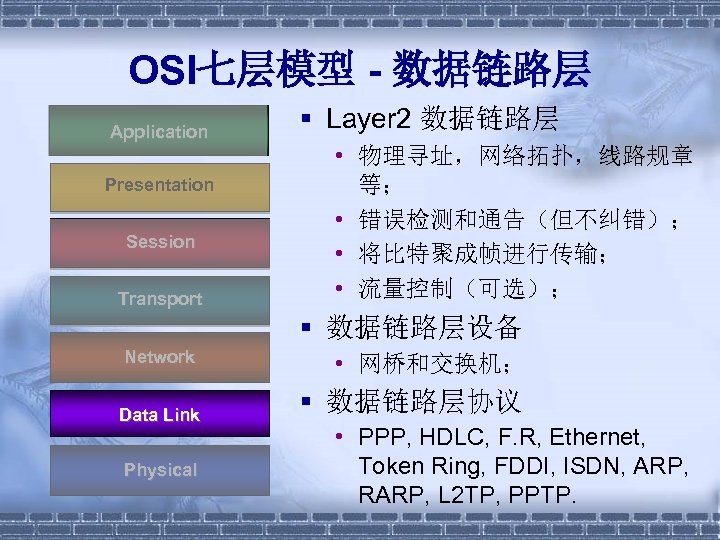
OSI七层模型 - 数据链路层 Application Presentation Session Transport § Layer 2 数据链路层 • 物理寻址,网络拓扑,线路规章 等; • 错误检测和通告(但不纠错); • 将比特聚成帧进行传输; • 流量控制(可选); § 数据链路层设备 Network Data Link Physical • 网桥和交换机; § 数据链路层协议 • PPP, HDLC, F. R, Ethernet, Token Ring, FDDI, ISDN, ARP, RARP, L 2 TP, PPTP.
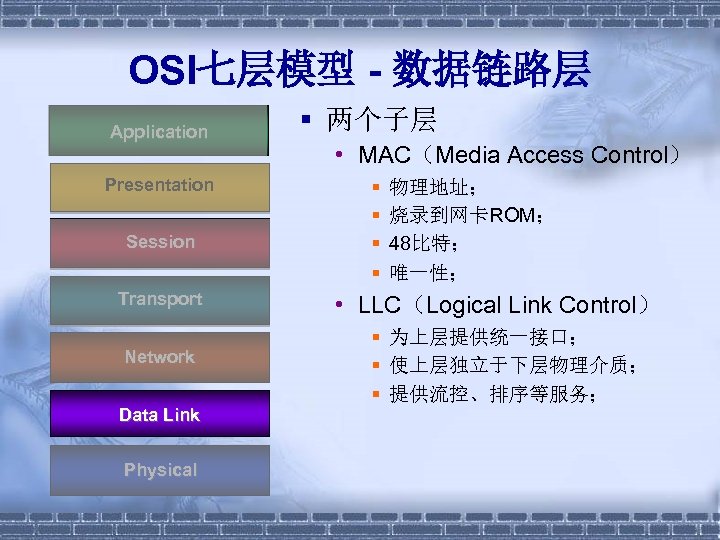
OSI七层模型 - 数据链路层 Application Presentation Session Transport Network Data Link Physical § 两个子层 • MAC(Media Access Control) § § 物理地址; 烧录到网卡ROM; 48比特; 唯一性; • LLC(Logical Link Control) § 为上层提供统一接口; § 使上层独立于下层物理介质; § 提供流控、排序等服务;
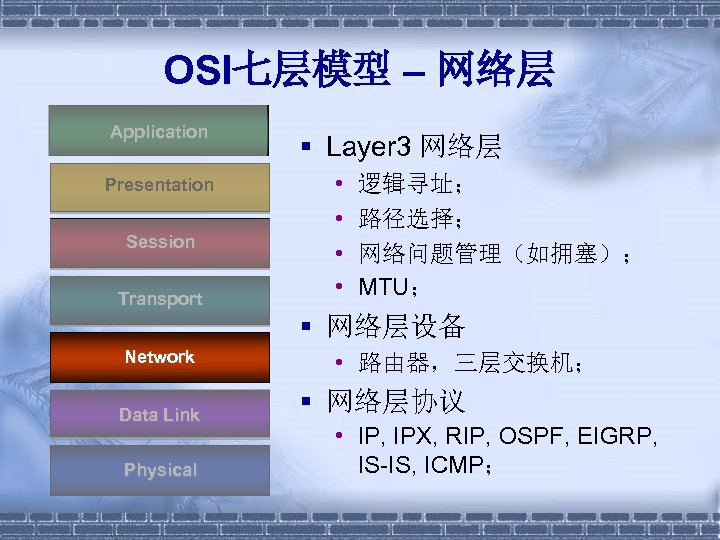
OSI七层模型 – 网络层 Application Presentation Session Transport § Layer 3 网络层 • • 逻辑寻址; 路径选择; 网络问题管理(如拥塞); MTU; § 网络层设备 Network Data Link Physical • 路由器,三层交换机; § 网络层协议 • IP, IPX, RIP, OSPF, EIGRP, IS-IS, ICMP;
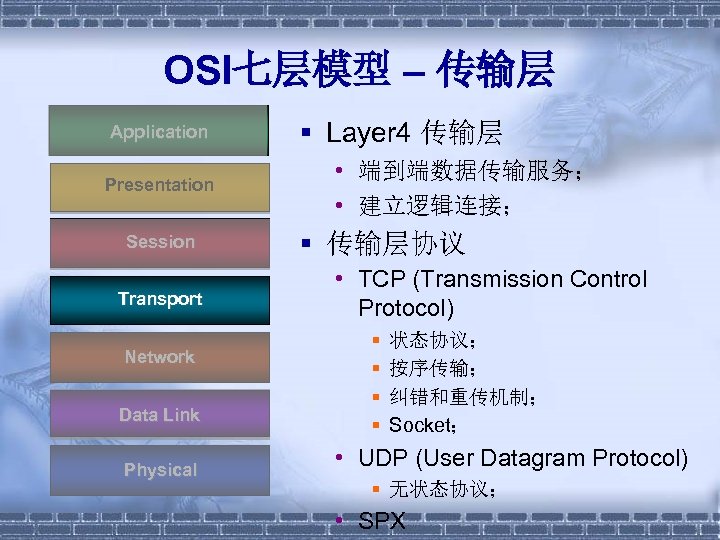
OSI七层模型 – 传输层 Application Presentation Session Transport Network Data Link Physical § Layer 4 传输层 • 端到端数据传输服务; • 建立逻辑连接; § 传输层协议 • TCP (Transmission Control Protocol) § § 状态协议; 按序传输; 纠错和重传机制; Socket; • UDP (User Datagram Protocol) § 无状态协议; • SPX
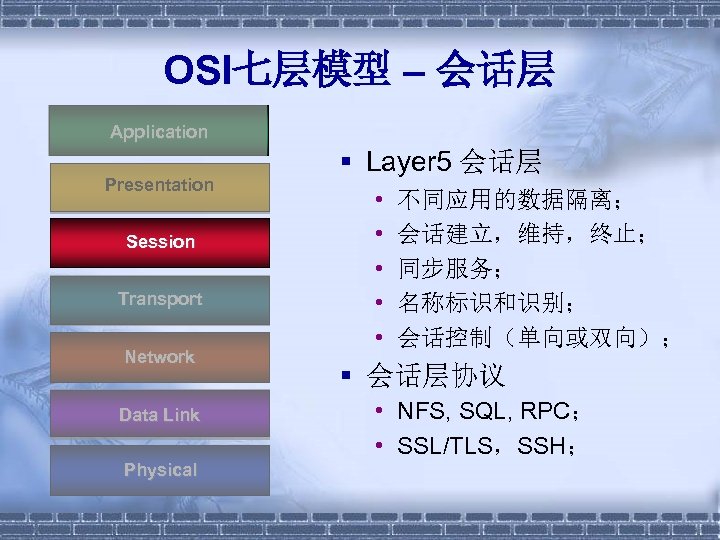
OSI七层模型 – 会话层 Application Presentation Session Transport Network Data Link Physical § Layer 5 会话层 • • • 不同应用的数据隔离; 会话建立,维持,终止; 同步服务; 名称标识和识别; 会话控制(单向或双向); § 会话层协议 • NFS, SQL, RPC; • SSL/TLS,SSH;
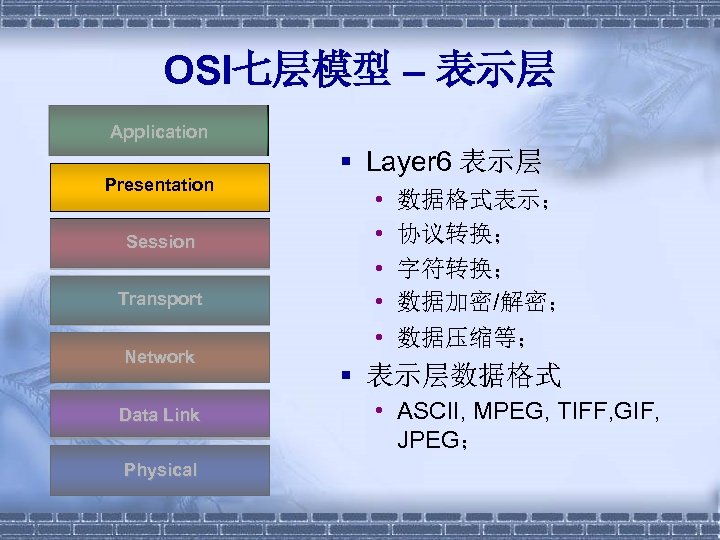
OSI七层模型 – 表示层 Application Presentation Session Transport Network Data Link Physical § Layer 6 表示层 • • • 数据格式表示; 协议转换; 字符转换; 数据加密/解密; 数据压缩等; § 表示层数据格式 • ASCII, MPEG, TIFF, GIF, JPEG;
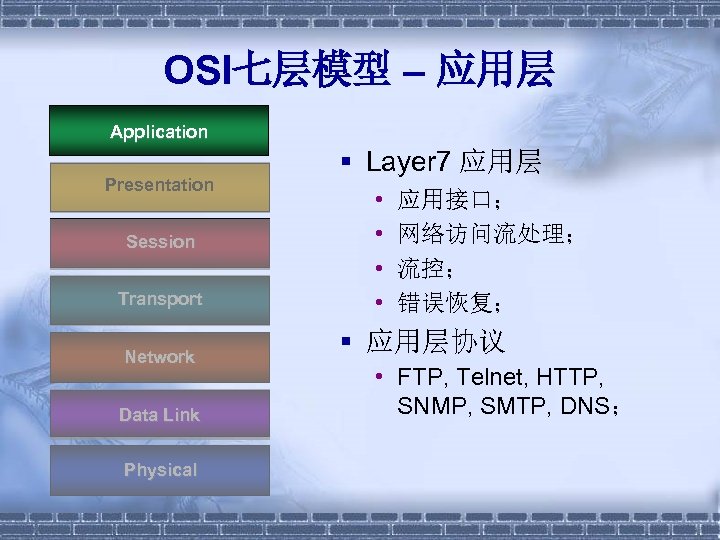
OSI七层模型 – 应用层 Application Presentation Session Transport Network Data Link Physical § Layer 7 应用层 • • 应用接口; 网络访问流处理; 流控; 错误恢复; § 应用层协议 • FTP, Telnet, HTTP, SNMP, SMTP, DNS;
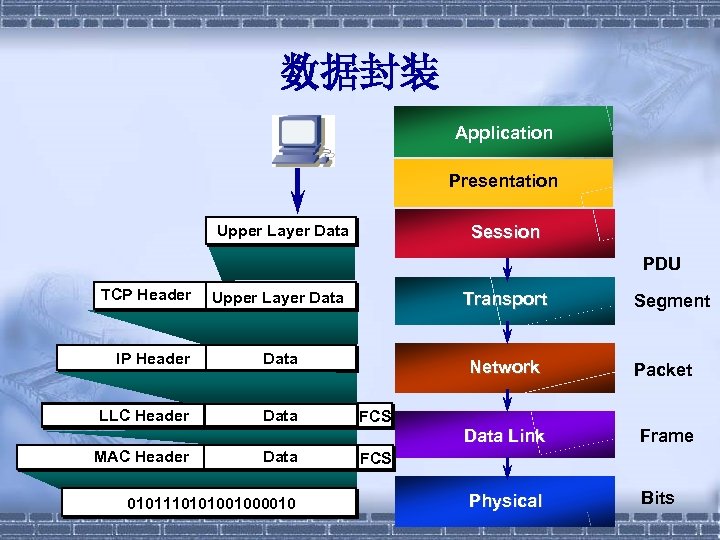
数据封装 Application Presentation Upper Layer Data Session PDU TCP Header Upper Layer Data Transport IP Header Data Network Packet LLC Header Data Link Frame Physical Bits MAC Header Data 0101110101001000010 Segment FCS
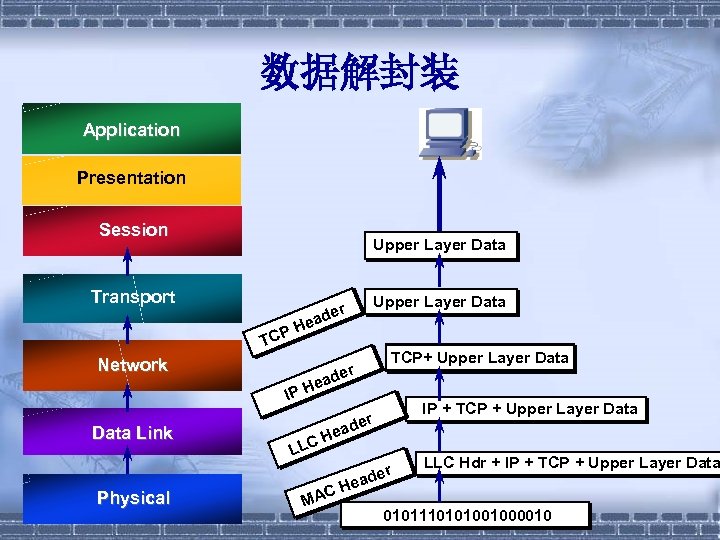
数据解封装 Application Presentation Session Upper Layer Data Transport TCP Network Physical der TCP+ Upper Layer Data ea IP H Data Link Upper Layer Data r ade He IP + TCP + Upper Layer Data der Hea C LL C MA er ead H LLC Hdr + IP + TCP + Upper Layer Data 0101110101001000010
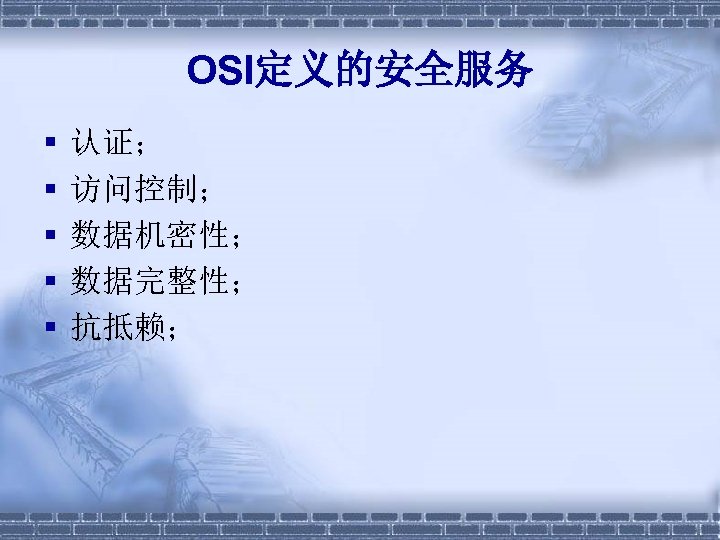
OSI定义的安全服务 § § § 认证; 访问控制; 数据机密性; 数据完整性; 抗抵赖;
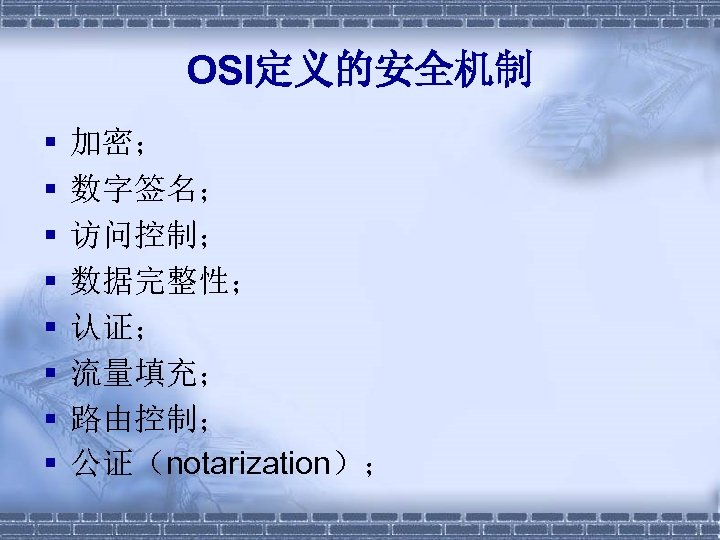
OSI定义的安全机制 § § § § 加密; 数字签名; 访问控制; 数据完整性; 认证; 流量填充; 路由控制; 公证(notarization);
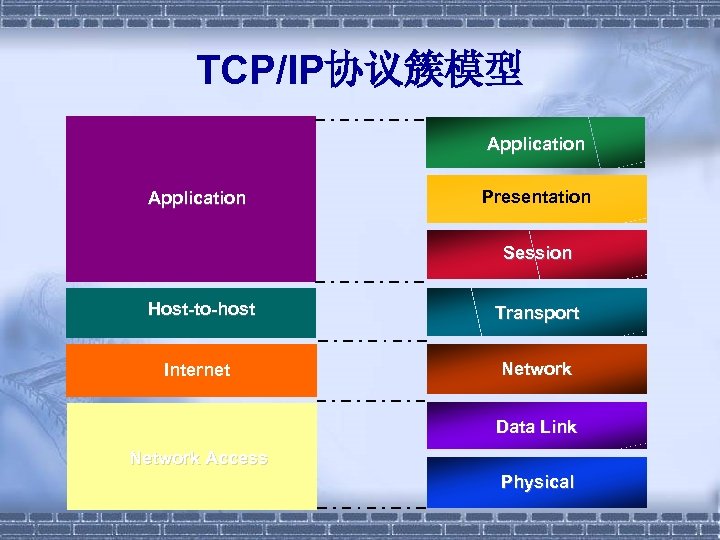
TCP/IP协议簇模型 Application Presentation Session Host-to-host Transport Internet Network Data Link Network Access Physical
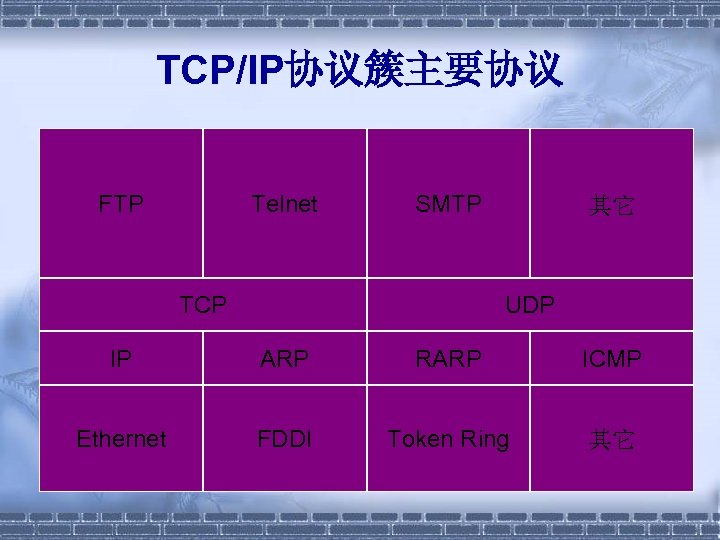
TCP/IP协议簇主要协议 FTP Telnet SMTP TCP 其它 UDP IP ARP RARP ICMP Ethernet FDDI Token Ring 其它

IP包头 Versio n IHL Type of Service Identification Time to Live Protocol Total Length Flags Fragment Offset Header Checksum Source Address Destination Address Options Padding
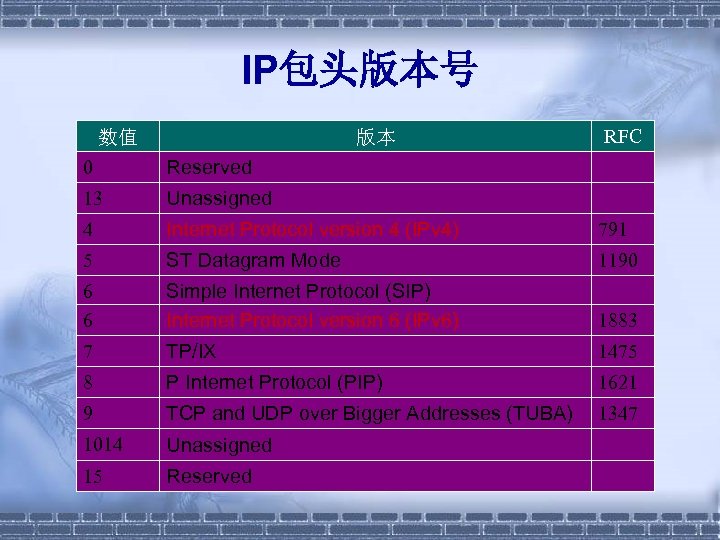
IP包头版本号 数值 RFC 版本 0 Reserved 13 Unassigned 4 Internet Protocol version 4 (IPv 4) 791 5 ST Datagram Mode 1190 6 6 Simple Internet Protocol (SIP) Internet Protocol version 6 (IPv 6) 1883 7 TP/IX 1475 8 P Internet Protocol (PIP) 1621 9 TCP and UDP over Bigger Addresses (TUBA) 1347 1014 Unassigned 15 Reserved

IP包头协议字段值 协议字段 值 1 2 4 6 17 45 46 47 54 88 89 协议 Internet Control Message Protocol (ICMP) Internet Group Management Protocol (IGMP) IP in IP (encapsulation) Transmission Control Protocol (TCP) User Datagram Protocol (UDP) Inter-Domain Routing Protocol (IDRP) Resource Reservation Protocol (RSVP) Generic Routing Encapsulation (GRE) NBMA Next Hop Resolution Protocol (NHRP) Cisco Internet Gateway Routing Protocol (IGRP) Open Shortest Path First (OSPF)
IP地址 § § § A类: 1 -126; B类: 128 -191; C类: 192 -223; D类: 224 -239; E类: 240 -254; RFC 1918;
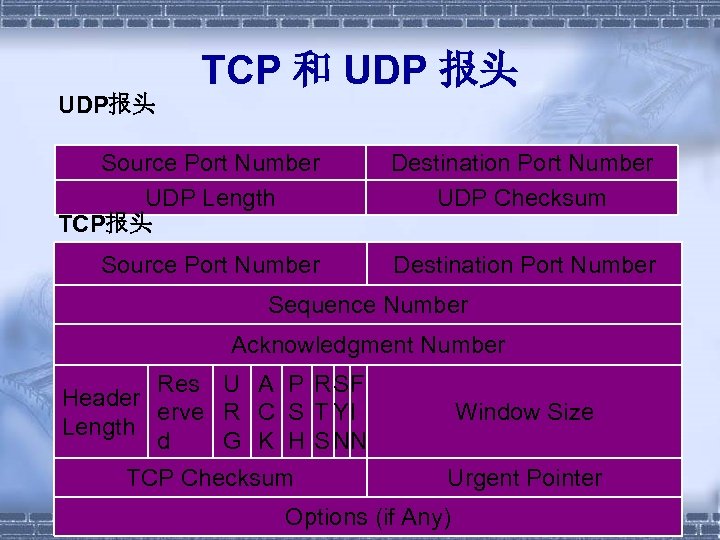
UDP报头 TCP 和 UDP 报头 Source Port Number UDP Length TCP报头 Destination Port Number UDP Checksum Source Port Number Destination Port Number Sequence Number Acknowledgment Number Res U A P R SF Header erve R C S T YI Length d G K H S NN Window Size TCP Checksum Urgent Pointer Options (if Any)

二、通信和网络技术
局域网(LAN) § 特点 • 高数据传输率; • 短距离; • 低误码率; § 线缆 • • 光纤(Fiber Optic) 非屏蔽双绞线(Unshielded Twisted Pair, UTP); 屏蔽双绞线(Shielded Twisted Pair, STP); 同轴电缆(Coaxial Cable); § 介质:以太网、令牌环、FDDI; § 拓扑:总线,星形,环形,网状;
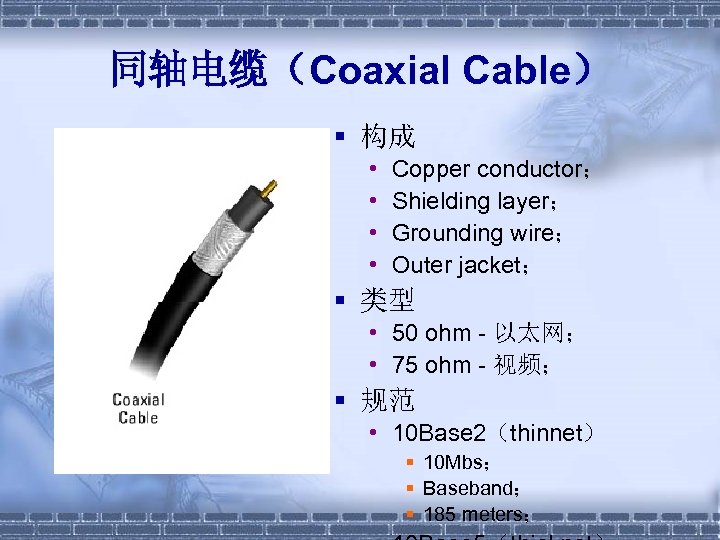
