777d5fabf84077ab34142afb0896d7c7.ppt
- Количество слайдов: 38
具安全性及自我組織能力的 無線網狀網路 Design of Efficient and Secure Multiple Wireless Mesh Network 研 究 生: 蔡憲邦 指導教授:柯開維 博士 2005/7/15
Outline n n n Introduction Background Design a Secure WMN Security Analysis Conclusion 2005/7/15 2
Introduction (1/2) n Wireless Mesh Network n n n Properties. Security Problem. Wireless Security Problem n n Attacks. Secure solution. 2005/7/15 3
Introduction (2/2) n This thesis n n Tree topology Define the WMN’s basic functions Security issue Compare with other security issue 2005/7/15 4
Wireless Mesh Network (WMN) n n n Full & Partial mesh network. Omni directional & directional. Benefit: n n Reduction of install cost Large-scale depolyment (last mile) Reliability Self-management 2005/7/15 5
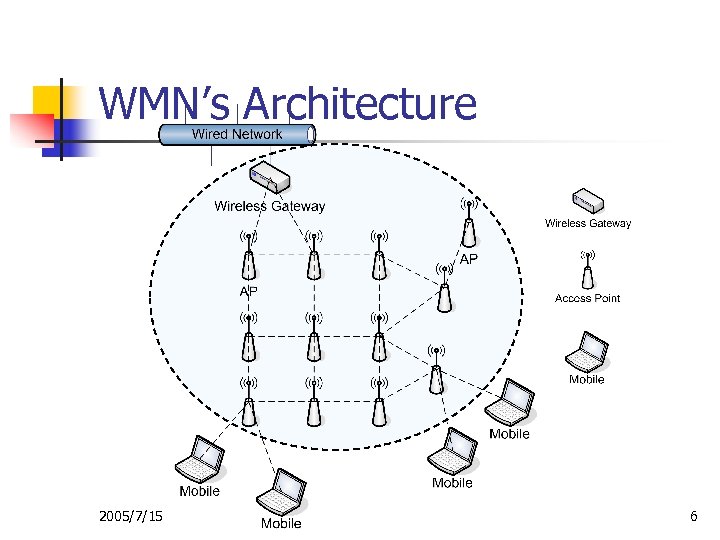
WMN’s Architecture 2005/7/15 6
Wireless Security n Wireless Environment n n n Open media Unlicensed ISM band Wireless Attacks n n Infrastructure Ad hoc 2005/7/15 7
