653fd15b5591f8c569450a0396af0810.ppt
- Количество слайдов: 164
「我國IPv 6建置發展計畫」 92年度期中成果報告 研究發展分項計畫 子計畫一:新一代網際網路移動環境與資 訊家電技術之研究
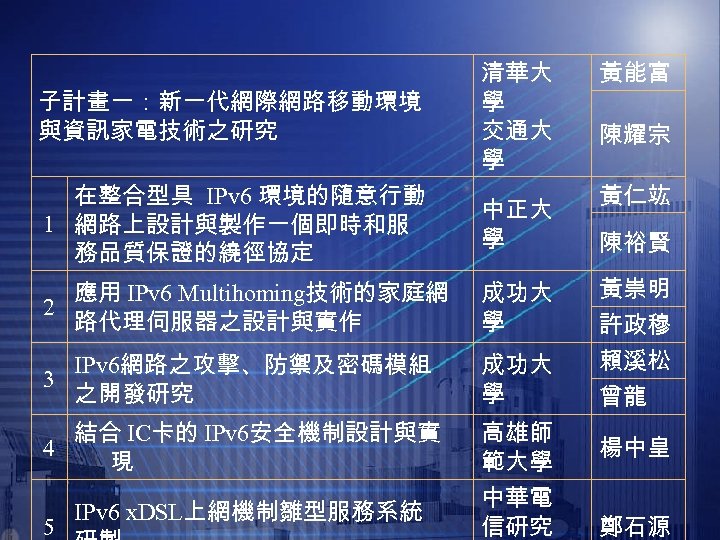
子計畫一:新一代網際網路移動環境 與資訊家電技術之研究 清華大 學 交通大 學 在整合型具 IPv 6 環境的隨意行動 1 網路上設計與製作一個即時和服 務品質保證的繞徑協定 中正大 學 應用 IPv 6 Multihoming技術的家庭網 2 路代理伺服器之設計與實作 成功大 學 3 IPv 6網路之攻擊、防禦及密碼模組 之開發研究 成功大 學 4 結合 IC卡的 IPv 6安全機制設計與實 現 高雄師 範大學 IPv 6 x. DSL上網機制雛型服務系統 中華電 信研究 5 黃能富 陳耀宗 黃仁竑 陳裕賢 黃崇明 許政穆 賴溪松 曾龍 楊中皇 鄭石源
Mobile IPv 6 over MANET 之雛形系統的 研製 計畫主持人:國立中正大學 資 系 陳裕賢 副教授 黃仁竑 教授
Outline n Part I: Mobile IPv 6 over MANET 之運作原理 介紹: l Why is the need of "Mobile IPv 6 over MANET" ? l The key difference between Mobile IPv 4 over MANET with Mobile IPv 6 over MANET l The difficulty of implementing the Mobile IPv 6 over MANET n Part II: Mobile IPv 6 over MANET 之雛形系統 架構
Part I: Mobile IPv 6 over MANET 之 運作原理介紹: Why is the need of "Mobile IPv 6 over MANET" ? l The key difference between Mobile IPv 4 over MANET with Mobile IPv 6 over MANET. l The difficulty of implementing the Mobile IPv 6 over MANET. l
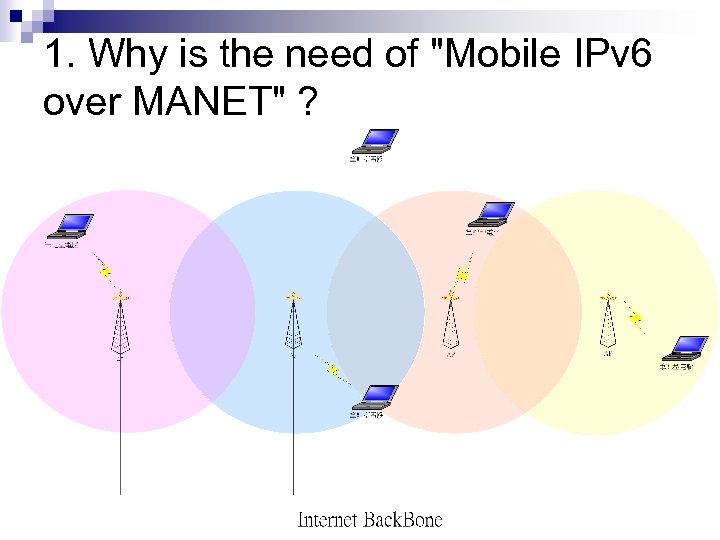
1. Why is the need of "Mobile IPv 6 over MANET" ?
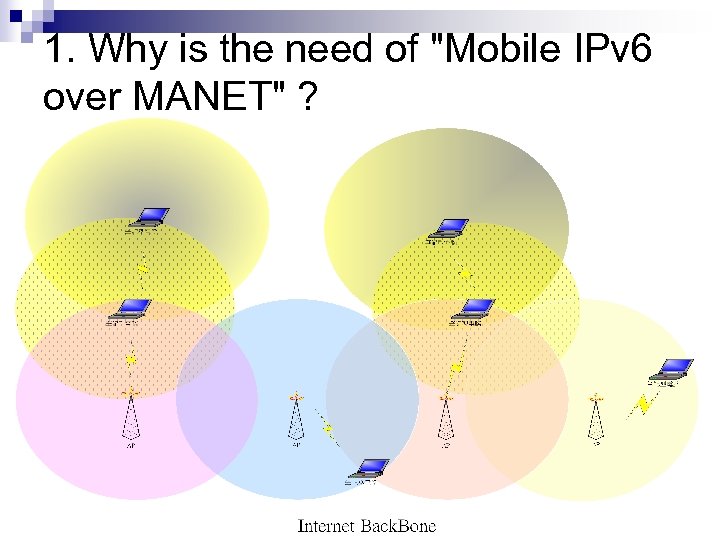
1. Why is the need of "Mobile IPv 6 over MANET" ?
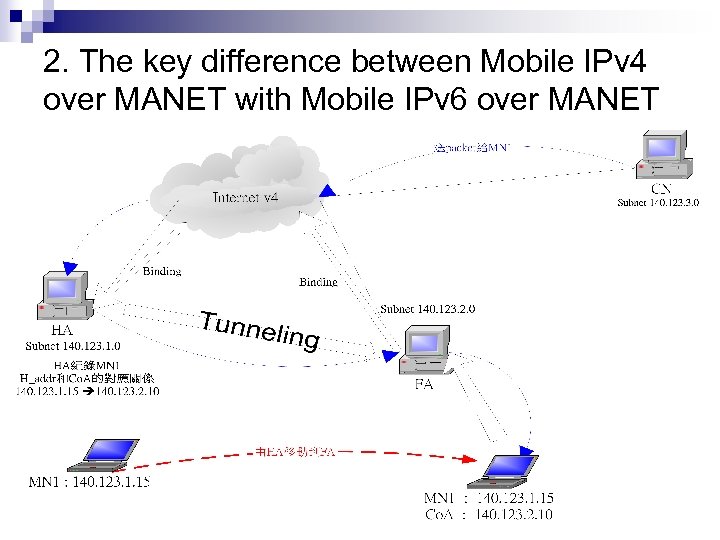
2. The key difference between Mobile IPv 4 over MANET with Mobile IPv 6 over MANET
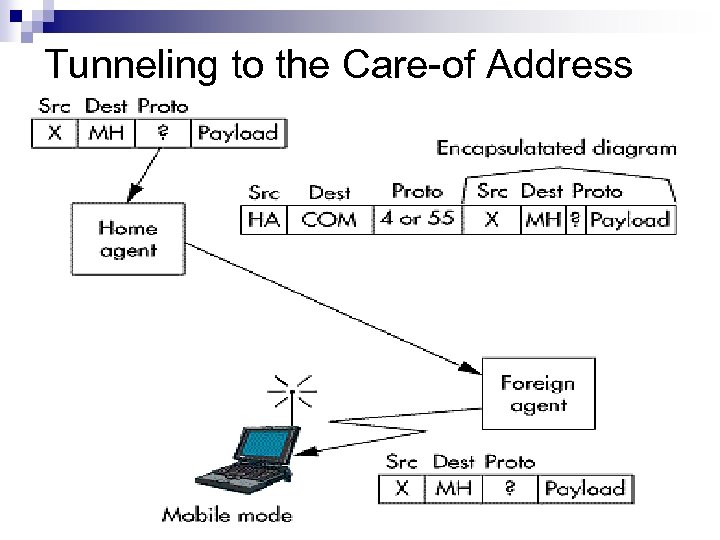
Tunneling to the Care-of Address
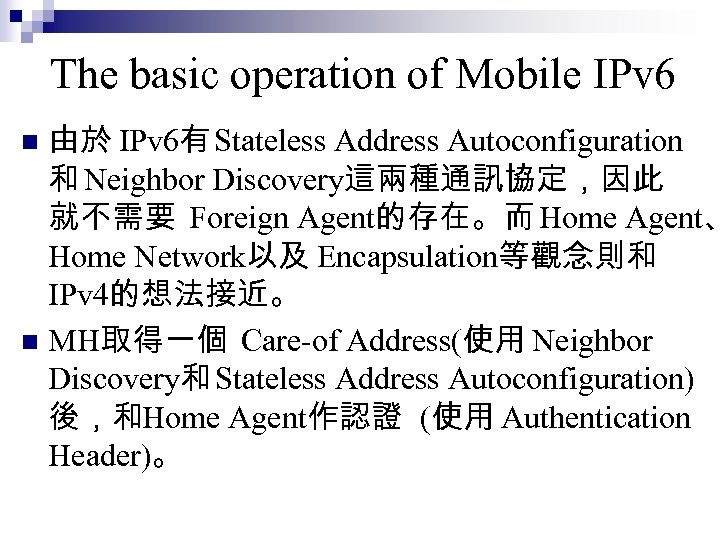
The basic operation of Mobile IPv 6 由於 IPv 6有 Stateless Address Autoconfiguration 和 Neighbor Discovery這兩種通訊協定,因此 就不需要 Foreign Agent的存在。而 Home Agent、 Home Network以及 Encapsulation等觀念則和 IPv 4的想法接近。 n MH取得一個 Care-of Address(使用 Neighbor Discovery和 Stateless Address Autoconfiguration) 後,和Home Agent作認證 (使用 Authentication Header)。 n
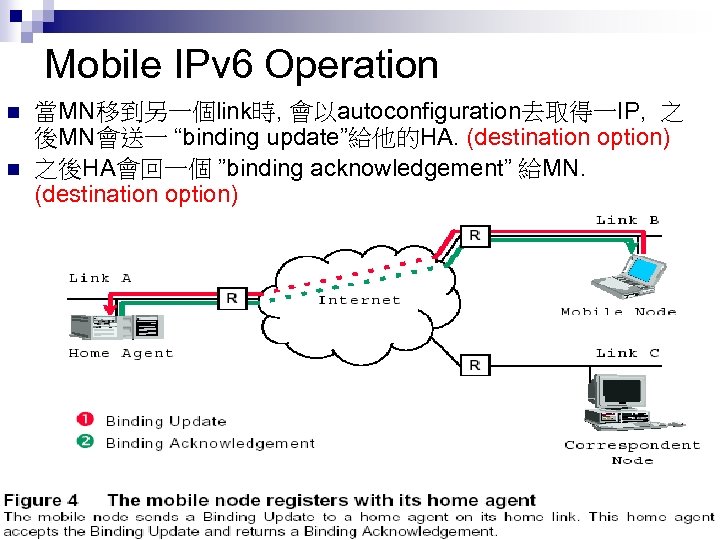
Mobile IPv 6 Operation n n 當MN移到另一個link時, 會以autoconfiguration去取得一IP, 之 後MN會送一 “binding update”給他的HA. (destination option) 之後HA會回一個 ”binding acknowledgement” 給MN. (destination option)
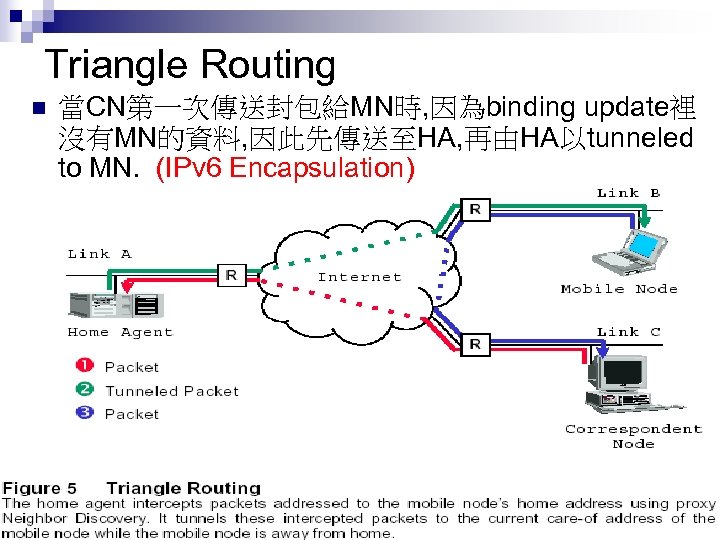
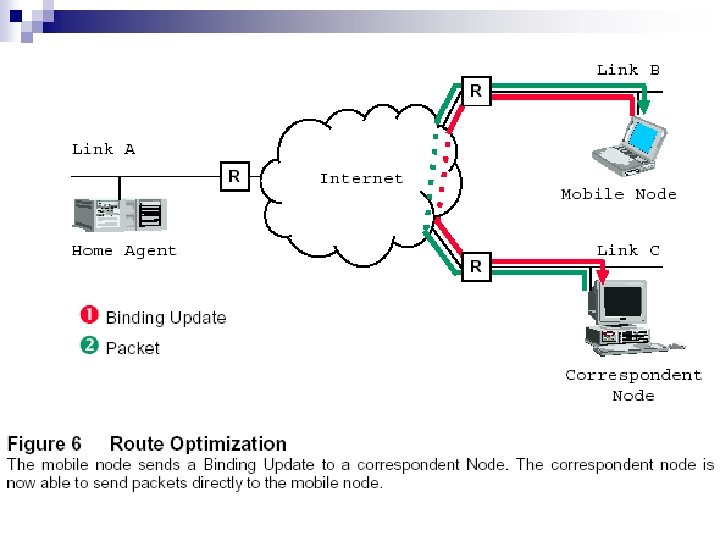
Triangle Routing n 當CN第一次傳送封包給MN時, 因為binding update裡 沒有MN的資料, 因此先傳送至HA, 再由HA以tunneled to MN. (IPv 6 Encapsulation)
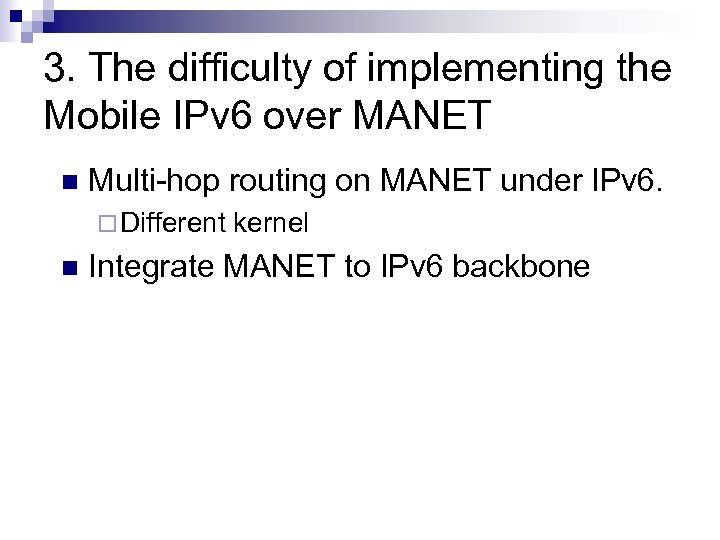
3. The difficulty of implementing the Mobile IPv 6 over MANET n Multi-hop routing on MANET under IPv 6. ¨ Different kernel n Integrate MANET to IPv 6 backbone
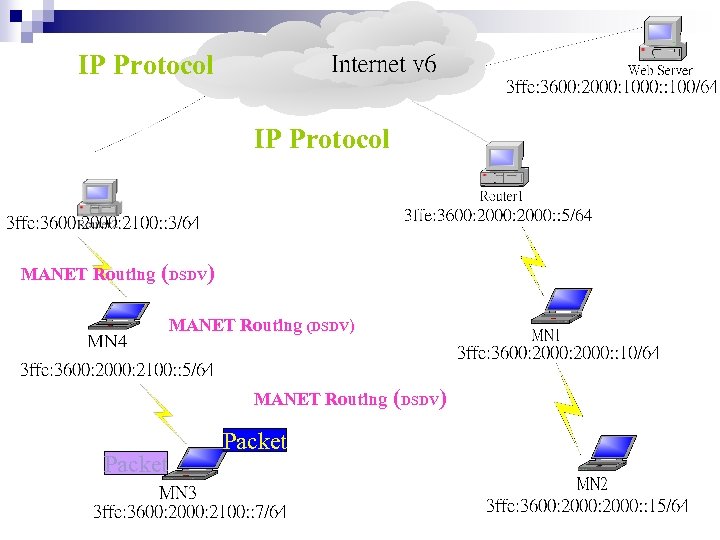
IP Protocol MANET Routing (DSDV) MANET Routing Packet (DSDV)
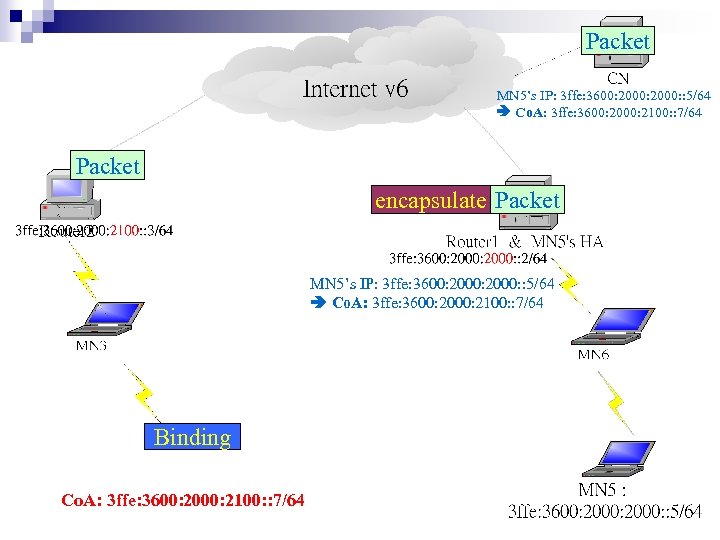
Packet MN 5’s IP: 3 ffe: 3600: 2000: : 5/64 Co. A: 3 ffe: 3600: 2000: 2100: : 7/64 Packet encapsulate Packet MN 5’s IP: 3 ffe: 3600: 2000: : 5/64 Co. A: 3 ffe: 3600: 2000: 2100: : 7/64 ICMPv 6 Binding Co. A: 3 ffe: 3600: 2000: 2100: : 7/64
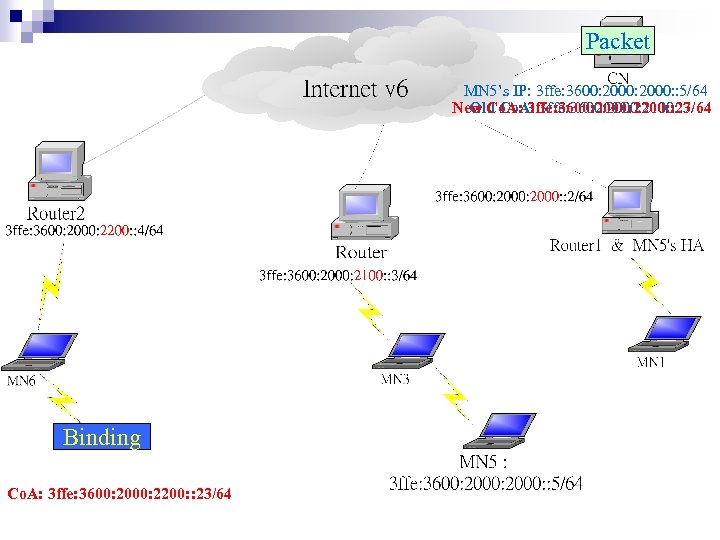
Packet MN 5’s IP: 3 ffe: 3600: 2000: : 5/64 New Co. A: 3 ffe: 3600: 2000: 2200: : 23/64 Old Co. A: 3 ffe: 3600: 2000: 2100: : 7/64 ICMPv 6 Binding Co. A: 3 ffe: 3600: 2000: 2200: : 23/64
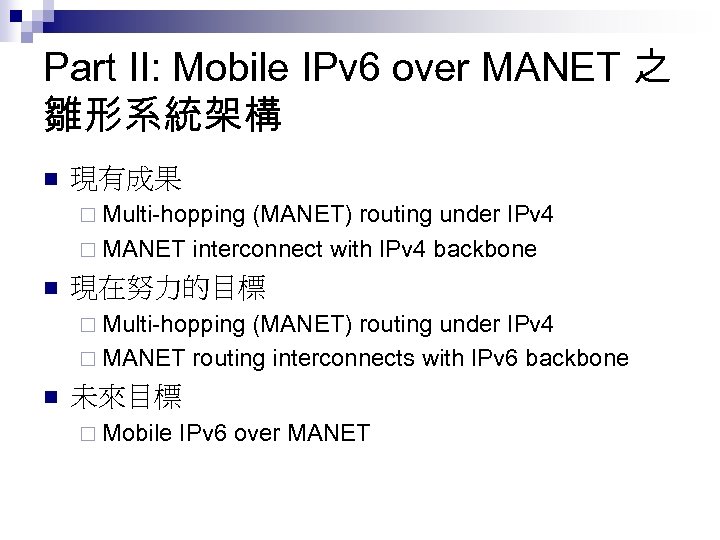
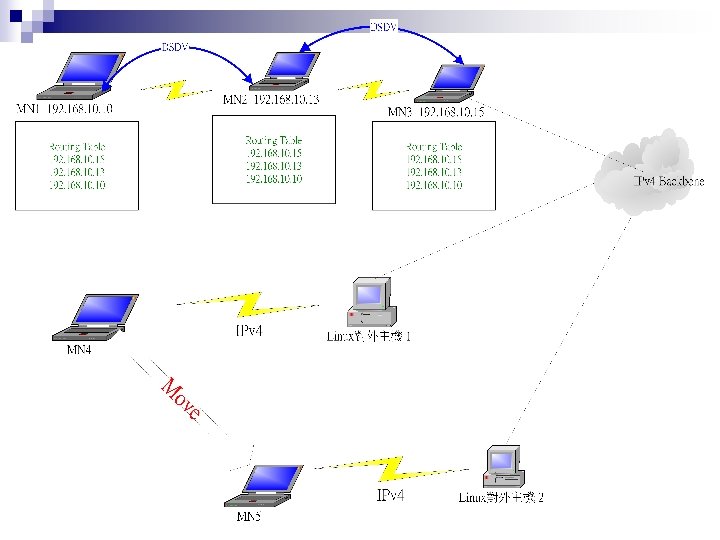
Part II: Mobile IPv 6 over MANET 之 雛形系統架構 n 現有成果 ¨ Multi-hopping (MANET) routing under IPv 4 ¨ MANET interconnect with IPv 4 backbone n 現在努力的目標 ¨ Multi-hopping (MANET) routing under IPv 4 ¨ MANET routing interconnects with IPv 6 backbone n 未來目標 ¨ Mobile IPv 6 over MANET
應用IPv 6 Multihoming技術 的家庭網路代理伺服器 之設計與實作 國立成功大學資訊 程系 國立中正大學資訊 程系
Outline n n n Multihoming Introduction Related Multihoming Internet-Draft Project Design and Implementation Conclusion Reference
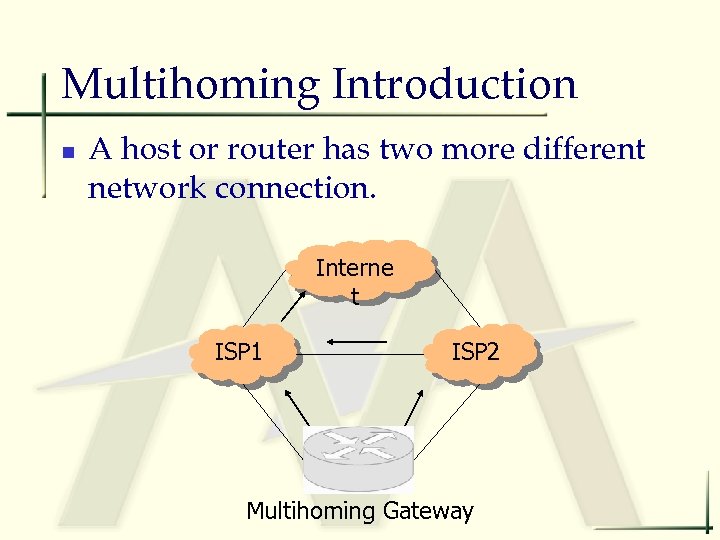
Multihoming Introduction n A host or router has two more different network connection. Interne t ISP 1 ISP 2 Multihoming Gateway
Multihoming Advantages n n Fault Tolerance Load Balance Provider Selection Link Aggregation
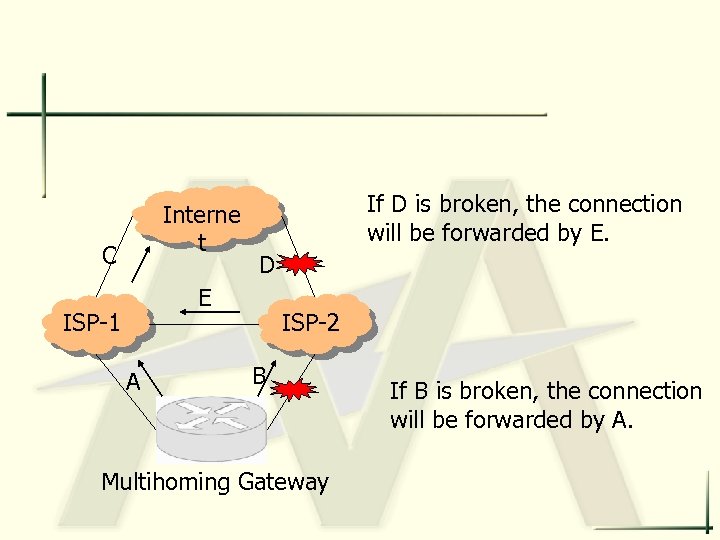
Interne t C If D is broken, the connection will be forwarded by E. D E ISP-1 A ISP-2 B Multihoming Gateway If B is broken, the connection will be forwarded by A.