同轴电缆(Coaxial Cable) § 构成 • • Copper conductor; Shielding layer; Grounding wire; Outer jacket; § 类型 • 50 ohm - 以太网; • 75 ohm - 视频; § 规范 • 10 Base 2(thinnet) § 10 Mbs; § Baseband; § 185 meters;

双绞线(Twisted Pair) § 构成 • 多对铜线; • Outer jacket; § 类型 • UTP(Unshielded Twisted Pair); • STP(Shielded Twisted Pair);
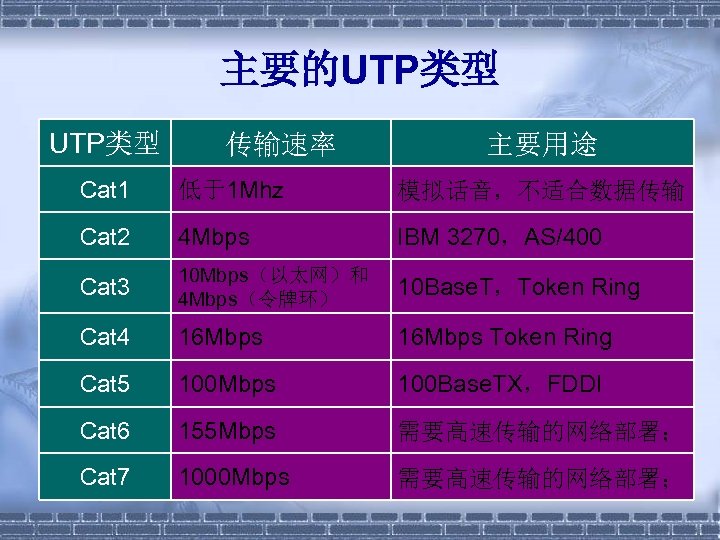
主要的UTP类型 传输速率 主要用途 Cat 1 低于1 Mhz 模拟话音,不适合数据传输 Cat 2 4 Mbps IBM 3270,AS/400 Cat 3 10 Mbps(以太网)和 4 Mbps(令牌环) 10 Base. T,Token Ring Cat 4 16 Mbps Token Ring Cat 5 100 Mbps 100 Base. TX,FDDI Cat 6 155 Mbps 需要高速传输的网络部署; Cat 7 1000 Mbps 需要高速传输的网络部署;
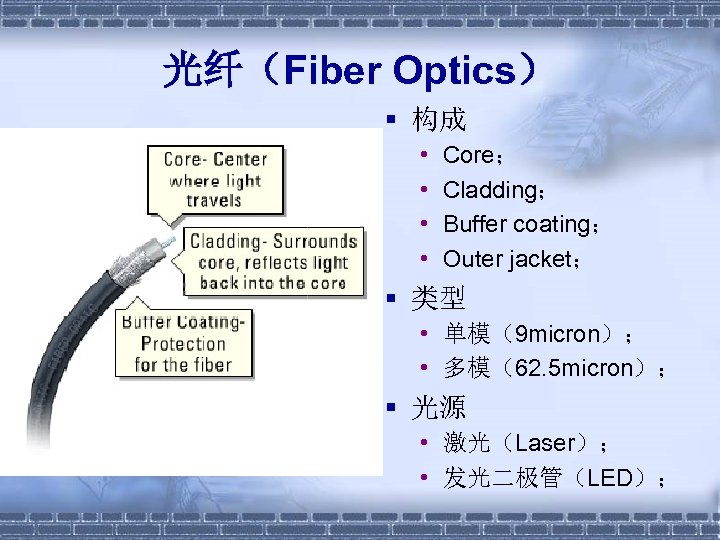
光纤(Fiber Optics) § 构成 • • Core; Cladding; Buffer coating; Outer jacket; § 类型 • 单模(9 micron); • 多模(62. 5 micron); § 光源 • 激光(Laser); • 发光二极管(LED);
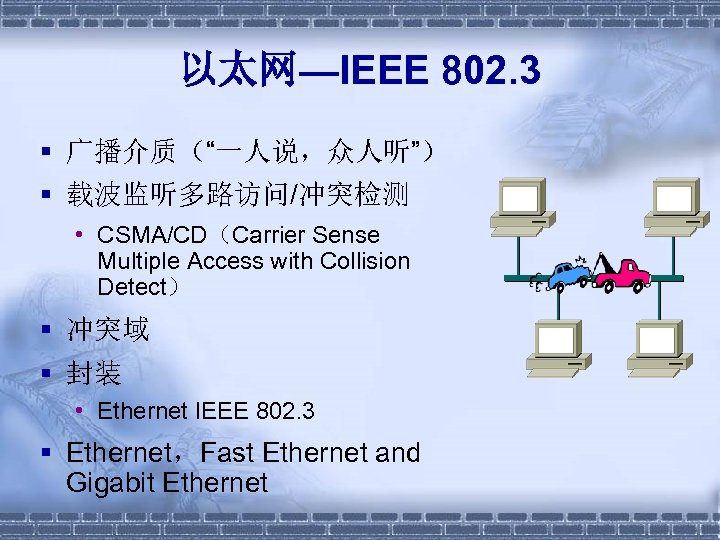
以太网—IEEE 802. 3 § 广播介质(“一人说,众人听”) § 载波监听多路访问/冲突检测 • CSMA/CD(Carrier Sense Multiple Access with Collision Detect) § 冲突域 § 封装 • Ethernet IEEE 802. 3 § Ethernet,Fast Ethernet and Gigabit Ethernet
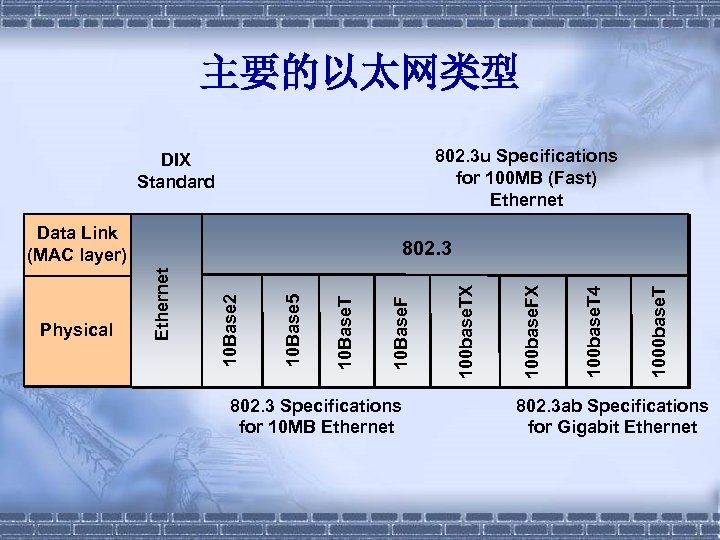
主要的以太网类型 802. 3 u Specifications for 100 MB (Fast) Ethernet DIX Standard Data Link (MAC layer) 802. 3 Specifications for 10 MB Ethernet 1000 base. T 100 base. T 4 100 base. FX 100 base. TX 10 Base. F 10 Base. T 10 Base 5 10 Base 2 Ethernet Physical 802. 3 ab Specifications for Gigabit Ethernet
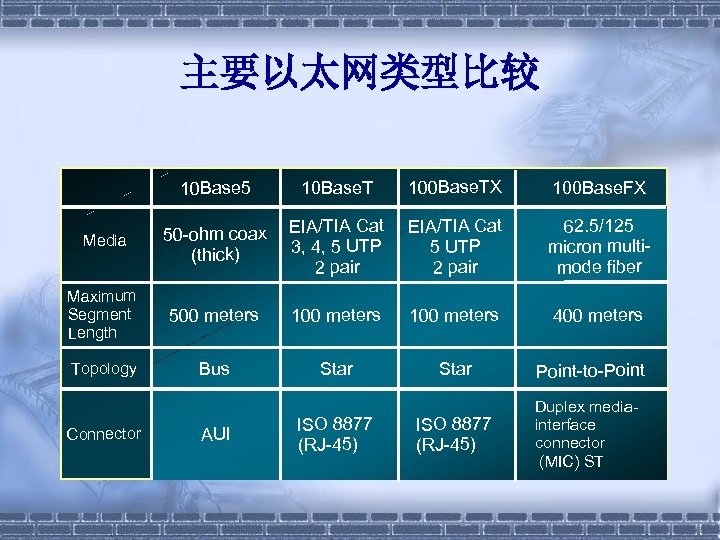
主要以太网类型比较 10 Base 5 10 Base. T 100 Base. TX 100 Base. FX Media 50 -ohm coax (thick) EIA/TIA Cat 3, 4, 5 UTP 2 pair EIA/TIA Cat 5 UTP 2 pair 62. 5/125 micron multimode fiber Maximum Segment Length 500 meters 100 meters 400 meters Topology Bus Star Point-to-Point ISO 8877 (RJ-45) Duplex mediainterface connector (MIC) ST Connector AUI ISO 8877 (RJ-45)
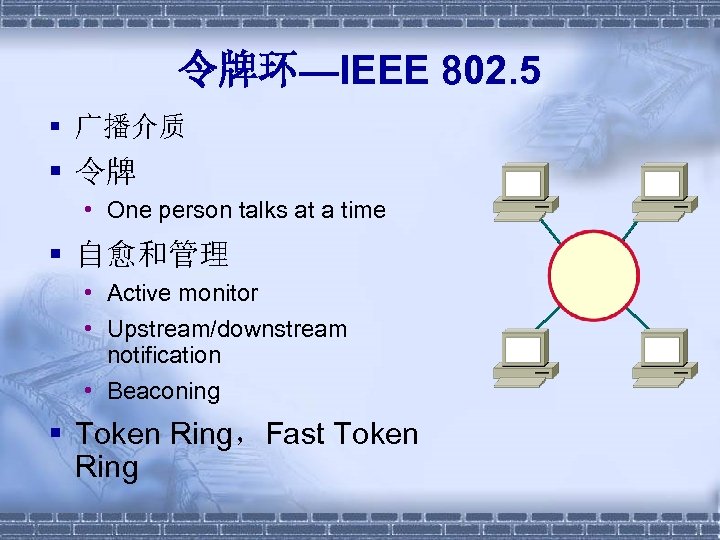
令牌环—IEEE 802. 5 § 广播介质 § 令牌 • One person talks at a time § 自愈和管理 • Active monitor • Upstream/downstream notification • Beaconing § Token Ring,Fast Token Ring
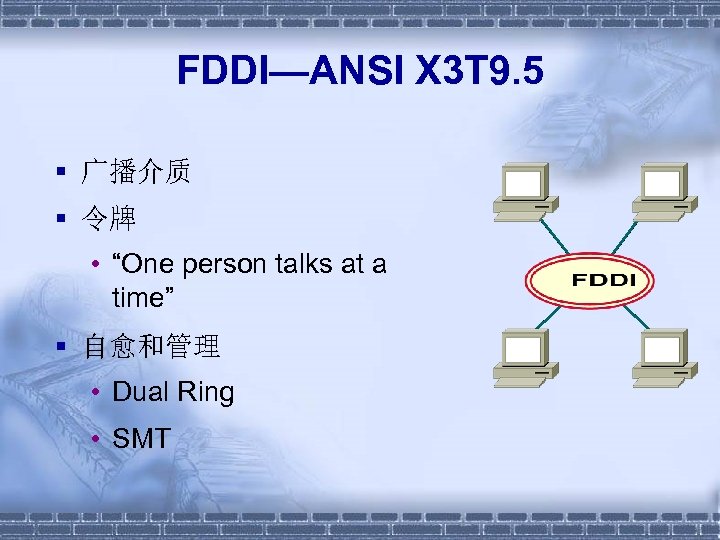
FDDI—ANSI X 3 T 9. 5 § 广播介质 § 令牌 • “One person talks at a time” § 自愈和管理 • Dual Ring • SMT
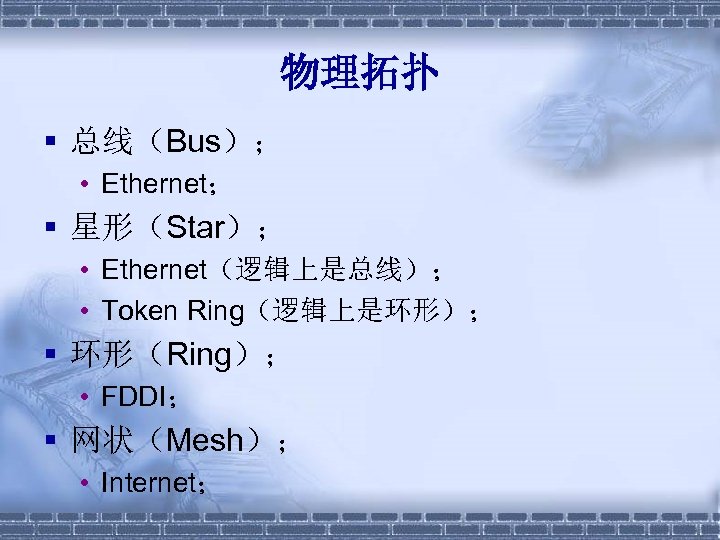
物理拓扑 § 总线(Bus); • Ethernet; § 星形(Star); • Ethernet(逻辑上是总线); • Token Ring(逻辑上是环形); § 环形(Ring); • FDDI; § 网状(Mesh); • Internet;
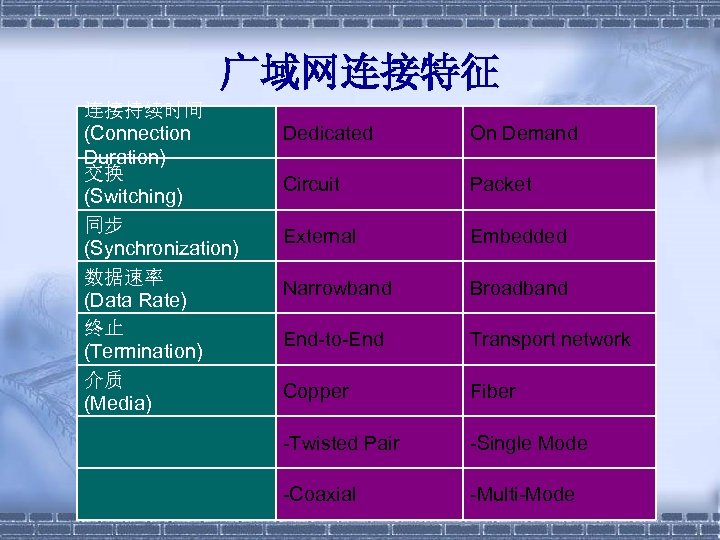
广域网连接特征 连接持续时间 (Connection Duration) 交换 (Switching) 同步 (Synchronization) 数据速率 (Data Rate) 终止 (Termination) 介质 (Media) Dedicated On Demand Circuit Packet External Embedded Narrowband Broadband End-to-End Transport network Copper Fiber -Twisted Pair -Single Mode -Coaxial -Multi-Mode
广域网连接类型 § § 专用电路交换; 按需电路交换; 包交换(虚电路); 宽带接入;
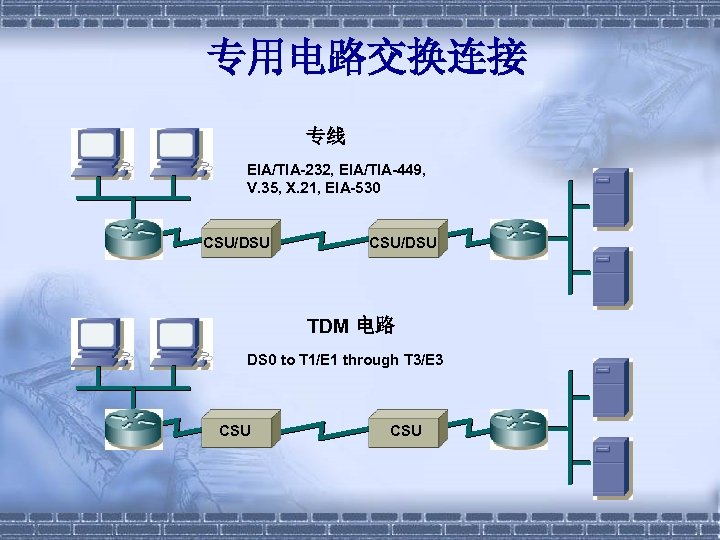
专用电路交换连接 专线 EIA/TIA-232, EIA/TIA-449, V. 35, X. 21, EIA-530 CSU/DSU TDM 电路 DS 0 to T 1/E 1 through T 3/E 3 CSU
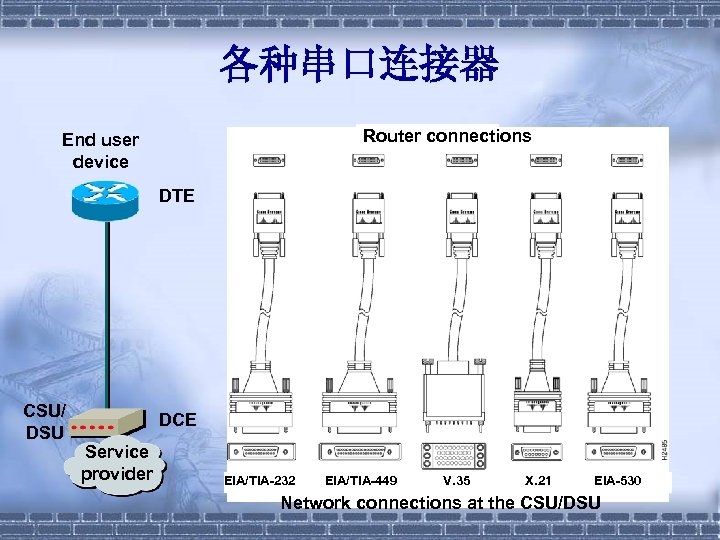
各种串口连接器 Router connections End user device DTE CSU/ DSU DCE Service provider EIA/TIA-232 EIA/TIA-449 V. 35 X. 21 EIA-530 Network connections at the CSU/DSU
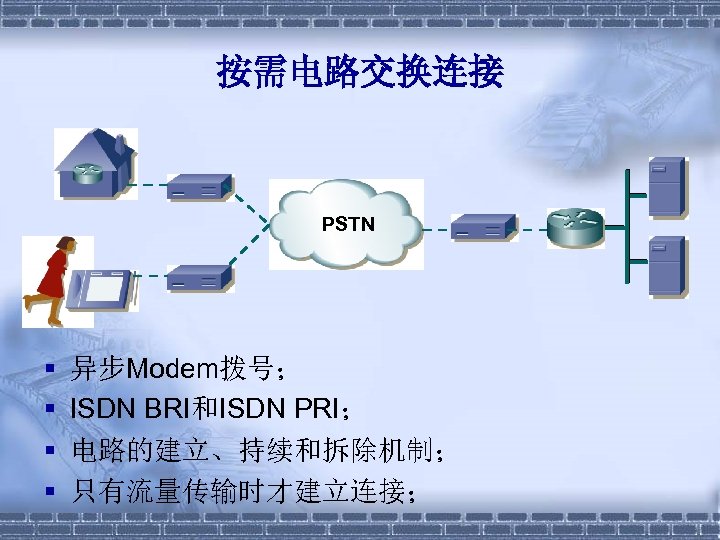
按需电路交换连接 PSTN § § 异步Modem拨号; ISDN BRI和ISDN PRI; 电路的建立、持续和拆除机制; 只有流量传输时才建立连接;
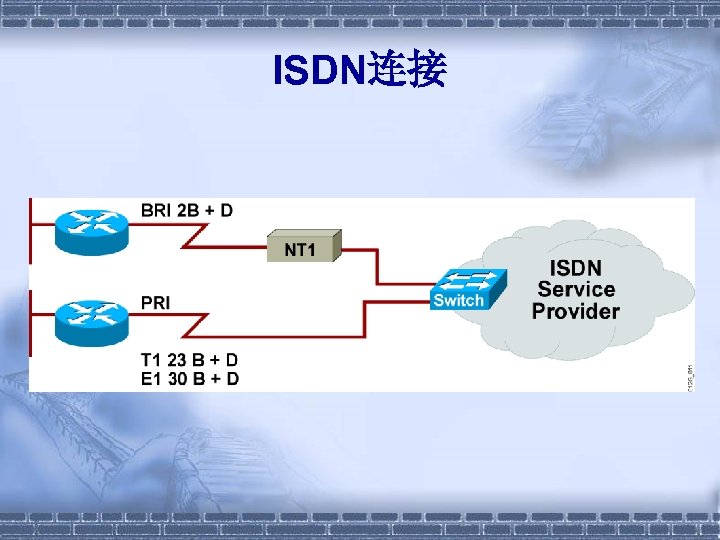
ISDN连接
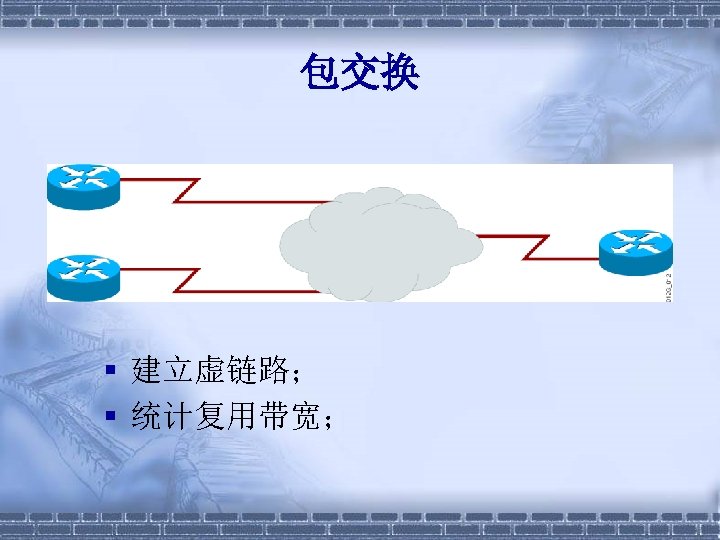
包交换 § 建立虚链路; § 统计复用带宽;
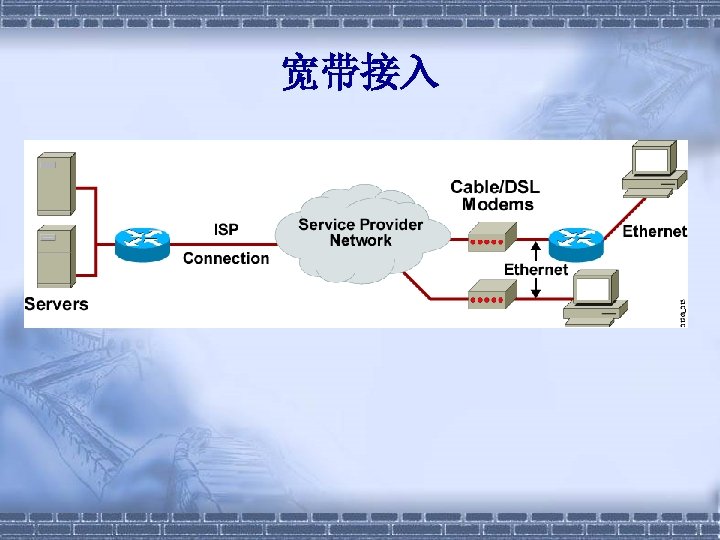
宽带接入

广域网速率 Digital Signal (DS)名 电 路比特率 称 DS 0 64 Kbps 使用 DS 0数 量 1 T载 波名称 E载 波名称 - - DS 1 1. 544 Mbps 24 T-1 - - 2. 048 Mbps 32 - E-1 DS 1 C 3. 152 Mbps 48 - - DS 2 6. 312 Mbps 96 T-2 - - 8. 448 Mbps 128 - E-2 - 34. 368 Mbps 512 - E-3 DS 3 44. 736 Mbps 672或 28 DS 1 s 139. 264 Mbps 2048 T-3 - - E-4 DS 4/NA 139. 264 Mbps 2176 - - DS 4 274. 176 Mbps 4032 - - 565. 148 Mbps 4 E-4 Channels - E-5 - -
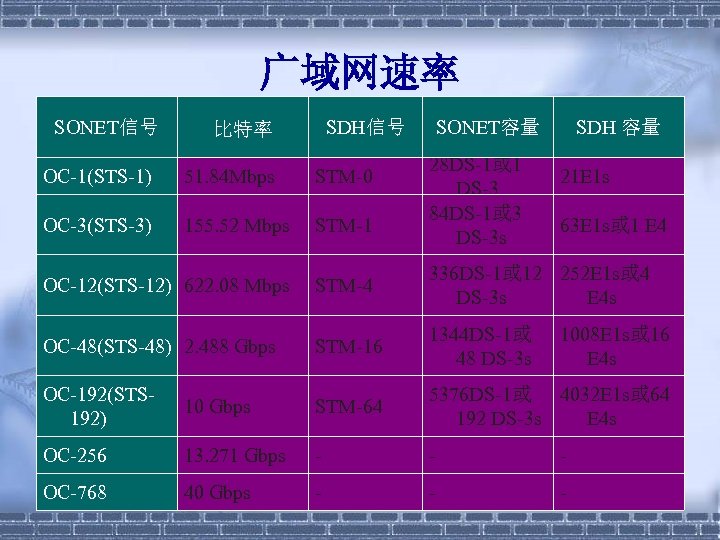
广域网速率 SONET信号 SDH信号 比特率 SONET容量 28 DS-1或 1 DS-3 84 DS-1或 3 DS-3 s SDH 容量 OC-1(STS-1) 51. 84 Mbps STM-0 21 E 1 s OC-3(STS-3) 155. 52 Mbps STM-1 OC-12(STS-12) 622. 08 Mbps STM-4 336 DS-1或 12 252 E 1 s或 4 DS-3 s E 4 s OC-48(STS-48) 2. 488 Gbps STM-16 1344 DS-1或 48 DS-3 s OC-192(STS 192) 10 Gbps STM-64 5376 DS-1或 4032 E 1 s或 64 192 DS-3 s E 4 s OC-256 13. 271 Gbps - - - OC-768 40 Gbps - - - 63 E 1 s或 1 E 4 1008 E 1 s或 16 E 4 s
SDLC/HDLC/PPP § IBM发明SDLC; § IEEE制定HDLC标 准; § IETF制定PPP标准; § 非广播介质 • 点到点; • 点到多点;
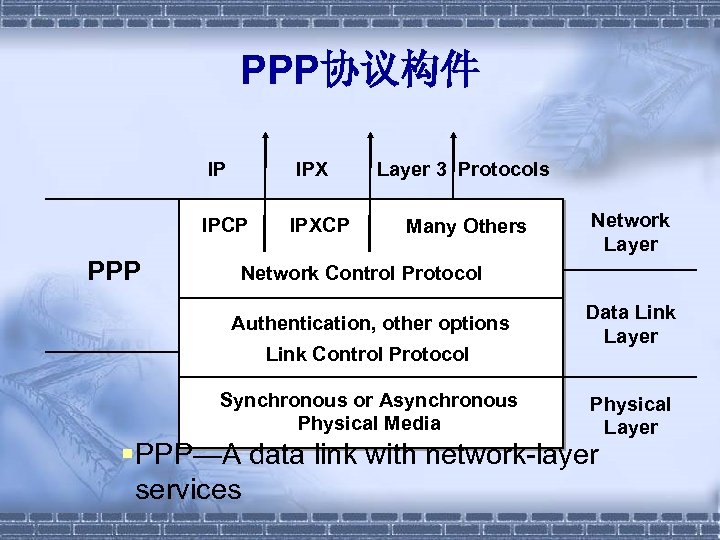
PPP协议构件 IP IPX IPCP PPP IPXCP Layer 3 Protocols Many Others Network Layer Network Control Protocol Authentication, other options Link Control Protocol Synchronous or Asynchronous Physical Media Data Link Layer Physical Layer §PPP—A data link with network-layer services
Frame Relay § 非广播介质 • 点到点; • 点到多点; § 拥塞避免 • FECN,BECN, DE;
