67ed8094c48dff062b88025d7efca10d.ppt
- Количество слайдов: 35
模型检验 1/36 高级软件 程 第八讲 模型检验 主要考虑如何发现设计缺陷! 1

模型检验 2/36 高级软件 程 内容 一、例子 二、模型检测概述 三、模型检测算法概览 四、模型检测 具 2
![模型检验 3/36 高级软件 程 一、例子 Needham-Schroeder 身份认证协议 通信过程可能被窃听!加密可以防止窃听!如何约定加密数字? 每人 有自己的标识:N 每人 公布自己的公钥: 只有N才能解开的消息: [****]N 模型检验 3/36 高级软件 程 一、例子 Needham-Schroeder 身份认证协议 通信过程可能被窃听!加密可以防止窃听!如何约定加密数字? 每人 有自己的标识:N 每人 公布自己的公钥: 只有N才能解开的消息: [****]N](https://present5.com/presentation/67ed8094c48dff062b88025d7efca10d/image-3.jpg)
模型检验 3/36 高级软件 程 一、例子 Needham-Schroeder 身份认证协议 通信过程可能被窃听!加密可以防止窃听!如何约定加密数字? 每人 有自己的标识:N 每人 公布自己的公钥: 只有N才能解开的消息: [****]N 每个对话过程 用一对数字对内容加密: S 1, S 2 每次对话前 需要首先建立这对数字 N [N, S 1]Z Z [S 1, S 2]N [S 2]Z 该协议于1978年被提出并得到广泛应用 3
![模型检验 4/36 高级软件 程 1996年,发现该协议存在设计缺陷: 攻击者可以伪装一方的身份 N [N, S 1]W W 开始伪装 [N, S 模型检验 4/36 高级软件 程 1996年,发现该协议存在设计缺陷: 攻击者可以伪装一方的身份 N [N, S 1]W W 开始伪装 [N, S](https://present5.com/presentation/67ed8094c48dff062b88025d7efca10d/image-4.jpg)
模型检验 4/36 高级软件 程 1996年,发现该协议存在设计缺陷: 攻击者可以伪装一方的身份 N [N, S 1]W W 开始伪装 [N, S 1]Z [S 1, S 2]N [S 2]W Z [S 2]Z 被欺骗! 不可信! 利用模型检测方法! 4
高级软件 程 模型检验 5/36 In 1992 Clarke and his students at CMU used SMV to verify the IEEE Future+ cache coherence protocol. • They found a number of previously undetected errors in the design of the protocol. • This was the first time that formal methods have been used to find errors in an IEEE standard. • Although the development of the protocol began in 1988, all previous attempts to validate it were based entirely on informal techniques. 5
高级软件 程 模型检验 6/36 In 1992 Dill and his students at Stanford used Murphito verify the cache coherence protocol of the IEEE Scalable Coherent Interface. • They found several errors, ranging from uninitialized variables to subtle logical errors. • The errors also existed in the complete protocol, although it had been extensively discussed, simulated, and even implemented. 6
高级软件 程 模型检验 7/36 In 1995 researchers from Bull and Verimag used LOTOS to describe the processors, memory controller, and bus Arbiter of the Power Scale multiprocessor architecture. • They identified four correctness requirements for proper functioning of the arbiter. • The properties were formalized using bisimulation relations between finite labeled transition systems. • Correctness was established automatically in a few minutes using the CÆSAR/ ALDÉBARAN toolbox. 7