Multihoming Scope n Provider-Level n n Site-Level n n draft-ieft-inpgwg-ipv 6 multihome-with-aggr 01 At site exit routers, RFC 3178 Subnet/Host-Level
Multihoming Problems n n ISPs cannot advertise prefixes of other ISPs Site cannot advertise to upstream providers’ prefixes longer than their assigned prefix

Multihoming Solutions n n Router-based Solutions Host-based Solutions Mobile-based Solutions Geographic or Exchange-based Solutions
Router-based Solutions n GSE/8+8 n draft-ipng-gseaddr-00 n n Multihoming with Route Aggregation n n GSE: Global, Site, and End System Address Elements draft-ietf-ipngwg-ipv 6 multihome-with-aggr 01 Multihoming Using Router Renumbering n draft-ietf-ipngwg-multi-isp-00
Router-based Solutions (Con’t) n Multihoming Support at Site Exit Routers n n IPv 6 Multihoming Support at Site Exit Routers, RFC 3178 Multihoming Aliasing Protocol (MHAP) n draft-py-mhap-intro-00
Host-based Solutions n Host-Centric IPv 6 Multihoming n n draft-huitema-multi 6 -hosts-01 Host Identity Payload Protocol (HIP)
Mobile-based Solutions n draft-bagnulo-multi 6 -mnm-00 n Application of the MIPv 6 protocol to the multi-homing problem

Geographic or Exchange-based Solutions n GAPI: A Geographically Aggregatable Provider Independent Address Space to Support Multihoming in IPv 6 n n draft-py-multi 6 -gapi-00 Extension Header for Site Multihoming Support n draft-bagnulo-multi 6 -mh. Ext. Hdr-00
Related Internet-Draft n draft-ietf-multi 6 -multihoming-requirements-06 n n draft-savola-multi 6 -nowwhat-00 n n IPv 6 Site Multihoming: Now What? draft-de-launois-multi 6 -naros-00 n n Goals for IPv 6 Site-Multihoming Architectures. NAROS : Host-Centric IPv 6 Multihoming with Traffic Engineering. draft-kurtis-multihoming-longprefix-00 n Multihoming in IPv 6 by multiple announcements of longer prefixes.
Related Internet-Draft (Con’t) n draft-hain-ipv 6 -pi-addr-use-04 n n draft-py-multi 6 -gapi-00 n n GAPI: A Geographically Aggregatable Provider Independent Address Space to Support Multihoming in IPv 6. draft-kurtis-multi 6 -roadmap-00 n n Application and Use of the IPv 6 Provider Independent. A road-map for multihoming in IPv 6. draft-savola-multi 6 -asn-pi-00 n Multihoming Using IPv 6 Addressing Derived from AS Numbers.

Our Design Goals n To build a Multihoming Gateway for IPv 6 -based Home. Network n n n Multiple Outgoing Interfaces Fault Tolerance Load Balance Bandwidth Aggregation Web Proxy …
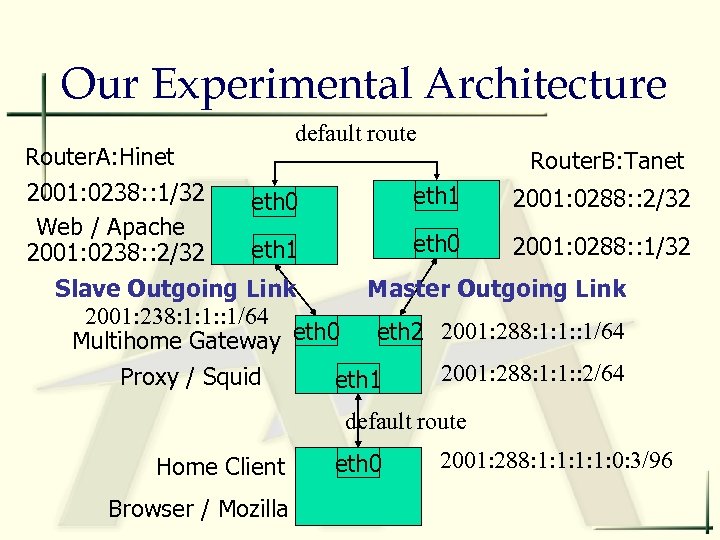
Our Experimental Architecture default route Router. A: Hinet Router. B: Tanet 2001: 0238: : 1/32 eth 1 2001: 0288: : 2/32 eth 0 Web / Apache eth 0 2001: 0288: : 1/32 eth 1 2001: 0238: : 2/32 Slave Outgoing Link Master Outgoing Link 2001: 238: 1: 1: : 1/64 eth 2 2001: 288: 1: 1: : 1/64 Multihome Gateway eth 0 2001: 288: 1: 1: : 2/64 Proxy / Squid eth 1 default route Home Client Browser / Mozilla eth 0 2001: 288: 1: 1: 0: 3/96
System Implementation n Interface/Link Detection n Using ICMPv 6 to detect the interface is available or not n n Interface/Link Detection Periodically Modify/Setup Routing Information
System Implementation (Con’t) n Fault Tolerance (Redundant Link) n Assume ISPs assign a prefix to users, not only one IPv 6 address. n n n Multihoming Gateway connects two outgoing links from different ISPs, with different ipv 6 prefix Choose a master link to communicate The other is a slave/backup link
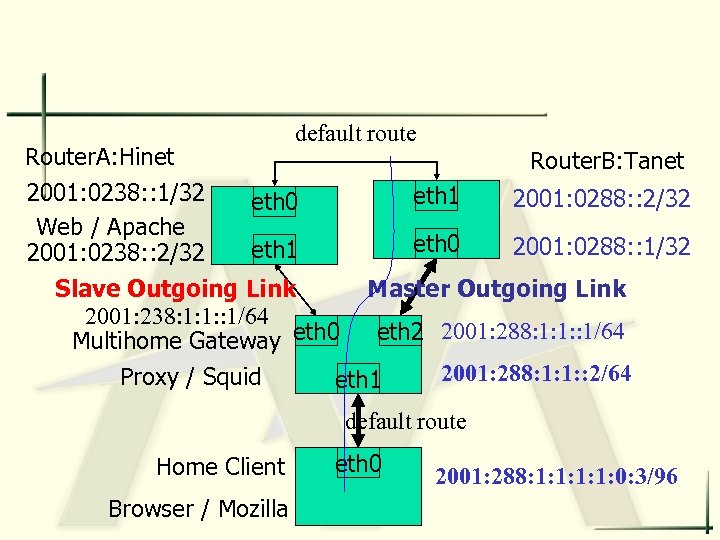
default route Router. A: Hinet Router. B: Tanet 2001: 0238: : 1/32 eth 1 2001: 0288: : 2/32 eth 0 Web / Apache eth 0 2001: 0288: : 1/32 eth 1 2001: 0238: : 2/32 Slave Outgoing Link Master Outgoing Link 2001: 238: 1: 1: : 1/64 eth 2 2001: 288: 1: 1: : 1/64 Multihome Gateway eth 0 2001: 288: 1: 1: : 2/64 Proxy / Squid eth 1 default route Home Client Browser / Mozilla eth 0 2001: 288: 1: 1: 0: 3/96
n When the master link is crashed n n The slave/backup link will be used The client need not change their IPs to fit the prefix of the slave/backup link n Use the IPv 6 address of the slave/backup link to communicate n n Using Network Address Translation Table Current Support n n ICMPv 6 TCP/UDP
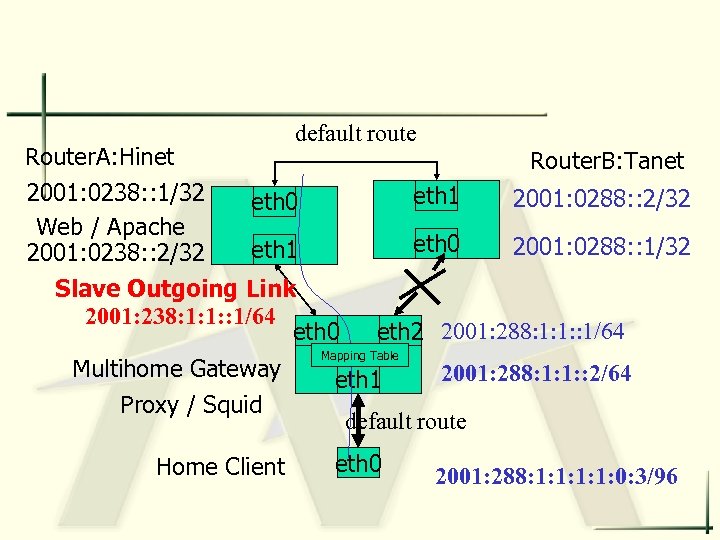
default route Router. A: Hinet 2001: 0238: : 1/32 eth 0 Web / Apache eth 1 2001: 0238: : 2/32 Slave Outgoing Link 2001: 238: 1: 1: : 1/64 eth 0 Multihome Gateway Proxy / Squid Home Client Router. B: Tanet eth 1 2001: 0288: : 2/32 eth 0 2001: 0288: : 1/32 eth 2 2001: 288: 1: 1: : 1/64 Mapping Table eth 1 2001: 288: 1: 1: : 2/64 default route eth 0 2001: 288: 1: 1: 0: 3/96
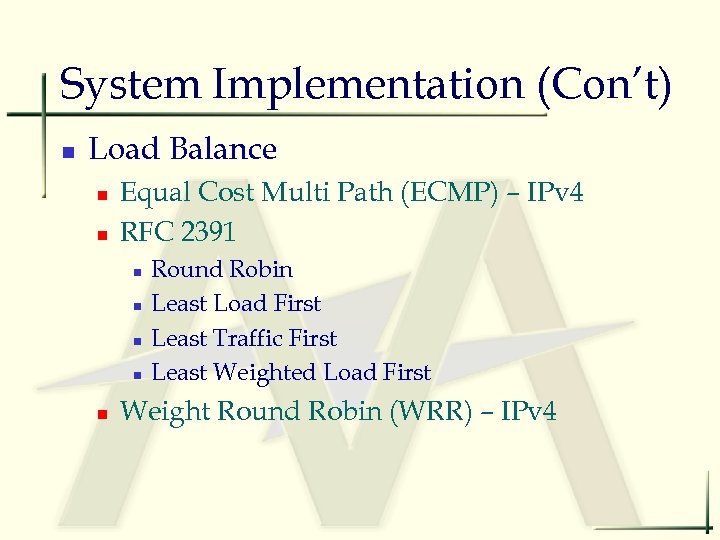
System Implementation (Con’t) n Load Balance n n Equal Cost Multi Path (ECMP) – IPv 4 RFC 2391 n n n Round Robin Least Load First Least Traffic First Least Weighted Load First Weight Round Robin (WRR) – IPv 4
n Web Proxy on the Multihoming Gateway n n n Squid supporting IPv 6 Installed on Multihoming Gateway Use the Fault-Tolerance to make the squid server workable at any time, expect all link are failed.
Conclusions n Introduce the benefits of Multihoming n n Apply Mulithoming to IPv 6 Home. Network n n Fault Tolerance Load Balance … Multihoming Gateway including the web proxy Describe Our Design Goals and Current System Implementation n n Reduce Cost Increase Performance
References n n n http: //www. ietf. org/html. charters/multi 6 -charter. html. draft-ietf-multi 6 -multihoming-requirements-06. txt. Il-sun Whang and Dongkyun Kim, “IPv 6 Multihoming”, KRnet 2002. David BINET, “Home Networking: The IPv 6 killer application? ”, France Telecom R&D, 2002. Jeff Doyle, “Issues in IPv 6 Deployment. “, Juniper NETWORKS.
The Design and Implementation of an IPv 6 -enabled Intrusion detection System: Status report Leader: C. S. Lai(NCKU) Core team-members: B. Tseng(Hsing-Kuo Univ. ) P. Chen(NCKU)
Agenda • Intrusion Detection System: An Overview • Our Work: IPv 6 -enabled Intrusion detection System • Further works:
I. Intrusion Detection System: An Overview • • What is Intrusion Detection System Model and Architecture Data Source Core technology Metric and Testing methodology Testing Environment and Test reports Development methodology: A softwareengineering viewpoint Other topics
Intrusion Detection System: What Intrusion detection is the process of monitoring the events occurring in a computer system or network and analyzing them for signs of intrusions, defined as attempts to compromise the confidentiality, integrity, availability, or to bypass the security mechanisms of a computer or network. Intrusions are caused by attackers accessing the systems from the Internet, authorized users of the systems who attempt to gain additional privileges for which they are not authorized, and authorized users who misuse the privileges given them. Intrusion Detection Systems (IDSs) are software or hardware products that automate this monitoring and analysis process.
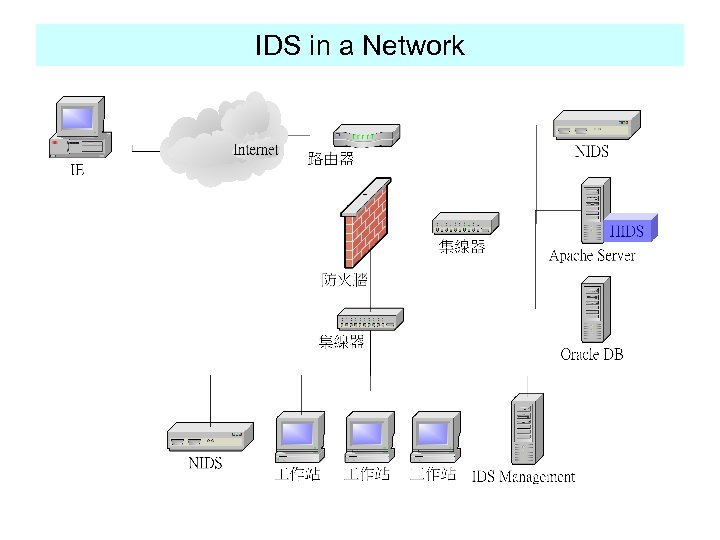
IDS in a Network
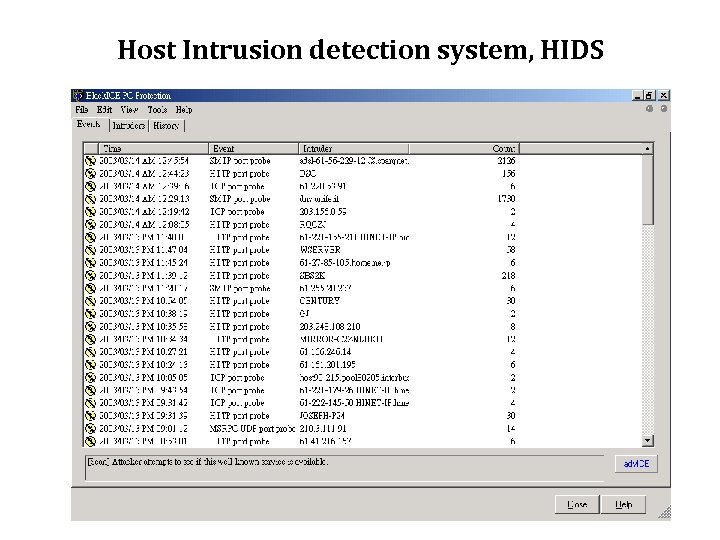
Host Intrusion detection system, HIDS
Model Denning, D. E. , "An Intrusion-Detection Model, "IEEE Transactions on Software Engineering, vol. 13, pp. 222 -232, 1987. Hypothesis: : exploitation of a system's vulnerabilities involves abnormal use, of the system; therefore, security violations could be detected from abnormal patterns of system usage. The model is independent of any particular system, application environment, system vulnerability, or type of intrusion, thereby providing a framework for a general-purpose intrusion-detection expert system.
Six main components • Subjects: Initiators of activity on a target system- normally users. • Objects: Resources managed by the system-files, commands, devices, etc. • Audit records: Generated by the target system in response to actions performed or attempted by subjects on objectsuser login, command execution, file access, etc. • Profiles: Structures that characterize the behavior of subjects with respect to objects in terms of statistical metrics and models of observed activity. Profiles are automatically generated and initialized from templates. • Anomaly records: Generated when abnormal behavior is detected. • Activity rules: Actions taken when some condition is satisfied, which update profiles, detect abnormal behavior, relate anomalies to suspected intrusions, and produce reports.