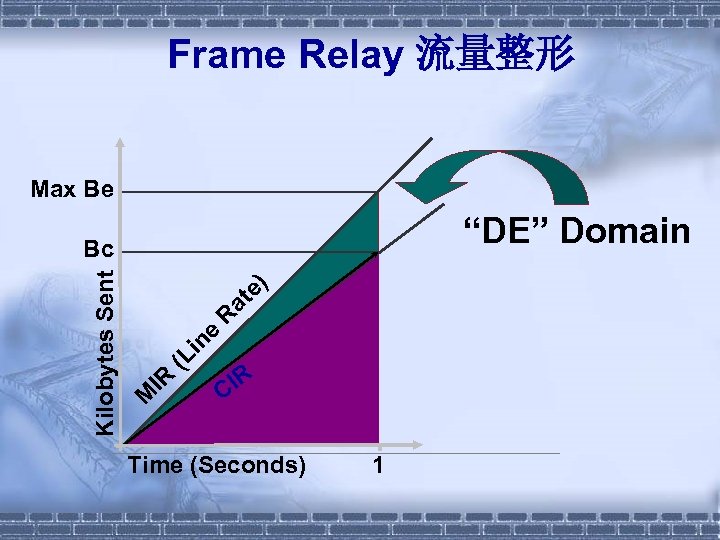
Frame Relay 流量整形 Max Be “DE” Domain Kilobytes Sent M IR (L in e R at e) Bc IR C Time (Seconds) 1
ATM(Asynchronous Transfer Mode) § 非广播介质 • 点到点; • 点到多点; § 53字节信元;
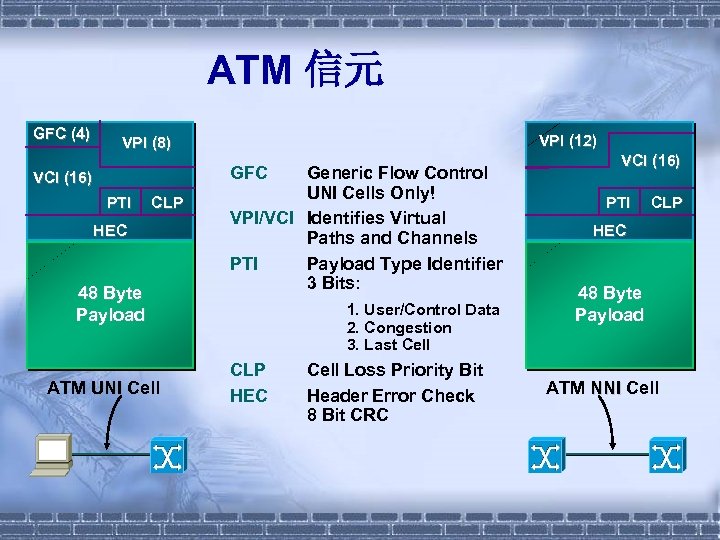
ATM 信元 GFC (4) VPI (12) VPI (8) GFC VCI (16) PTI CLP HEC 48 Byte Payload ATM UNI Cell Generic Flow Control UNI Cells Only! VPI/VCI Identifies Virtual Paths and Channels PTI Payload Type Identifier 3 Bits: 1. User/Control Data 2. Congestion 3. Last Cell CLP HEC Cell Loss Priority Bit Header Error Check 8 Bit CRC VCI (16) PTI CLP HEC 48 Byte Payload ATM NNI Cell
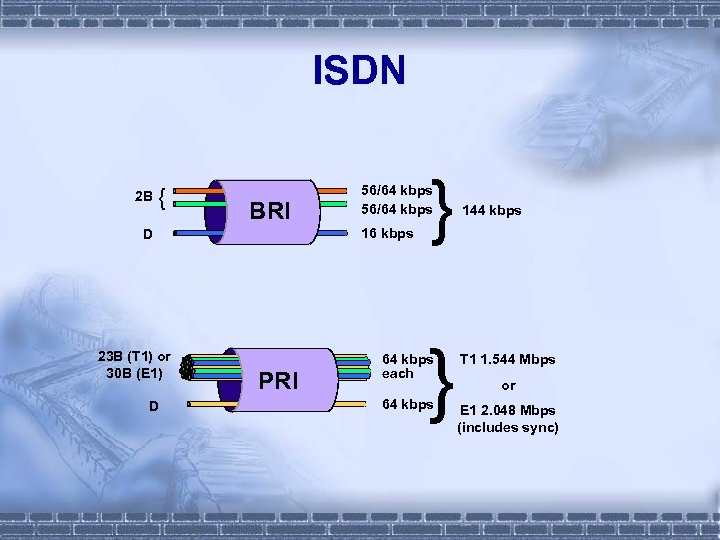
ISDN 2 B { BRI 16 kbps D 23 B (T 1) or 30 B (E 1) D PRI } 56/64 kbps } 144 kbps 64 kbps each T 1 1. 544 Mbps 64 kbps E 1 2. 048 Mbps (includes sync) or
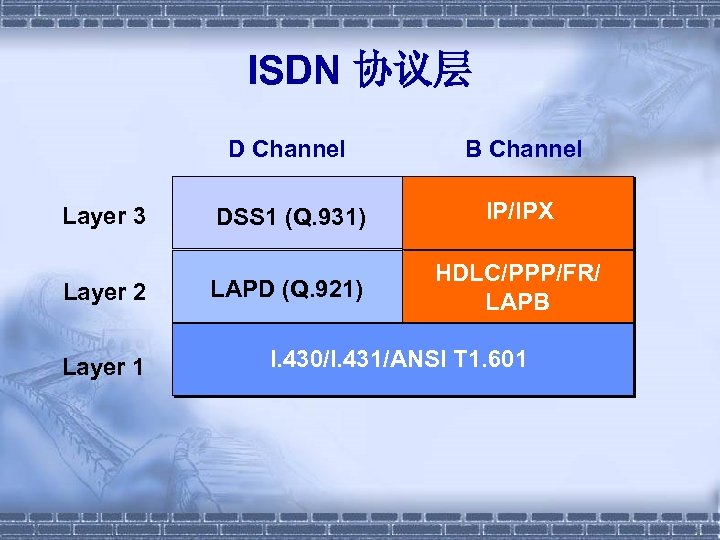
ISDN 协议层 D Channel Layer 3 Layer 2 Layer 1 B Channel DSS 1 (Q. 931) IP/IPX LAPD (Q. 921) HDLC/PPP/FR/ LAPB I. 430/I. 431/ANSI T 1. 601

x. DSL服务 VDSL—Very High Bit-Rate DSL 数据最大下行 铜缆对数 是否支持 /上行速率 模拟话音 (bps) 最大距离 (km-Feet) 25 M/1. 6 M or 8 M/8 M 1 Yes 0. 9 – 3, 000 ADSL—Asymmetric DSL 7 M/1 M 1 Yes 5. 5 – 18, 000 HDSL—High Bit Rate DSL 1. 5 M – 2. 0 M/ 1. 5 M – 2. 0 M 2 No 4. 6 – 15, 000 SDSL—Symmetric DSL 784 K/784 K 1 No 6. 9 – 22, 000 IDSL —ISDN DSL 144 K/144 K 1 No 5. 5 – 18, 000 ISDN 128 K/128 K 1 No 5. 5 – 18, 000
有关概念的区分 § § 模拟信号Vs. 数字信号; 同步通信Vs. 异步通信; 基带传输Vs. 宽带传输; 单播、组播、广播
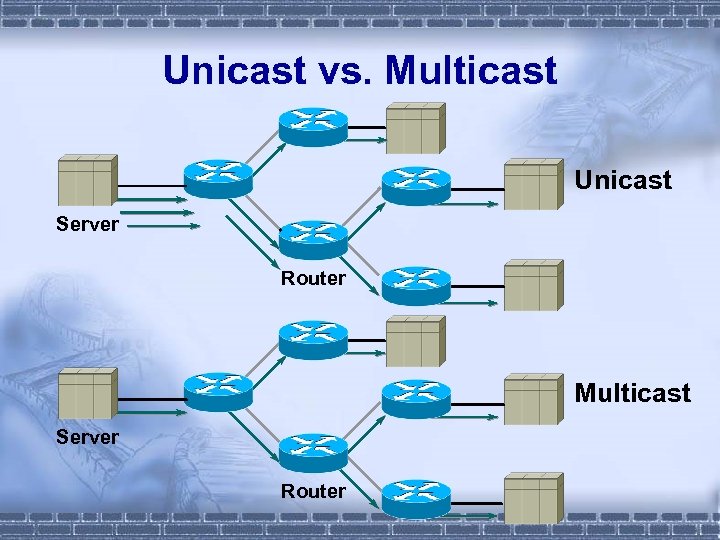
Unicast vs. Multicast Unicast Server Router Multicast Server Router

二、互联网技术与服务
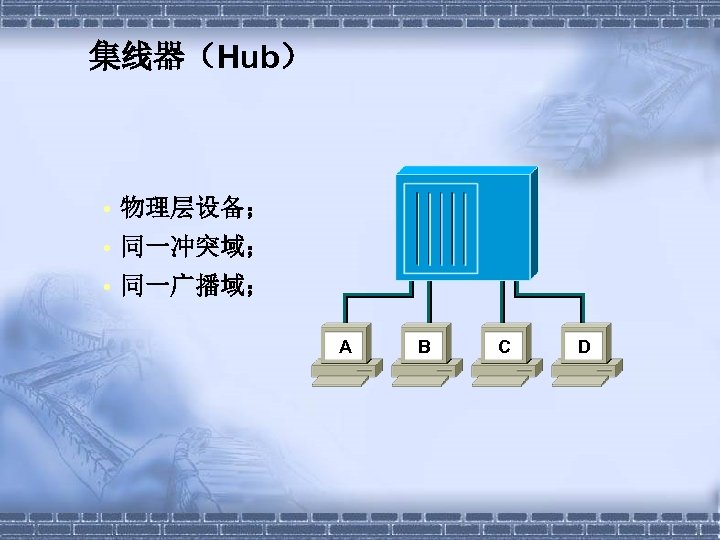
集线器(Hub) • 物理层设备; • 同一冲突域; • 同一广播域; A B C D
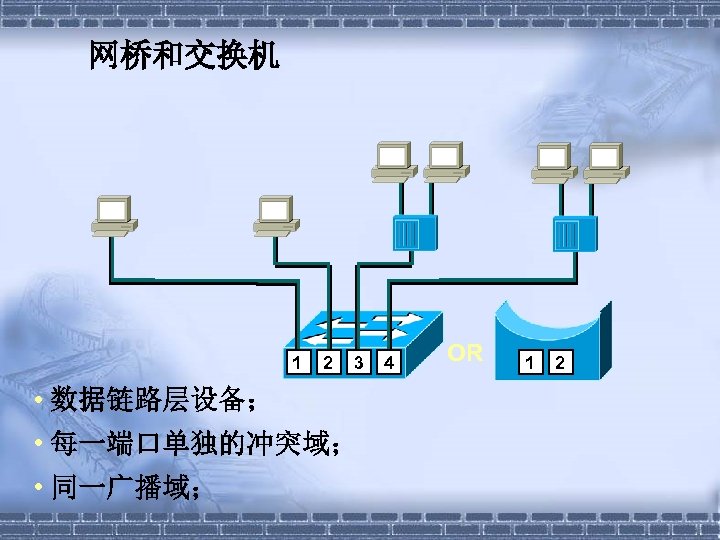
网桥和交换机 1 2 3 • 数据链路层设备; • 每一端口单独的冲突域; • 同一广播域; 4 OR 1 2
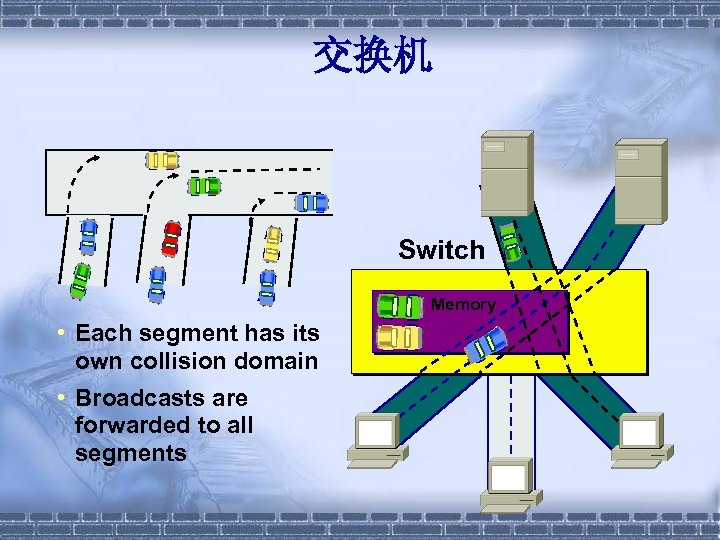
交换机 Switch Memory • Each segment has its own collision domain • Broadcasts are forwarded to all segments
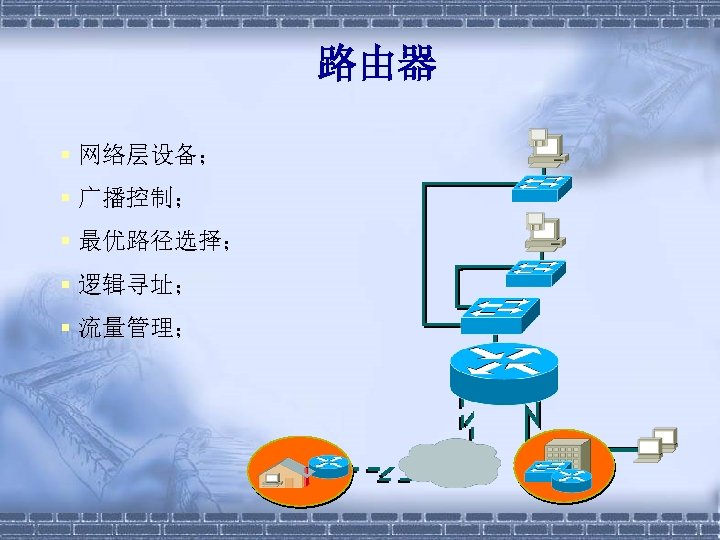
路由器 § 网络层设备; § 广播控制; § 最优路径选择; § 逻辑寻址; § 流量管理;
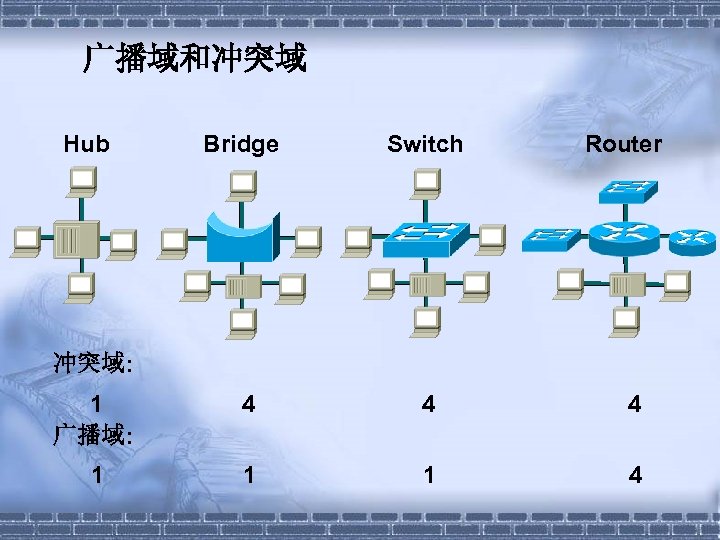
广播域和冲突域 Hub Bridge Switch Router 冲突域: 1 广播域: 4 4 4 1 1 1 4
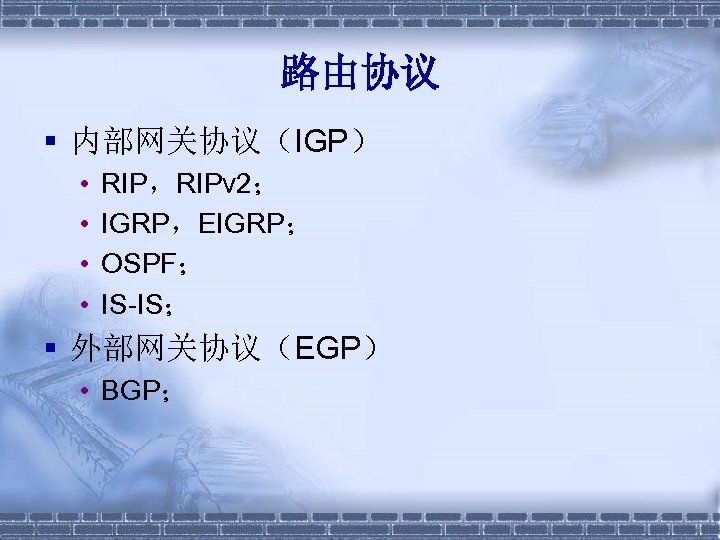
路由协议 § 内部网关协议(IGP) • • RIP,RIPv 2; IGRP,EIGRP; OSPF; IS-IS; § 外部网关协议(EGP) • BGP;
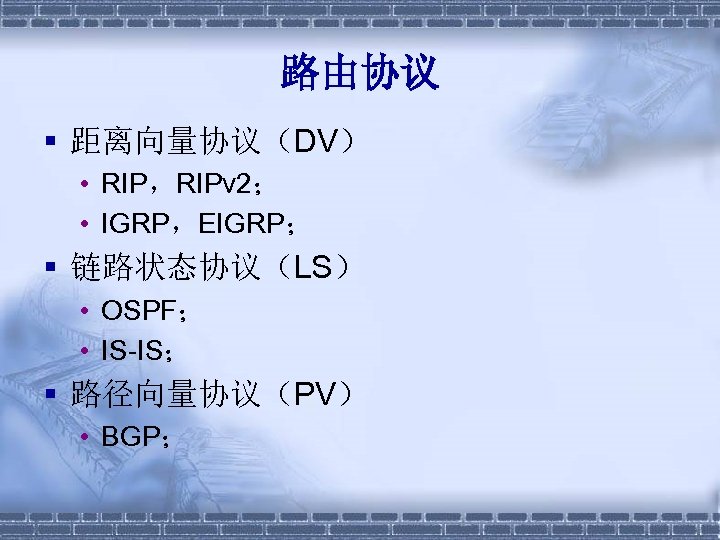
路由协议 § 距离向量协议(DV) • RIP,RIPv 2; • IGRP,EIGRP; § 链路状态协议(LS) • OSPF; • IS-IS; § 路径向量协议(PV) • BGP;
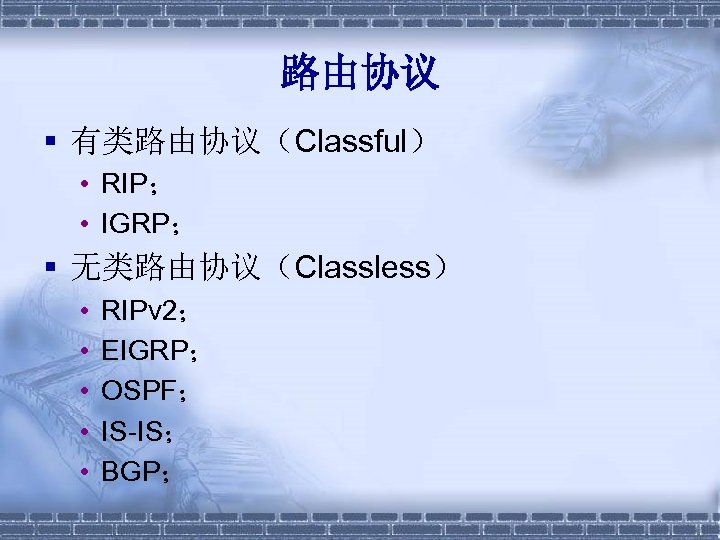
路由协议 § 有类路由协议(Classful) • RIP; • IGRP; § 无类路由协议(Classless) • • • RIPv 2; EIGRP; OSPF; IS-IS; BGP;
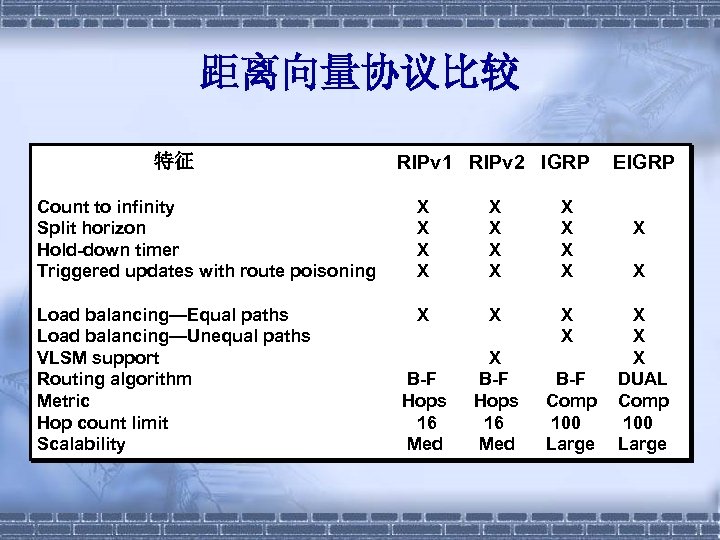
距离向量协议比较 特征 RIPv 1 RIPv 2 IGRP Count to infinity Split horizon Hold-down timer Triggered updates with route poisoning X X X Load balancing—Equal paths Load balancing—Unequal paths VLSM support Routing algorithm Metric Hop count limit Scalability X X B-F Hops 16 Med B-F Comp 100 Large EIGRP X X X DUAL Comp 100 Large
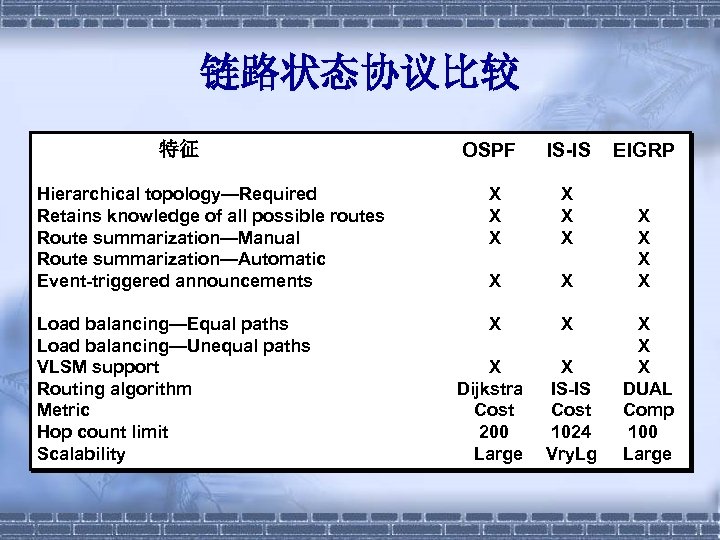
链路状态协议比较 特征 OSPF IS-IS Hierarchical topology—Required Retains knowledge of all possible routes Route summarization—Manual Route summarization—Automatic Event-triggered announcements X X X X Load balancing—Equal paths Load balancing—Unequal paths VLSM support Routing algorithm Metric Hop count limit Scalability X X X Dijkstra Cost 200 Large X IS-IS Cost 1024 Vry. Lg EIGRP X X X X DUAL Comp 100 Large
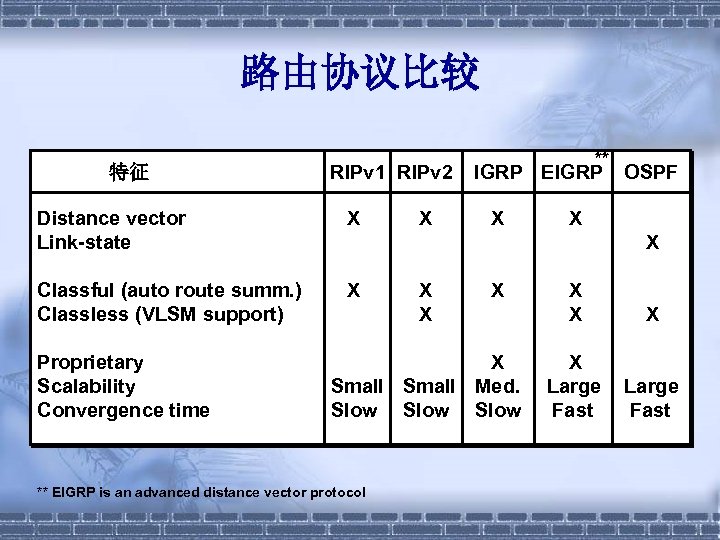
路由协议比较 特征 RIPv 1 RIPv 2 Distance vector Link-state X Classful (auto route summ. ) Classless (VLSM support) X Proprietary Scalability Convergence time X ** IGRP EIGRP X OSPF X X X Small Med. Slow ** EIGRP is an advanced distance vector protocol X X Large Fast
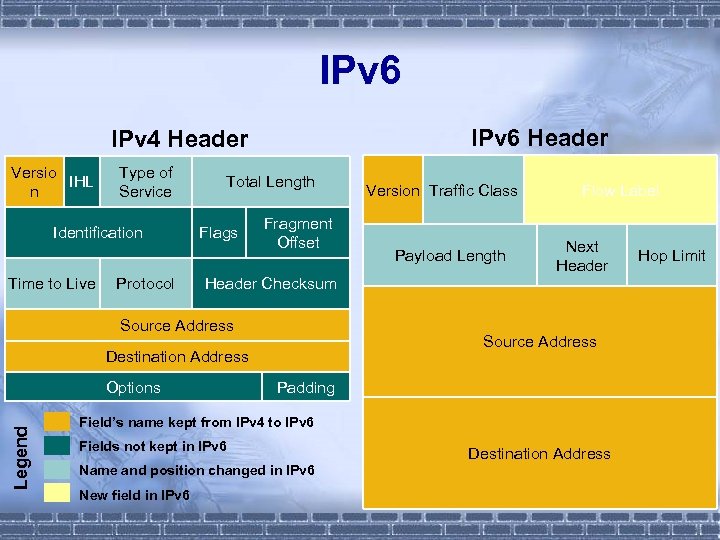
IPv 6 Header IPv 4 Header Versio IHL n Type of Service Identification Time to Live Protocol Total Length Flags Fragment Offset Payload Length Flow Label Next Header Checksum Source Address Destination Address Options Legend Version Traffic Class Padding Field’s name kept from IPv 4 to IPv 6 Fields not kept in IPv 6 Name and position changed in IPv 6 New field in IPv 6 Destination Address Hop Limit
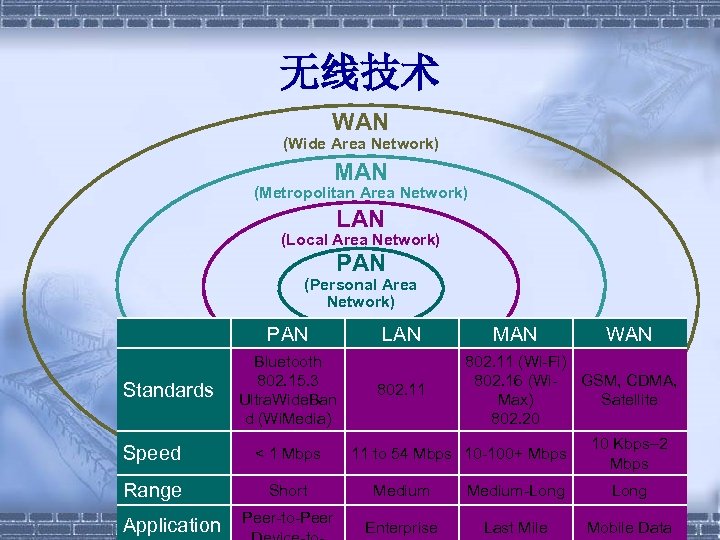
无线技术 WAN (Wide Area Network) MAN (Metropolitan Area Network) LAN (Local Area Network) PAN (Personal Area Network) PAN Standards Bluetooth 802. 15. 3 Ultra. Wide. Ban d (Wi. Media) Speed < 1 Mbps Range Short Application Peer-to-Peer LAN 802. 11 MAN WAN 802. 11 (Wi-Fi) 802. 16 (Wi. GSM, CDMA, Max) Satellite 802. 20 11 to 54 Mbps 10 -100+ Mbps 10 Kbps– 2 Mbps Medium-Long Enterprise Last Mile Mobile Data
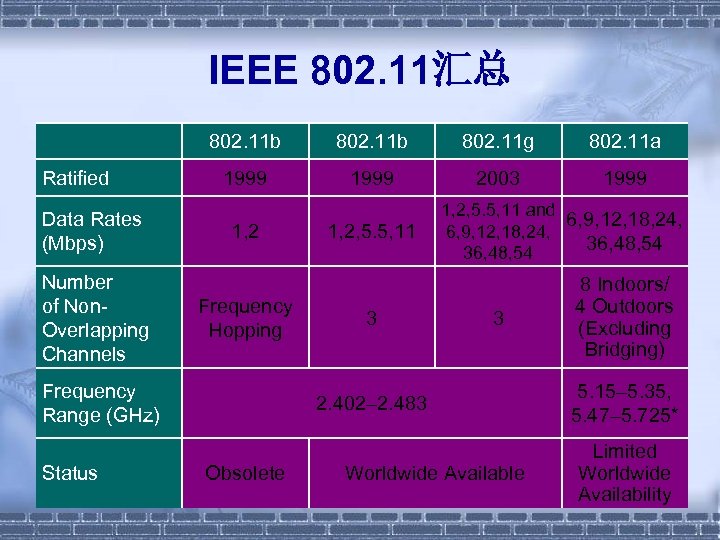