Wireless Attacks n Infrastructure n n Insertion Interception and Monitoring Jamming Ad hoc n n Black hole Impersonation 2005/7/15 8
Wireless Security Solutions n Main Purposes n n n Authentication Data encryption Infrastructure n n WEP IEEE 802. 1 x 2005/7/15 n Ad hoc n n Share Key Public Key Infrastructure (PKI) 9
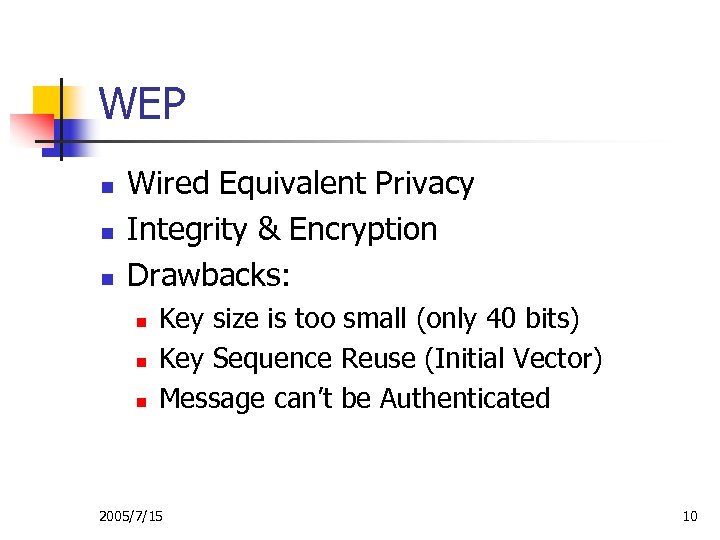
WEP n n n Wired Equivalent Privacy Integrity & Encryption Drawbacks: n n n Key size is too small (only 40 bits) Key Sequence Reuse (Initial Vector) Message can’t be Authenticated 2005/7/15 10
IEEE 802. 1 x (1/2) n n n Provide network access authentication. Supplicant, Authenticator and Authentication Server. Drawback: n n One-way authentication. Not protect authentication. 2005/7/15 11
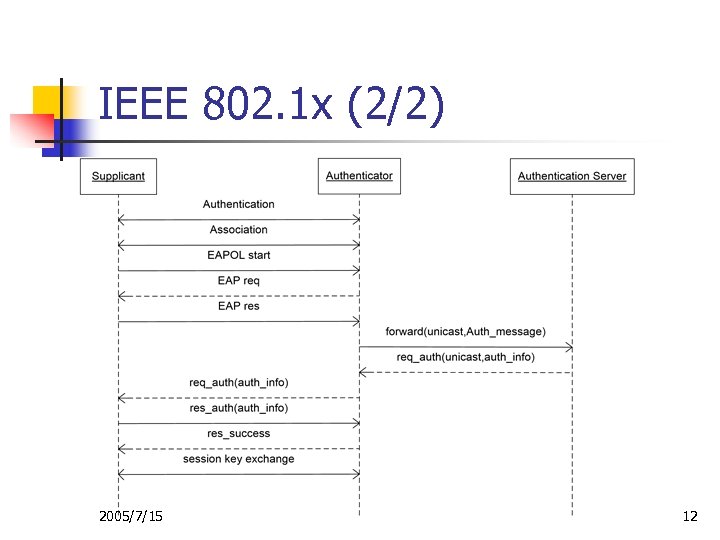
IEEE 802. 1 x (2/2) 2005/7/15 12
Share Key n n Use one key to authenticate and encryption in ad hoc network. Drawbacks: n n n Only one key Non-repudiation Key management 2005/7/15 13