Architecture • Monolithic • Hierarchal structure • Agent-based IDS • Distributed IDS
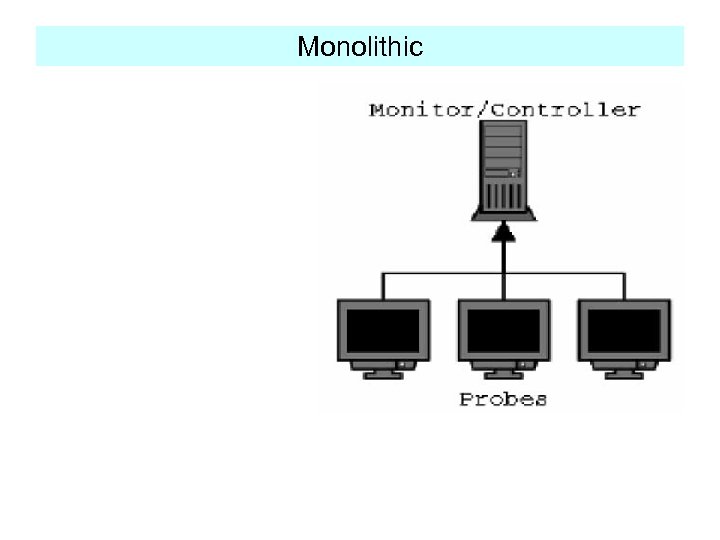
Monolithic
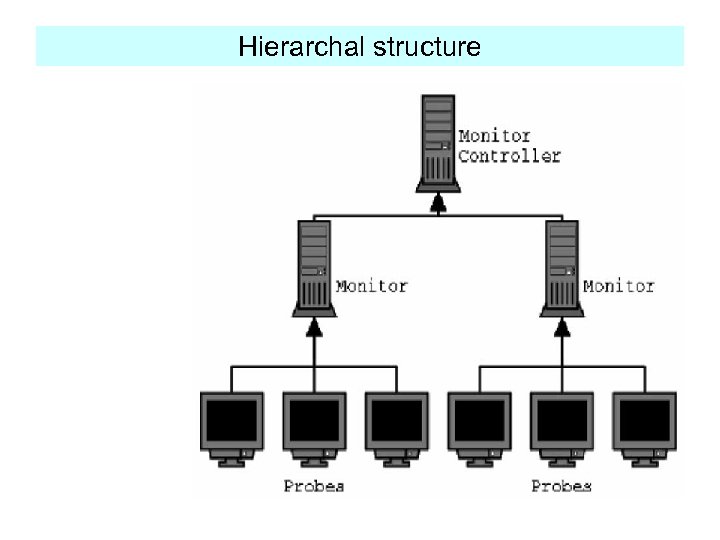
Hierarchal structure
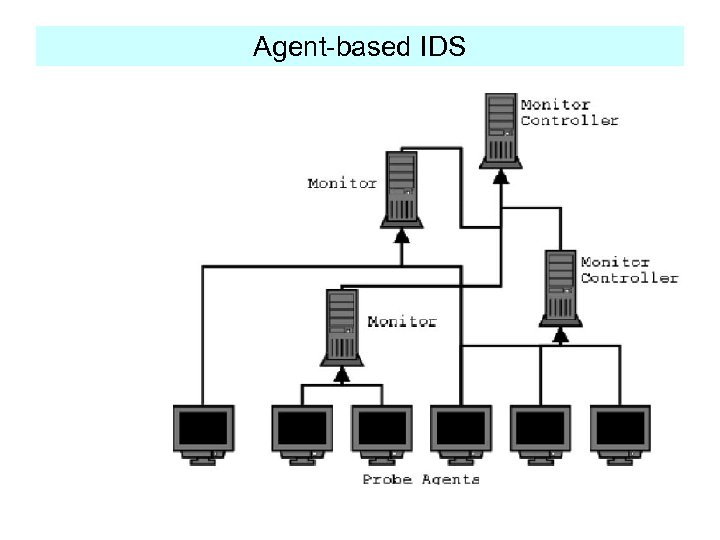
Agent-based IDS
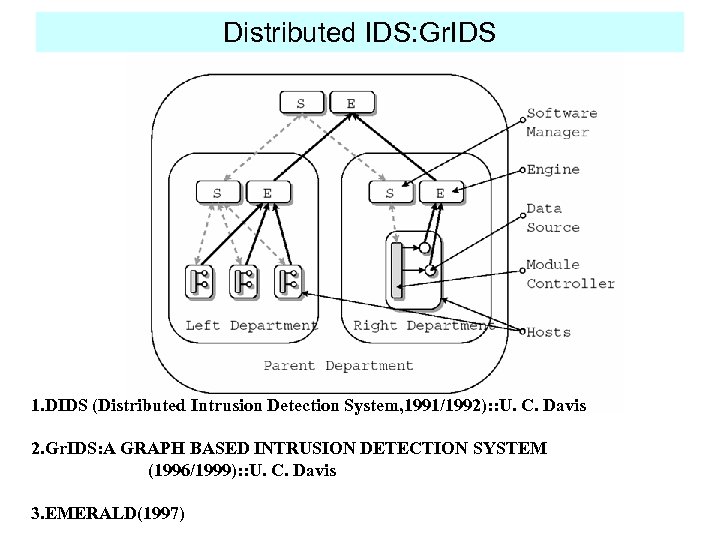
Distributed IDS: Gr. IDS 1. DIDS (Distributed Intrusion Detection System, 1991/1992): : U. C. Davis 2. Gr. IDS: A GRAPH BASED INTRUSION DETECTION SYSTEM (1996/1999): : U. C. Davis 3. EMERALD(1997)
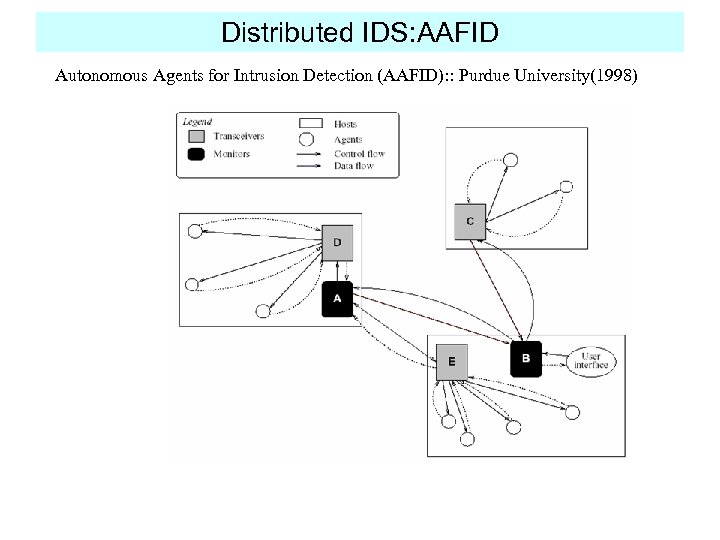
Distributed IDS: AAFID Autonomous Agents for Intrusion Detection (AAFID): : Purdue University(1998)
Data Source 1. Audit log: : SUN Solaris/BSM(Basic security Module) WINDOWS/Event log System log Linux/*BSD: : syslog App. Log too many, …. . 2. Network packet flow: 3. Windows registry: only for Windows Frank Apap, Andrew Honig, Shlomo Hershkop, Eleazar Eskin, and Sal Stolfo (Columbia University), RAID 2002, LNCS 2516, pp. 36– 53, 2002. ……
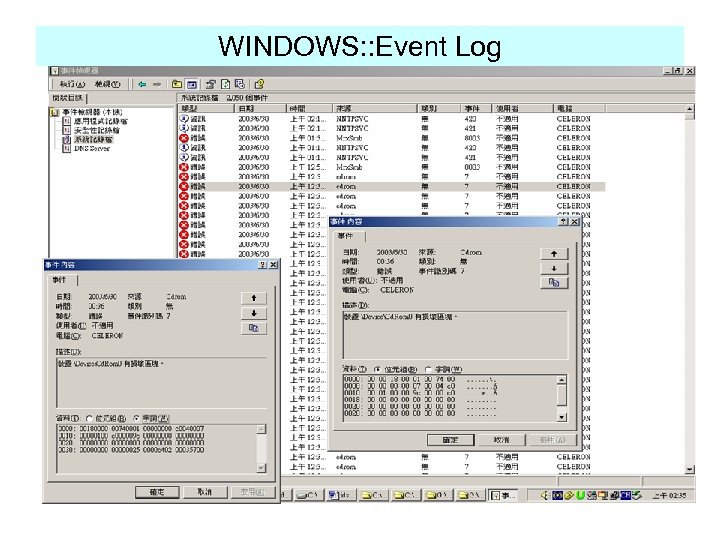
WINDOWS: : Event Log
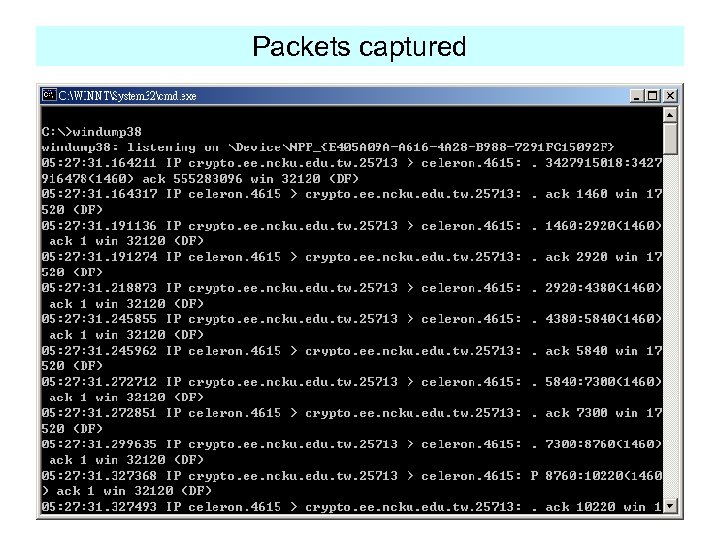
Packets captured
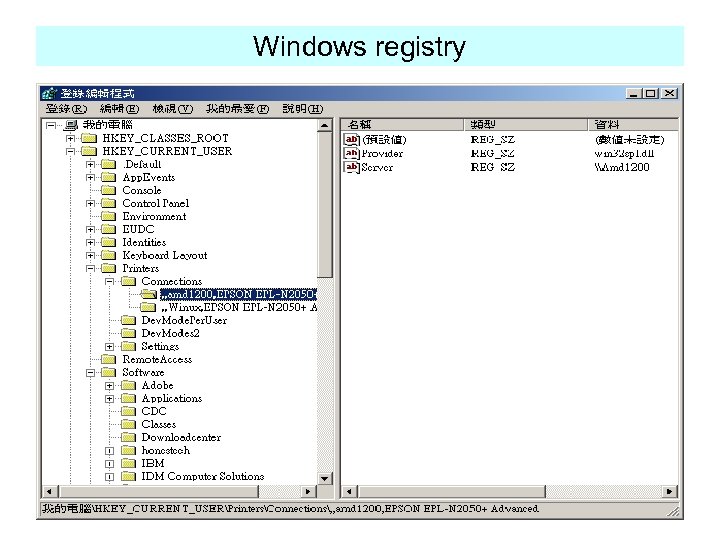
Windows registry
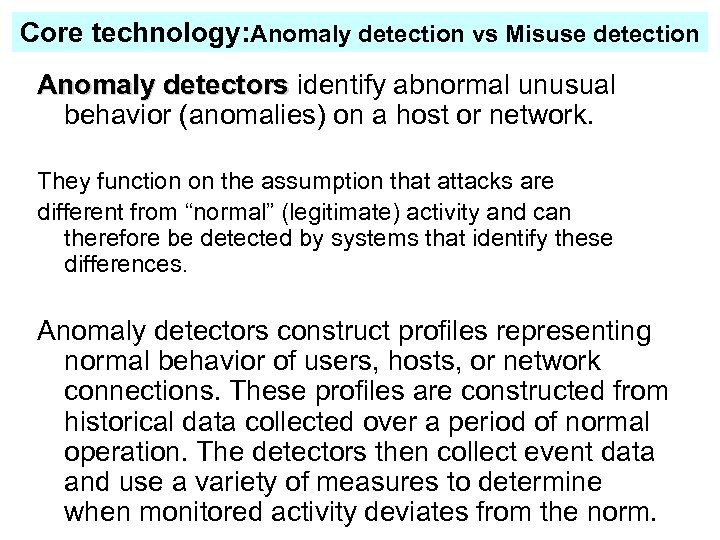
Core technology: Anomaly detection vs Misuse detection Anomaly detectors identify abnormal unusual detectors behavior (anomalies) on a host or network. They function on the assumption that attacks are different from “normal” (legitimate) activity and can therefore be detected by systems that identify these differences. Anomaly detectors construct profiles representing normal behavior of users, hosts, or network connections. These profiles are constructed from historical data collected over a period of normal operation. The detectors then collect event data and use a variety of measures to determine when monitored activity deviates from the norm.
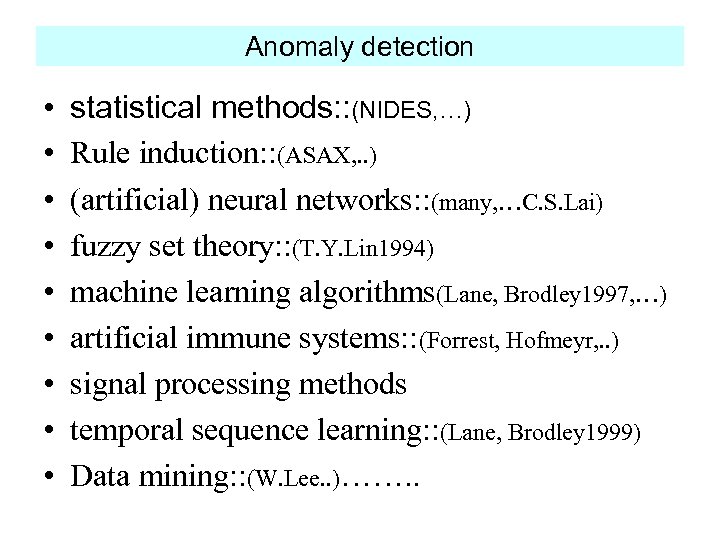
Anomaly detection • • • statistical methods: : (NIDES, …) Rule induction: : (ASAX, . . ) (artificial) neural networks: : (many, …C. S. Lai) fuzzy set theory: : (T. Y. Lin 1994) machine learning algorithms(Lane, Brodley 1997, …) artificial immune systems: : (Forrest, Hofmeyr, . . ) signal processing methods temporal sequence learning: : (Lane, Brodley 1999) Data mining: : (W. Lee. . )……. .
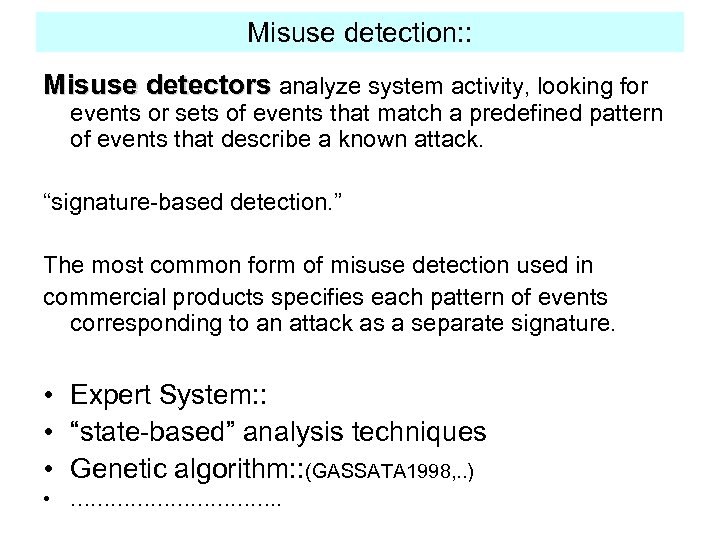
Misuse detection: : Misuse detectors analyze system activity, looking for events or sets of events that match a predefined pattern of events that describe a known attack. “signature-based detection. ” The most common form of misuse detection used in commercial products specifies each pattern of events corresponding to an attack as a separate signature. • Expert System: : • “state-based” analysis techniques • Genetic algorithm: : (GASSATA 1998, . . ) • ……………. .
Testing Environment and Test reports • Mitre(1997): Netranger, Realsecure, ASIM • Information Warfare Conf. (1998): Realsecure, NFR • MIT/Lincoln Labs(1998/1999): DARPAfunded • SANS 2000 ID-NET(2000. 3): Intrusiondetection-focused conf. • ………………. .
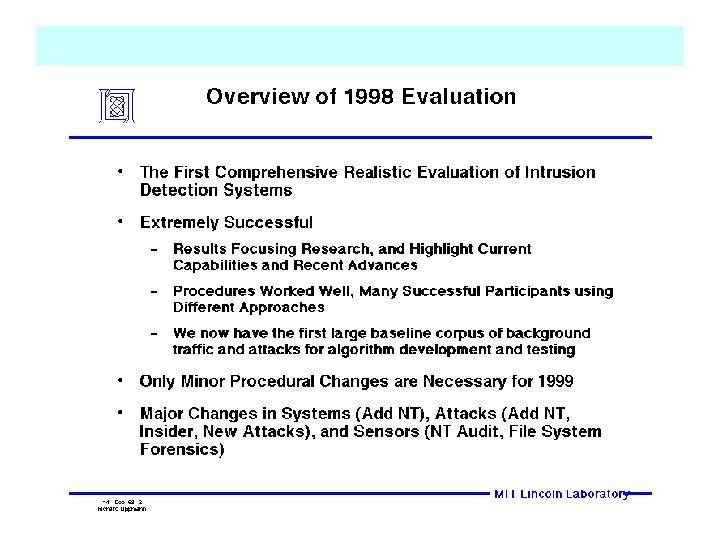
• 1998 DARPA Intrusion Detection Evaluation • 1999 DARPA Intrusion Detection Evaluation
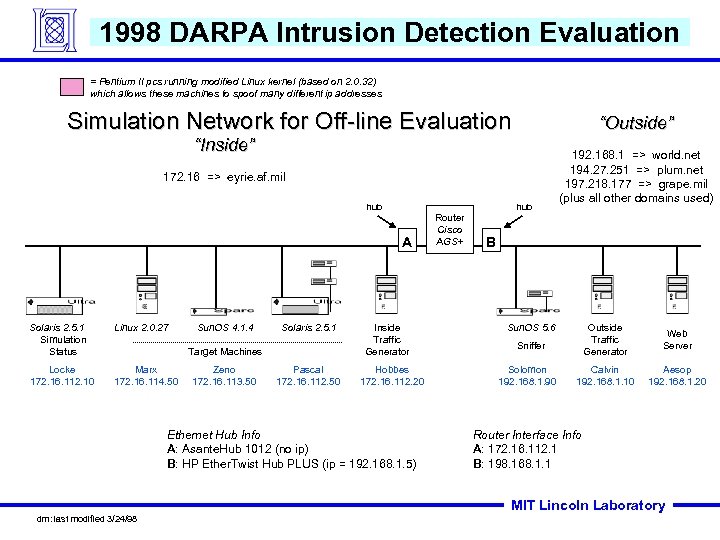
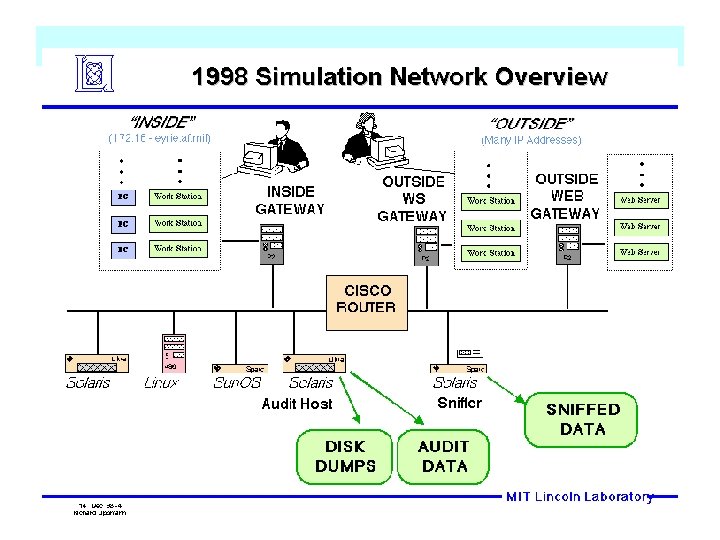
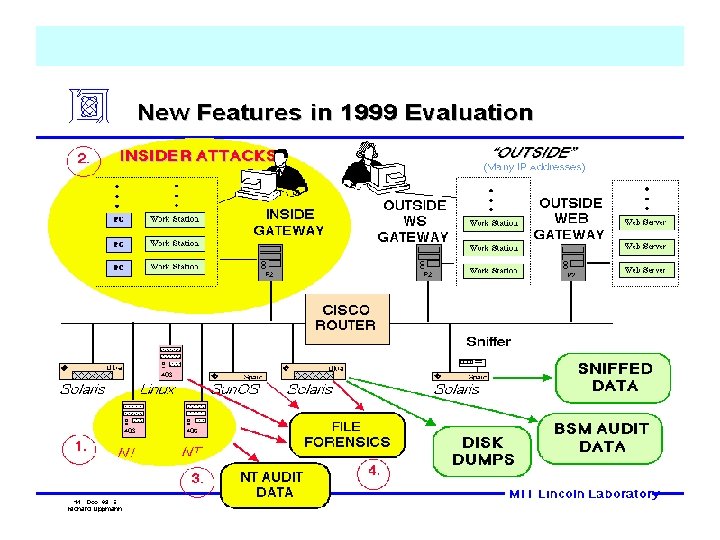
1998 DARPA Intrusion Detection Evaluation = Pentium II pcs running modified Linux kernel (based on 2. 0. 32) which allows these machines to spoof many different ip addresses Simulation Network for Off-line Evaluation “Outside” “Inside” 172. 16 => eyrie. af. mil hub A Solaris 2. 5. 1 Simulation Status Linux 2. 0. 27 Locke 172. 16. 112. 10 Marx 172. 16. 114. 50 Sun. OS 4. 1. 4 Solaris 2. 5. 1 Target Machines Zeno 172. 16. 113. 50 Pascal 172. 16. 112. 50 Inside Traffic Generator Hobbes 172. 16. 112. 20 Ethernet Hub Info A: Asante. Hub 1012 (no ip) B: HP Ether. Twist Hub PLUS (ip = 192. 168. 1. 5) Router Cisco AGS+ 192. 168. 1 => world. net 194. 27. 251 => plum. net 197. 218. 177 => grape. mil (plus all other domains used) B Sun. OS 5. 6 Outside Traffic Generator Web Server Calvin 192. 168. 1. 10 Aesop 192. 168. 1. 20 Sniffer Solomon 192. 168. 1. 90 Router Interface Info A: 172. 16. 112. 1 B: 198. 168. 1. 1 MIT Lincoln Laboratory dm: last modified 3/24/98