IEEE 802. 11汇总 802. 11 b Ratified Data Rates (Mbps) Number of Non. Overlapping Channels 802. 11 b 802. 11 g 802. 11 a 1999 2003 1999 1, 2 Frequency Hopping Frequency Range (GHz) Status 1, 2, 5. 5, 11 3 1, 2, 5. 5, 11 and 6, 9, 12, 18, 24, 36, 48, 54 3 2. 402– 2. 483 Obsolete Worldwide Available 8 Indoors/ 4 Outdoors (Excluding Bridging) 5. 15– 5. 35, 5. 47– 5. 725* Limited Worldwide Availability
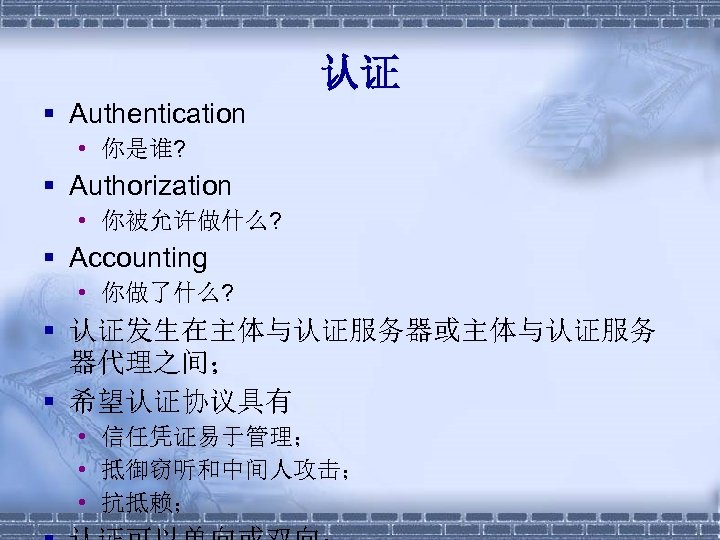
认证 § Authentication • 你是谁? § Authorization • 你被允许做什么? § Accounting • 你做了什么? § 认证发生在主体与认证服务器或主体与认证服务 器代理之间; § 希望认证协议具有 • 信任凭证易于管理; • 抵御窃听和中间人攻击; • 抗抵赖;
认证协议 § § § PAP CHAP EAP 802. 1 x Kerberos
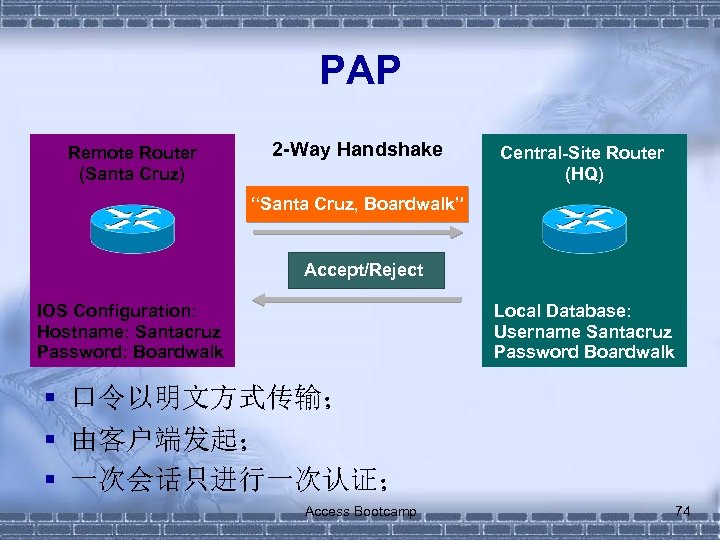
PAP Remote Router (Santa Cruz) 2 -Way Handshake Central-Site Router (HQ) “Santa Cruz, Boardwalk” Accept/Reject IOS Configuration: Hostname: Santacruz Password: Boardwalk Local Database: Username Santacruz Password Boardwalk § 口令以明文方式传输; § 由客户端发起; § 一次会话只进行一次认证; Access Bootcamp 74
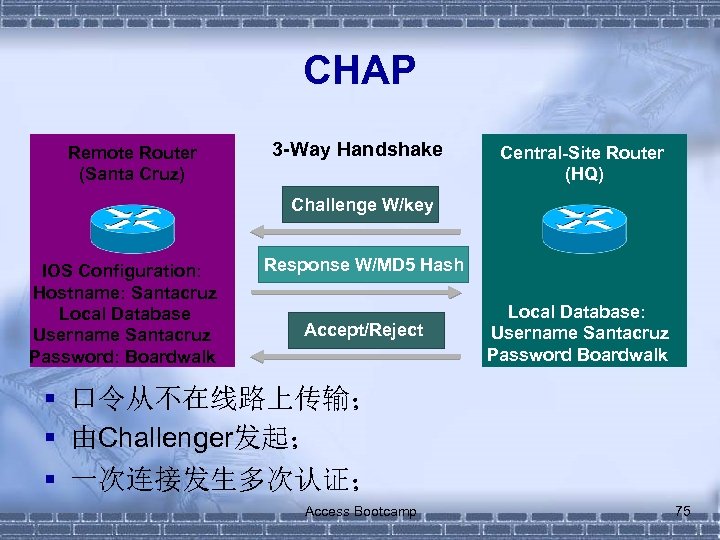
CHAP Remote Router (Santa Cruz) 3 -Way Handshake Central-Site Router (HQ) Challenge W/key IOS Configuration: Hostname: Santacruz Local Database Username Santacruz Password: Boardwalk Response W/MD 5 Hash Accept/Reject Local Database: Username Santacruz Password Boardwalk § 口令从不在线路上传输; § 由Challenger发起; § 一次连接发生多次认证; Access Bootcamp 75
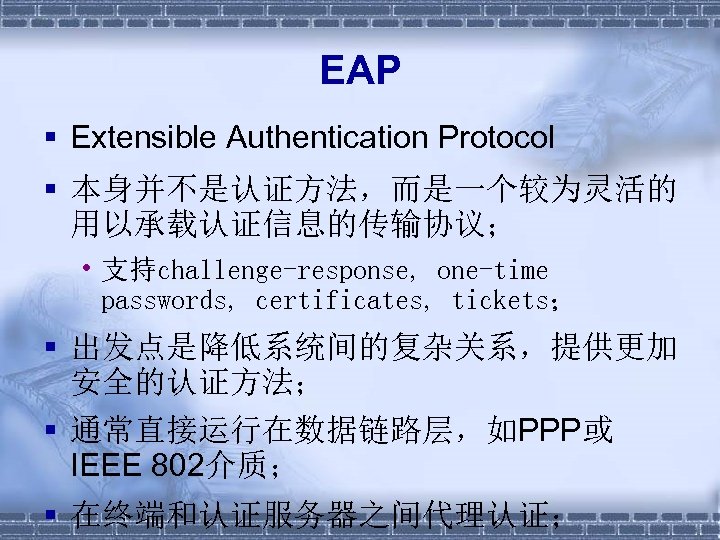
EAP § Extensible Authentication Protocol § 本身并不是认证方法,而是一个较为灵活的 用以承载认证信息的传输协议; • 支持challenge-response, one-time passwords, certificates, tickets; § 出发点是降低系统间的复杂关系,提供更加 安全的认证方法; § 通常直接运行在数据链路层,如PPP或 IEEE 802介质; § 在终端和认证服务器之间代理认证;
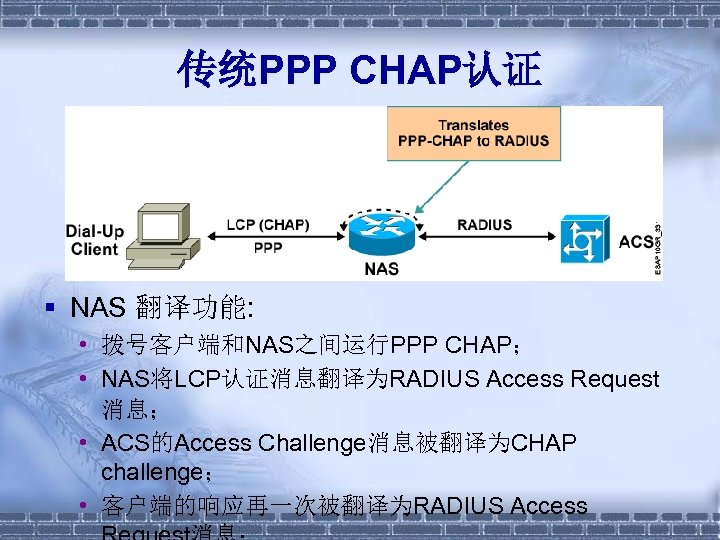
传统PPP CHAP认证 § NAS 翻译功能: • 拨号客户端和NAS之间运行PPP CHAP; • NAS将LCP认证消息翻译为RADIUS Access Request 消息; • ACS的Access Challenge消息被翻译为CHAP challenge; • 客户端的响应再一次被翻译为RADIUS Access
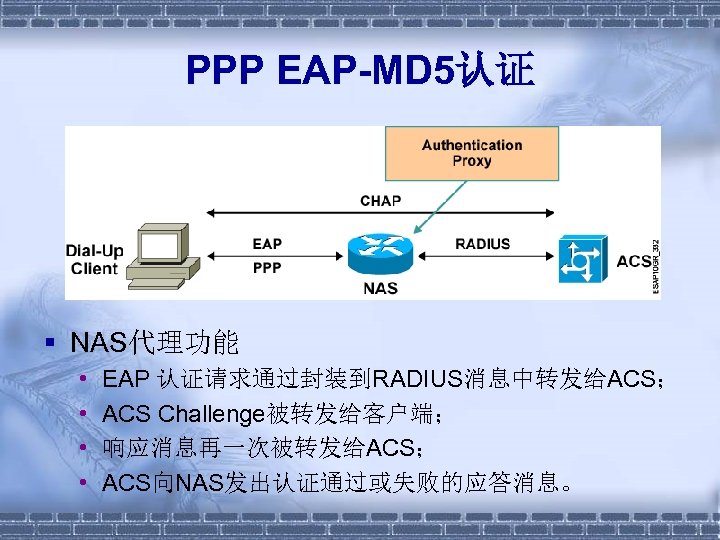
PPP EAP-MD 5认证 § NAS代理功能 • • EAP 认证请求通过封装到RADIUS消息中转发给ACS; ACS Challenge被转发给客户端; 响应消息再一次被转发给ACS; ACS向NAS发出认证通过或失败的应答消息。
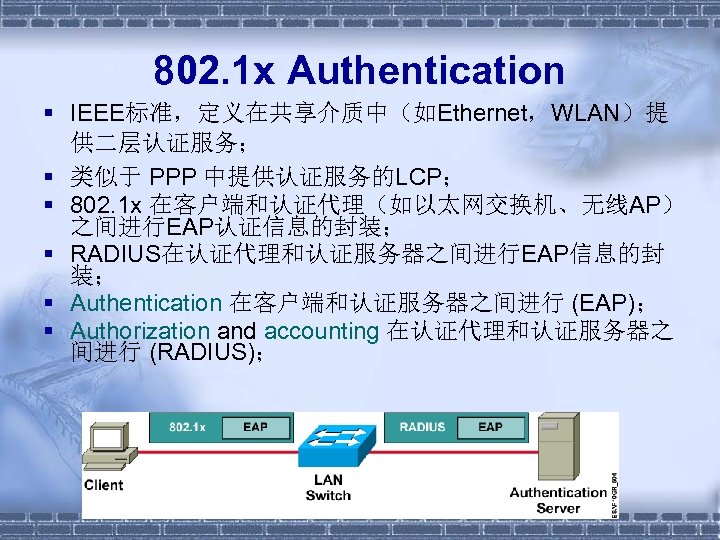
802. 1 x Authentication § IEEE标准,定义在共享介质中(如Ethernet,WLAN)提 供二层认证服务; § 类似于 PPP 中提供认证服务的LCP; § 802. 1 x 在客户端和认证代理(如以太网交换机、无线AP) 之间进行EAP认证信息的封装; § RADIUS在认证代理和认证服务器之间进行EAP信息的封 装; § Authentication 在客户端和认证服务器之间进行 (EAP); § Authorization and accounting 在认证代理和认证服务器之 间进行 (RADIUS);
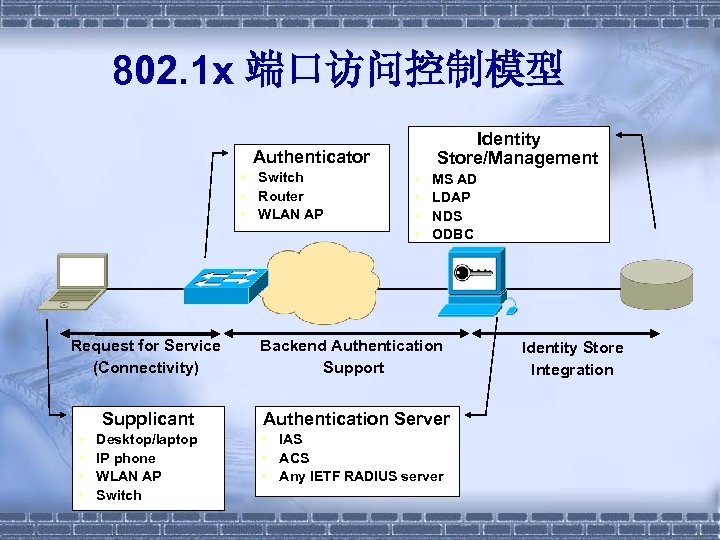
802. 1 x 端口访问控制模型 Identity Store/Management Authenticator • Switch • Router • WLAN AP Request for Service (Connectivity) Supplicant • • Desktop/laptop IP phone WLAN AP Switch • • MS AD LDAP NDS ODBC Backend Authentication Support Authentication Server • IAS • ACS • Any IETF RADIUS server Identity Store Integration

Kerberos § 认证协议: • 口令从不在网络中传输; • SSO (Single sign-on); § 三个实体: • 访问应用服务器上运行服务的客户端; • 认证服务器 ,即KDC (Key Distribution Center § 认证服务; § ticket-granting服务; • 应用服务器; § 使用DES对所有消息(除初始化请求)进
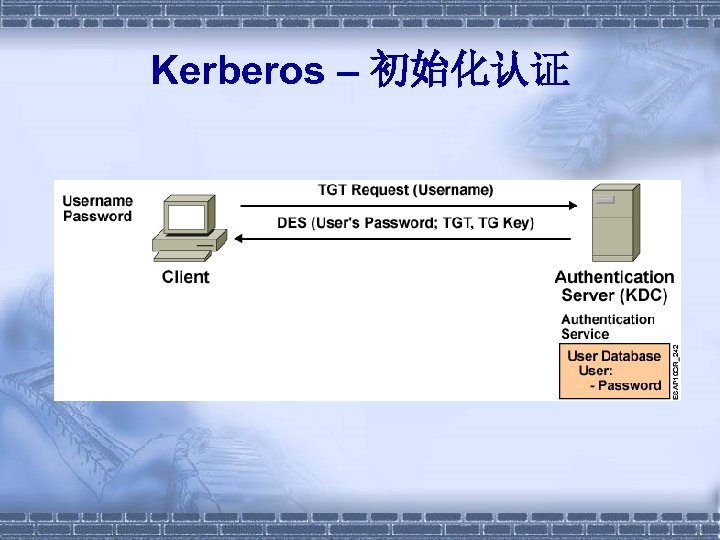
Kerberos – 初始化认证
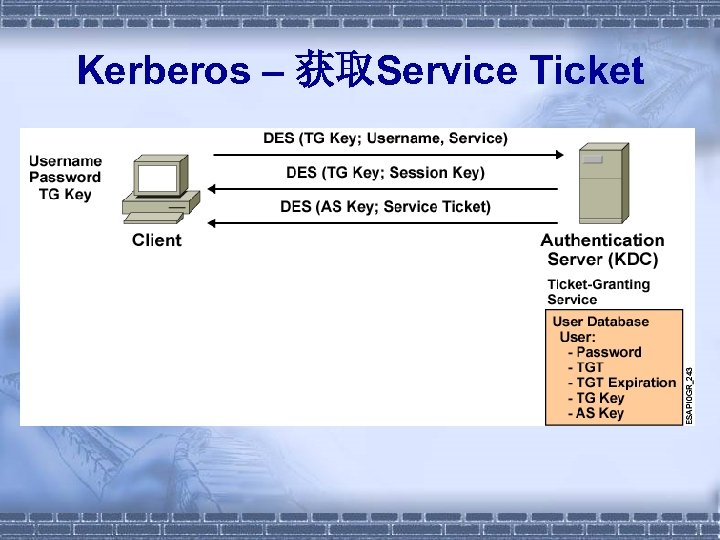
Kerberos – 获取Service Ticket
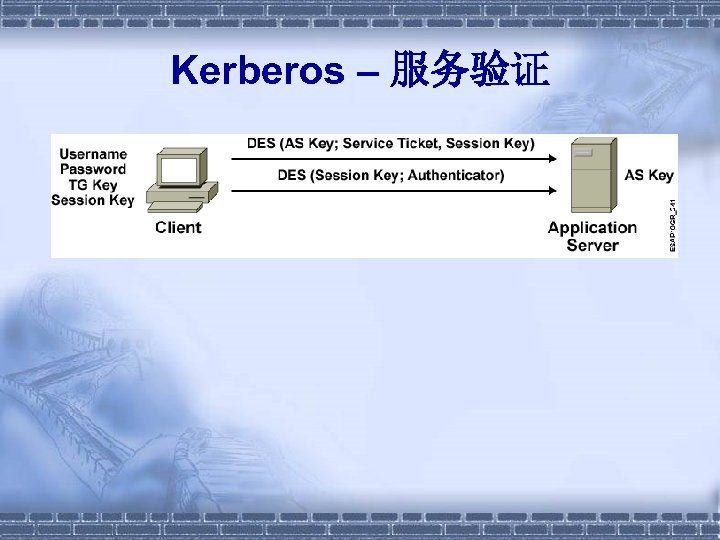
Kerberos – 服务验证
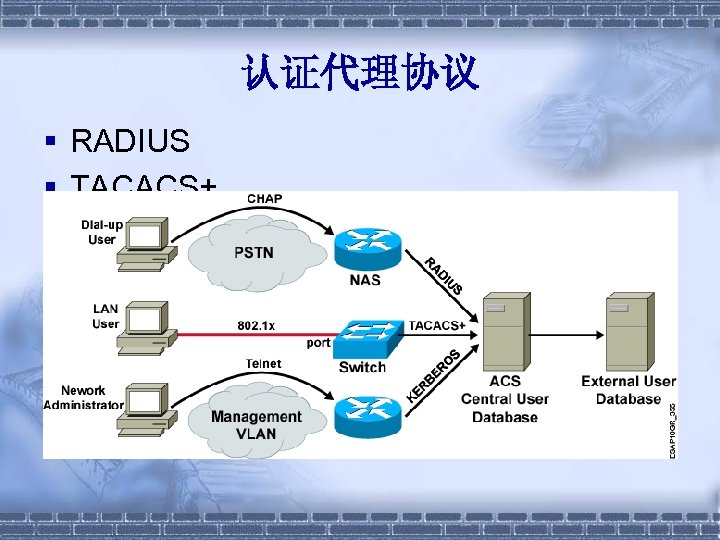
认证代理协议 § RADIUS § TACACS+
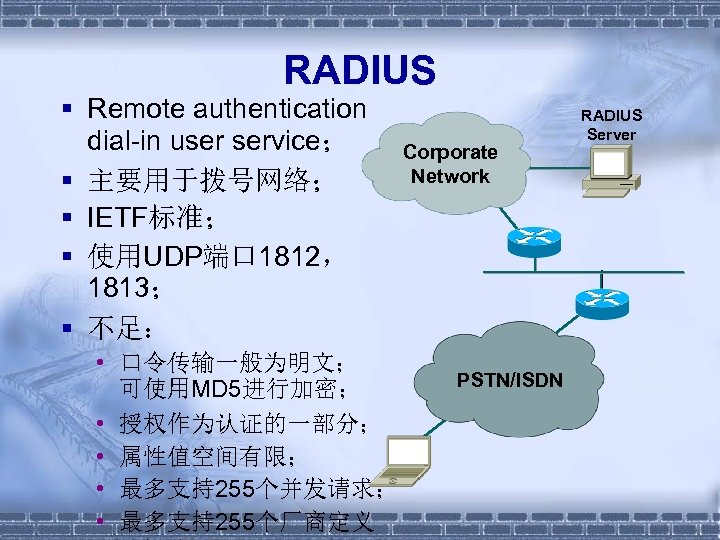
RADIUS § Remote authentication dial-in user service; § 主要用于拨号网络; § IETF标准; § 使用UDP端口 1812, 1813; § 不足: • 口令传输一般为明文; 可使用MD 5进行加密; • 授权作为认证的一部分; • 属性值空间有限; • 最多支持255个并发请求; • 最多支持255个厂商定义 Corporate Network PSTN/ISDN RADIUS Server
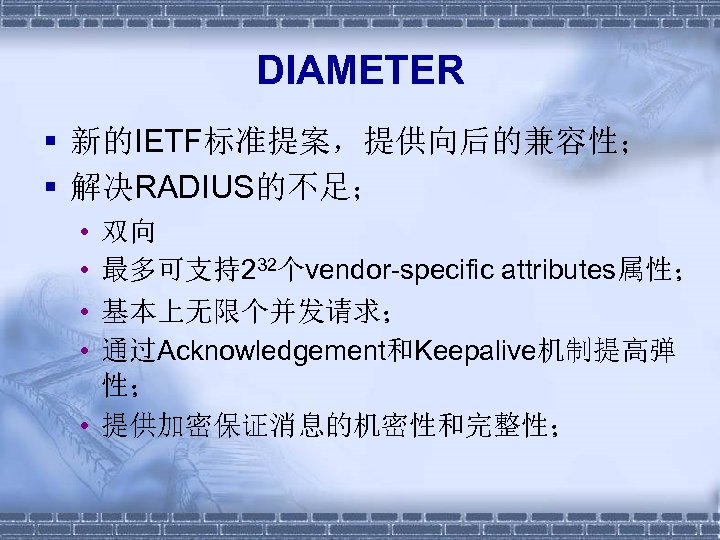
DIAMETER § 新的IETF标准提案,提供向后的兼容性; § 解决RADIUS的不足; • • 双向 最多可支持232个vendor-specific attributes属性; 基本上无限个并发请求; 通过Acknowledgement和Keepalive机制提高弹 性; • 提供加密保证消息的机密性和完整性;
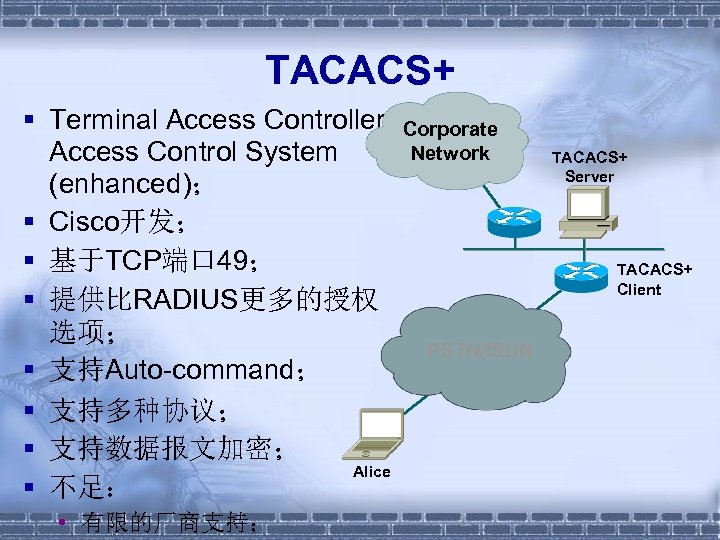
TACACS+ § Terminal Access Controller Access Control System (enhanced); § Cisco开发; § 基于TCP端口 49; § 提供比RADIUS更多的授权 选项; § 支持Auto-command; § 支持多种协议; § 支持数据报文加密; Alice § 不足: • 有限的厂商支持; Corporate Network TACACS+ Server TACACS+ Client PSTN/ISDN
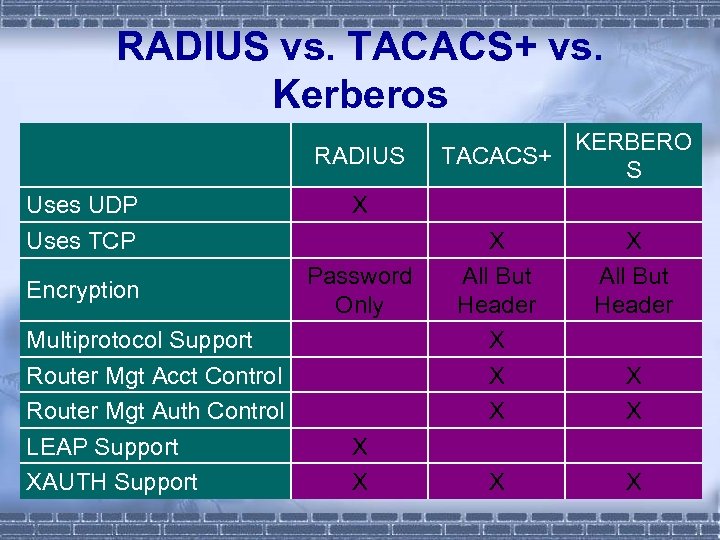
RADIUS vs. TACACS+ vs. Kerberos RADIUS Uses UDP Uses TCP Encryption Multiprotocol Support Router Mgt Acct Control Router Mgt Auth Control LEAP Support XAUTH Support TACACS+ KERBERO S X Password Only X X X All But Header X X X X

四. 主要网络安全协议和机制
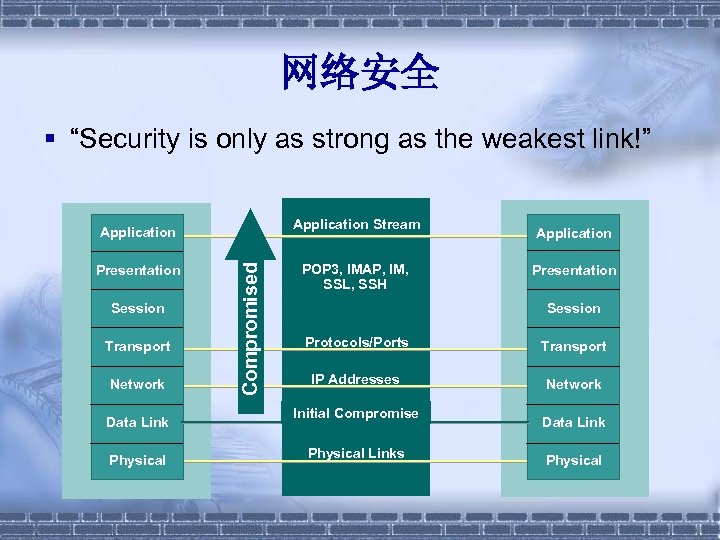
网络安全 § “Security is only as strong as the weakest link!” Application Stream Presentation Session Transport Network Data Link Physical Compromised Application POP 3, IMAP, IM, SSL, SSH Application Presentation Session Protocols/Ports Transport IP Addresses Network Initial Compromise MAC Addresses Physical Links Data Link Physical