Public Key Infrastructure n Key feature of public key cryptosystem n n n Two keys: Public Key & Private Key Computational infeasible to determine decryption key. Drawbacks n n Certificate Authority (CA) Spend a lot of time to en/decrypt. 2005/7/15 14
Outline n n n Introduction Background Design a Secure WMN Security Analysis Conclusion 2005/7/15 15
The Properties of WMN n Similar to ad hoc network n n AP should select a routing path. The routing path is always fix. Most data are sent to WG. My propose: Tree Topology. 2005/7/15 16
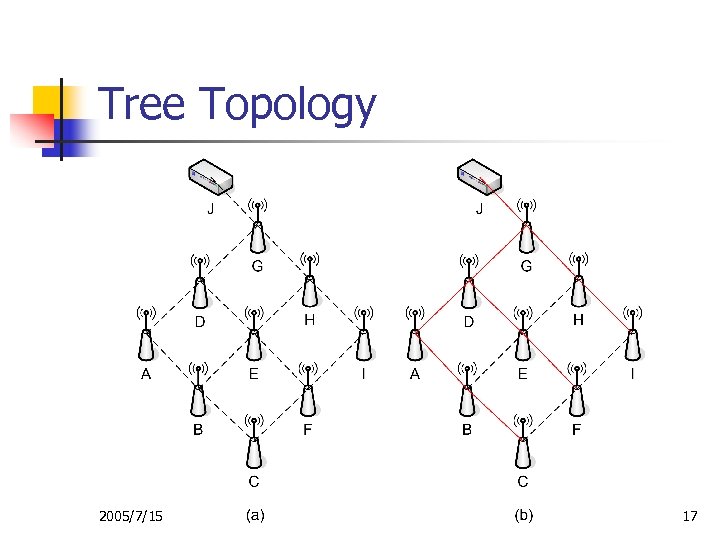
Tree Topology 2005/7/15 17
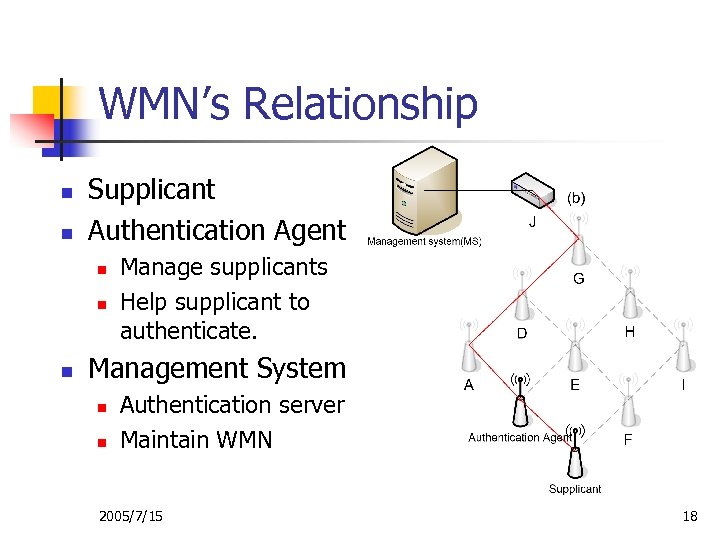
WMN’s Relationship n n Supplicant Authentication Agent n n n Manage supplicants Help supplicant to authenticate. Management System n n Authentication server Maintain WMN 2005/7/15 18
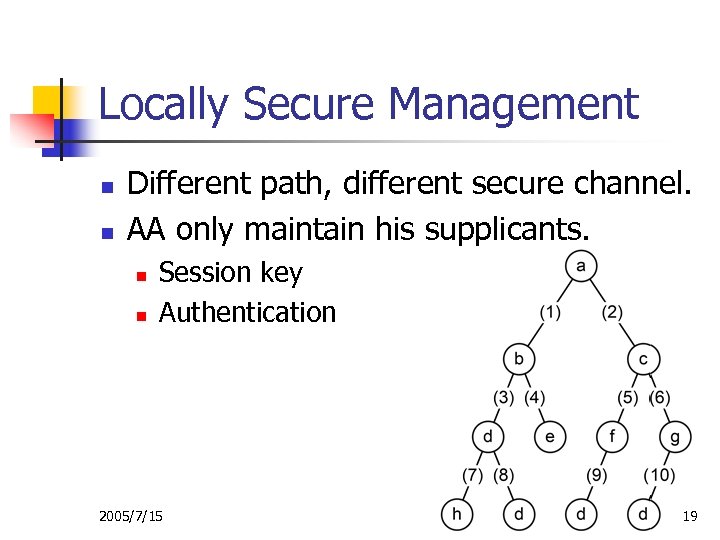