•
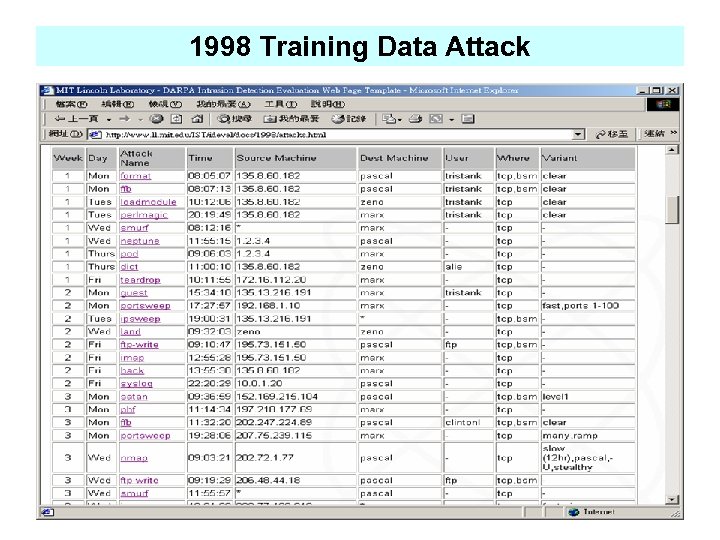
1998 Training Data Attack
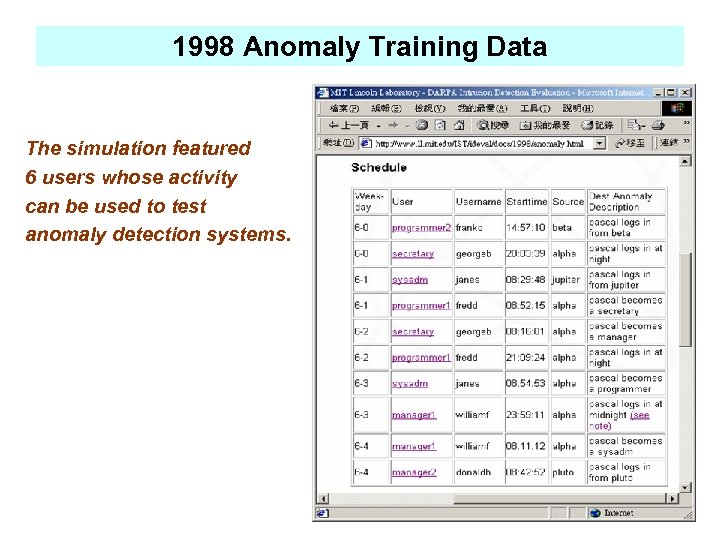
1998 Anomaly Training Data The simulation featured 6 users whose activity can be used to test anomaly detection systems.
Test the following types of misuse 1. Denial of service 2. Unauthorized access from a remote machine 3. Unauthorized transition to root by an unprivileged user 4. Surveillance and probing 5. Anomalous user behavior
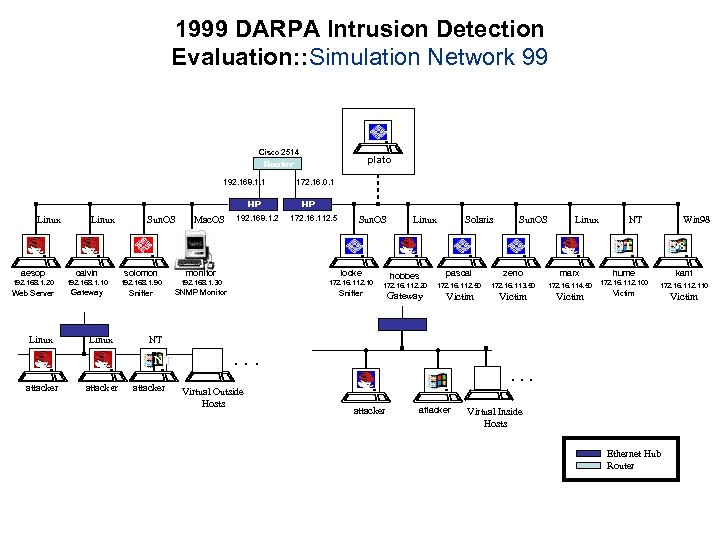
1999 DARPA Intrusion Detection Evaluation: : Simulation Network 99 Cisco 2514 Router CISCO 192. 168. 1. 1 172. 16. 0. 1 HP Linux Sun. OS Mac. OS 192. 168. 1. 2 plato HP 172. 16. 112. 5 Sun. OS Linux Solaris Sun. OS Linux NT Win 98 NT aesop calvin solomon monitor locke 192. 168. 1. 20 192. 168. 1. 10 192. 168. 1. 90 192. 168. 1. 30 172. 16. 112. 10 Web Server Gateway Sniffer SNMP Monitor Sniffer Linux attacker hobbes pascal zeno marx hume kant 172. 16. 112. 20 172. 16. 112. 50 172. 16. 113. 50 172. 16. 114. 50 172. 16. 112. 100 172. 16. 112. 110 Gateway Victim NT NT attacker 98 attacker . . . Virtual Outside Hosts attacker Virtual Inside Hosts Ethernet Hub Router Victim
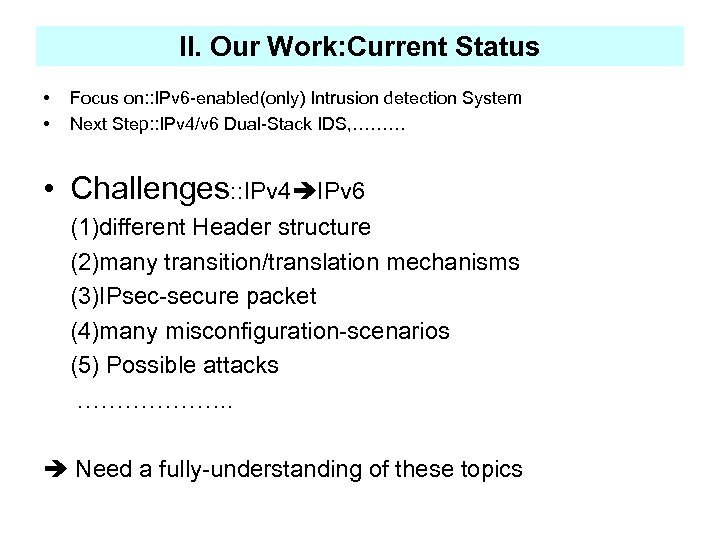
II. Our Work: Current Status • • Focus on: : IPv 6 -enabled(only) Intrusion detection System Next Step: : IPv 4/v 6 Dual-Stack IDS, ……… • Challenges: : IPv 4 IPv 6 (1)different Header structure (2)many transition/translation mechanisms (3)IPsec-secure packet (4)many misconfiguration-scenarios (5) Possible attacks ………………. . Need a fully-understanding of these topics
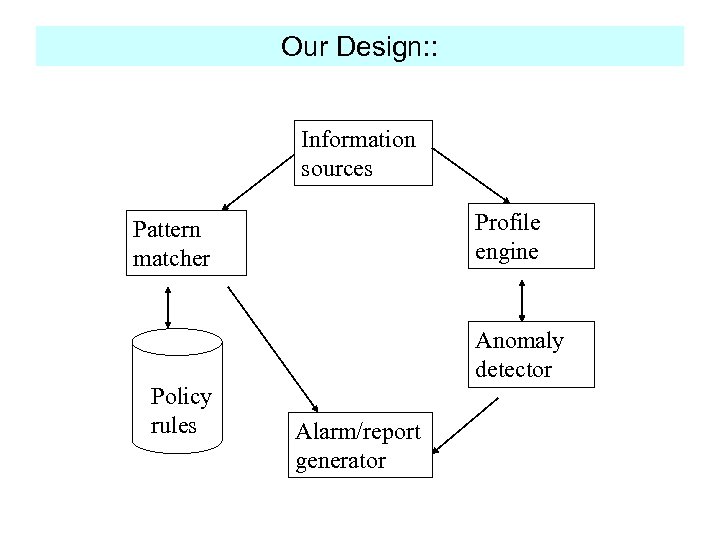
Our Design: : Information sources Profile engine Pattern matcher Anomaly detector Policy rules Alarm/report generator
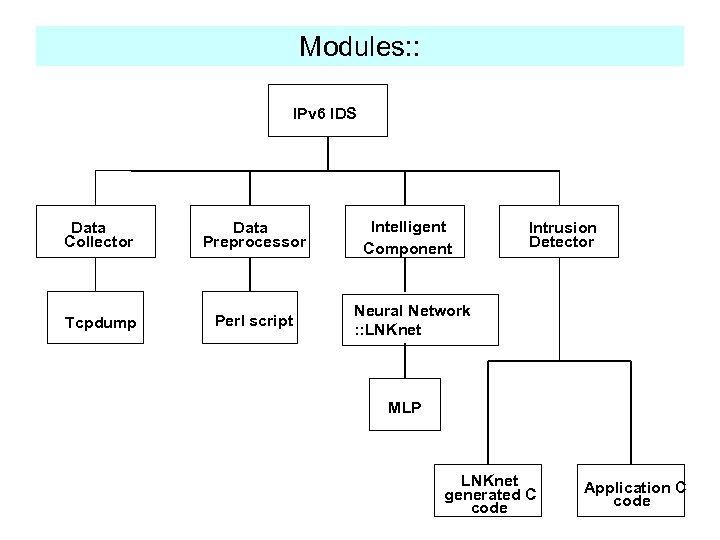
Modules: : IPv 6 IDS Data Collector Data Preprocessor Tcpdump Perl script Intelligent Component Intrusion Detector Neural Network : : LNKnet MLP LNKnet generated C code Application C code
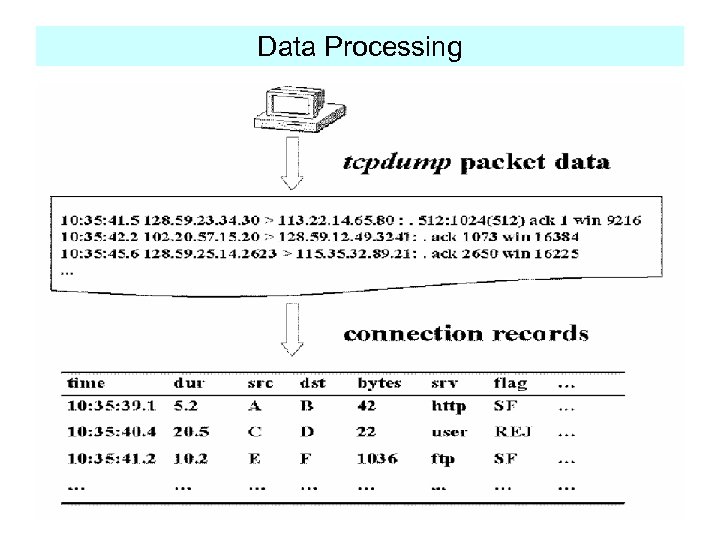
Data Processing
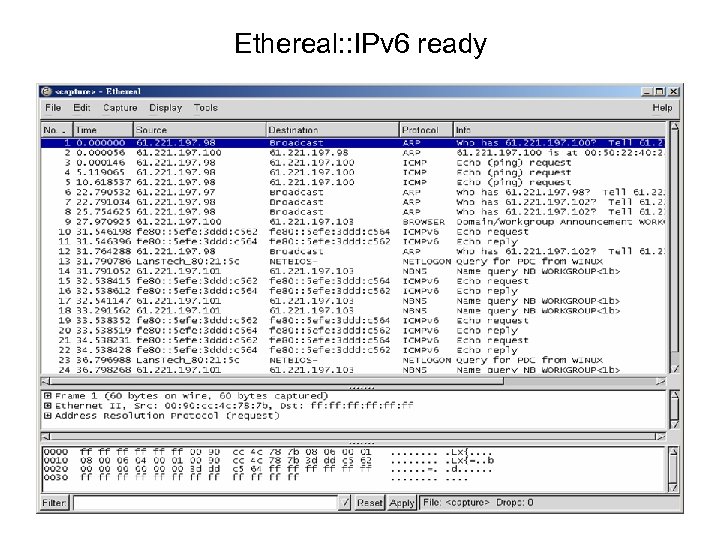
Ethereal: : IPv 6 ready
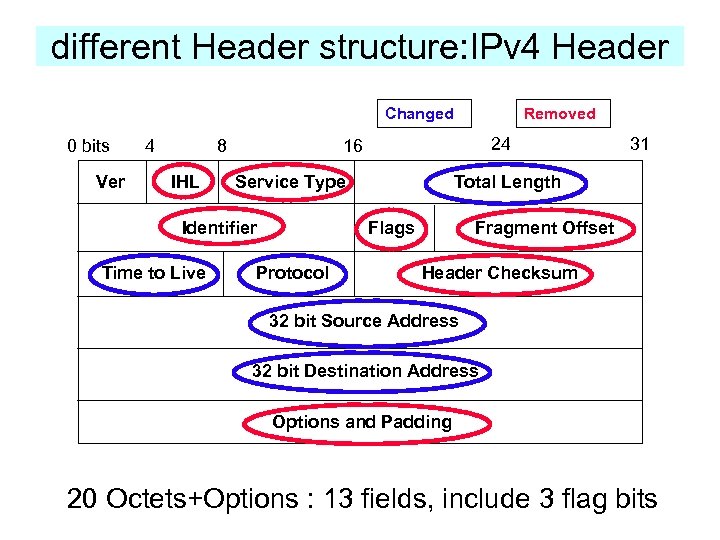
different Header structure: IPv 4 Header Changed 0 bits Ver 4 8 IHL 24 16 Service Type Identifier Time to Live Removed Total Length Flags Protocol 31 Fragment Offset Header Checksum 32 bit Source Address 32 bit Destination Address Options and Padding 20 Octets+Options : 13 fields, include 3 flag bits
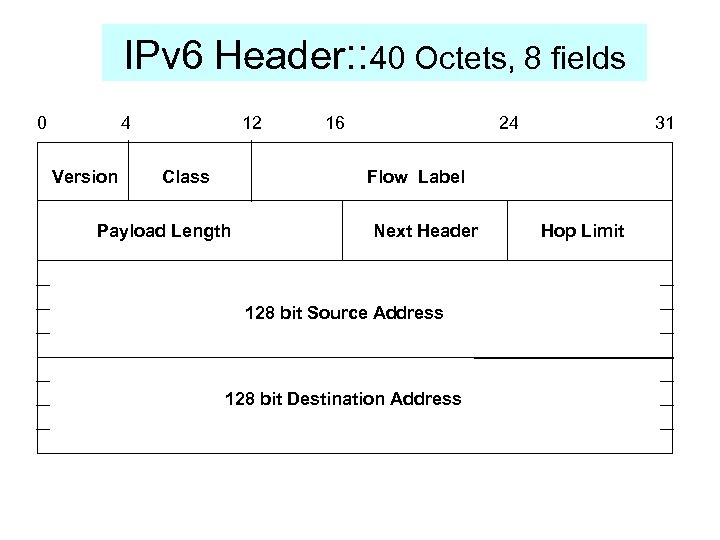