数据链路层安全 § § § VLAN Hopping攻击; MAC/IP欺骗攻击; DHCP服务器攻击; CAM表溢出攻击; Spanning Tree攻击; ARP攻击;
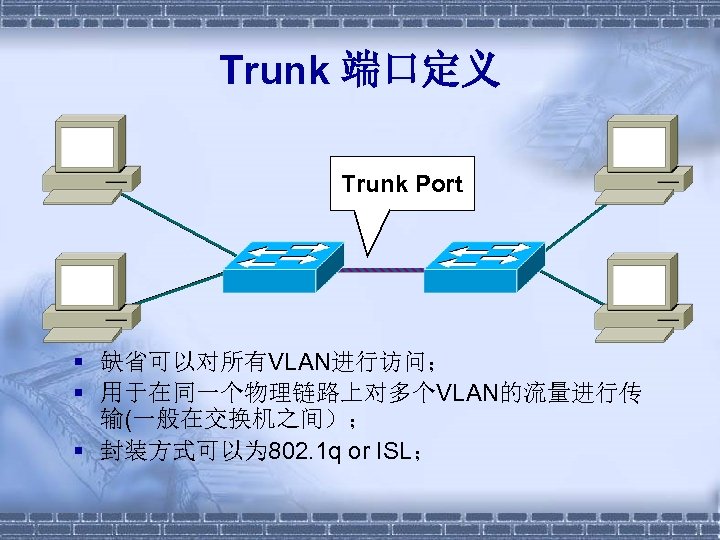
Trunk 端口定义 Trunk Port § 缺省可以对所有VLAN进行访问; § 用于在同一个物理链路上对多个VLAN的流量进行传 输(一般在交换机之间); § 封装方式可以为 802. 1 q or ISL;
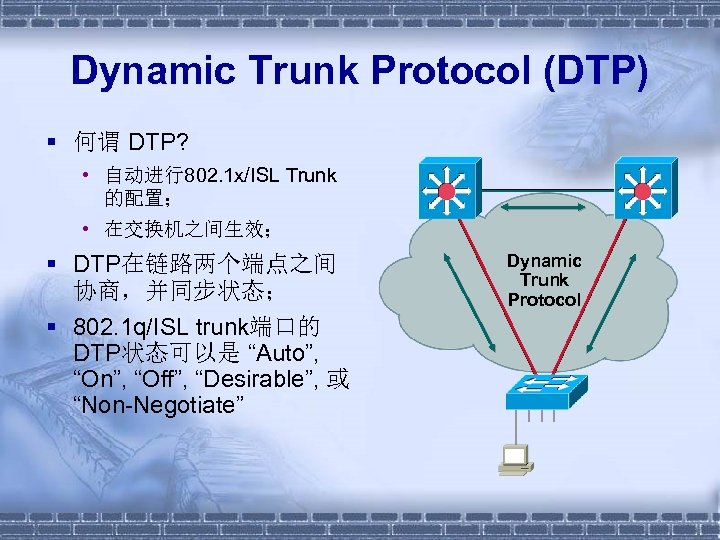
Dynamic Trunk Protocol (DTP) § 何谓 DTP? • 自动进行802. 1 x/ISL Trunk 的配置; • 在交换机之间生效; § DTP在链路两个端点之间 协商,并同步状态; § 802. 1 q/ISL trunk端口的 DTP状态可以是 “Auto”, “On”, “Off”, “Desirable”, 或 “Non-Negotiate” Dynamic Trunk Protocol
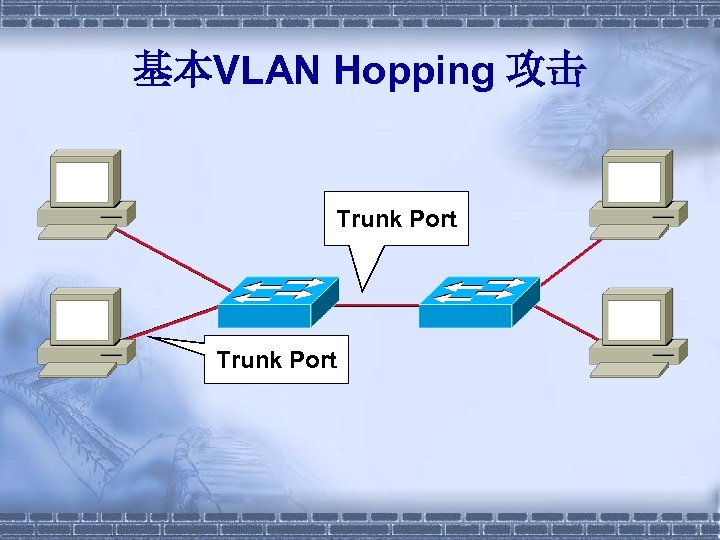
基本VLAN Hopping 攻击 Trunk Port
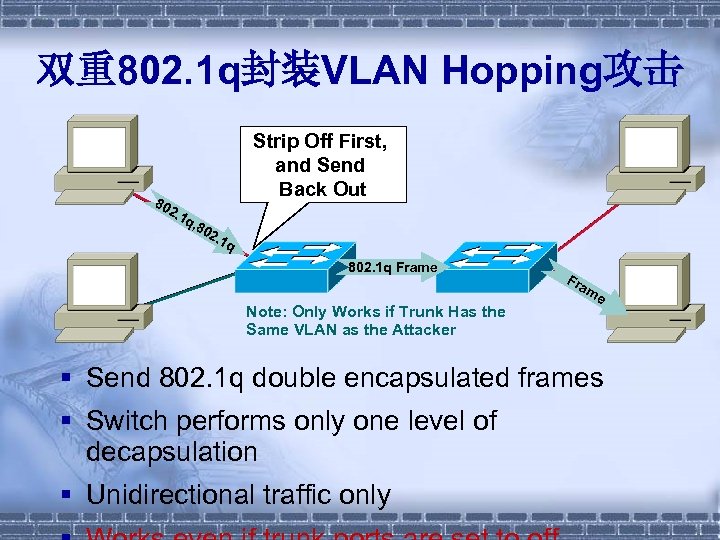
双重802. 1 q封装VLAN Hopping攻击 80 Strip Off First, and Send Back Out 2. 1 q, 8 02. 1 q 802. 1 q Frame Note: Only Works if Trunk Has the Same VLAN as the Attacker Fr am e § Send 802. 1 q double encapsulated frames § Switch performs only one level of decapsulation § Unidirectional traffic only
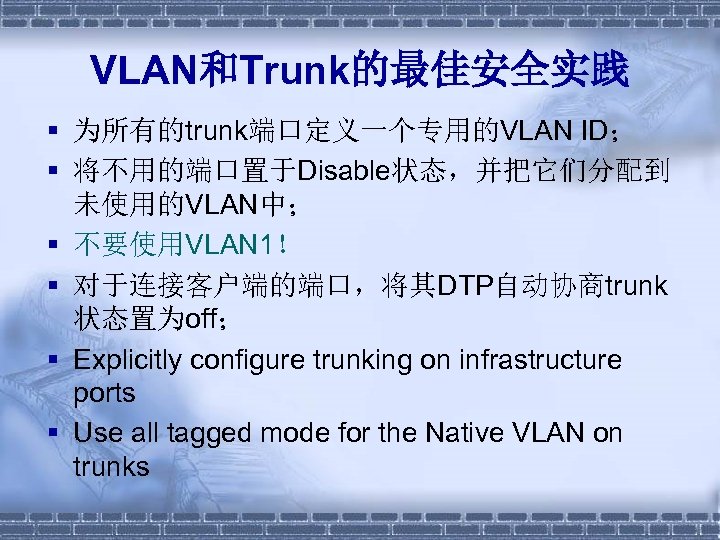
VLAN和Trunk的最佳安全实践 § 为所有的trunk端口定义一个专用的VLAN ID; § 将不用的端口置于Disable状态,并把它们分配到 未使用的VLAN中; § 不要使用VLAN 1! § 对于连接客户端的端口,将其DTP自动协商trunk 状态置为off; § Explicitly configure trunking on infrastructure ports § Use all tagged mode for the Native VLAN on trunks
数据链路层安全 § § § VLAN Hopping攻击; MAC/IP欺骗攻击; DHCP服务器攻击; CAM表溢出攻击; Spanning Tree攻击; ARP攻击;
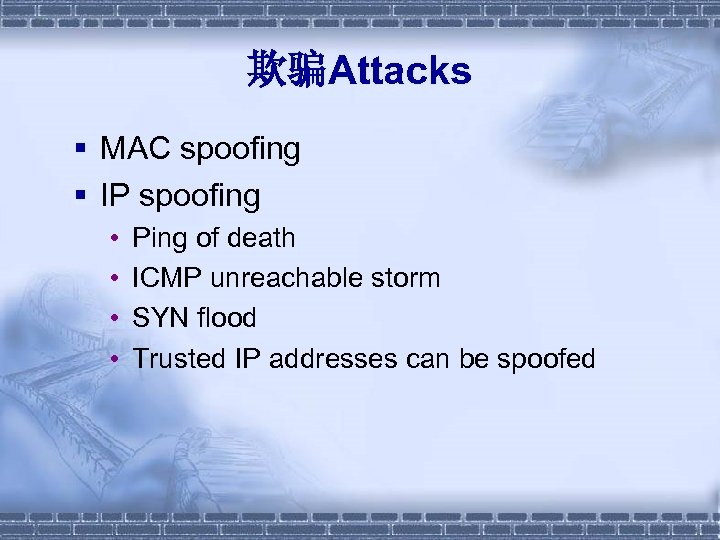
欺骗Attacks § MAC spoofing § IP spoofing • • Ping of death ICMP unreachable storm SYN flood Trusted IP addresses can be spoofed
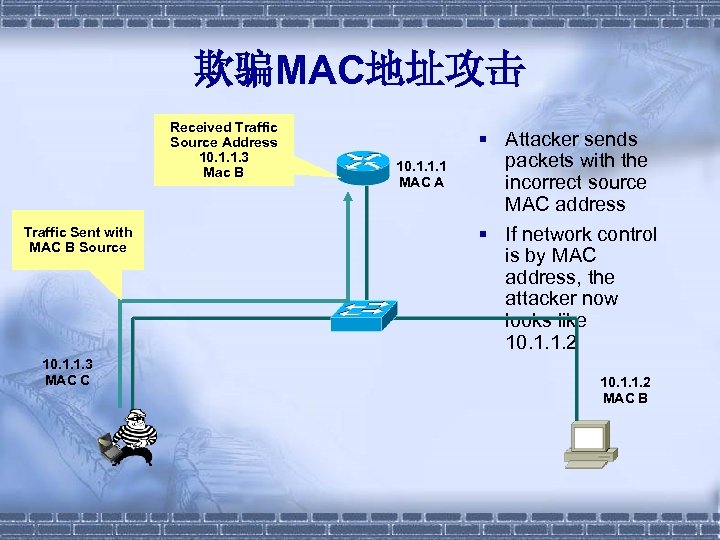
欺骗MAC地址攻击 Received Traffic Source Address 10. 1. 1. 3 Mac B Traffic Sent with MAC B Source 10. 1. 1. 3 MAC C 10. 1. 1. 1 MAC A § Attacker sends packets with the incorrect source MAC address § If network control is by MAC address, the attacker now looks like 10. 1. 1. 2 MAC B
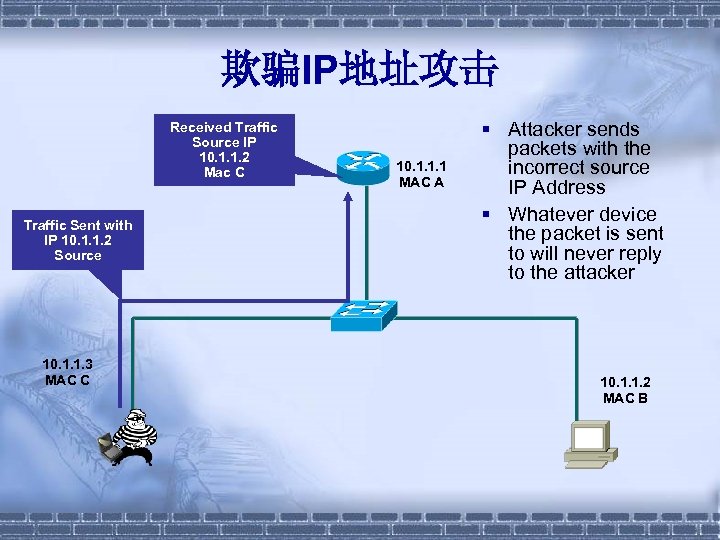
欺骗IP地址攻击 Received Traffic Source IP 10. 1. 1. 2 Mac C Traffic Sent with IP 10. 1. 1. 2 Source 10. 1. 1. 3 MAC C 10. 1. 1. 1 MAC A § Attacker sends packets with the incorrect source IP Address § Whatever device the packet is sent to will never reply to the attacker 10. 1. 1. 2 MAC B
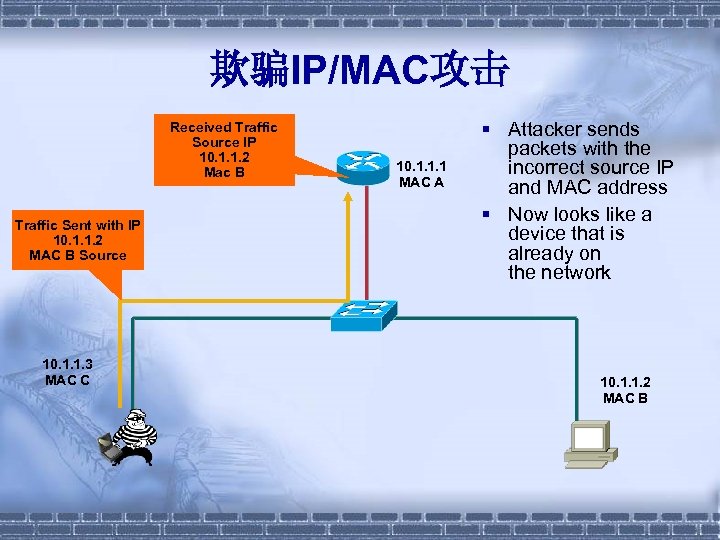
欺骗IP/MAC攻击 Received Traffic Source IP 10. 1. 1. 2 Mac B Traffic Sent with IP 10. 1. 1. 2 MAC B Source 10. 1. 1. 3 MAC C 10. 1. 1. 1 MAC A § Attacker sends packets with the incorrect source IP and MAC address § Now looks like a device that is already on the network 10. 1. 1. 2 MAC B
数据链路层安全 § § § VLAN Hopping攻击; MAC/IP欺骗攻击; DHCP服务器攻击; CAM表溢出攻击; Spanning Tree攻击; ARP攻击;
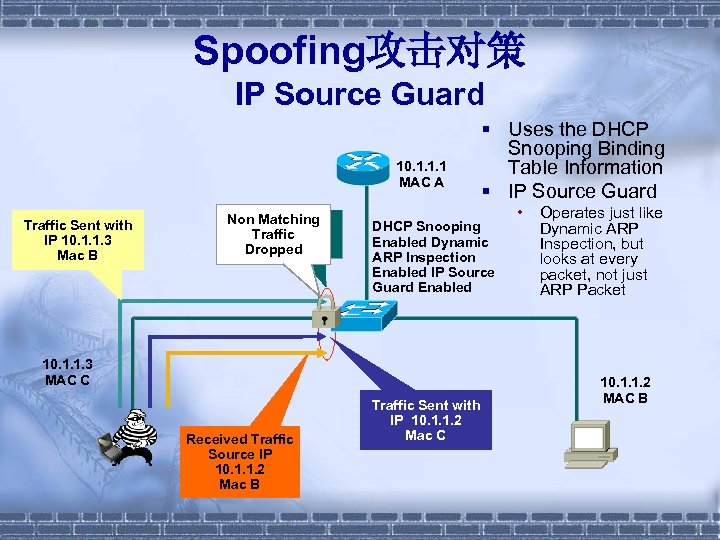
Spoofing攻击对策 IP Source Guard 10. 1. 1. 1 MAC A Traffic Sent with IP 10. 1. 1. 3 Mac B Is This Is My Non Matching Traffic Binding NO! Dropped Table? DHCP Snooping Enabled Dynamic ARP Inspection Enabled IP Source Guard Enabled 10. 1. 1. 3 MAC C Received Traffic Source IP 10. 1. 1. 2 Mac B § Uses the DHCP Snooping Binding Table Information § IP Source Guard Traffic Sent with IP 10. 1. 1. 2 Mac C • Operates just like Dynamic ARP Inspection, but looks at every packet, not just ARP Packet 10. 1. 1. 2 MAC B
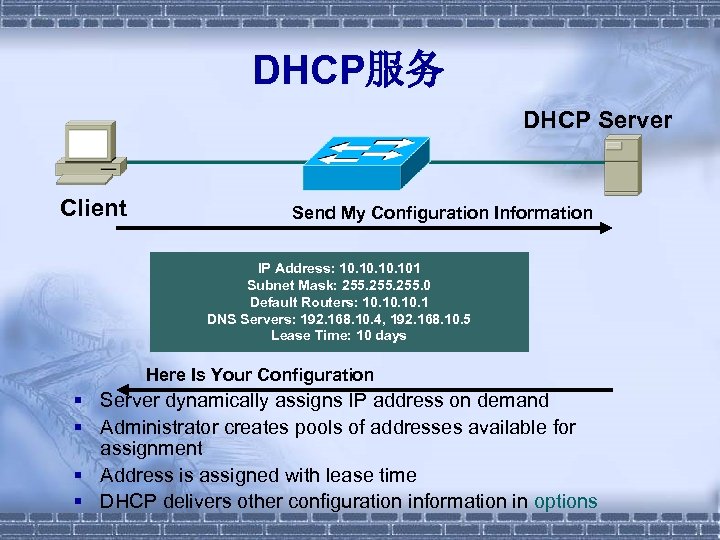
DHCP服务 DHCP Server Client Send My Configuration Information IP Address: 10. 10. 101 Subnet Mask: 255. 0 Default Routers: 10. 10. 1 DNS Servers: 192. 168. 10. 4, 192. 168. 10. 5 Lease Time: 10 days Here Is Your Configuration § Server dynamically assigns IP address on demand § Administrator creates pools of addresses available for assignment § Address is assigned with lease time § DHCP delivers other configuration information in options
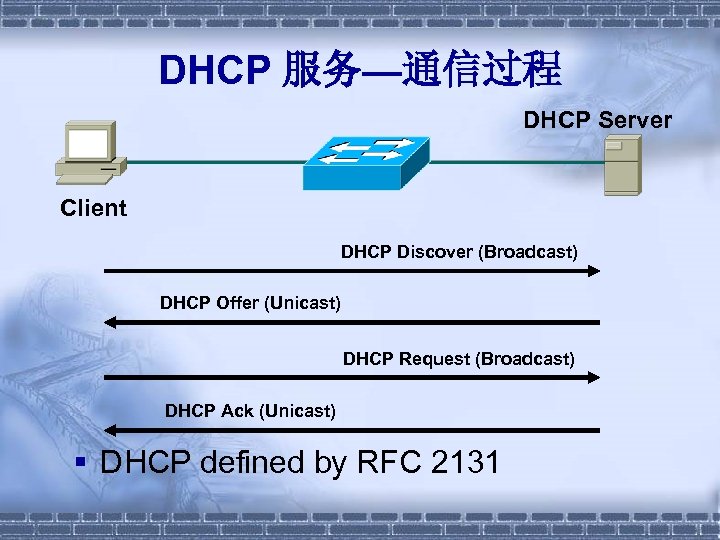
DHCP 服务—通信过程 DHCP Server Client DHCP Discover (Broadcast) DHCP Offer (Unicast) DHCP Request (Broadcast) DHCP Ack (Unicast) § DHCP defined by RFC 2131
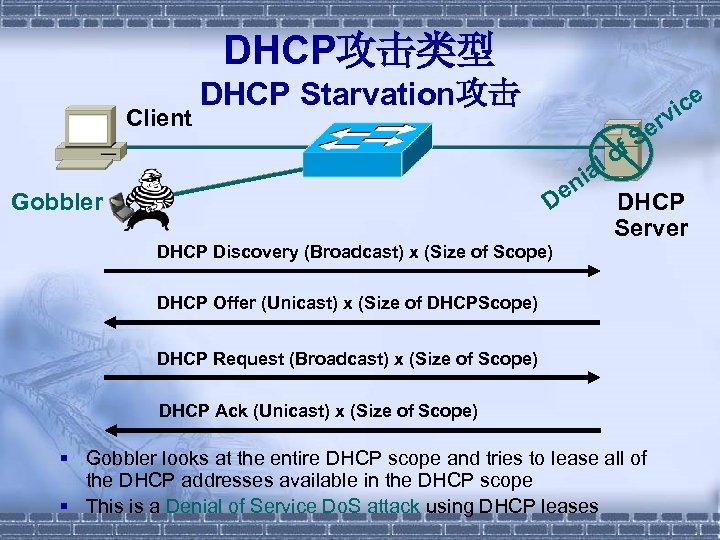
DHCP攻击类型 Client DHCP Starvation攻击 ice v er f. S lo a ni e Gobbler D DHCP Server DHCP Discovery (Broadcast) x (Size of Scope) DHCP Offer (Unicast) x (Size of DHCPScope) DHCP Request (Broadcast) x (Size of Scope) DHCP Ack (Unicast) x (Size of Scope) § Gobbler looks at the entire DHCP scope and tries to lease all of the DHCP addresses available in the DHCP scope § This is a Denial of Service Do. S attack using DHCP leases
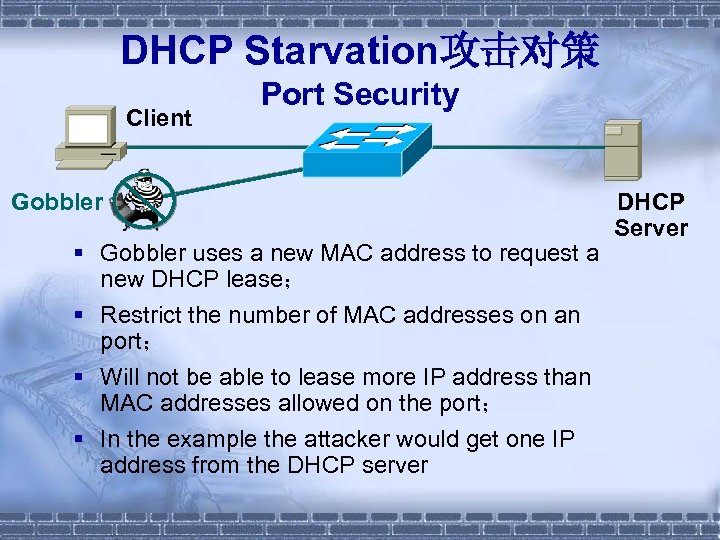
DHCP Starvation攻击对策 Client Port Security Gobbler § Gobbler uses a new MAC address to request a new DHCP lease; § Restrict the number of MAC addresses on an port; § Will not be able to lease more IP address than MAC addresses allowed on the port; § In the example the attacker would get one IP address from the DHCP server DHCP Server