高级软件 程 模型检验 8/36 A High-level Data Link Controller was being designed at AT&T in Madrid in 1996 • Researchers at Bell Labs offered to check some properties of the design using the Formal Check verifier. • Within five hours, six properties were specified and five were verified. • The sixth property failed, uncovering a bug that would have reduced through put or caused lost transmissions! 8
高级软件 程 模型检验 9/36 Richard Raimi used Motorola’s Verdict model checker to debug a hardware laboratory failure. • Initial silicon of the Power. PC 620 microprocessor Crashed during boot of an operating system. • In a matter of seconds, Verdict found a BIU deadlock causing the failure. 9
高级软件 程 模型检验 10/36 In 1994 Bosscher, Polak, and Vaandrager won a bestpaper award for proving manually the correctness of a control protocol used in Philips stereo components. • In 1995 Ho and Wong-Toi verified an abstraction of this protocol automatically using Hy. Tech. • Later in 1995 Daws and Yovine used Kronos to check all the properties stated and hand proved by Bosscher, et al. 10
高级软件 程 模型检验 11/36 The New. Co. Re Project (89 -92) was the first application of formal verification in a software project within AT&T. • A special purpose model checker was used in the development of the CCITT ISDN User Part Protocol. • Five “verification engineers” analyzed 145 requirements. • A total of 7, 500 lines of SDL source code was verified. • 112 errors were found; about 55%of the original design requirements were logically inconsistent. 11
高级软件 程 模型检验 12/36 In 1995 the Concurrency Workbench was used to analyze an active structural control system to make buildings more resistant to earthquakes. • The control system sampled the forces being applied to the structure and used hydraulic actuators to exert countervailing forces. • A timing error was discovered that could have caused the controller to worsen, rather than dampen, the vibration experienced during earthquakes. 12
高级软件 程 模型检验 13/36 ACM 2007年度图灵奖(Turing Award) Edmund M. Clarke, E Allen Emerson, Joseph Sifakis 1981年,美国的Edmund Clarke和Allen Emerson以及 在法国的Sifakis分别提出了模型检测(Model Checking)的最初概念 l 他们开发了一套用于判断硬件和软件设计的理论模型 是否满足规范的方法 l 当系统检测失败时,还能利用它确定问题存在的位置 l 13