IPv 6 Header: : 40 Octets, 8 fields 0 4 Version 12 Class 16 24 31 Flow Label Payload Length Next Header 128 bit Source Address 128 bit Destination Address Hop Limit
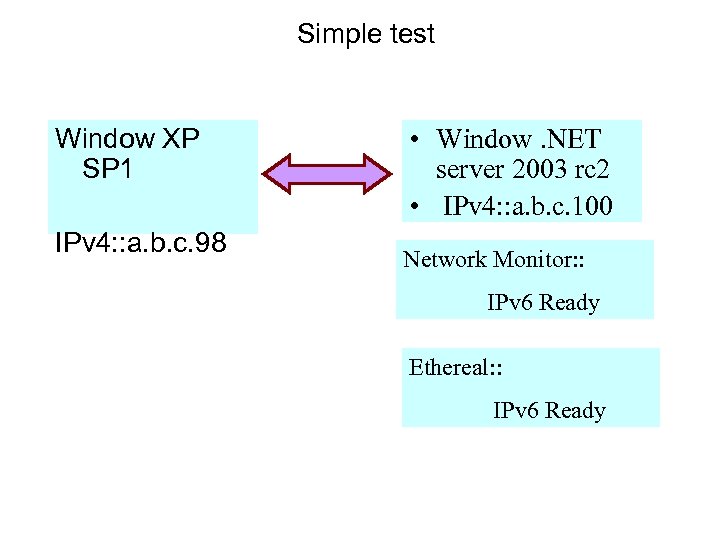
Simple test Window XP SP 1 IPv 4: : a. b. c. 98 • Window. NET server 2003 rc 2 • IPv 4: : a. b. c. 100 Network Monitor: : IPv 6 Ready Ethereal: : IPv 6 Ready
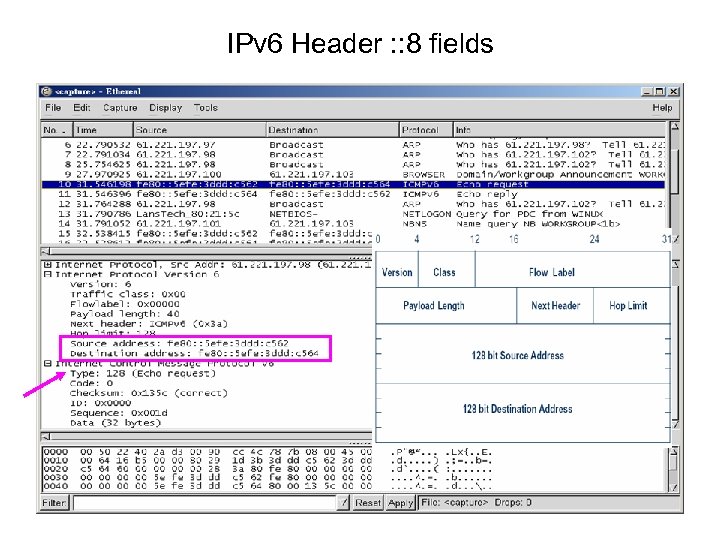
IPv 6 Header : : 8 fields
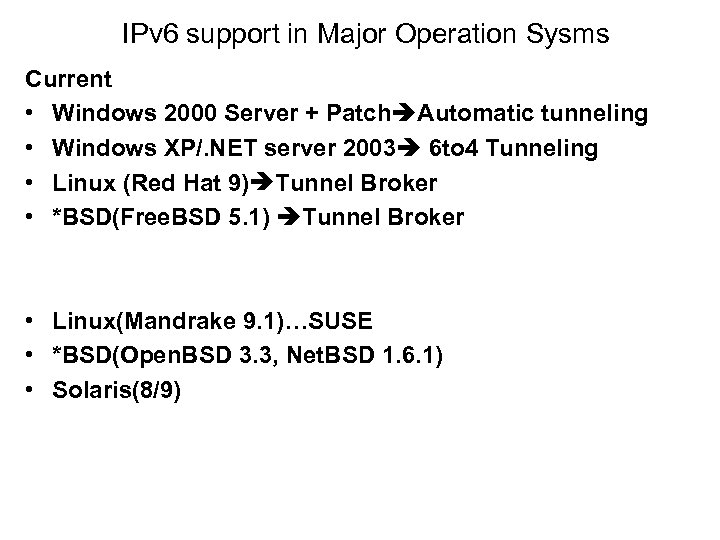
IPv 6 support in Major Operation Sysms Current • Windows 2000 Server + Patch Automatic tunneling • Windows XP/. NET server 2003 6 to 4 Tunneling • Linux (Red Hat 9) Tunnel Broker • *BSD(Free. BSD 5. 1) Tunnel Broker • Linux(Mandrake 9. 1)…SUSE • *BSD(Open. BSD 3. 3, Net. BSD 1. 6. 1) • Solaris(8/9)
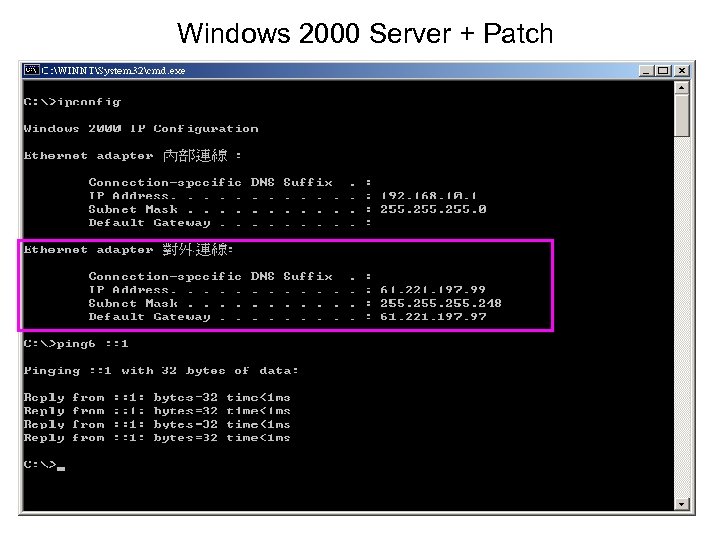
Windows 2000 Server + Patch
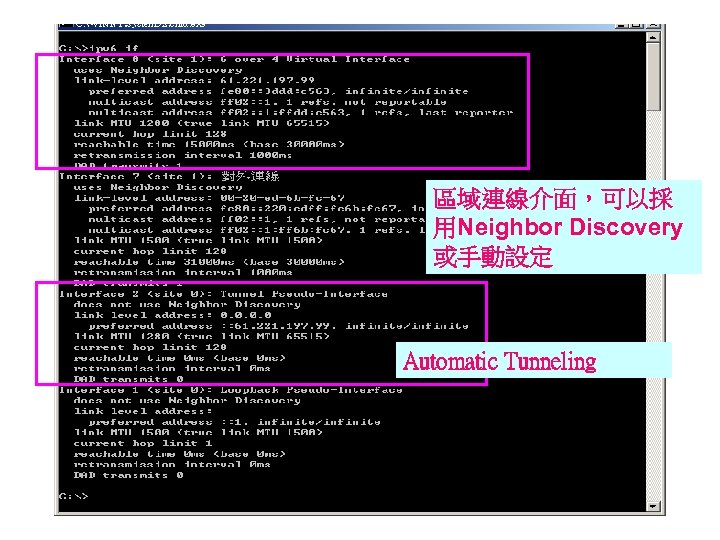
區域連線介面,可以採 用Neighbor Discovery 或手動設定 Automatic Tunneling
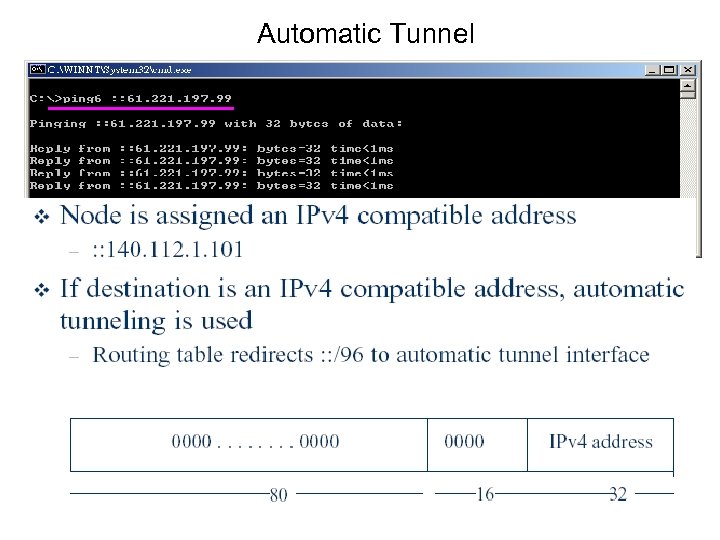
Automatic Tunnel
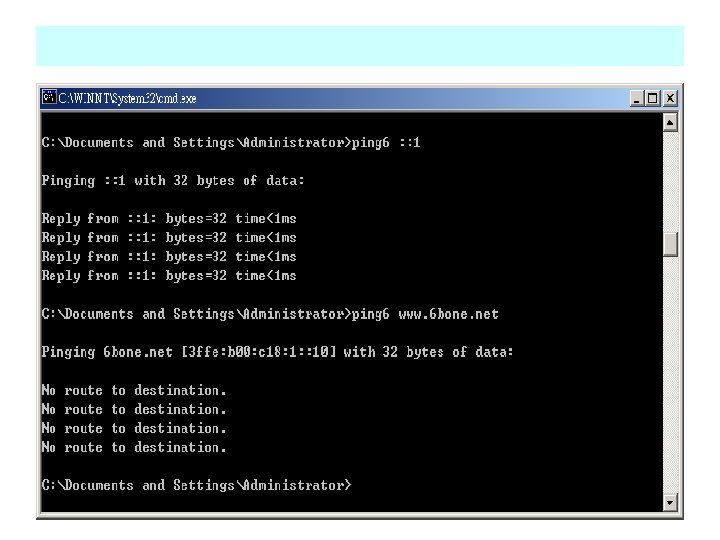
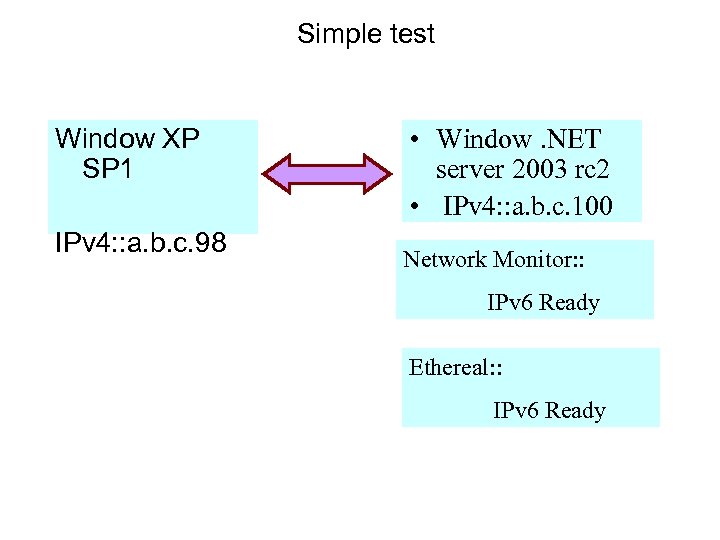
Simple test Window XP SP 1 IPv 4: : a. b. c. 98 • Window. NET server 2003 rc 2 • IPv 4: : a. b. c. 100 Network Monitor: : IPv 6 Ready Ethereal: : IPv 6 Ready
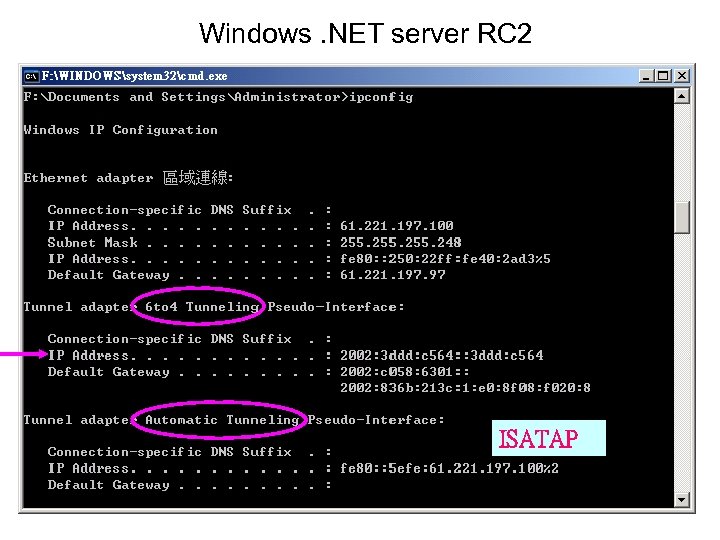
Windows. NET server RC 2 ISATAP
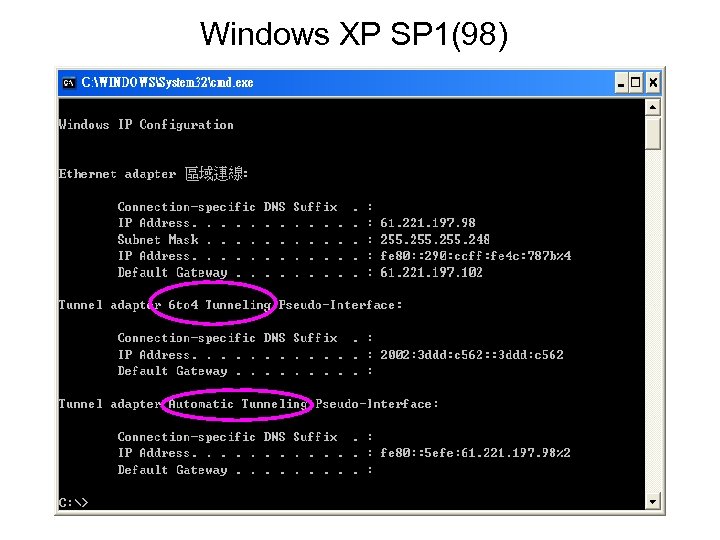
Windows XP SP 1(98)
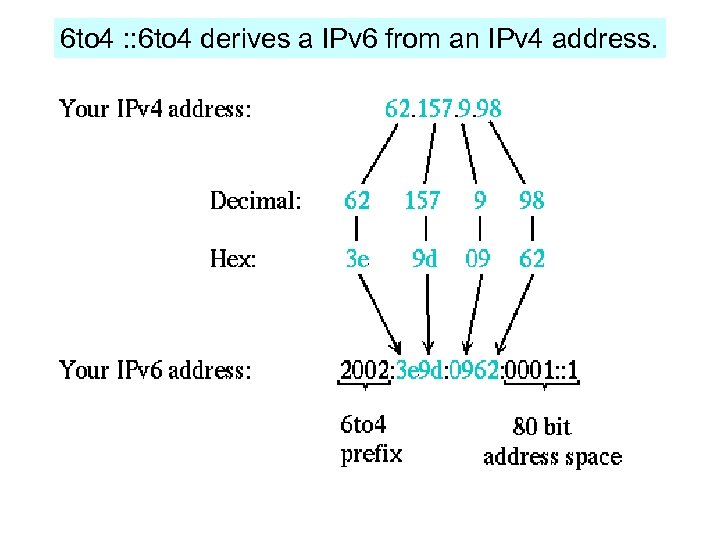
6 to 4 : : 6 to 4 derives a IPv 6 from an IPv 4 address.
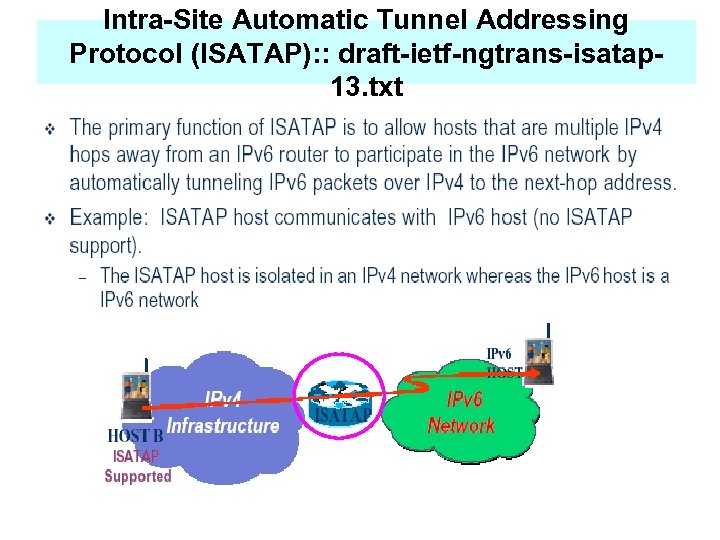
Intra-Site Automatic Tunnel Addressing Protocol (ISATAP): : draft-ietf-ngtrans-isatap 13. txt
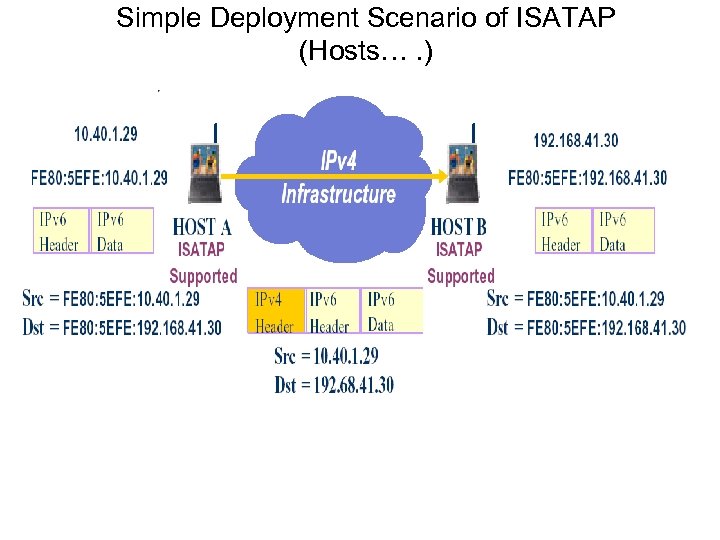
Simple Deployment Scenario of ISATAP (Hosts…. )
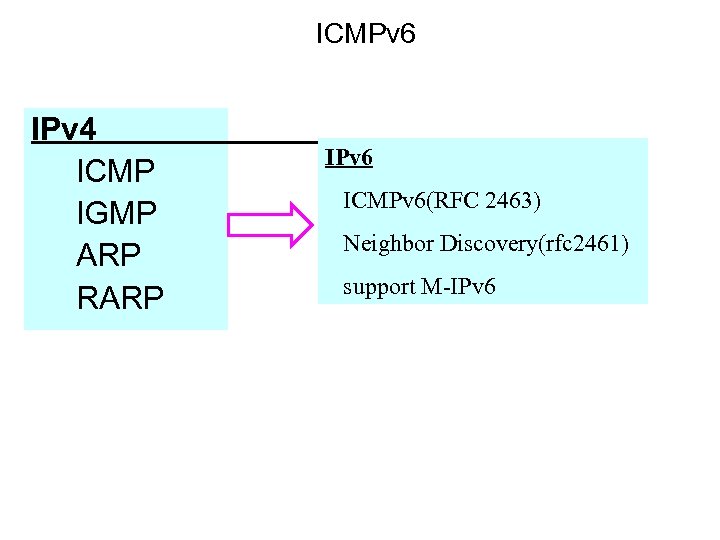
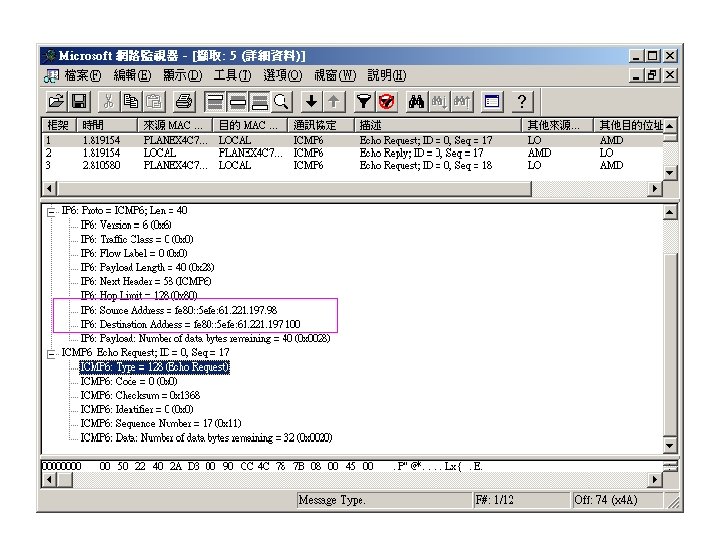
ICMPv 6 IPv 4 ICMP IGMP ARP RARP IPv 6 ICMPv 6(RFC 2463) Neighbor Discovery(rfc 2461) support M-IPv 6
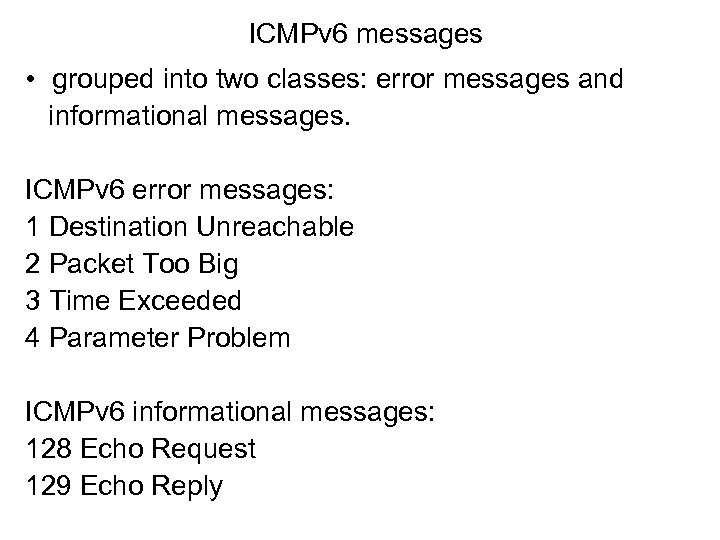
ICMPv 6 messages • grouped into two classes: error messages and informational messages. ICMPv 6 error messages: 1 Destination Unreachable 2 Packet Too Big 3 Time Exceeded 4 Parameter Problem ICMPv 6 informational messages: 128 Echo Request 129 Echo Reply
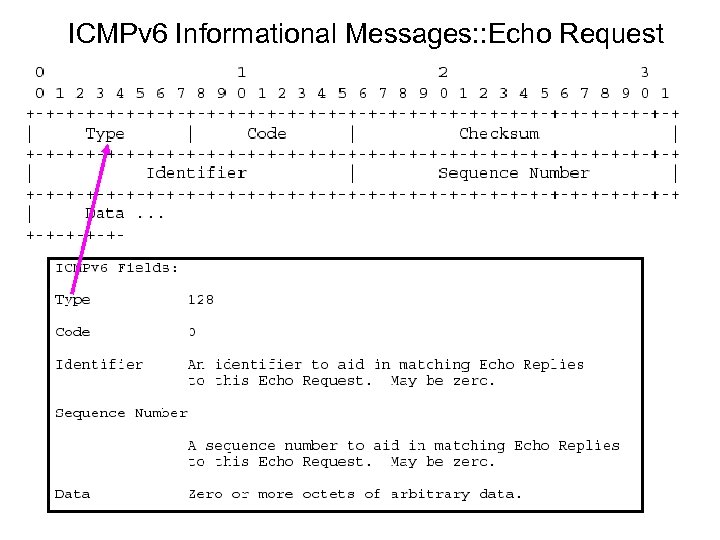
ICMPv 6 Informational Messages: : Echo Request
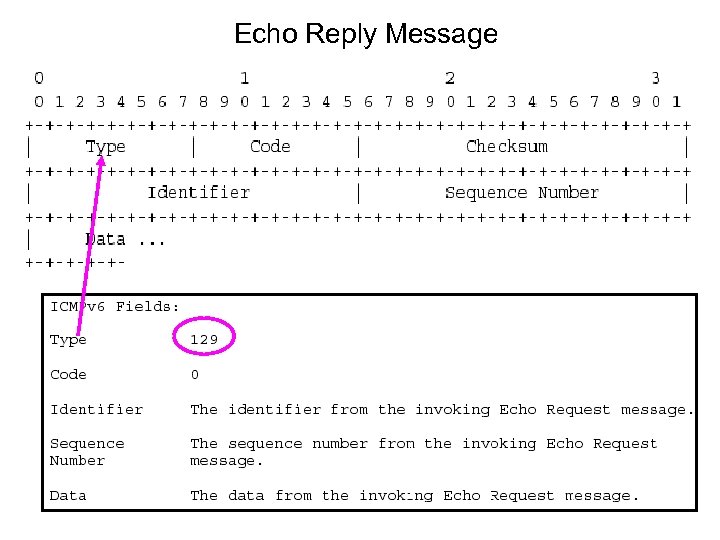
Echo Reply Message
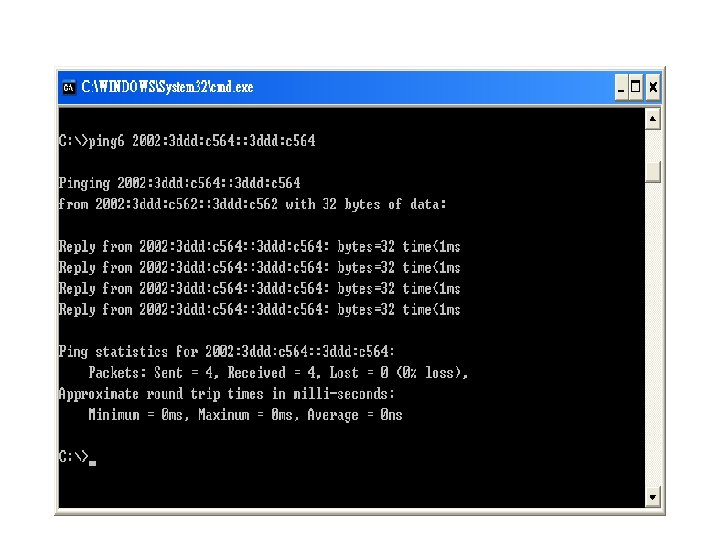
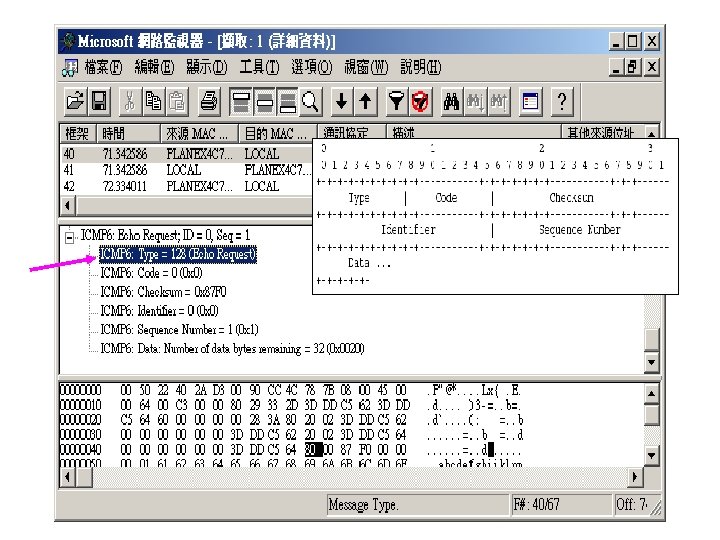
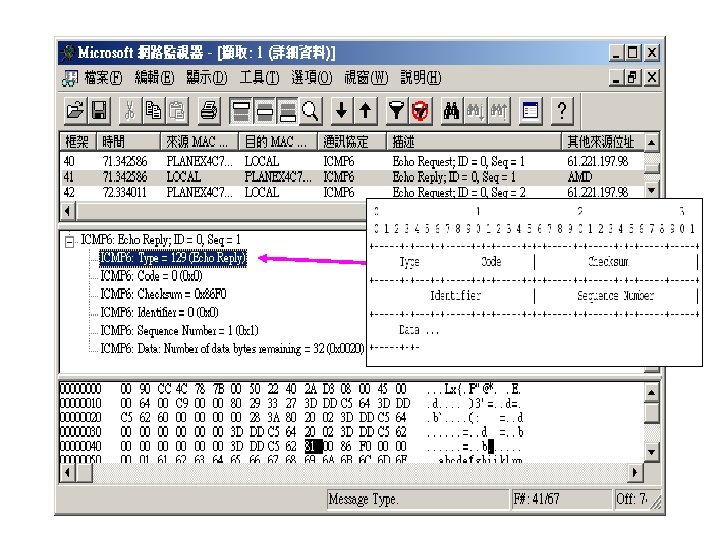