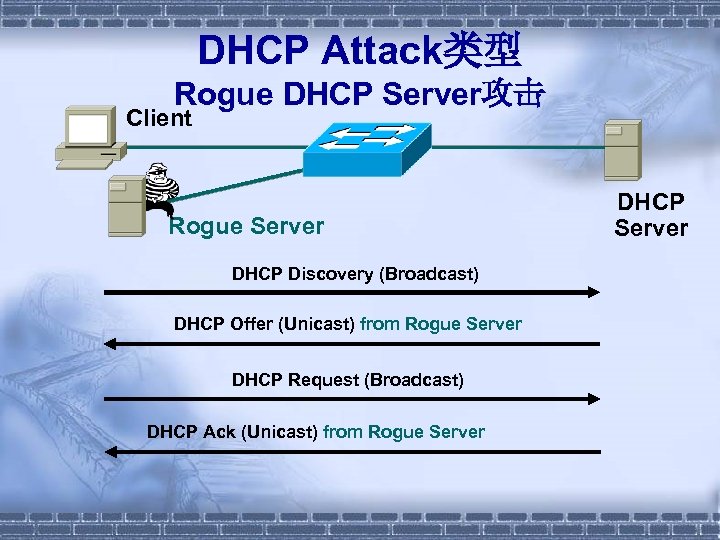
DHCP Attack类型 Rogue DHCP Server攻击 Client Rogue Server DHCP Discovery (Broadcast) DHCP Offer (Unicast) from Rogue Server DHCP Request (Broadcast) DHCP Ack (Unicast) from Rogue Server DHCP Server
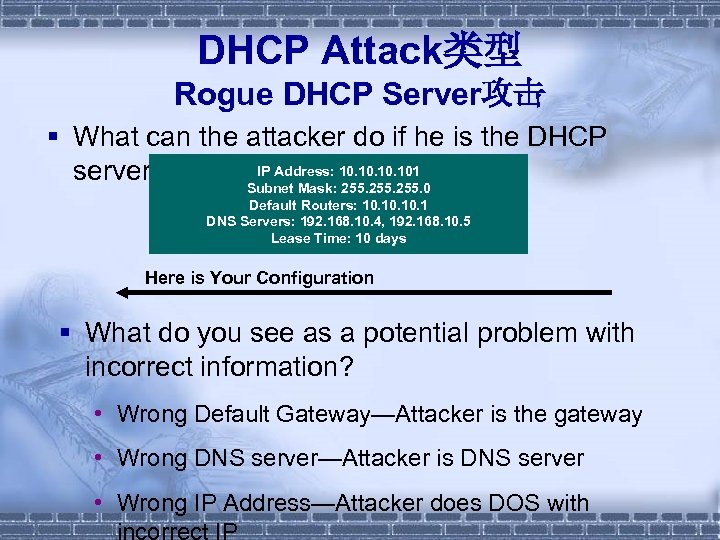
DHCP Attack类型 Rogue DHCP Server攻击 § What can the attacker do if he is the DHCP IP Address: 10. 10. 101 server? Subnet Mask: 255. 0 Default Routers: 10. 10. 1 DNS Servers: 192. 168. 10. 4, 192. 168. 10. 5 Lease Time: 10 days Here is Your Configuration § What do you see as a potential problem with incorrect information? • Wrong Default Gateway—Attacker is the gateway • Wrong DNS server—Attacker is DNS server • Wrong IP Address—Attacker does DOS with incorrect IP
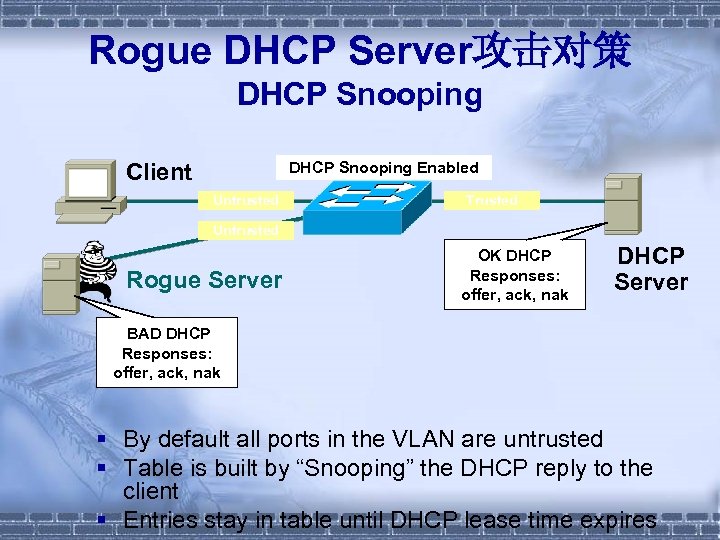
Rogue DHCP Server攻击对策 DHCP Snooping Client DHCP Snooping Enabled Untrusted Trusted Untrusted Rogue Server OK DHCP Responses: offer, ack, nak DHCP Server BAD DHCP Responses: offer, ack, nak § By default all ports in the VLAN are untrusted § Table is built by “Snooping” the DHCP reply to the client § Entries stay in table until DHCP lease time expires
数据链路层安全 § § § VLAN Hopping攻击; MAC/IP欺骗攻击; DHCP服务器攻击; CAM表溢出攻击; Spanning Tree攻击; ARP攻击;
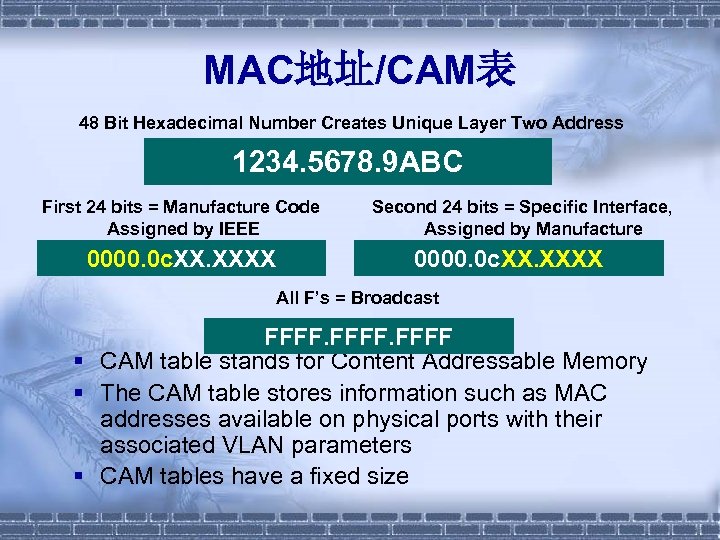
MAC地址/CAM表 48 Bit Hexadecimal Number Creates Unique Layer Two Address 1234. 5678. 9 ABC First 24 bits = Manufacture Code Assigned by IEEE 0000. 0 c. XXXX Second 24 bits = Specific Interface, Assigned by Manufacture 0000. 0 c. XXXX All F’s = Broadcast FFFF § CAM table stands for Content Addressable Memory § The CAM table stores information such as MAC addresses available on physical ports with their associated VLAN parameters § CAM tables have a fixed size
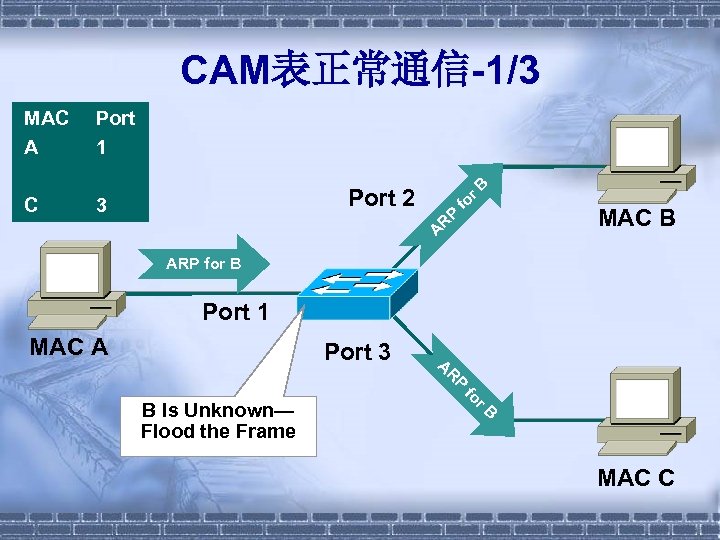
CAM表正常通信-1/3 3 fo Port 2 MAC B P C r. B Port 1 A R MAC A ARP for B Port 1 MAC A Port 3 R A P r. B fo B Is Unknown— Flood the Frame MAC C
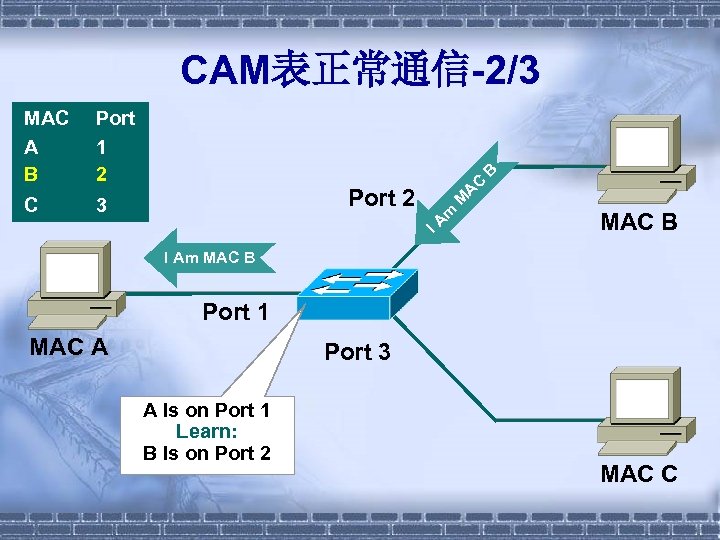
CAM表正常通信-2/3 3 C M A Port 2 m C B Port 1 2 IA MAC A B MAC B I Am MAC B Port 1 MAC A Port 3 A Is on Port 1 Learn: B Is on Port 2 MAC C
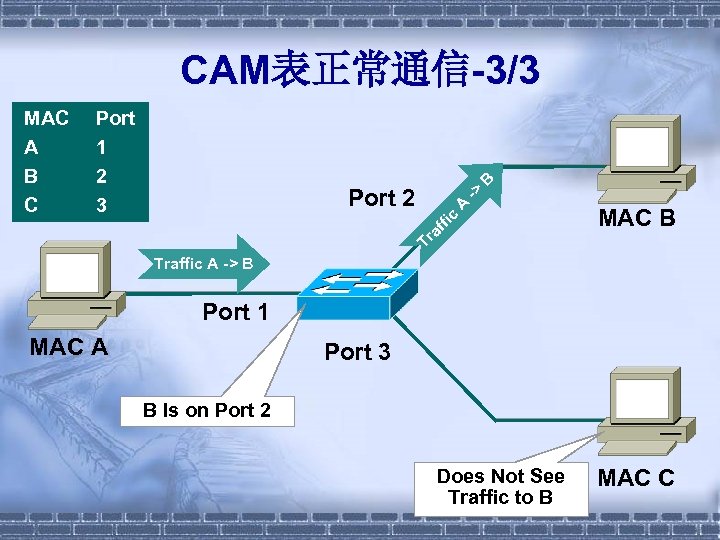
Port 1 2 3 fic A -> Port 2 MAC B Tr af MAC A B CAM表正常通信-3/3 Traffic A -> B Port 1 MAC A Port 3 B Is on Port 2 Does Not See Traffic to B MAC C
CAM表溢出-1/3 § Macof tool since 1999 • About 100 lines of perl • Included in “dsniff” § Attack successful by exploiting the size limit on CAM tables
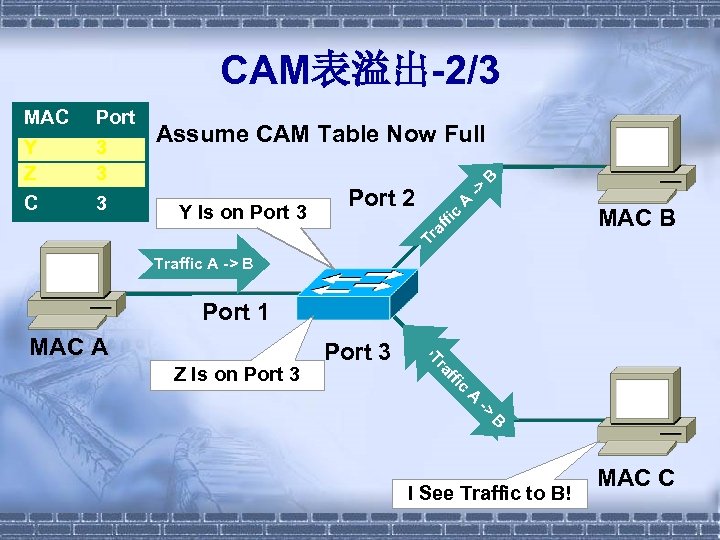
CAM表溢出-2/3 B Assume CAM Table Now Full A -> Port 2 MAC B c Y Is on Port 3 ffi Port 1 3 3 2 3 Tr a MAC A Y Z B C Traffic A -> B Port 1 Z Is on Port 3 Z > CAY CA ic M ff. A M m ra TA Im IA MAC A B I See Traffic to B! MAC C
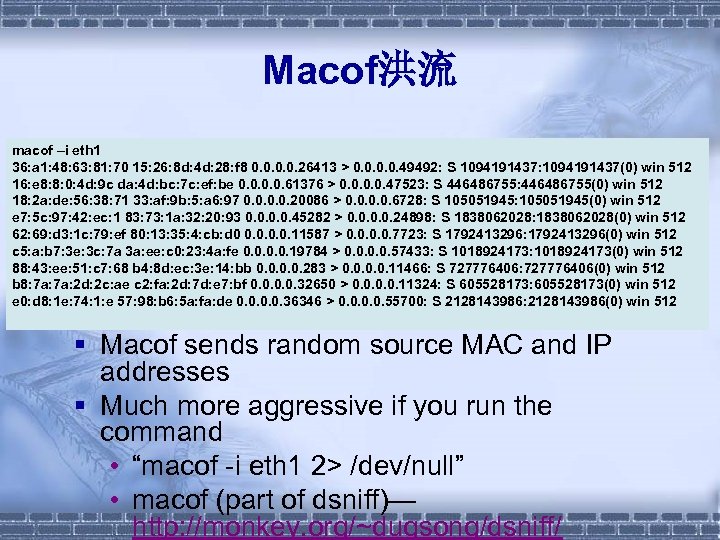
Macof洪流 macof –i eth 1 36: a 1: 48: 63: 81: 70 15: 26: 8 d: 4 d: 28: f 8 0. 0. 26413 > 0. 0. 49492: S 1094191437: 1094191437(0) win 512 16: e 8: 8: 0: 4 d: 9 c da: 4 d: bc: 7 c: ef: be 0. 0. 61376 > 0. 0. 47523: S 446486755: 446486755(0) win 512 18: 2 a: de: 56: 38: 71 33: af: 9 b: 5: a 6: 97 0. 0. 20086 > 0. 0. 6728: S 105051945: 105051945(0) win 512 e 7: 5 c: 97: 42: ec: 1 83: 73: 1 a: 32: 20: 93 0. 0. 45282 > 0. 0. 24898: S 1838062028: 1838062028(0) win 512 62: 69: d 3: 1 c: 79: ef 80: 13: 35: 4: cb: d 0 0. 0. 11587 > 0. 0. 7723: S 1792413296: 1792413296(0) win 512 c 5: a: b 7: 3 e: 3 c: 7 a 3 a: ee: c 0: 23: 4 a: fe 0. 0. 19784 > 0. 0. 57433: S 1018924173: 1018924173(0) win 512 88: 43: ee: 51: c 7: 68 b 4: 8 d: ec: 3 e: 14: bb 0. 0. 283 > 0. 0. 11466: S 727776406: 727776406(0) win 512 b 8: 7 a: 2 d: 2 c: ae c 2: fa: 2 d: 7 d: e 7: bf 0. 0. 32650 > 0. 0. 11324: S 605528173: 605528173(0) win 512 e 0: d 8: 1 e: 74: 1: e 57: 98: b 6: 5 a: fa: de 0. 0. 36346 > 0. 0. 55700: S 2128143986: 2128143986(0) win 512 § Macof sends random source MAC and IP addresses § Much more aggressive if you run the command • “macof -i eth 1 2> /dev/null” • macof (part of dsniff)— http: //monkey. org/~dugsong/dsniff/
CAM表满了! § Each switch has a limit on CAM tables; § Once the CAM table on the switch is full, traffic without a CAM entry is flooded out every port on that VLAN § This will turn a VLAN on a switch basically into a hub; § This attack will also fill the CAM tables of adjacent switches; 10. 1. 1. 22 -> (broadcast) ARP C Who is 10. 1. 1. 1, 10. 1. 1. 1 ? 10. 1. 1. 22 -> (broadcast) ARP C Who is 10. 1. 1. 19, 10. 1. 1. 19 ? 10. 1. 1. 26 -> 10. 1. 1. 25 ICMP Echo request (ID: 256 Sequence number: 7424) OOPS 10. 1. 1. 25 -> 10. 1. 1. 26 ICMP Echo reply (ID: 256 Sequence number: 7424) OOPS