模型检验 14/36 高级软件 程 用于软件? 软件设计模型? • Statecharts …… 软件代码? Use static analysis to extract a finite state synchronization skeleton from the program. Model check the result. • Bandera --Kansas State • Java Path. Finder --NASA Ames • Slam Project (Bebop) --Microsoft 14
模型检验 15/36 高级软件 程 二、模型检测概述 1、基本情况 2、什么是模型检测 3、基本思想 4、过程描述 15
高级软件 程 模型检验 16/36 1、基本情况 l 产生 – 20世纪 80年代初,Clarke, Emerson等提出了用 于并发系统性质的CTL逻辑,设计了检测有穷 状态系统是否满足给定CTL公式的算法 l 特性 – 能给出反例 – 自动化程度高 l 应用 – 计算机硬件、通信协议、控制系统、安全认证 协议、软件安全 等 16
![模型检验 17/36 高级软件 程 2、什么是模型检测 l 定义[Clarke & Emerson 1981] “Model checking is an 模型检验 17/36 高级软件 程 2、什么是模型检测 l 定义[Clarke & Emerson 1981] “Model checking is an](https://present5.com/presentation/67ed8094c48dff062b88025d7efca10d/image-17.jpg)
模型检验 17/36 高级软件 程 2、什么是模型检测 l 定义[Clarke & Emerson 1981] “Model checking is an automated technique that, given a finite-state model of a system and a logical property, systematically checks whether this property holds for (a given initial state in) that model. ” 给定一个系统的有限状态模型,和一个逻辑性质,系 统地检测:这个模型(含初始状态)满足该性质 17
高级软件 程 模型检验 18/36 3、基本思想 (1)用状态迁移系统(S)表示系统的行为,用模态/ 时序逻辑公式(F)描述系统的性质。 (2)“系统是否具有某种期望的性质”就转化数学问 题“状态迁移系统S是否是公式F的一个模型?” 公式表 示:S |= F? 对于有限状态迁移系统,这个问题是可以判定的。 18
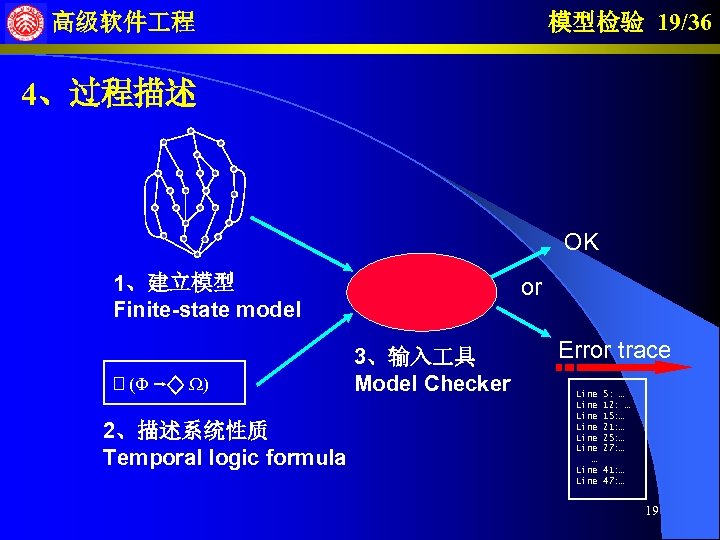
模型检验 19/36 高级软件 程 4、过程描述 OK 1、建立模型 Finite-state model (F W) 2、描述系统性质 Temporal logic formula or 3、输入 具 Model Checker Error trace Line Line … Line 5: … 12: … 15: … 21: … 25: … 27: … 41: … 47: … 19
模型检验 20/36 高级软件 程 三、模型检测算法概览 1、系统的表示 2、属性的表示 3、搜索状态空间 2个例子:CTL 与 LTL 20
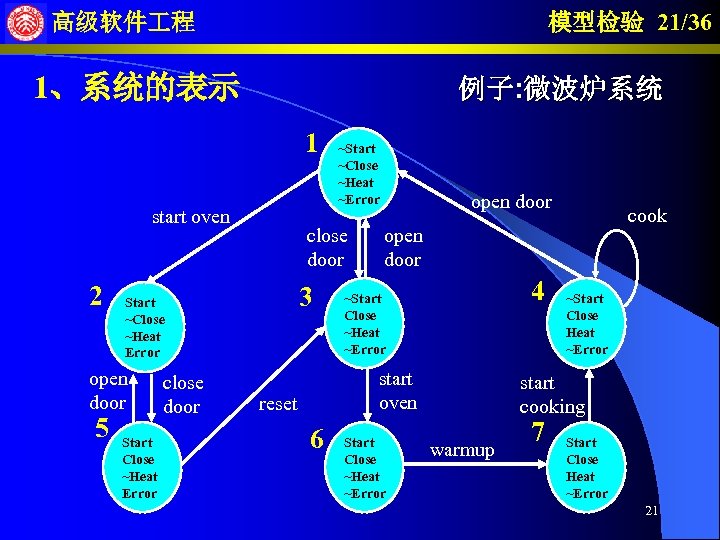
模型检验 21/36 高级软件 程 1、系统的表示 例子: 微波炉系统 1 start oven 2 5 close door 3 Start ~Close ~Heat Error open door Start Close ~Heat Error close door ~Start ~Close ~Heat ~Error open door 4 ~Start Close ~Heat ~Error start oven reset 6 cook Start Close ~Heat ~Error ~Start Close Heat ~Error start cooking warmup 7 Start Close Heat ~Error 21
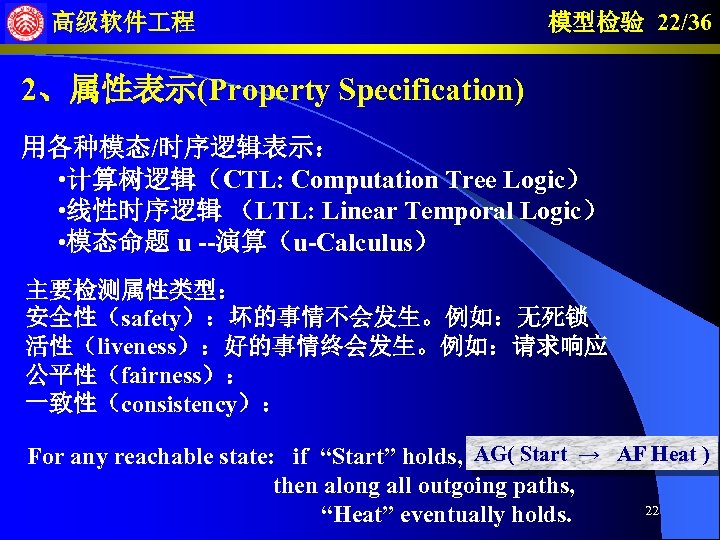
高级软件 程 模型检验 22/36 2、属性表示(Property Specification) 用各种模态/时序逻辑表示: • 计算树逻辑(CTL: Computation Tree Logic) • 线性时序逻辑 (LTL: Linear Temporal Logic) • 模态命题 u --演算(u-Calculus) 主要检测属性类型: 安全性(safety):坏的事情不会发生。例如:无死锁 活性(liveness):好的事情终会发生。例如:请求响应 公平性(fairness): 一致性(consistency): For any reachable state: if “Start” holds, AG( Start → AF Heat ) then along all outgoing paths, 22 “Heat” eventually holds.