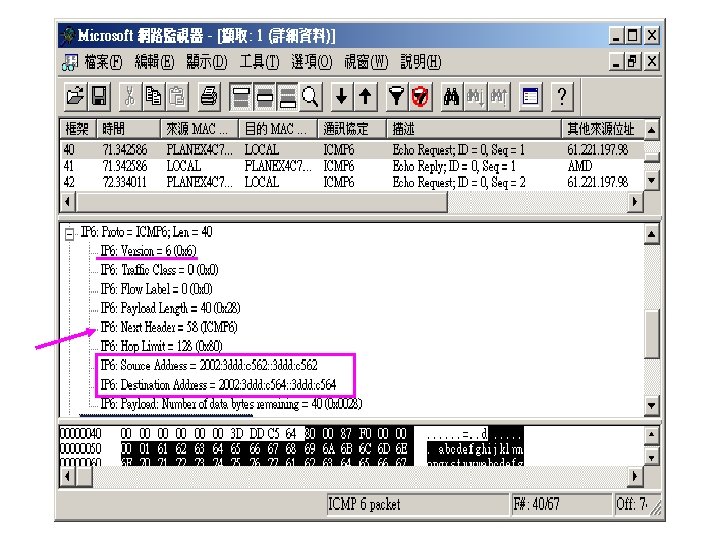
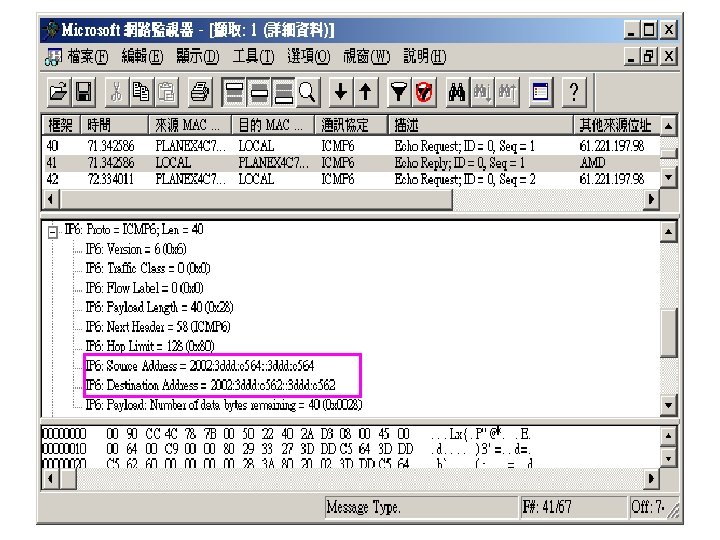
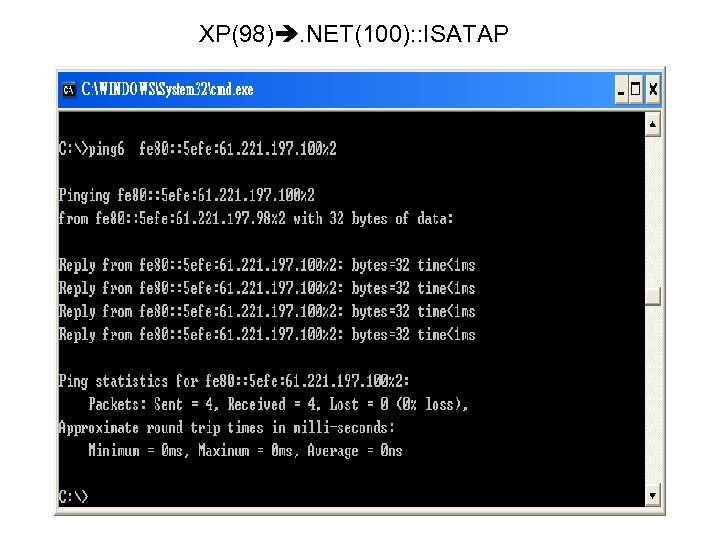
XP(98). NET(100): : ISATAP
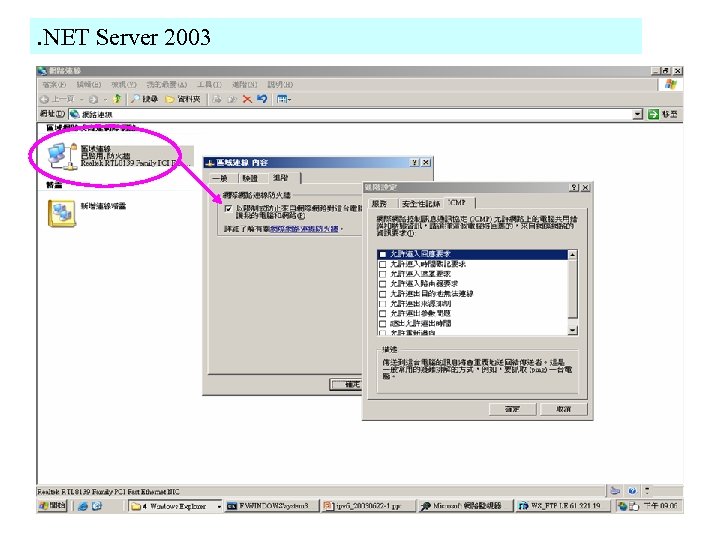
. NET Server 2003
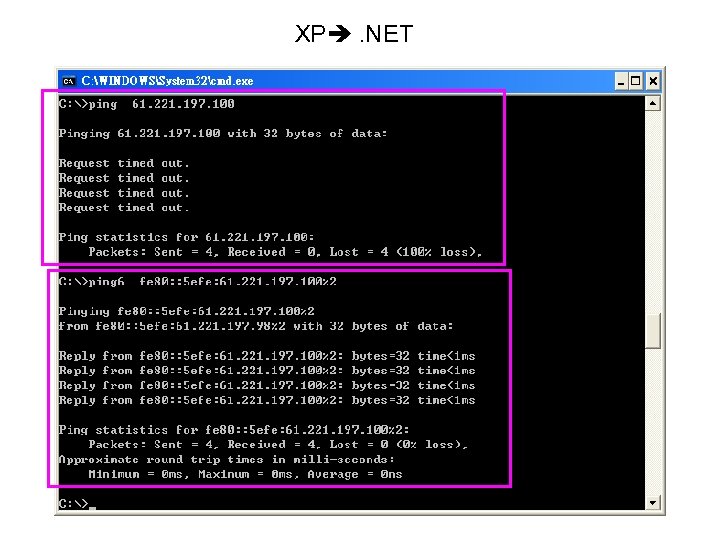
XP . NET
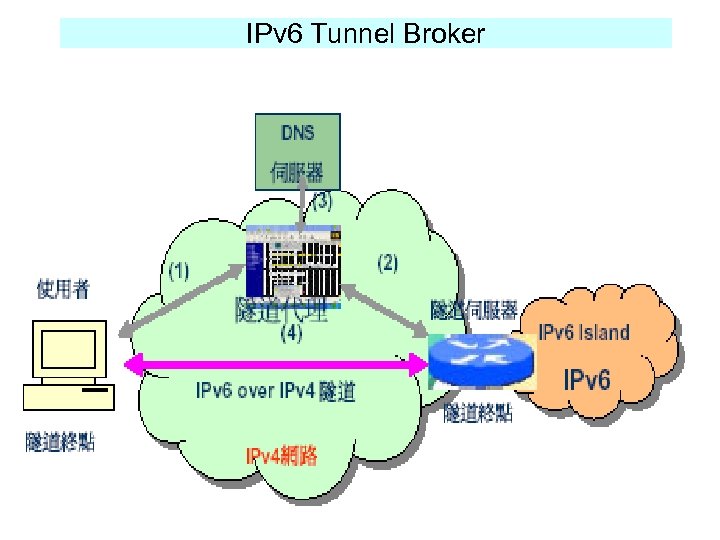
IPv 6 Tunnel Broker
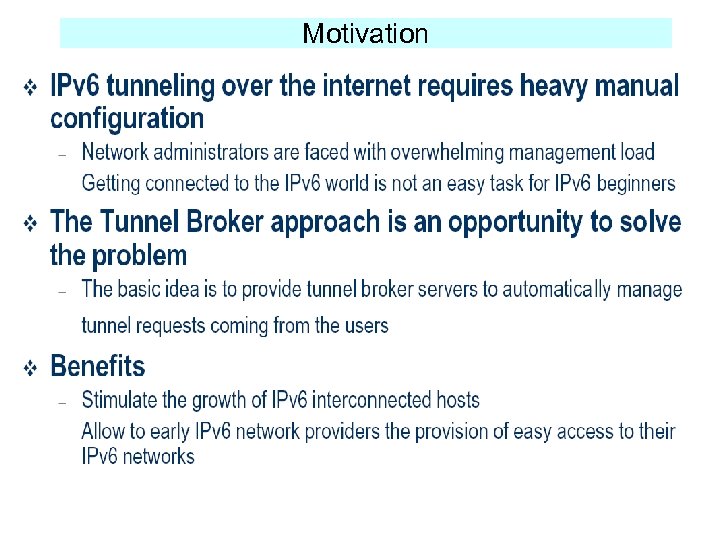
Motivation
Tunnel Broker Virtual IPv 6 ISP
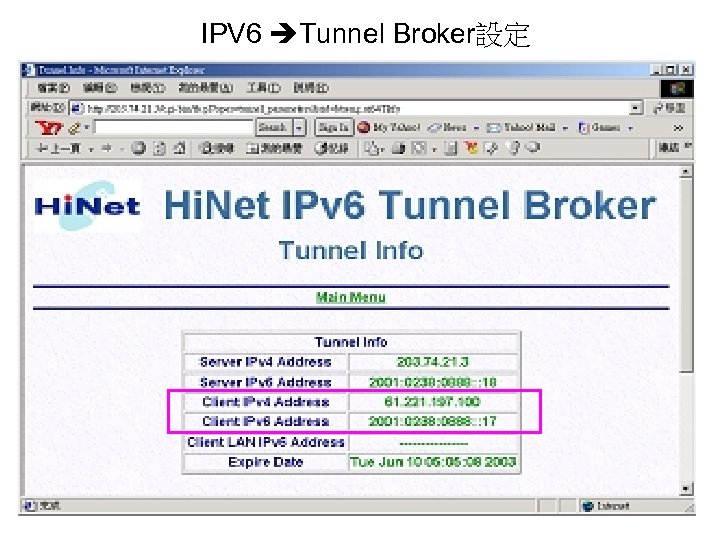
IPV 6 Tunnel Broker設定
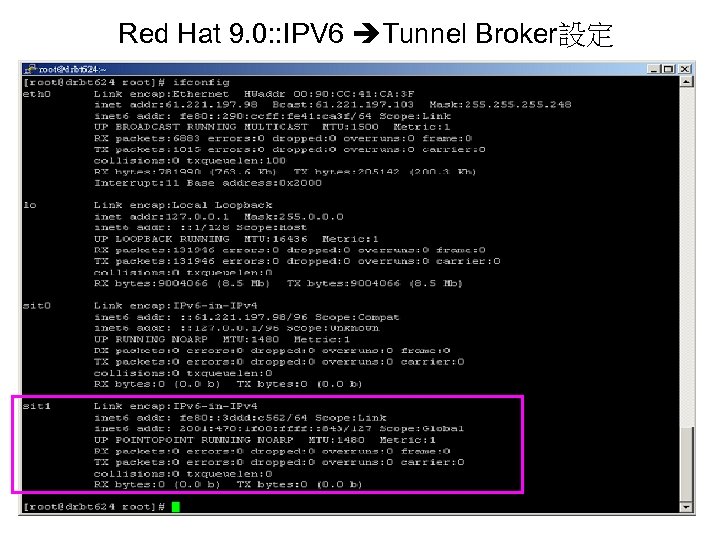
Red Hat 9. 0: : IPV 6 Tunnel Broker設定
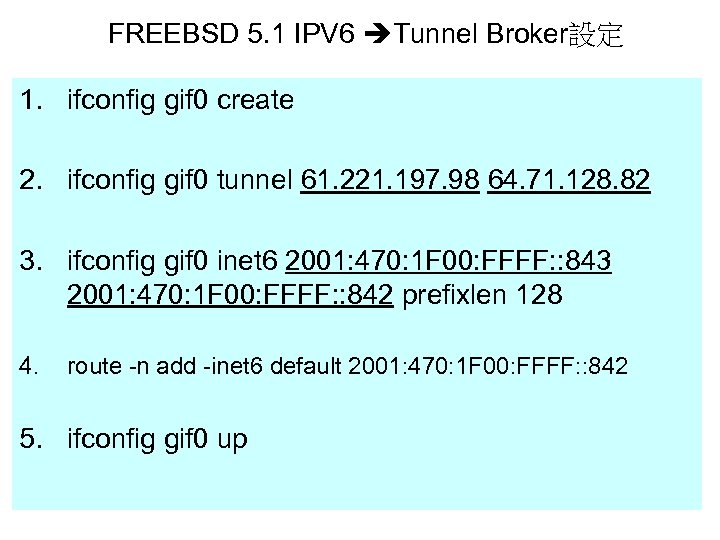
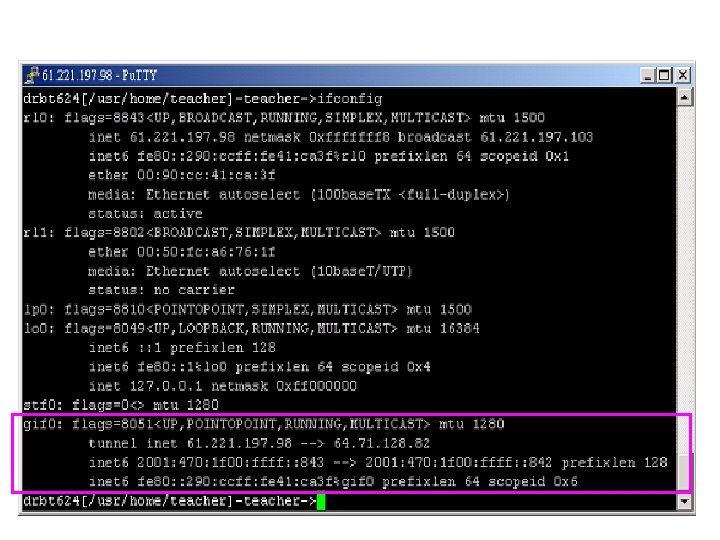
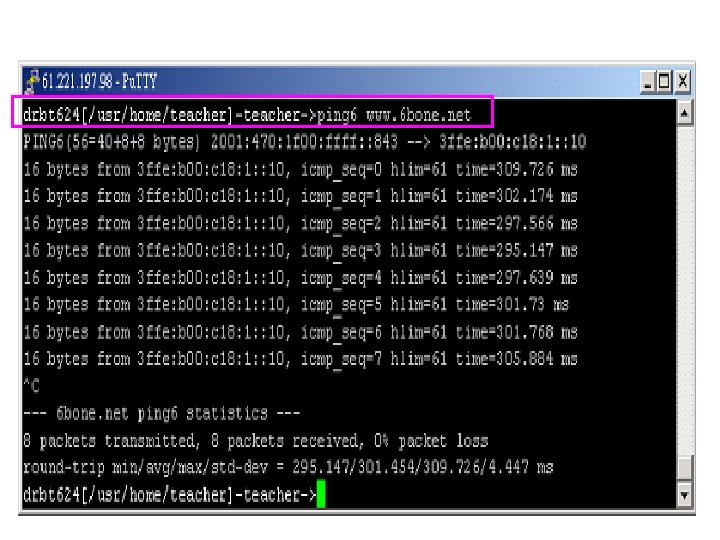
FREEBSD 5. 1 IPV 6 Tunnel Broker設定 1. ifconfig gif 0 create 2. ifconfig gif 0 tunnel 61. 221. 197. 98 64. 71. 128. 82 3. ifconfig gif 0 inet 6 2001: 470: 1 F 00: FFFF: : 843 2001: 470: 1 F 00: FFFF: : 842 prefixlen 128 4. route -n add -inet 6 default 2001: 470: 1 F 00: FFFF: : 842 5. ifconfig gif 0 up
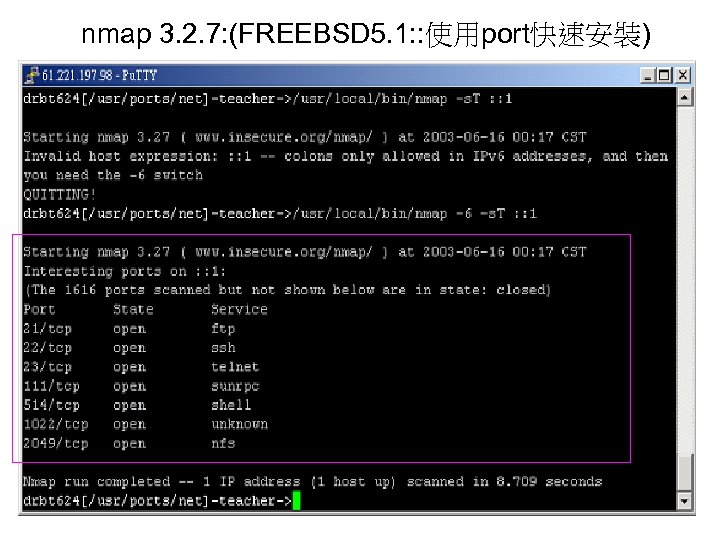
nmap 3. 2. 7: (FREEBSD 5. 1: : 使用port快速安裝)
Further Works: In the near future • A IPv 6 testbed with different OS and server will be built up • More packets captured and audit logs will be analyzed • A prototype will be built up • Some simple attacks will be tested
計畫名稱:結合IC卡的IPv 6安全 機制設計與實現 計畫主持人:楊中皇 博士 報告人:翁木龍
報告大綱 n n n 研究架構 IPSec機制 IC卡的優點 計畫執行進度 後續 作
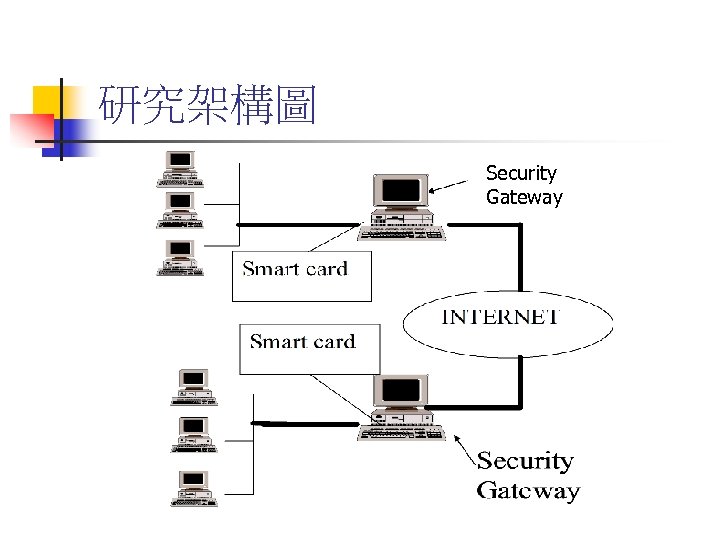
研究架構圖 Security Gateway
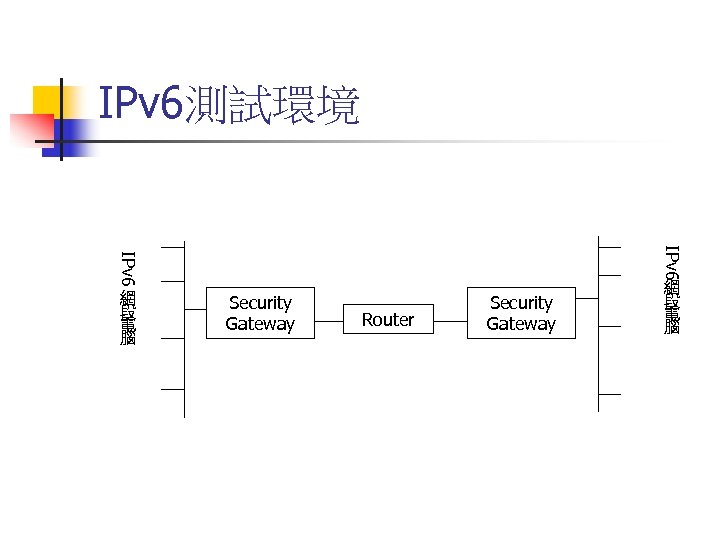
IPv 6測試環境 IPv 6 網 段 電 腦 Security Gateway Router Security Gateway 網 段 電 腦
預期研究成果 n n 在linux環境中,將身分認證的KEY放在IC 卡中,以提高IPSec通訊安全 架構出IPv 6之VPN環境,建立屬於自己的 私有網路,保障網路互連之安全性及隱 私性
IPSec n n IETF(Internet Engineering Task Force)所訂定 的一套開放標準網路安全協定IPSec(IP Security),將密碼學的技術應用在網路層,以 提供傳送、接收端做資料的認證 (Authentication)、完整性(Integrity)、存取控 制(Access Control)以及機密性(Confidentiality) 等安全服務。 IPSec 在IPv 4與IPv 6: n n IPv 4: 隨意的(Optional) IPv 6: 強制的(Mandatory)
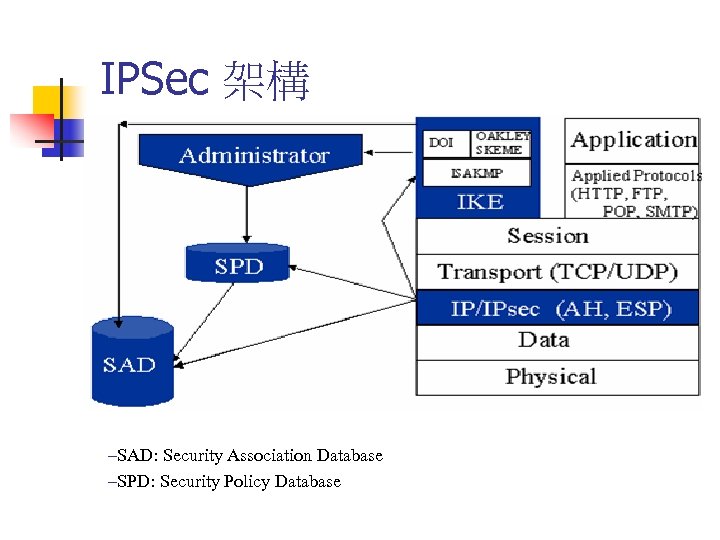
IPSec 架構 –SAD: Security Association Database –SPD: Security Policy Database
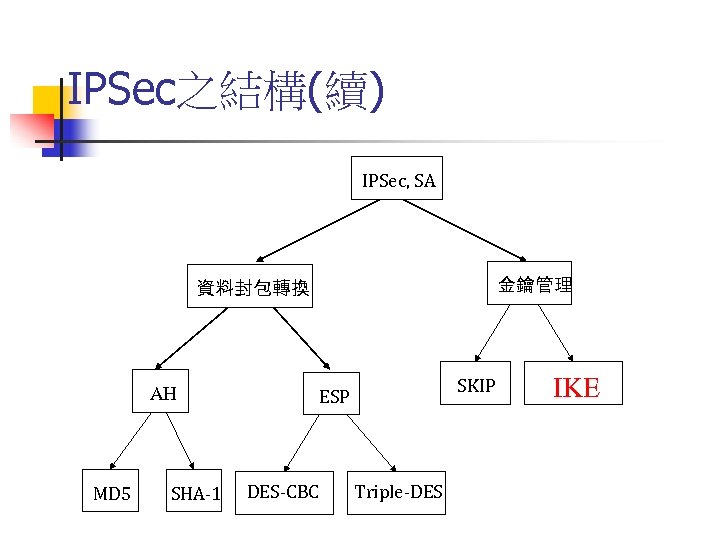
IPSec之結構(續) IPSec, SA 金鑰管理 資料封包轉換 AH MD 5 SHA-1 SKIP ESP DES-CBC Triple-DES IKE
IPSec的金鑰交換與管理 n n n 運用IPSec的實體兩端必須建立一組相對應 的加解密及驗證金鑰才能達到安全的目的 密鑰可以用人 手動或系統自動的方式交換 IETF定義了一組金鑰交換的通訊協定 Internet Key Exchange(IKE) ,可自動交換 密鑰
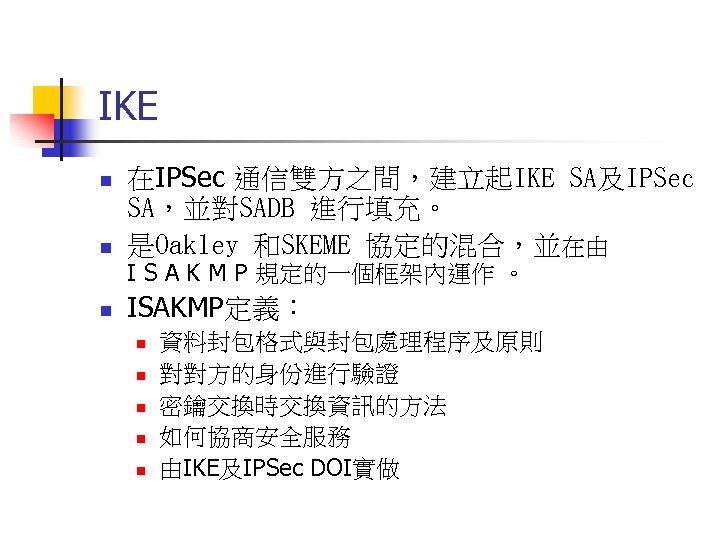
IKE n 在IPSec 通信雙方之間,建立起IKE SA及IPSec SA,並對SADB 進行填充。 是Oakley 和SKEME 協定的混合,並在由 n ISAKMP定義: n I S A K M P 規定的一個框架內運作 。 n n n 資料封包格式與封包處理程序及原則 對對方的身份進行驗證 密鑰交換時交換資訊的方法 如何協商安全服務 由IKE及IPSec DOI實做