Locally Secure Management n n Different path, different secure channel. AA only maintain his supplicants. n n Session key Authentication 2005/7/15 19
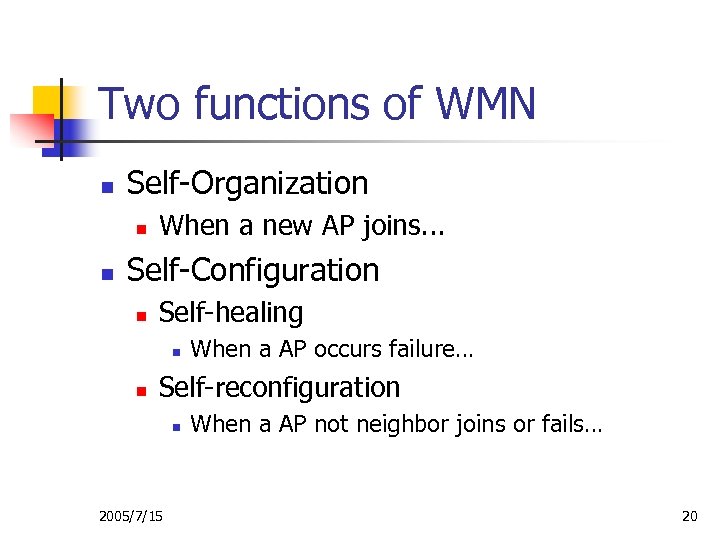
Two functions of WMN n Self-Organization n n When a new AP joins. . . Self-Configuration n Self-healing n n When a AP occurs failure… Self-reconfiguration n 2005/7/15 When a AP not neighbor joins or fails… 20
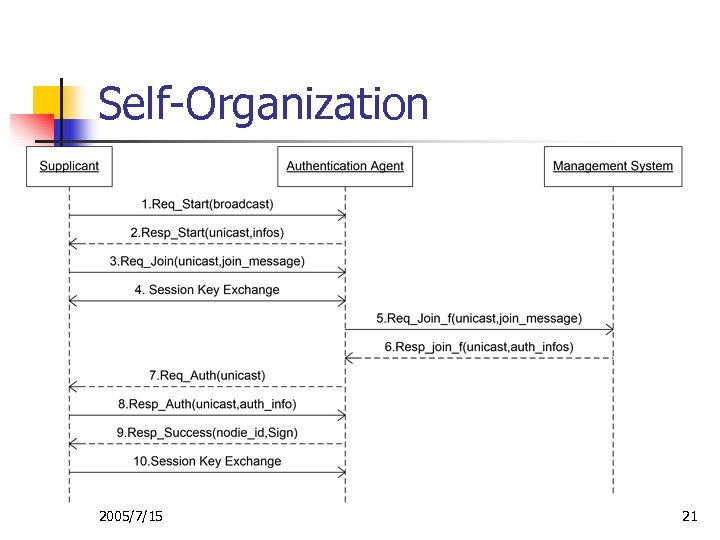
Self-Organization 2005/7/15 21
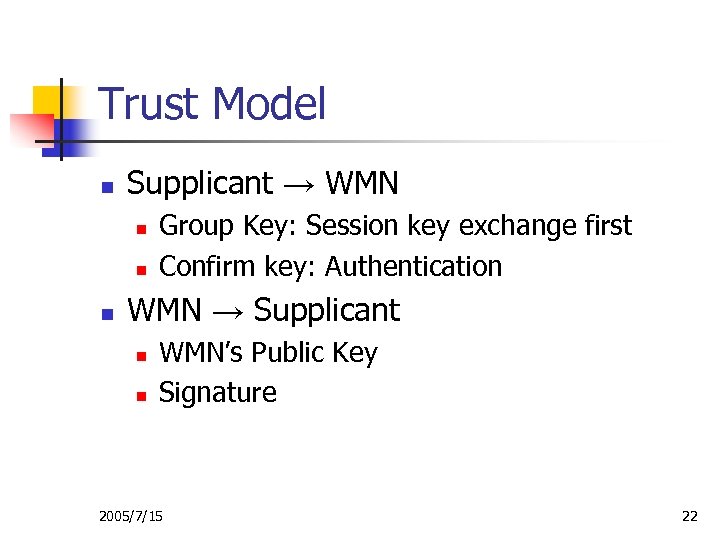
Trust Model n Supplicant → WMN n n n Group Key: Session key exchange first Confirm key: Authentication WMN → Supplicant n n WMN’s Public Key Signature 2005/7/15 22
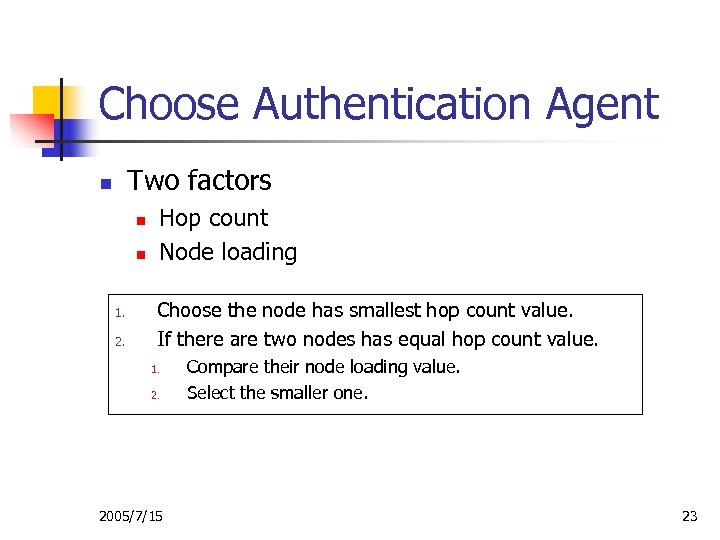
Choose Authentication Agent Two factors n n n 1. 2. Hop count Node loading Choose the node has smallest hop count value. If there are two nodes has equal hop count value. 1. 2. 2005/7/15 Compare their node loading value. Select the smaller one. 23