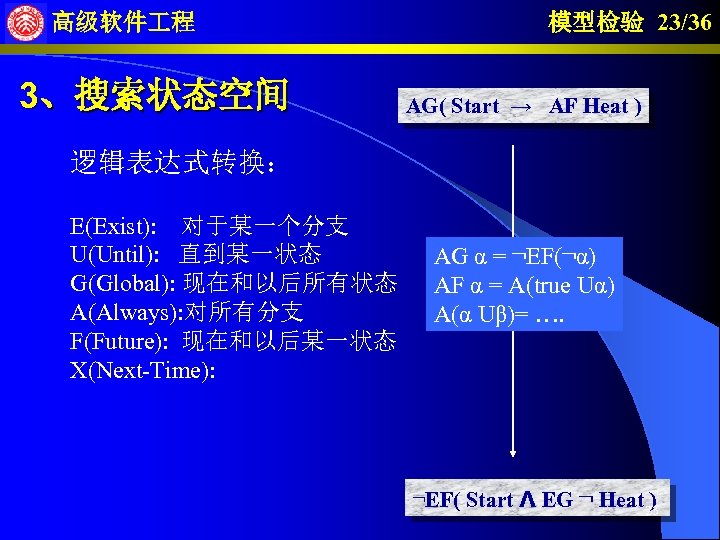
高级软件 程 3、搜索状态空间 模型检验 23/36 AG( Start → AF Heat ) 逻辑表达式转换: E(Exist): 对于某一个分支 U(Until): 直到某一状态 G(Global): 现在和以后所有状态 A(Always): 对所有分支 F(Future): 现在和以后某一状态 X(Next-Time): AG α = ¬EF(¬α) AF α = A(true Uα) A(α Uβ)= …. ¬EF( Start Λ EG ¬ Heat 23 )
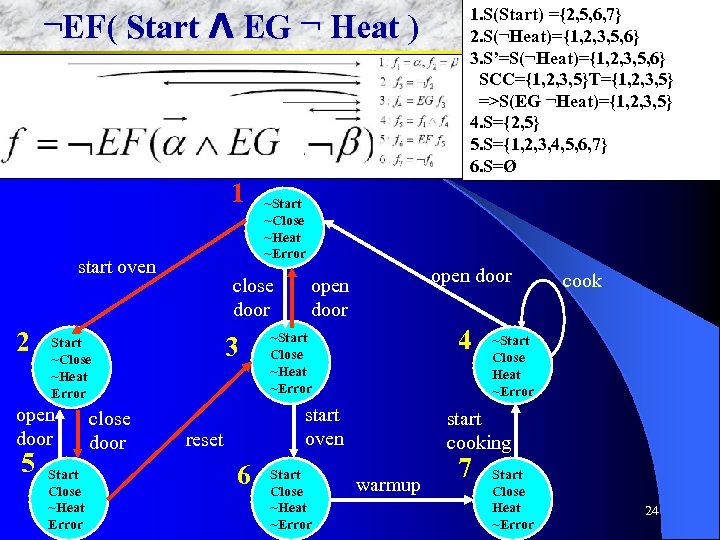
高级软件 程 ¬EF( Start Λ EG ¬ Heat ) 1 start oven 2 open door 5 Start Close ~Heat Error close door ~Start ~Close ~Heat ~Error close door 3 Start ~Close ~Heat Error open door 4 ~Start Close ~Heat ~Error start oven reset 6 1. S(Start) ={2, 5, 6, 7} 模型检验 24/36 2. S(¬Heat)={1, 2, 3, 5, 6} 3. S’=S(¬Heat)={1, 2, 3, 5, 6} SCC={1, 2, 3, 5}T={1, 2, 3, 5} =>S(EG ¬Heat)={1, 2, 3, 5} 4. S={2, 5} 5. S={1, 2, 3, 4, 5, 6, 7} 6. S=Ø Start Close ~Heat ~Error cook ~Start Close Heat ~Error start cooking warmup 7 Start Close Heat ~Error 24
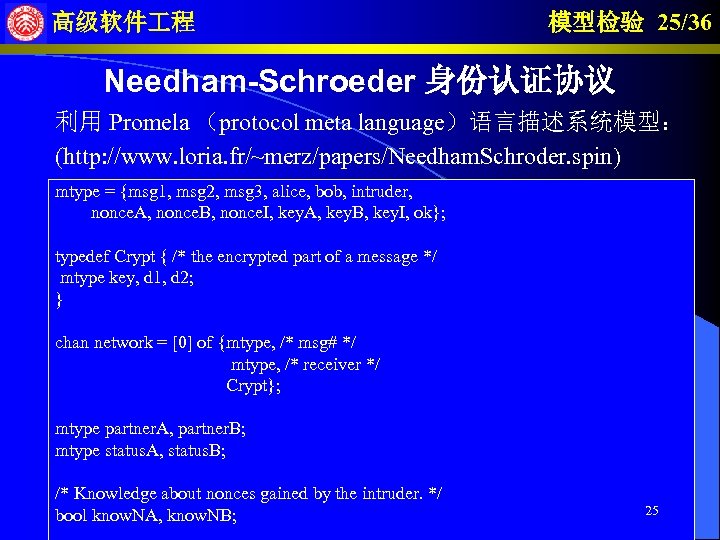
高级软件 程 模型检验 25/36 Needham-Schroeder 身份认证协议 利用 Promela (protocol meta language)语言描述系统模型: (http: //www. loria. fr/~merz/papers/Needham. Schroder. spin) mtype = {msg 1, msg 2, msg 3, alice, bob, intruder, nonce. A, nonce. B, nonce. I, key. A, key. B, key. I, ok}; typedef