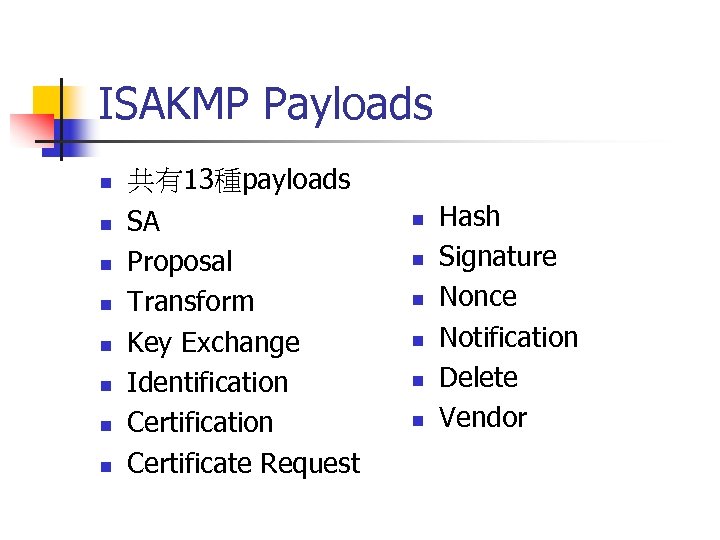
ISAKMP Payloads n n n n 共有13種payloads SA Proposal Transform Key Exchange Identification Certificate Request n n n Hash Signature Nonce Notification Delete Vendor
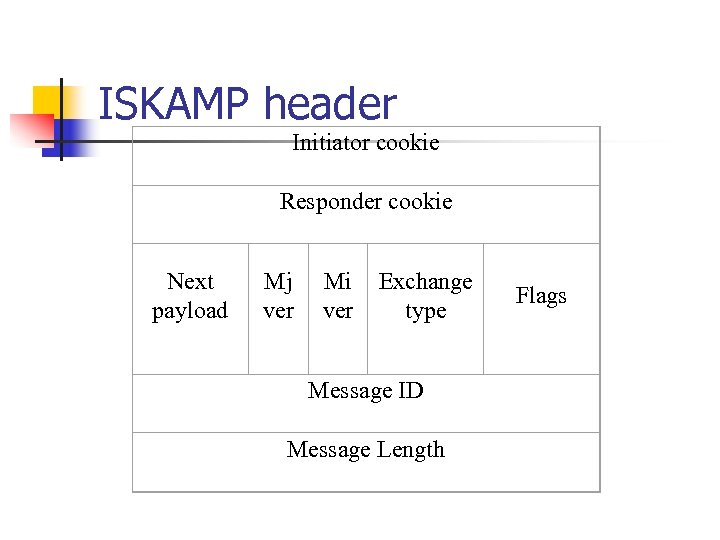
ISKAMP header Initiator cookie Responder cookie Next payload Mj ver Mi ver Exchange type Message ID Message Length Flags
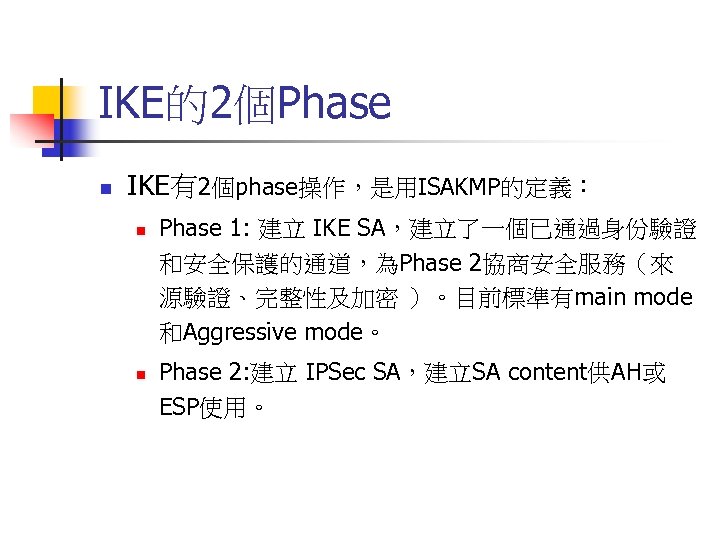
IKE的2個Phase n IKE有2個phase操作,是用ISAKMP的定義︰ n n Phase 1: 建立 IKE SA,建立了一個已通過身份驗證 和安全保護的通道,為Phase 2協商安全服務(來 源驗證、完整性及加密 )。目前標準有main mode 和Aggressive mode。 Phase 2: 建立 IPSec SA,建立SA content供AH或 ESP使用。
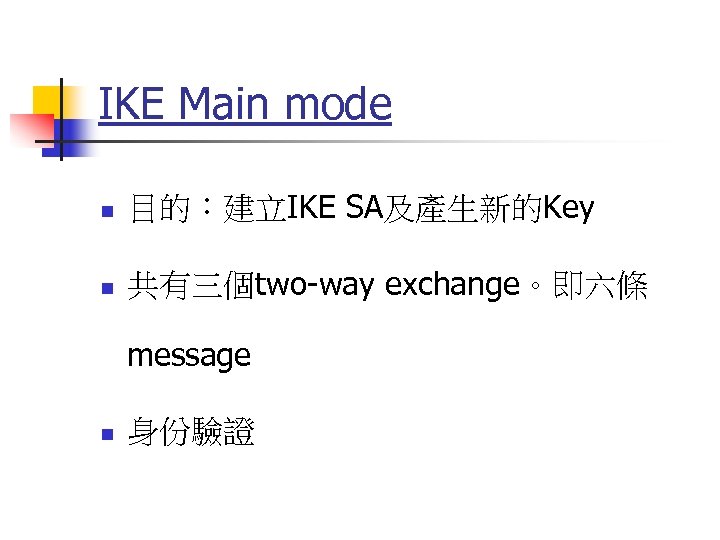
IKE Main mode n 目的︰建立IKE SA及產生新的Key n 共有三個two-way exchange。即六條 message n 身份驗證
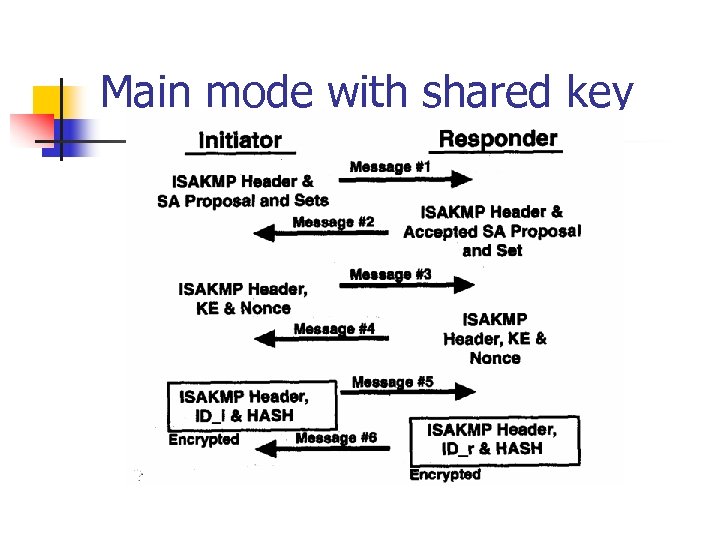
Main mode with shared key
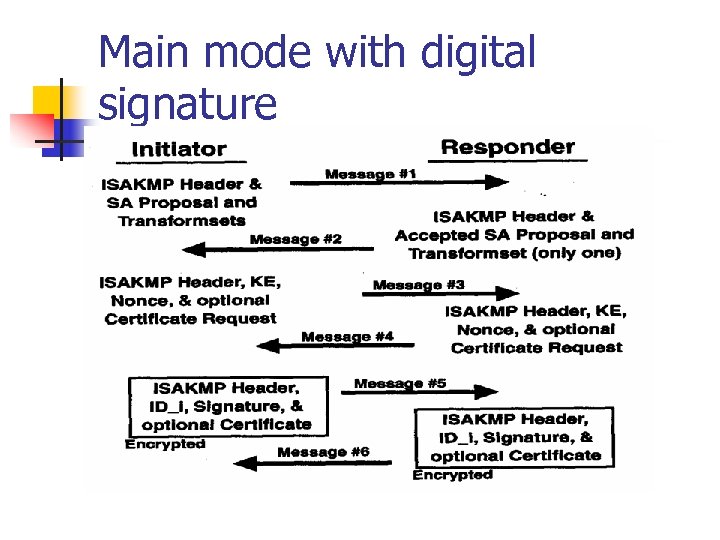
Main mode with digital signature
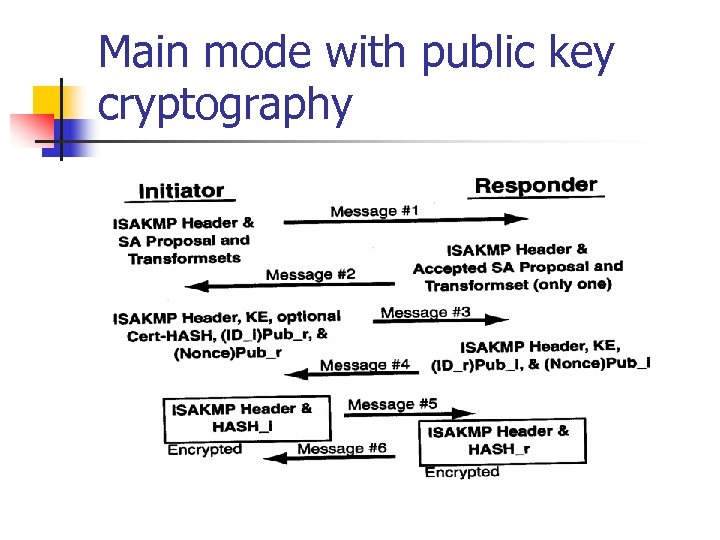
Main mode with public key cryptography
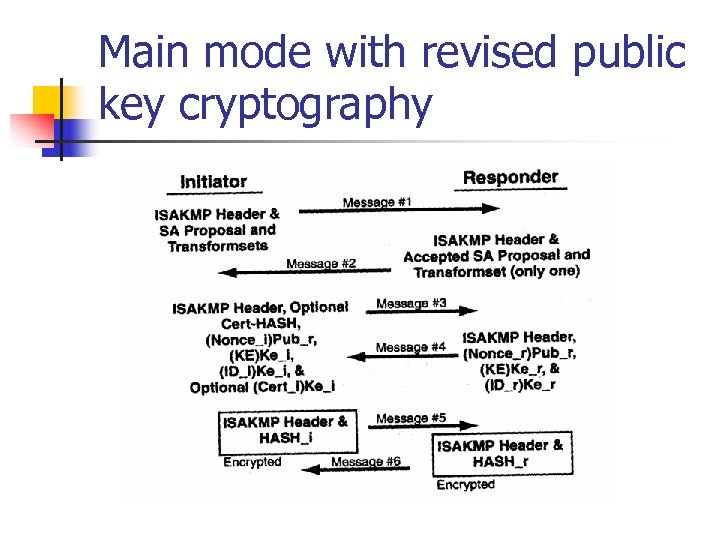
Main mode with revised public key cryptography
Linux IPv 6 IPSec implement n n n Kernel 2. 4之後版本 i. ABG(www. ipv 6. iabg. de) USAGI(www. linux-ipv 6. org)
IC卡優點 n n n 記憶容量大 資料可重複多次寫入 不易偽造 卡片真偽辨識 資料存取控制 內存資料可加密
IC卡配合身分認證Key n n n 以linux平台作為security gateway效率高, 成本低 但linux環境下尚沒有一致的IC卡讀寫標 準 將身分認證Key寫入IC卡中,有助於密鑰 管理
計畫執行進度 n n 研究環境已建立完成 主要的IETF IPSEC Working Group之RFC 已完成研讀 Linux環境下的IC卡讀卡程式,已進行 Coding 作,正處於測試階段。 累計進度完成度: 38%
後續 作 n n n 如何將IC卡與IPSec機制作更完整的結合 完成IC卡讀卡程式Coding IPSec原始碼研讀
IPv 6 x. DSL上網機制之雛形服務系統 的研製 wander@cht. com. tw 2003/07/24 中華電信研究所寬網研究室 Chunghwa Telecom Labs.
Agenda n n Introduction IPv 4/IPv 6轉移機制 n n IPv 6 x. DSL上網機制之雛形服務系統 n n n Dual Stack Tunneling Translator Tunnel Broker Service Model(RFC 3053) System Architecture Functional Diagram Software Requirement Dial-Up ADSL IPv 6 Connection Conclusion 中華電信研究所寬網研究室 Chunghwa Telecom Labs.
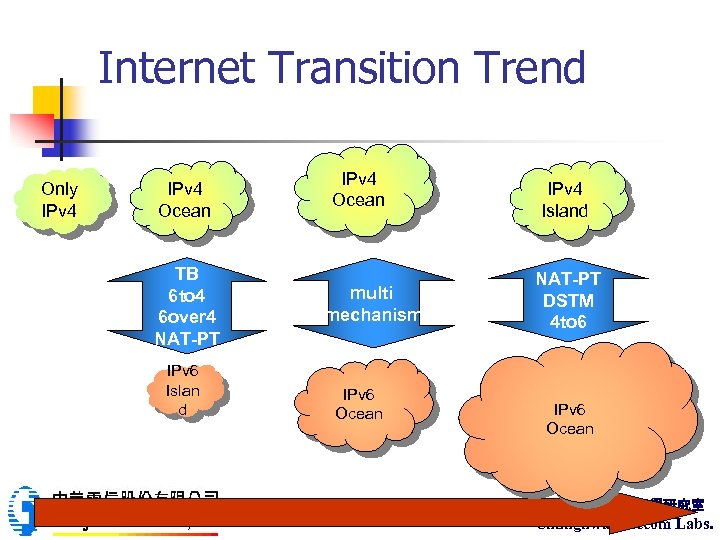
Internet Transition Trend Only IPv 4 Ocean TB 6 to 4 6 over 4 NAT-PT IPv 6 Islan d IPv 4 Ocean multi mechanism IPv 6 Ocean IPv 4 Island NAT-PT DSTM 4 to 6 IPv 6 Ocean 中華電信研究所寬網研究室 Chunghwa Telecom Labs.
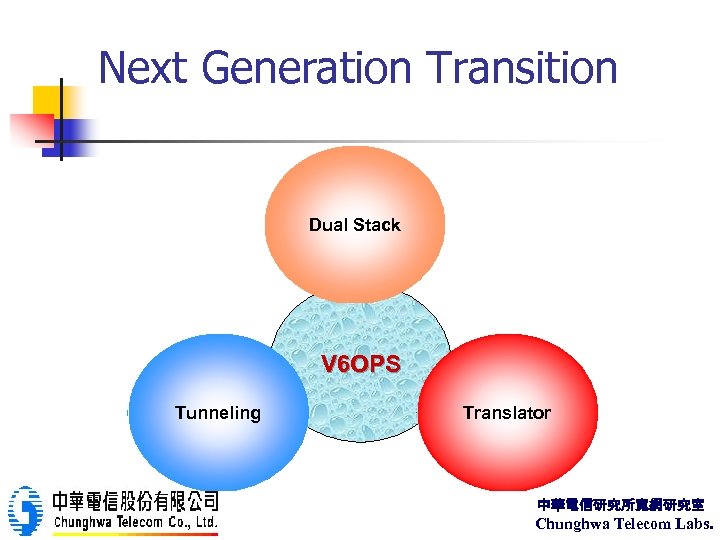
Next Generation Transition Dual Stack V 6 OPS Tunneling Translator 中華電信研究所寬網研究室 Chunghwa Telecom Labs.
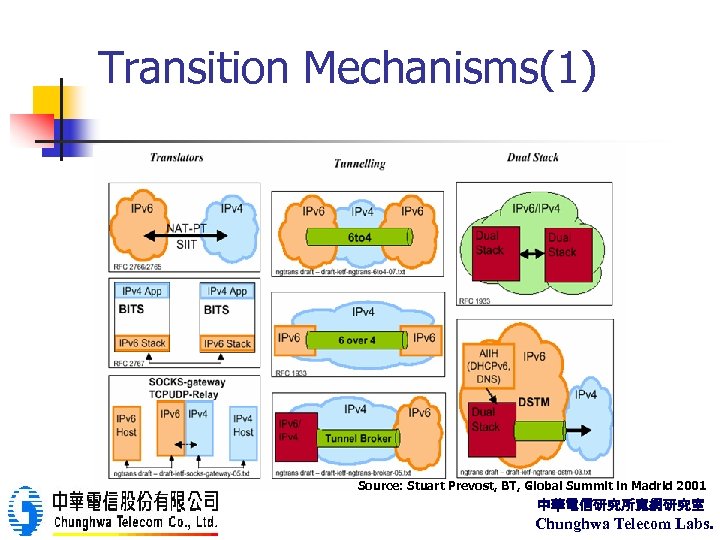
Transition Mechanisms(1) Source: Stuart Prevost, BT, Global Summit in Madrid 2001 中華電信研究所寬網研究室 Chunghwa Telecom Labs.