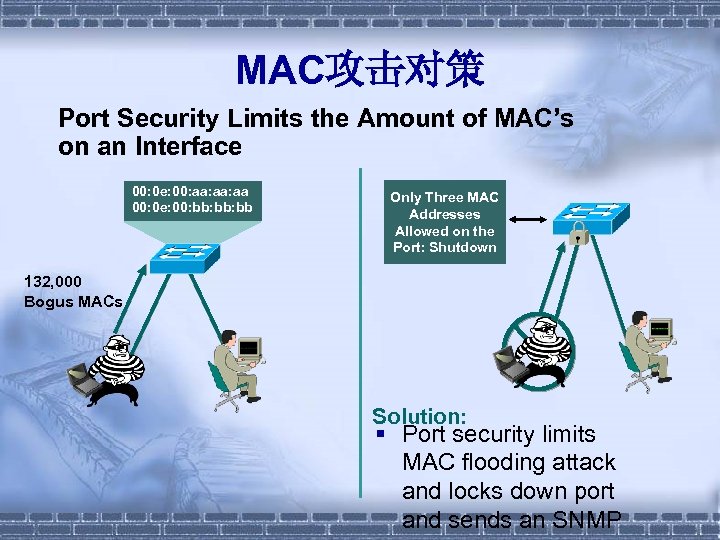
MAC攻击对策 Port Security Limits the Amount of MAC’s on an Interface 00: 0 e: 00: aa: aa 00: 0 e: 00: bb: bb Only Three MAC Addresses Allowed on the Port: Shutdown 132, 000 Bogus MACs Solution: § Port security limits MAC flooding attack and locks down port and sends an SNMP
数据链路层安全 § § § VLAN Hopping攻击; MAC/IP欺骗攻击; DHCP服务器攻击; CAM表溢出攻击; Spanning Tree攻击; ARP攻击;
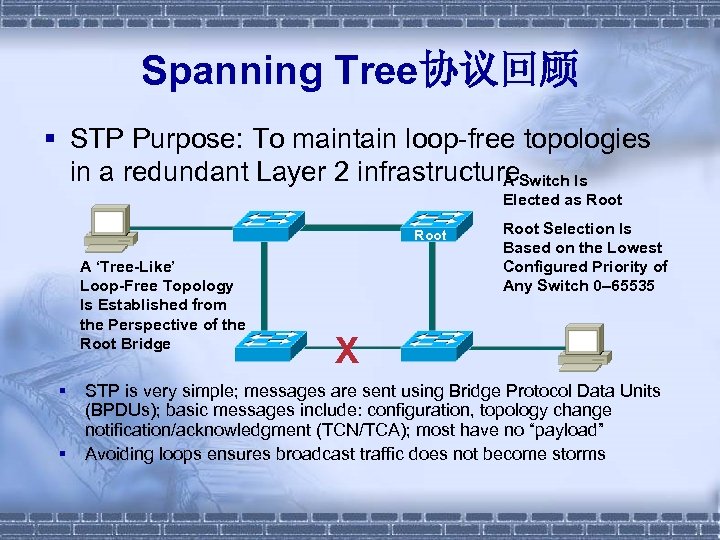
Spanning Tree协议回顾 § STP Purpose: To maintain loop-free topologies in a redundant Layer 2 infrastructure. Switch Is A Elected as Root A ‘Tree-Like’ Loop-Free Topology Is Established from the Perspective of the Root Bridge § § Root Selection Is Based on the Lowest Configured Priority of Any Switch 0– 65535 X STP is very simple; messages are sent using Bridge Protocol Data Units (BPDUs); basic messages include: configuration, topology change notification/acknowledgment (TCN/TCA); most have no “payload” Avoiding loops ensures broadcast traffic does not become storms
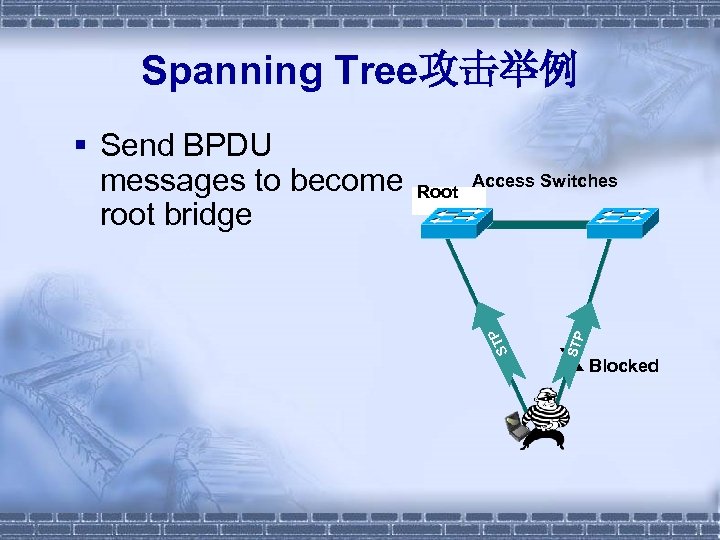
Spanning Tree攻击举例 STP Access Switches Root P ST § Send BPDU messages to become root bridge X Blocked
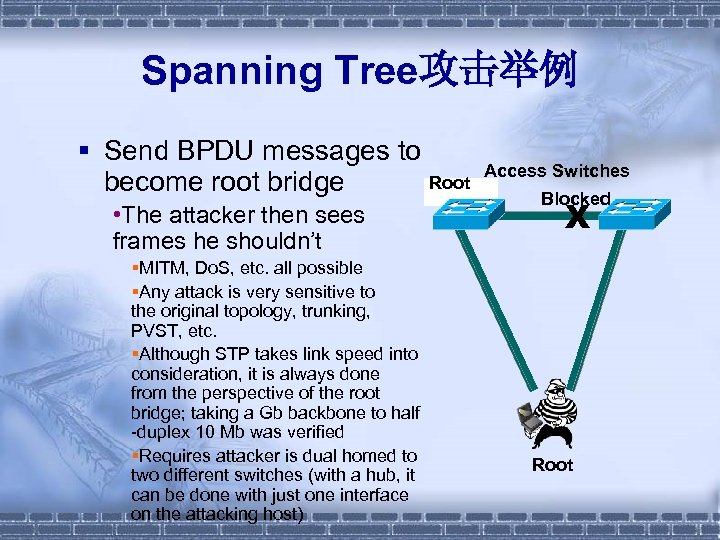
Spanning Tree攻击举例 § Send BPDU messages to Access Switches Root become root bridge Root • The attacker then sees frames he shouldn’t §MITM, Do. S, etc. all possible §Any attack is very sensitive to the original topology, trunking, PVST, etc. §Although STP takes link speed into consideration, it is always done from the perspective of the root bridge; taking a Gb backbone to half -duplex 10 Mb was verified §Requires attacker is dual homed to two different switches (with a hub, it can be done with just one interface on the attacking host) Blocked X Root
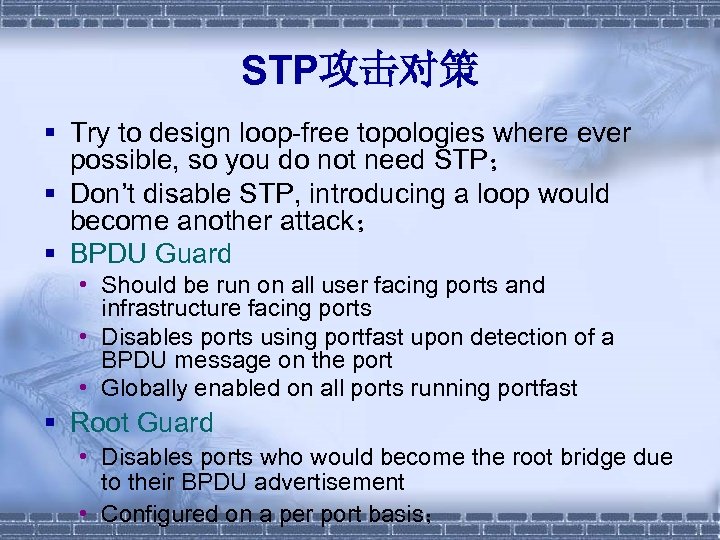
STP攻击对策 § Try to design loop-free topologies where ever possible, so you do not need STP; § Don’t disable STP, introducing a loop would become another attack; § BPDU Guard • Should be run on all user facing ports and infrastructure facing ports • Disables ports using portfast upon detection of a BPDU message on the port • Globally enabled on all ports running portfast § Root Guard • Disables ports who would become the root bridge due to their BPDU advertisement • Configured on a per port basis;
数据链路层安全 § § § VLAN Hopping攻击; MAC/IP欺骗攻击; DHCP服务器攻击; CAM表溢出攻击; Spanning Tree攻击; ARP攻击;
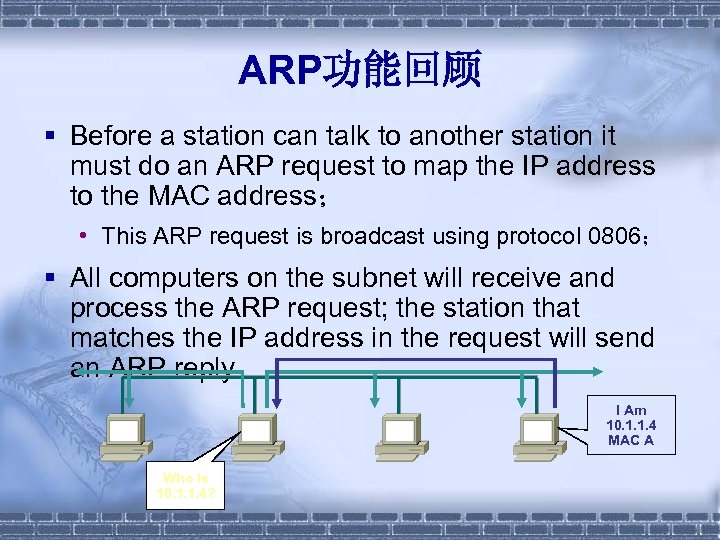
ARP功能回顾 § Before a station can talk to another station it must do an ARP request to map the IP address to the MAC address; • This ARP request is broadcast using protocol 0806; § All computers on the subnet will receive and process the ARP request; the station that matches the IP address in the request will send an ARP reply I Am 10. 1. 1. 4 MAC A Who Is 10. 1. 1. 4?
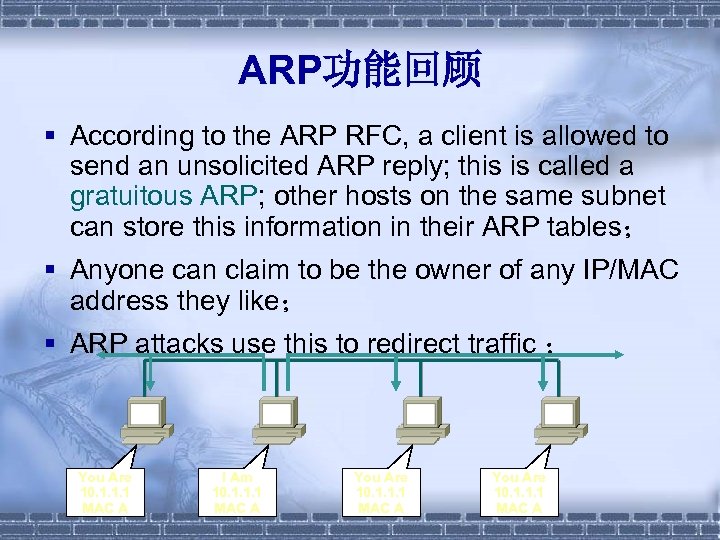
ARP功能回顾 § According to the ARP RFC, a client is allowed to send an unsolicited ARP reply; this is called a gratuitous ARP; other hosts on the same subnet can store this information in their ARP tables; § Anyone can claim to be the owner of any IP/MAC address they like; § ARP attacks use this to redirect traffic ; You Are 10. 1. 1. 1 MAC A I Am 10. 1. 1. 1 MAC A You Are 10. 1. 1. 1 MAC A
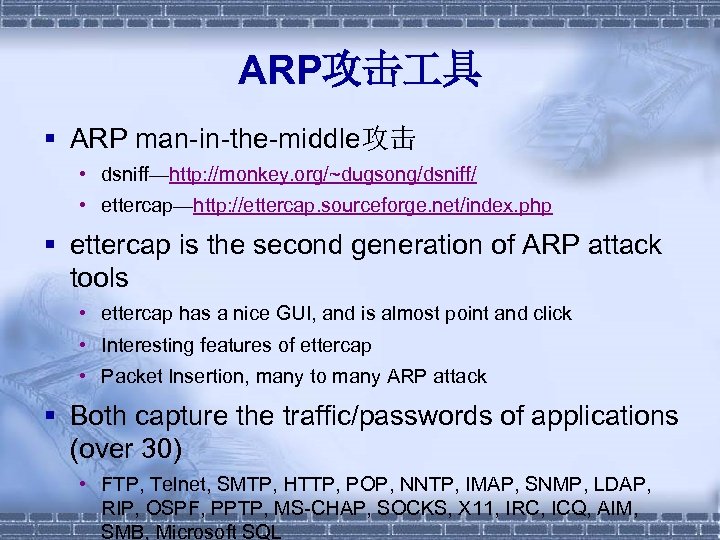
ARP攻击 具 § ARP man-in-the-middle攻击 • dsniff—http: //monkey. org/~dugsong/dsniff/ • ettercap—http: //ettercap. sourceforge. net/index. php § ettercap is the second generation of ARP attack tools • ettercap has a nice GUI, and is almost point and click • Interesting features of ettercap • Packet Insertion, many to many ARP attack § Both capture the traffic/passwords of applications (over 30) • FTP, Telnet, SMTP, HTTP, POP, NNTP, IMAP, SNMP, LDAP, RIP, OSPF, PPTP, MS-CHAP, SOCKS, X 11, IRC, ICQ, AIM, SMB, Microsoft SQL
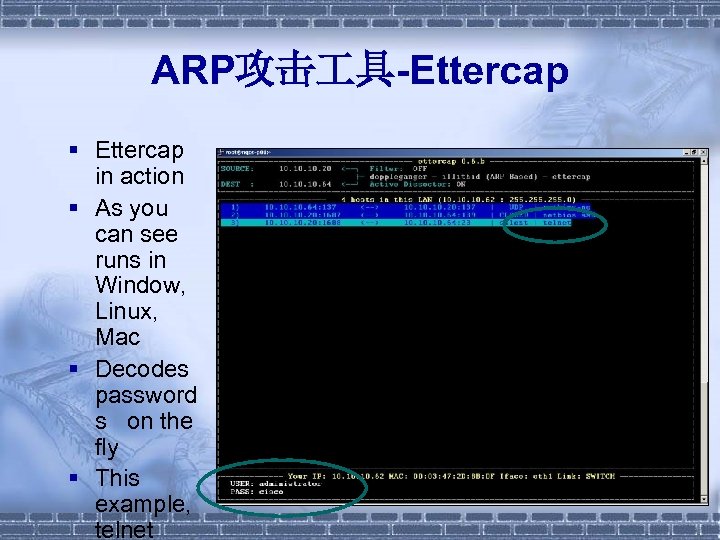
ARP攻击 具-Ettercap § Ettercap in action § As you can see runs in Window, Linux, Mac § Decodes password s on the fly § This example, telnet
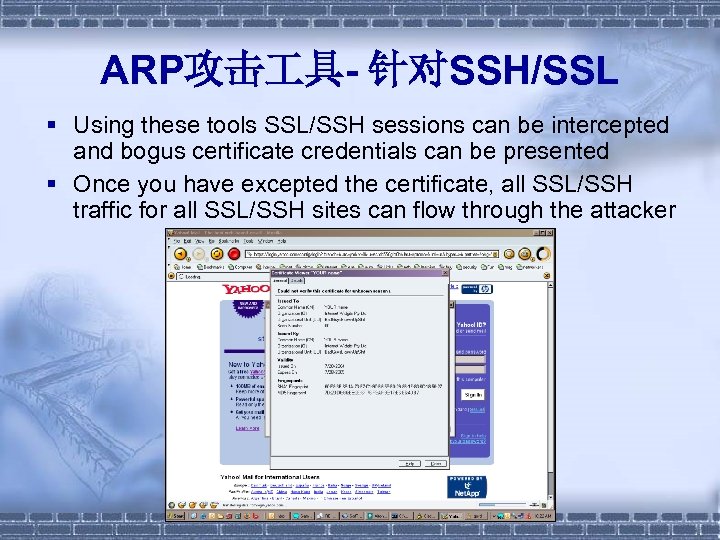
ARP攻击 具- 针对SSH/SSL § Using these tools SSL/SSH sessions can be intercepted and bogus certificate credentials can be presented § Once you have excepted the certificate, all SSL/SSH traffic for all SSL/SSH sites can flow through the attacker
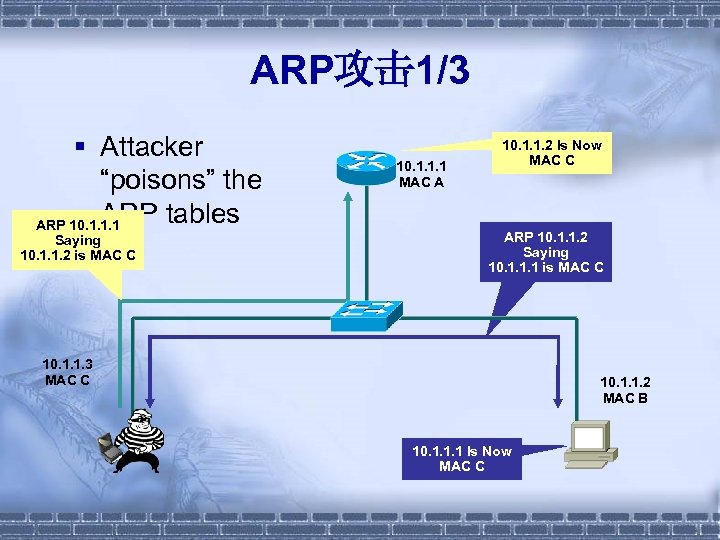
ARP攻击 1/3 § Attacker “poisons” the ARP tables ARP 10. 1. 1. 1 Saying 10. 1. 1. 2 is MAC C 10. 1. 1. 1 MAC A 10. 1. 1. 2 Is Now MAC C ARP 10. 1. 1. 2 Saying 10. 1. 1. 1 is MAC C 10. 1. 1. 3 MAC C 10. 1. 1. 2 MAC B 10. 1. 1. 1 Is Now MAC C