Crypt { /* the encrypted part of a message */ mtype key, d 1, d 2; } chan network = [0] of {mtype, /* msg# */ mtype, /* receiver */ Crypt}; mtype partner. A, partner. B; mtype status. A, status. B; /* Knowledge about nonces gained by the intruder. */ bool know. NA, know. NB; 25
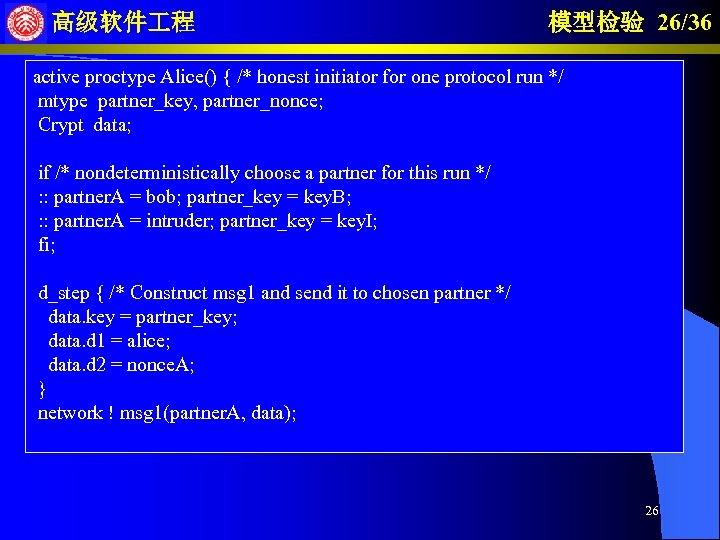
高级软件 程 模型检验 26/36 active proctype Alice() { /* honest initiator for one protocol run */ mtype partner_key, partner_nonce; Crypt data; if /* nondeterministically choose a partner for this run */ : : partner. A = bob; partner_key = key. B; : : partner. A = intruder; partner_key = key. I; fi; d_step { /* Construct msg 1 and send it to chosen partner */ data. key = partner_key; data. d 1 = alice; data. d 2 = nonce. A; } network ! msg 1(partner. A, data); 26
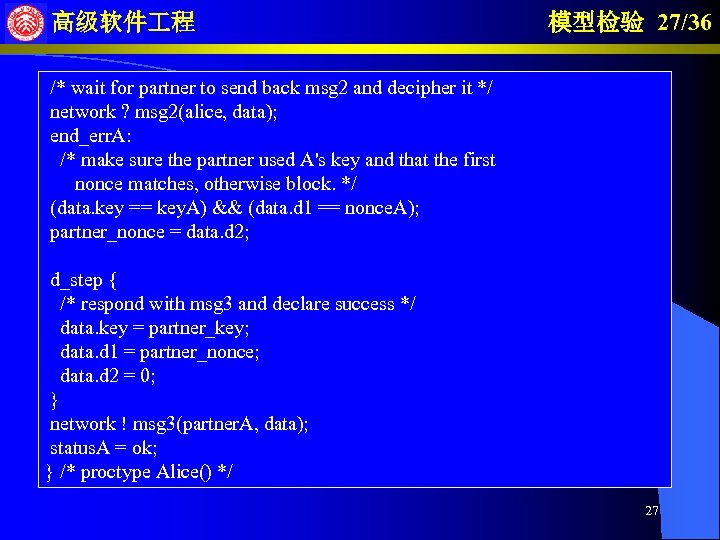
高级软件 程 模型检验 27/36 /* wait for partner to send back msg 2 and decipher it */ network ? msg 2(alice, data); end_err. A: /* make sure the partner used A's key and that the first nonce matches, otherwise block. */ (data. key == key. A) && (data. d 1 == nonce. A); partner_nonce = data. d 2; d_step { /* respond with