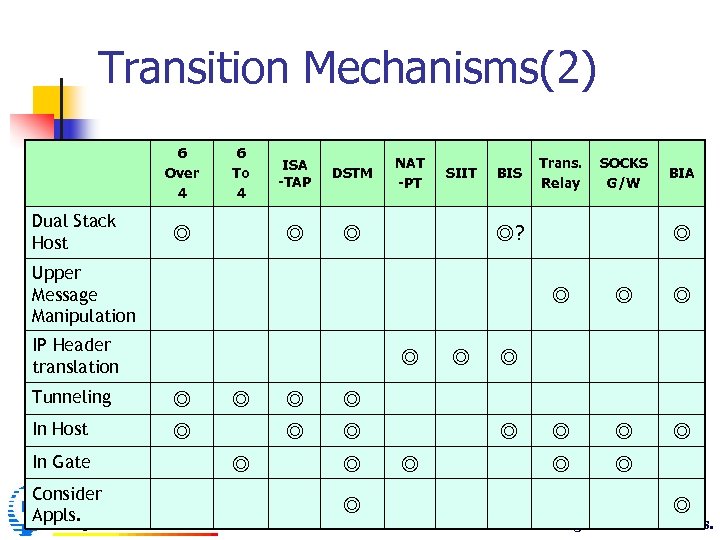
Transition Mechanisms(2) 6 Over 4 Dual Stack Host 6 To 4 DSTM ◎ ◎ ISA -TAP NAT -PT ◎ SIIT BIS BIA ◎ ◎ IP Header translation ◎ Tunneling ◎ In Host ◎ Consider Appls. SOCKS G/W ◎? Upper Message Manipulation In Gate Trans. Relay ◎ ◎ ◎ ◎ ◎ 中華電信研究所寬網研究室 ◎ Chunghwa Telecom Labs.
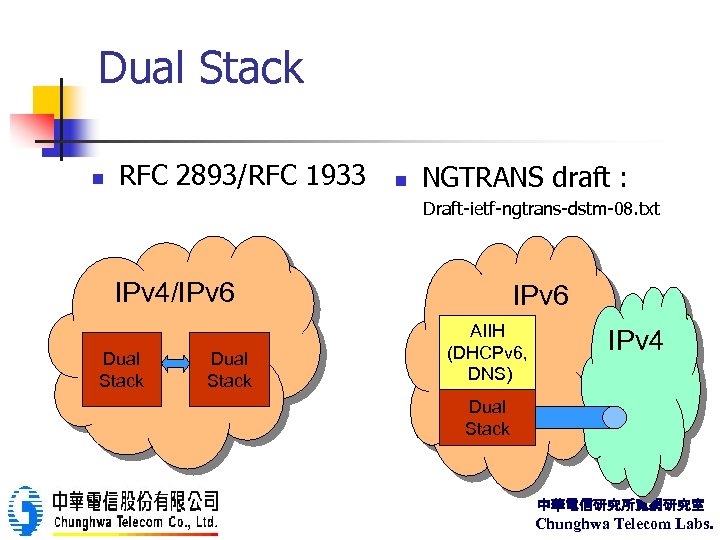
Dual Stack n RFC 2893/RFC 1933 n NGTRANS draft : Draft-ietf-ngtrans-dstm-08. txt IPv 4/IPv 6 Dual Stack IPv 6 AIIH (DHCPv 6, DNS) IPv 4 Dual Stack 中華電信研究所寬網研究室 Chunghwa Telecom Labs.
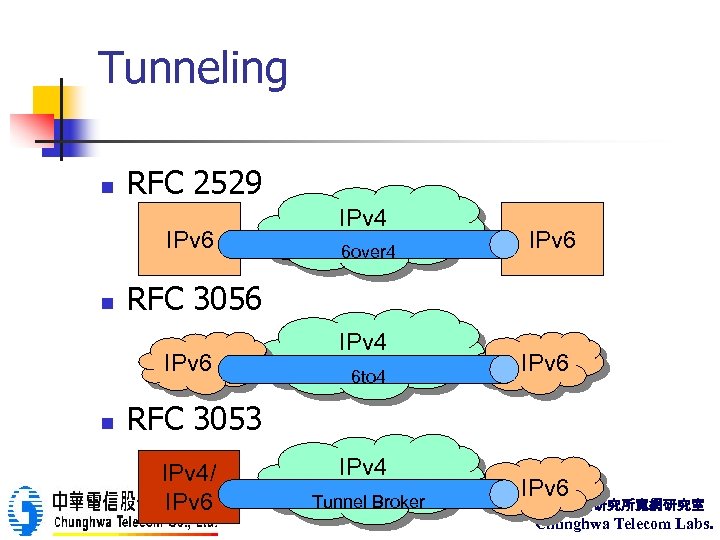
Tunneling n RFC 2529 IPv 6 n 6 over 4 IPv 6 RFC 3056 IPv 6 n IPv 4 6 to 4 IPv 6 RFC 3053 IPv 4/ IPv 6 IPv 4 Tunnel Broker IPv 6 中華電信研究所寬網研究室 Chunghwa Telecom Labs.
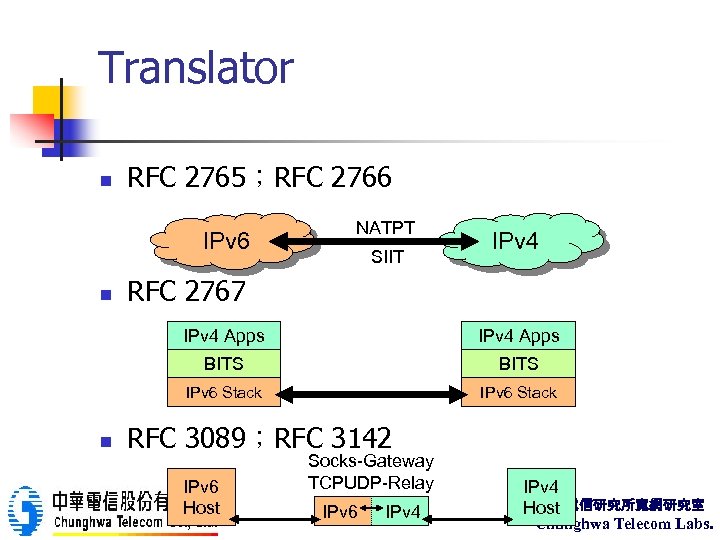
Translator n RFC 2765;RFC 2766 IPv 6 n NATPT SIIT IPv 4 RFC 2767 IPv 4 Apps BITS IPv 6 Stack n IPv 4 Apps IPv 6 Stack RFC 3089;RFC 3142 IPv 6 Host Socks-Gateway TCPUDP-Relay IPv 6 IPv 4 中華電信研究所寬網研究室 Host Chunghwa Telecom Labs.
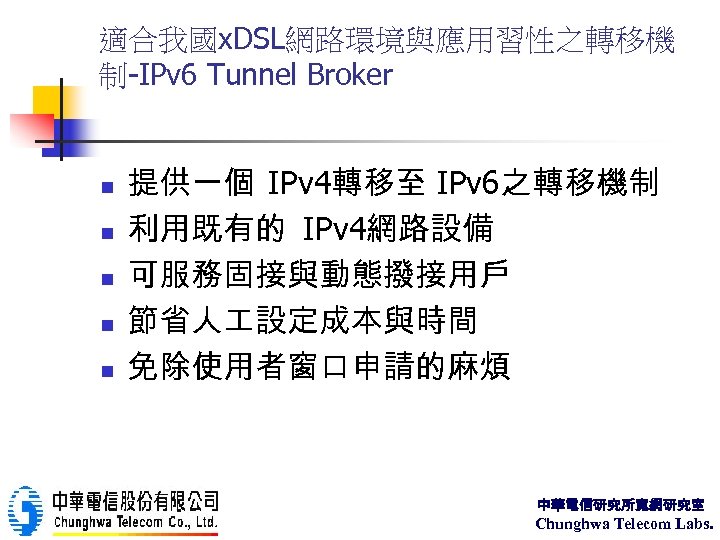
適合我國x. DSL網路環境與應用習性之轉移機 制-IPv 6 Tunnel Broker n n n 提供一個 IPv 4轉移至 IPv 6之轉移機制 利用既有的 IPv 4網路設備 可服務固接與動態撥接用戶 節省人 設定成本與時間 免除使用者窗口申請的麻煩 中華電信研究所寬網研究室 Chunghwa Telecom Labs.
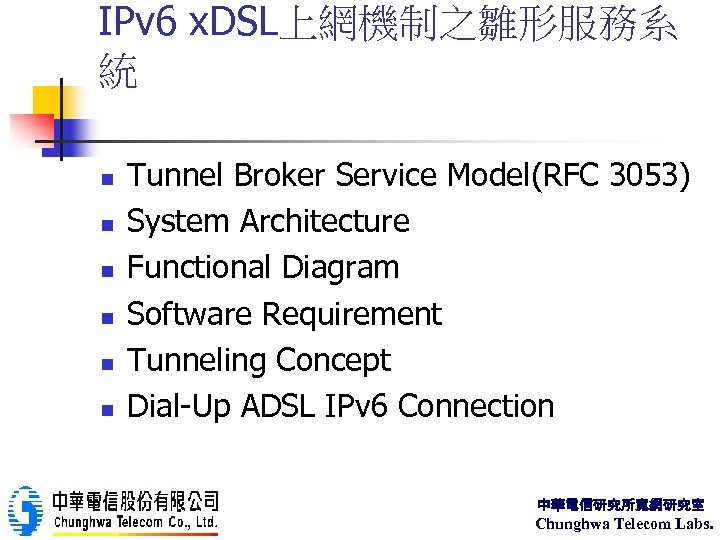
IPv 6 x. DSL上網機制之雛形服務系 統 n n n Tunnel Broker Service Model(RFC 3053) System Architecture Functional Diagram Software Requirement Tunneling Concept Dial-Up ADSL IPv 6 Connection 中華電信研究所寬網研究室 Chunghwa Telecom Labs.
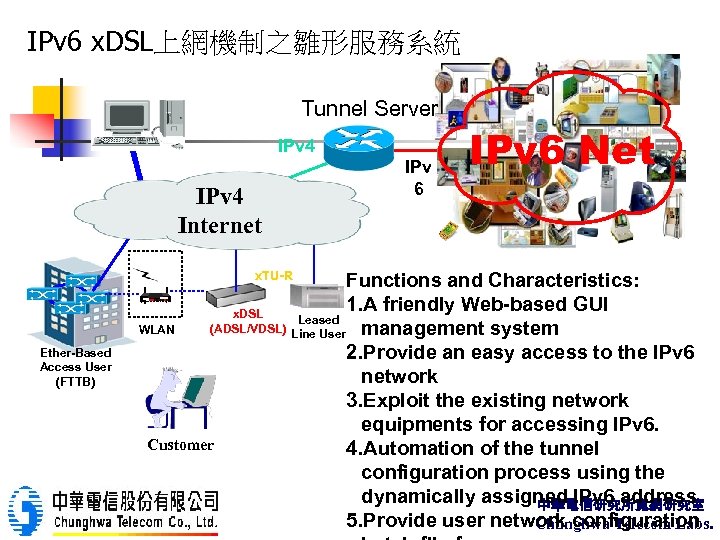
IPv 6 x. DSL上網機制之雛形服務系統 Tunnel Server IPv 4 Internet x. TU-R Ether-Based Access User (FTTB) IPv 6 Net Functions and Characteristics: 1. A friendly Web-based GUI x. DSL Leased (ADSL/VDSL) Line User management system WLAN 2. Provide an easy access to the IPv 6 network 3. Exploit the existing network equipments for accessing IPv 6. Customer 4. Automation of the tunnel configuration process using the dynamically assigned IPv 6 address 中華電信研究所寬網研究室 5. Provide user network configuration Chunghwa Telecom Labs.
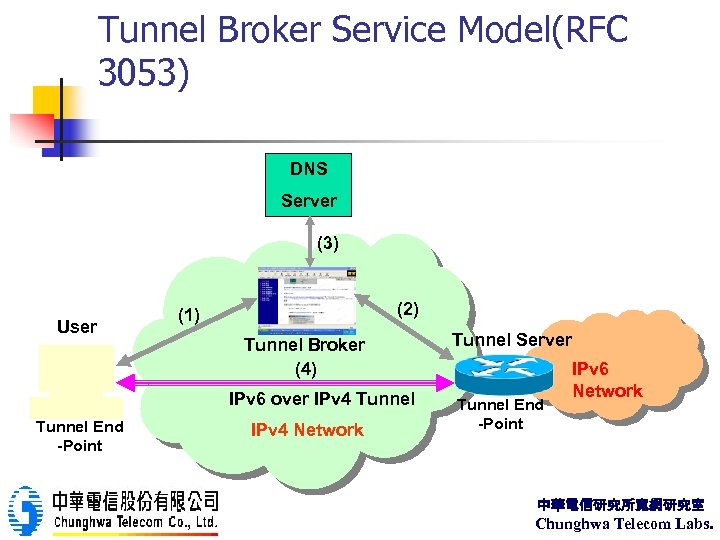
Tunnel Broker Service Model(RFC 3053) DNS Server (3) User (2) (1) Tunnel Broker (4) IPv 6 over IPv 4 Tunnel End -Point IPv 4 Network Tunnel Server Tunnel End -Point IPv 6 Network 中華電信研究所寬網研究室 Chunghwa Telecom Labs.
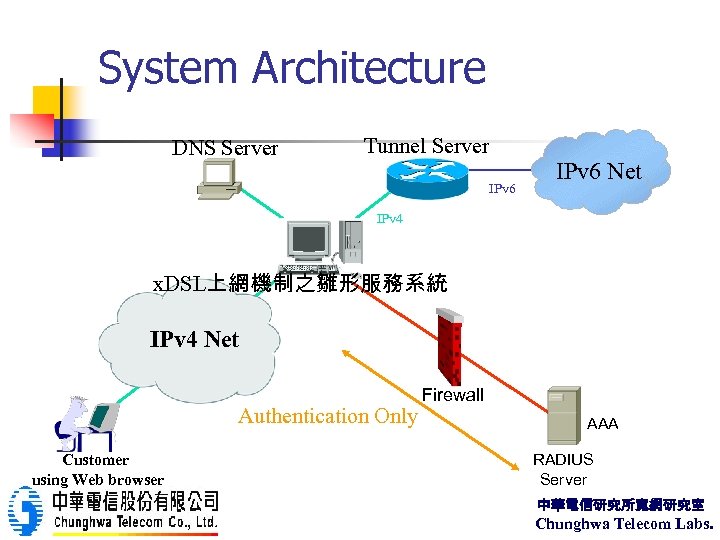
System Architecture DNS Server Tunnel Server IPv 6 Net IPv 4 x. DSL上網機制之雛形服務系統 IPv 4 Net Authentication Only Customer using Web browser Firewall AAA RADIUS Server 中華電信研究所寬網研究室 Chunghwa Telecom Labs.
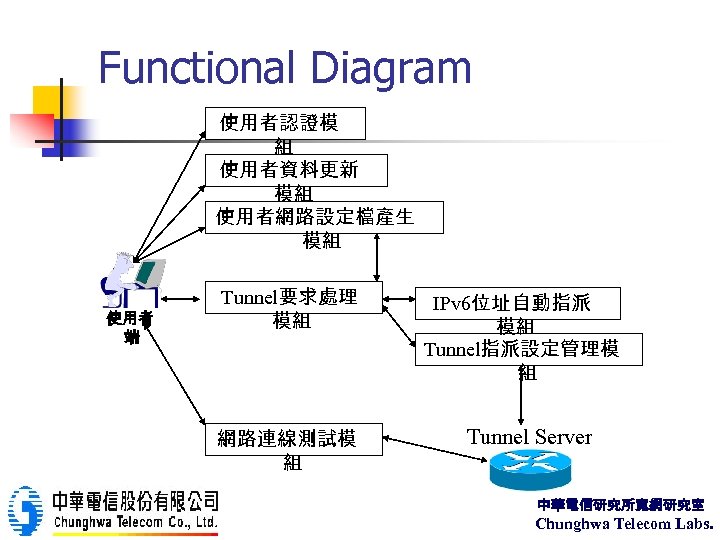
Functional Diagram 使用者認證模 組 使用者資料更新 模組 使用者網路設定檔產生 模組 使用者 端 Tunnel要求處理 模組 網路連線測試模 組 IPv 6位址自動指派 模組 Tunnel指派設定管理模 組 Tunnel Server 中華電信研究所寬網研究室 Chunghwa Telecom Labs.
Software Requirement n n n Windows 2000 Server Internet Information Server(內含ASP) Free ASP Components n n n ASPExec SA-SMTPMail SQL Server 2000 Standard Edition Active Perl(Free) Visual C++ 中華電信研究所寬網研究室 Chunghwa Telecom Labs.
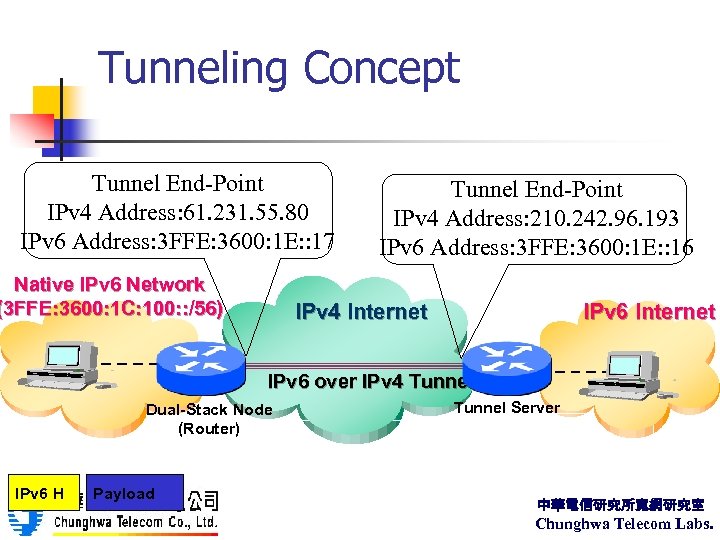
Tunneling Concept Tunnel End-Point IPv 4 Address: 61. 231. 55. 80 IPv 6 Address: 3 FFE: 3600: 1 E: : 17 Native IPv 6 Network (3 FFE: 3600: 1 C: 100: : /56) Tunnel End-Point IPv 4 Address: 210. 242. 96. 193 IPv 6 Address: 3 FFE: 3600: 1 E: : 16 IPv 4 Internet IPv 6 over IPv 4 Tunnel Dual-Stack Node (Router) IPv 6 H Payload Tunnel Server 中華電信研究所寬網研究室 Chunghwa Telecom Labs.
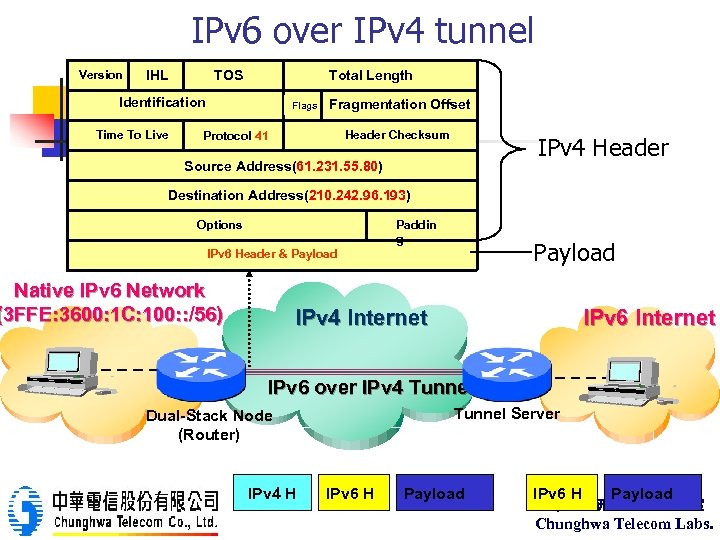
IPv 6 over IPv 4 tunnel Version IHL TOS Total Length Identification Time To Live Flags Fragmentation Offset Header Checksum Protocol 41 IPv 4 Header Source Address(61. 231. 55. 80) Destination Address(210. 242. 96. 193) Paddin g Options Payload IPv 6 Header & Payload Native IPv 6 Network (3 FFE: 3600: 1 C: 100: : /56) IPv 4 Internet IPv 6 over IPv 4 Tunnel Server Dual-Stack Node (Router) IPv 4 H IPv 6 H Payload 中華電信研究所寬網研究室 Chunghwa Telecom Labs.
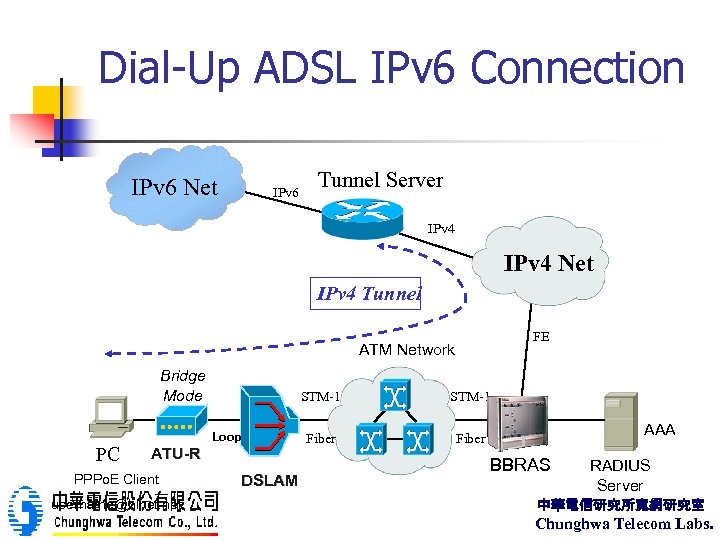
Dial-Up ADSL IPv 6 Connection IPv 6 Net IPv 6 Tunnel Server IPv 4 Net IPv 4 Tunnel FE ATM Network Bridge Mode PC STM-1 Loop ATU-R PPPo. E Client username@hinet. net DSLAM STM-1 Fiber AAA BBRAS RADIUS Server 中華電信研究所寬網研究室 Chunghwa Telecom Labs.

IPv 6 Let’s go to Next-Generation Future Vision Internet New Era Anytime, Anywhere, Everything Connecting On the Internet IPv 6 中華電信研究所寬網研究室 Chunghwa Telecom Labs.
653fd15b5591f8c569450a0396af0810.ppt