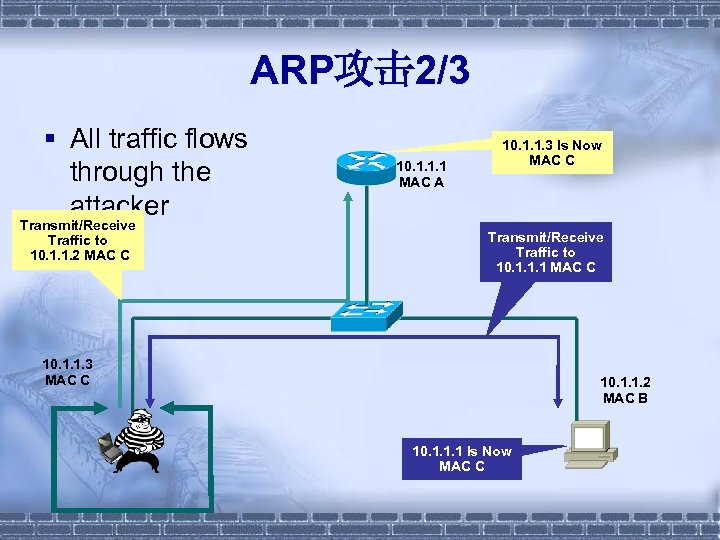
ARP攻击 2/3 § All traffic flows through the attacker Transmit/Receive Traffic to 10. 1. 1. 2 MAC C 10. 1. 1. 1 MAC A 10. 1. 1. 3 Is Now MAC C Transmit/Receive Traffic to 10. 1. 1. 1 MAC C 10. 1. 1. 3 MAC C 10. 1. 1. 2 MAC B 10. 1. 1. 1 Is Now MAC C
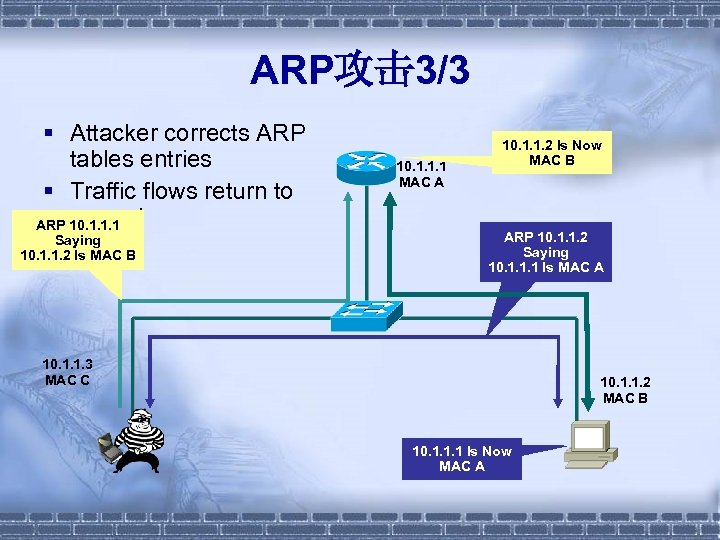
ARP攻击 3/3 § Attacker corrects ARP tables entries § Traffic flows return to normal ARP 10. 1. 1. 1 Saying 10. 1. 1. 2 Is MAC B 10. 1. 1. 1 MAC A 10. 1. 1. 2 Is Now MAC B ARP 10. 1. 1. 2 Saying 10. 1. 1. 1 Is MAC A 10. 1. 1. 3 MAC C 10. 1. 1. 2 MAC B 10. 1. 1. 1 Is Now MAC A
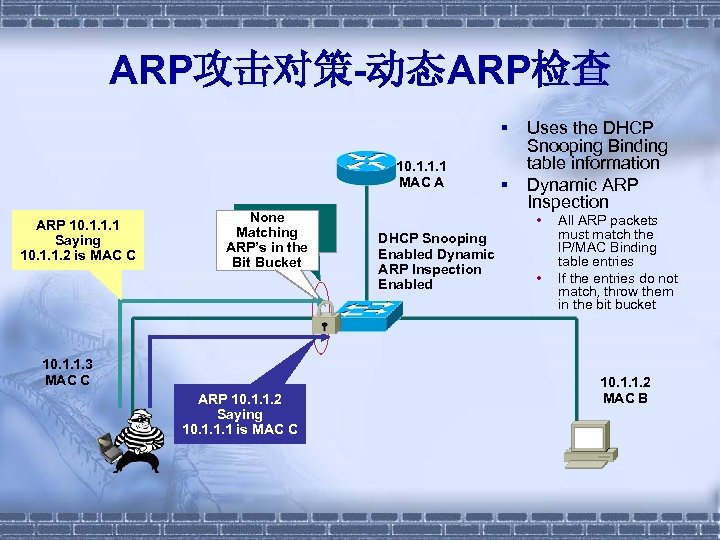
ARP攻击对策-动态ARP检查 § 10. 1. 1. 1 MAC A ARP 10. 1. 1. 1 Saying 10. 1. 1. 2 is MAC C Is This Is My None Binding NO! Matching Table? ARP’s in the Bit Bucket 10. 1. 1. 3 MAC C ARP 10. 1. 1. 2 Saying 10. 1. 1. 1 is MAC C § Uses the DHCP Snooping Binding table information Dynamic ARP Inspection • DHCP Snooping Enabled Dynamic ARP Inspection Enabled • All ARP packets must match the IP/MAC Binding table entries If the entries do not match, throw them in the bit bucket 10. 1. 1. 2 MAC B
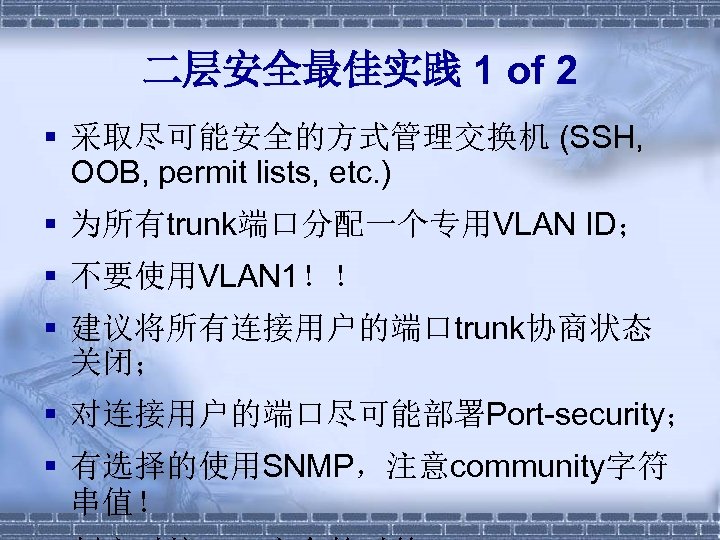
二层安全最佳实践 1 of 2 § 采取尽可能安全的方式管理交换机 (SSH, OOB, permit lists, etc. ) § 为所有trunk端口分配一个专用VLAN ID; § 不要使用VLAN 1!! § 建议将所有连接用户的端口trunk协商状态 关闭; § 对连接用户的端口尽可能部署Port-security; § 有选择的使用SNMP,注意community字符 串值!
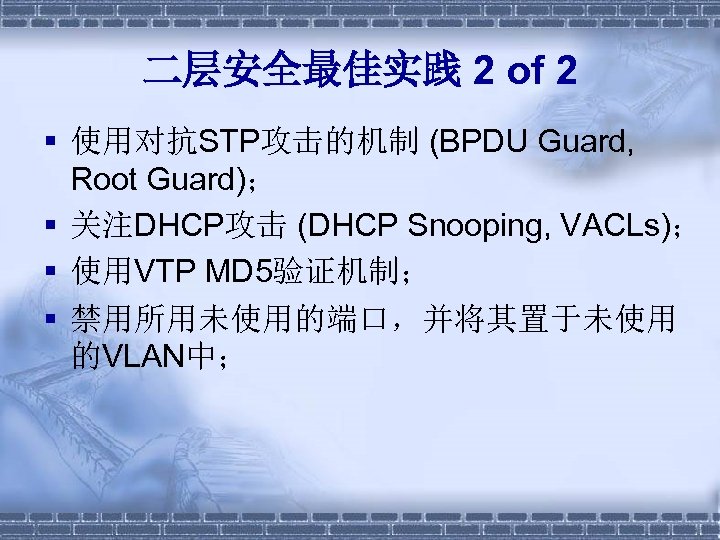
二层安全最佳实践 2 of 2 § 使用对抗STP攻击的机制 (BPDU Guard, Root Guard); § 关注DHCP攻击 (DHCP Snooping, VACLs); § 使用VTP MD 5验证机制; § 禁用所用未使用的端口,并将其置于未使用 的VLAN中;
网络层安全 § § § IPsec(略); PPTP (略); L 2 TP (略); 路由协议安全; NAT;
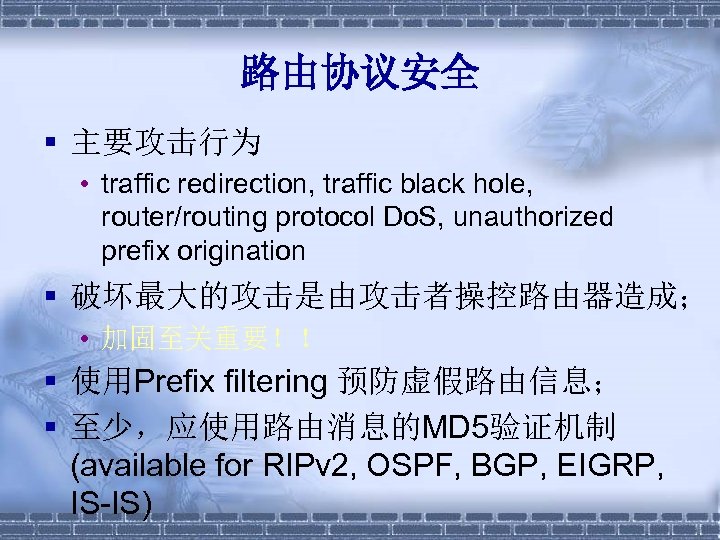
路由协议安全 § 主要攻击行为 • traffic redirection, traffic black hole, router/routing protocol Do. S, unauthorized prefix origination § 破坏最大的攻击是由攻击者操控路由器造成; • 加固至关重要!! § 使用Prefix filtering 预防虚假路由信息; § 至少,应使用路由消息的MD 5验证机制 (available for RIPv 2, OSPF, BGP, EIGRP, IS-IS)
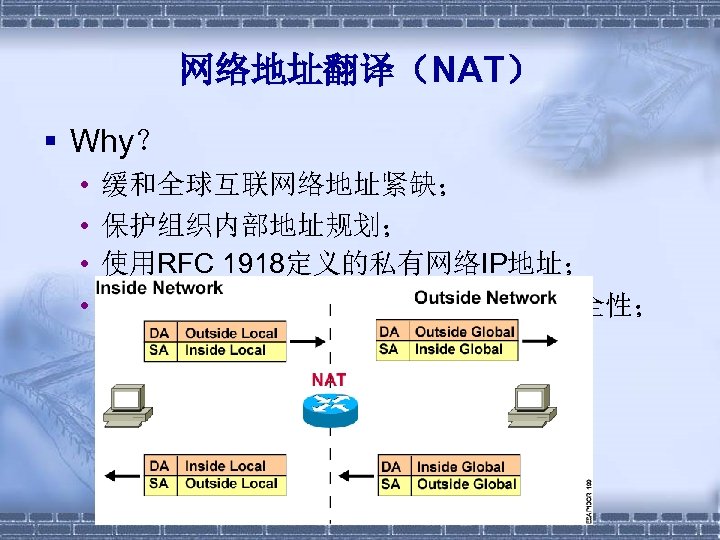
网络地址翻译(NAT) § Why? • • 缓和全球互联网络地址紧缺; 保护组织内部地址规划; 使用RFC 1918定义的私有网络IP地址; 另,通过隐藏内部网络拓扑结构增强安全性;
传输层安全 § SSL; § TLS; § SSH;
SSL § 由Netscape 通信公司于1994年开发,以保 护互联网上的安全交易 ; § 包括 • SSL Record Protocol; • SSL Handshake Protocol; § 提供 • Private; • Authentication; • Reliable;
TLS § IETF在SSL 3. 0基础上开发; § Transport Layer Security (TLS) protocol; § 包括两层; • TLS Record Protocol; § Private; § Reliable; • TLS Handshake Protocol; § The peer‘s identity can be authenticated using asymmetric cryptography; § The negotiation of a shared secret is secure; § The negotiation is reliable;
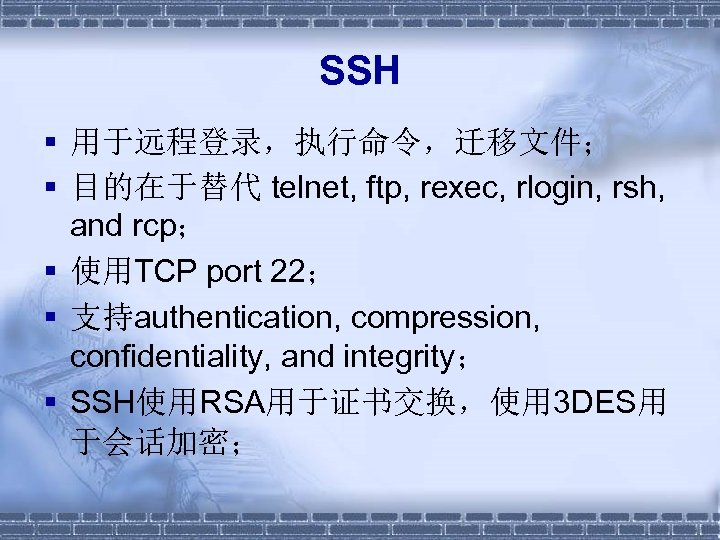
SSH § 用于远程登录,执行命令,迁移文件; § 目的在于替代 telnet, ftp, rexec, rlogin, rsh, and rcp; § 使用TCP port 22; § 支持authentication, compression, confidentiality, and integrity; § SSH使用RSA用于证书交换,使用 3 DES用 于会话加密;
应用层安全 § § § SET PEM S-HTTP Vs HTTPS MIME S/MIME PGP
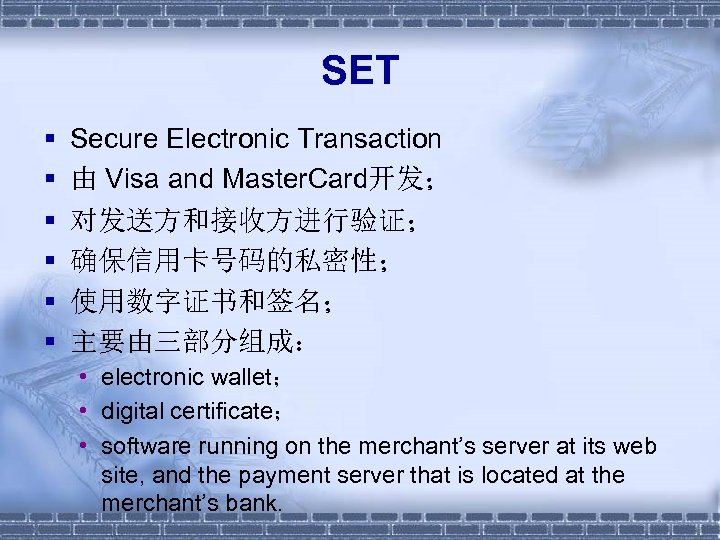
SET § § § Secure Electronic Transaction 由 Visa and Master. Card开发; 对发送方和接收方进行验证; 确保信用卡号码的私密性; 使用数字证书和签名; 主要由三部分组成: • electronic wallet; • digital certificate; • software running on the merchant’s server at its web site, and the payment server that is located at the merchant’s bank.
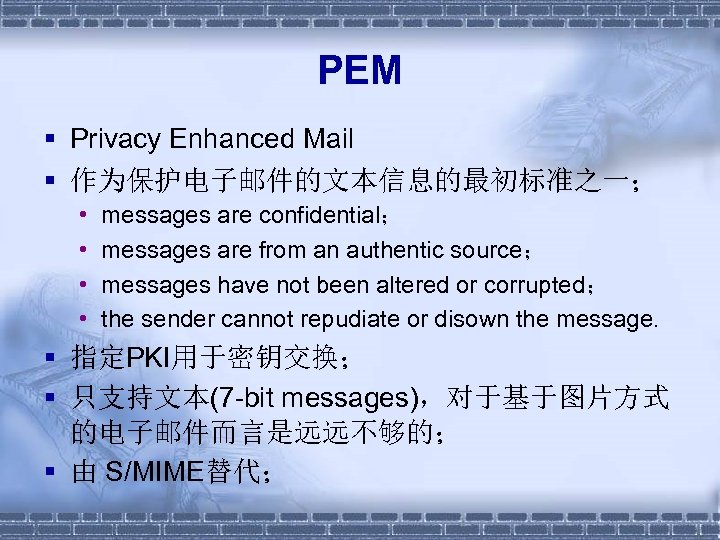
PEM § Privacy Enhanced Mail § 作为保护电子邮件的文本信息的最初标准之一; • • messages are confidential; messages are from an authentic source; messages have not been altered or corrupted; the sender cannot repudiate or disown the message. § 指定PKI用于密钥交换; § 只支持文本(7 -bit messages),对于基于图片方式 的电子邮件而言是远远不够的; § 由 S/MIME替代;
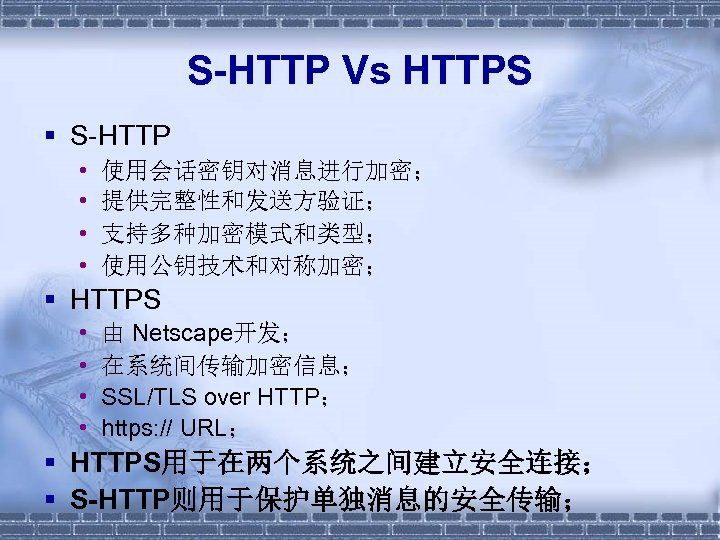
S-HTTP Vs HTTPS § S-HTTP • • 使用会话密钥对消息进行加密; 提供完整性和发送方验证; 支持多种加密模式和类型; 使用公钥技术和对称加密; § HTTPS • • 由 Netscape开发; 在系统间传输加密信息; SSL/TLS over HTTP; https: // URL; § HTTPS用于在两个系统之间建立安全连接; § S-HTTP则用于保护单独消息的安全传输;
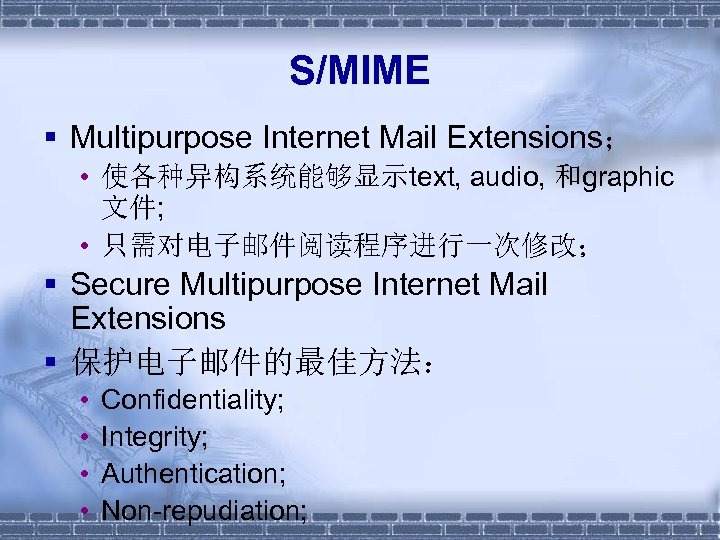
S/MIME § Multipurpose Internet Mail Extensions; • 使各种异构系统能够显示text, audio, 和graphic 文件; • 只需对电子邮件阅读程序进行一次修改; § Secure Multipurpose Internet Mail Extensions § 保护电子邮件的最佳方法: • • Confidentiality; Integrity; Authentication; Non-repudiation;
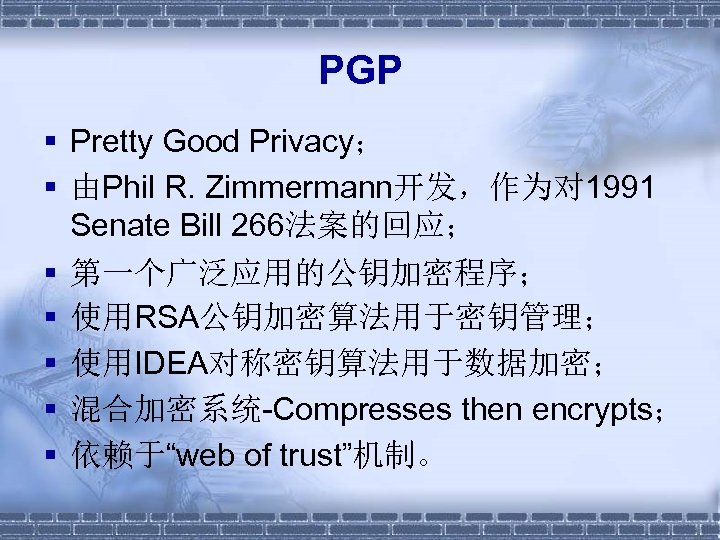
PGP § Pretty Good Privacy; § 由Phil R. Zimmermann开发,作为对 1991 Senate Bill 266法案的回应; § 第一个广泛应用的公钥加密程序; § 使用RSA公钥加密算法用于密钥管理; § 使用IDEA对称密钥算法用于数据加密; § 混合加密系统-Compresses then encrypts; § 依赖于“web of trust”机制。
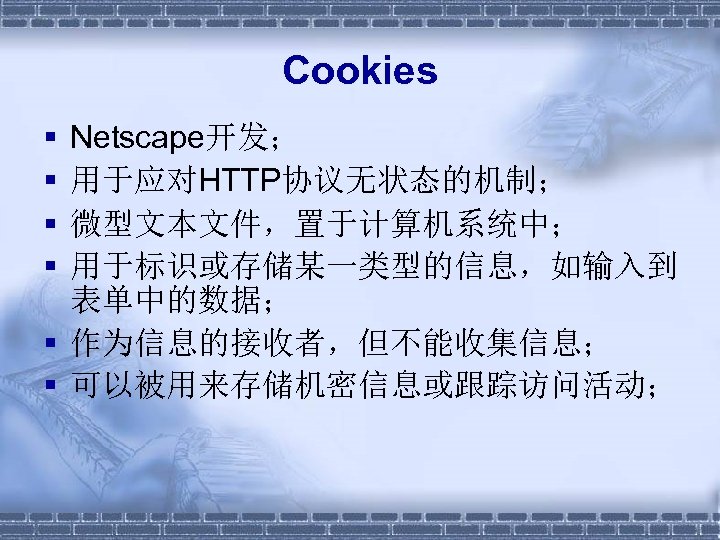
Cookies § § Netscape开发; 用于应对HTTP协议无状态的机制; 微型文本文件,置于计算机系统中; 用于标识或存储某一类型的信息,如输入到 表单中的数据; § 作为信息的接收者,但不能收集信息; § 可以被用来存储机密信息或跟踪访问活动;

http: //www. itsec. g ov. cn
7df58a3cf633969cce3d928bfa883eee.ppt