msg 3 and declare success */ data. key = partner_key; data. d 1 = partner_nonce; data. d 2 = 0; } network ! msg 3(partner. A, data); status. A = ok; } /* proctype Alice() */ 27
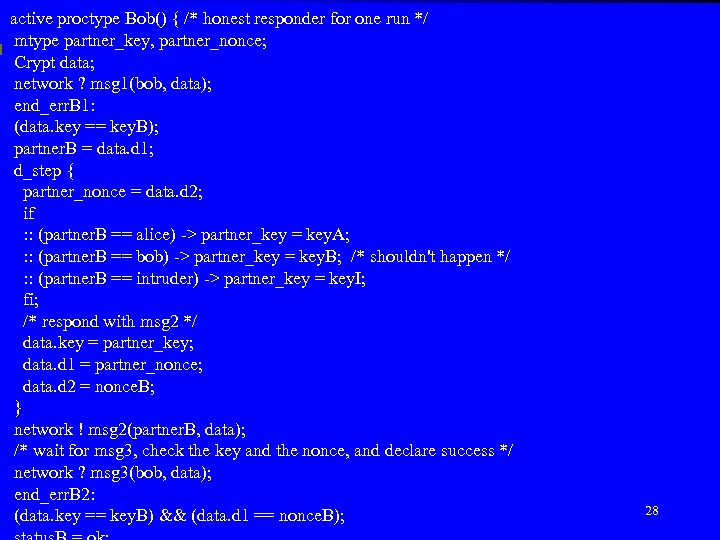
active高级软件 程 honest responder for one run */ proctype Bob() { /* mtype partner_key, partner_nonce; Crypt data; network ? msg 1(bob, data); end_err. B 1: (data. key == key. B); partner. B = data. d 1; d_step { partner_nonce = data. d 2; if : : (partner. B == alice) -> partner_key = key. A; : : (partner. B == bob) -> partner_key = key. B; /* shouldn't happen */ : : (partner. B == intruder) -> partner_key = key. I; fi; /* respond with msg 2 */ data. key = partner_key; data. d 1 = partner_nonce; data. d 2 = nonce. B; } network ! msg 2(partner. B, data); /* wait for msg 3, check the key and the nonce, and declare success */ network ? msg 3(bob, data); end_err. B 2: (data. key == key. B) && (data. d 1 == nonce. B); 模型检验 28/36 28
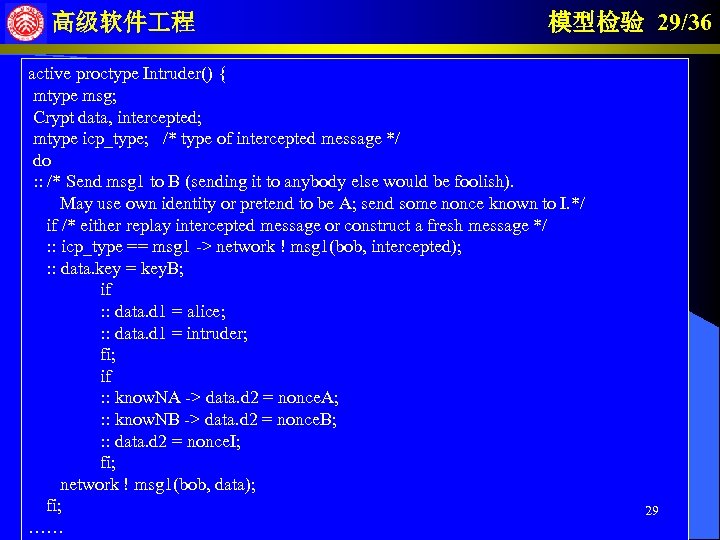
高级软件 程 模型检验 29/36 active proctype Intruder() { mtype msg; Crypt data, intercepted; mtype icp_type; /* type of intercepted message */ do : : /* Send msg 1 to B (sending it to anybody else would be foolish). May use own identity or pretend to be A; send some nonce known to I. */ if /* either replay intercepted message or construct a fresh message */ : : icp_type == msg 1 -> network ! msg 1(bob, intercepted); : : data. key = key. B; if : : data. d 1 = alice; : : data. d 1 = intruder; fi; if : : know. NA -> data. d 2 = nonce. A; : : know. NB -> data. d 2 = nonce. B; : : data. d 2 = nonce. I; fi; network ! msg 1(bob, data); fi; …… 29
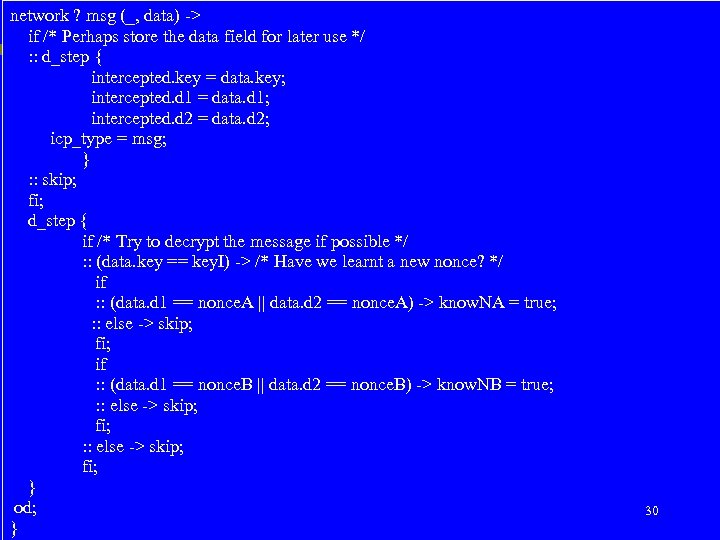
network ? msg (_, data) -> 模型检验 30/36 高级软件 程 if /* Perhaps store the data field for later use */ : : d_step { intercepted. key = data. key; intercepted. d 1 = data. d 1; intercepted. d 2 = data. d 2; icp_type = msg; } : : skip; fi; d_step { if /* Try to decrypt the message if possible */ : : (data. key == key. I) -> /* Have we learnt a new nonce? */ if : : (data. d 1 == nonce. A || data. d 2 == nonce. A) -> know. NA = true; : : else -> skip; fi; if : : (data. d 1 == nonce. B || data. d 2 == nonce. B) -> know. NB = true; : : else -> skip; fi; } od; 30 }
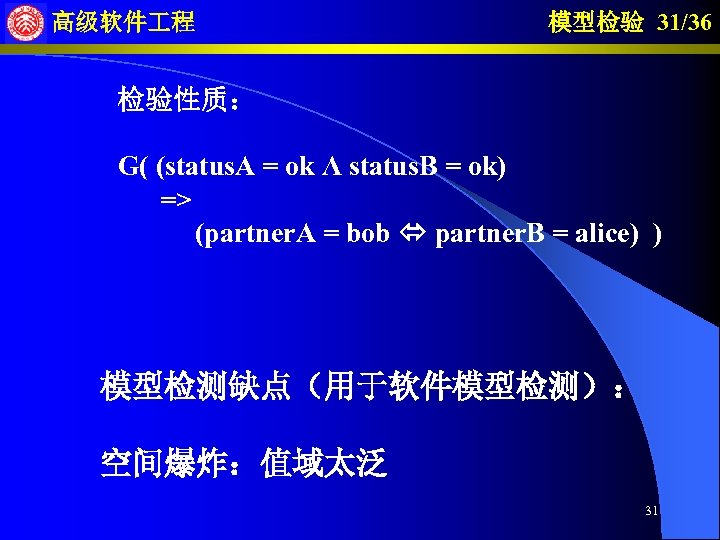
高级软件 程 模型检验 31/36 检验性质: G( (status. A = ok Λ status. B = ok) => (partner. A = bob partner. B = alice) ) 模型检测缺点(用于软件模型检测): 空间爆炸:值域太泛 31

模型检验 32/36 高级软件 程 四、模型检测 具 1、SMV 2、SPIN 3、其它 具 32
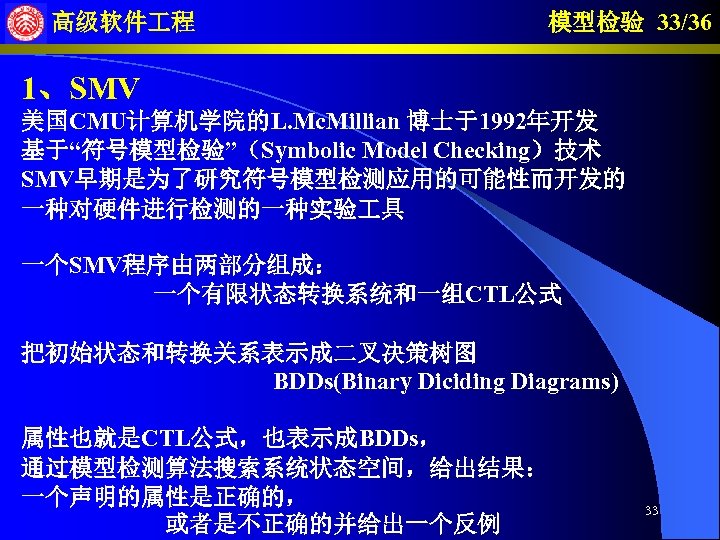
高级软件 程 模型检验 33/36 1、SMV 美国CMU计算机学院的L. Mc. Millian 博士于1992年开发 基于“符号模型检验”(Symbolic Model Checking)技术 SMV早期是为了研究符号模型检测应用的可能性而开发的 一种对硬件进行检测的一种实验 具 一个SMV程序由两部分组成: 一个有限状态转换系统和一组CTL公式 把初始状态和转换关系表示成二叉决策树图 BDDs(Binary Diciding Diagrams) 属性也就是CTL公式,也表示成BDDs, 通过模型检测算法搜索系统状态空间,给出结果: 一个声明的属性是正确的, 或者是不正确的并给出一个反例 33
高级软件 程 模型检验 34/36 2、SPIN 由贝尔实验室的形式化方法与验证小组 于1980年开始开发的模型检测 具 建模方式:使用Promela语言建模,整个系统可以看作是一组 同步的可扩展的有限状态机 模型检测器:可当做一个完整的LTL(Linear Temporal Logic) 模型检验系统来使用,支持所有的可用的线性时态逻辑表示的 正确性验证要求,也可以在有效的on-the-fly检验系统中用来检 验协议的安全特征 其他的特征:将偏序简约(partial order reductions)技术、 Bit State Hashing方法和线性时序逻辑有效的结合使用 适合用于:通信协议的检测和线性时序逻辑模型检测 34
高级软件 程 模型检验 35/36 3、其它 具 • PROD • 建模方式:基于Pr/T Petri网,有自己的对Pr/T Petri网的描述语言 • 分析方式:实现可达图的CTL模型检测以及基于on-the-fly方法的LTL验证 Perti 网 具:INA、Lola、PEP、Design/CPN… Uppaal和Kronos:是用于时控系统的模型检测 具 Caesar Aldebaran(CADP):是基于LTSs的一组模型检测 具 Java Pathfinder 2:是Java程序检测器 Slam:一个检测C程序的检测 具 35
67ed8094c48dff062b88025d7efca10d.ppt