Session Key Exchange n n n Session key exchange first. Session key should be modified periodically. Default Key: 2005/7/15 24
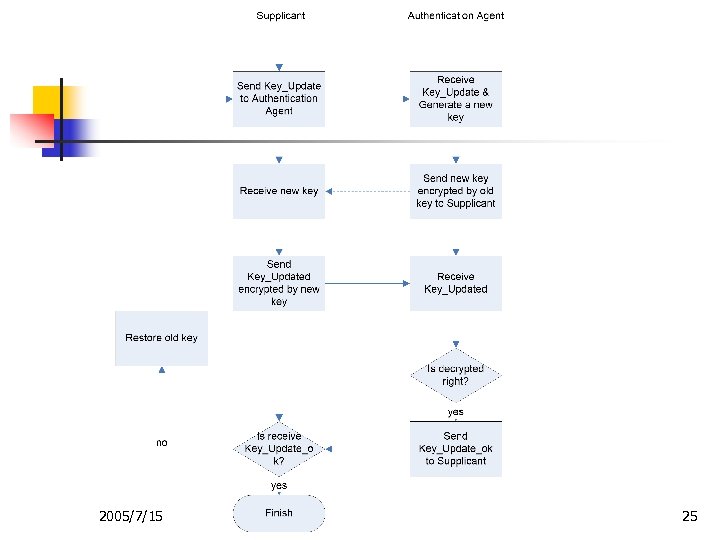
2005/7/15 25
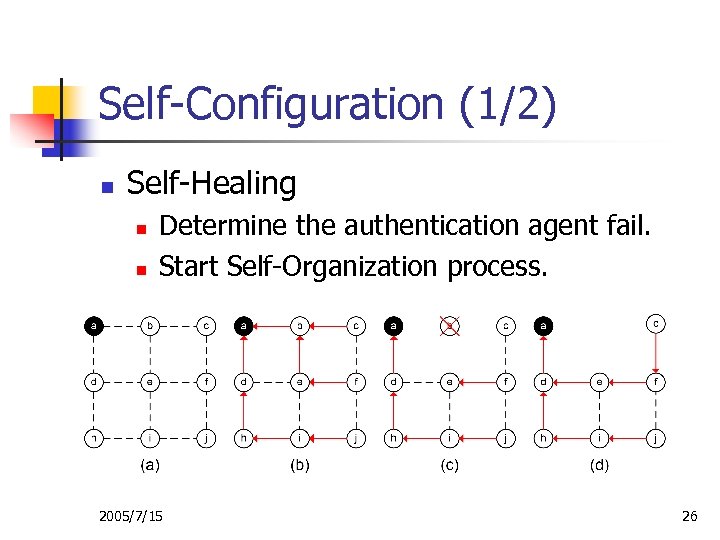
Self-Configuration (1/2) n Self-Healing n n Determine the authentication agent fail. Start Self-Organization process. 2005/7/15 26
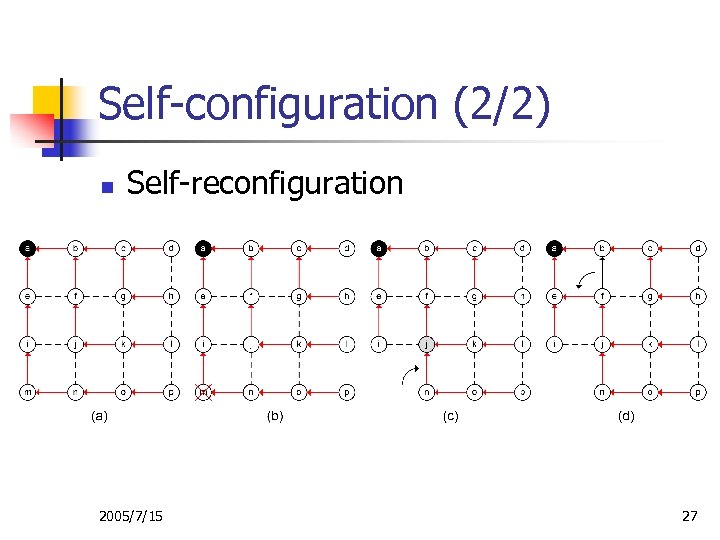
Self-configuration (2/2) n Self-reconfiguration 2005/7/15 27
Outline n n n Introduction Background Design a Secure WMN Security Analysis Conclusion 2005/7/15 28
Security Issue n n n Message encryption: data & control Locality security Trust model Session key exchange first Period session key exchange 2005/7/15 29
Attacks Defense n n n Man-in-middle (MIM) Forge AP Session Hijack Route Swindle Denial of Service (Do. S) 2005/7/15 30
MIM & Forge AP n Man-in-Middle (MIM) n n n Use session key create secure channel. Period session key exchange. Forge AP n Period session key exchange. 2005/7/15 31
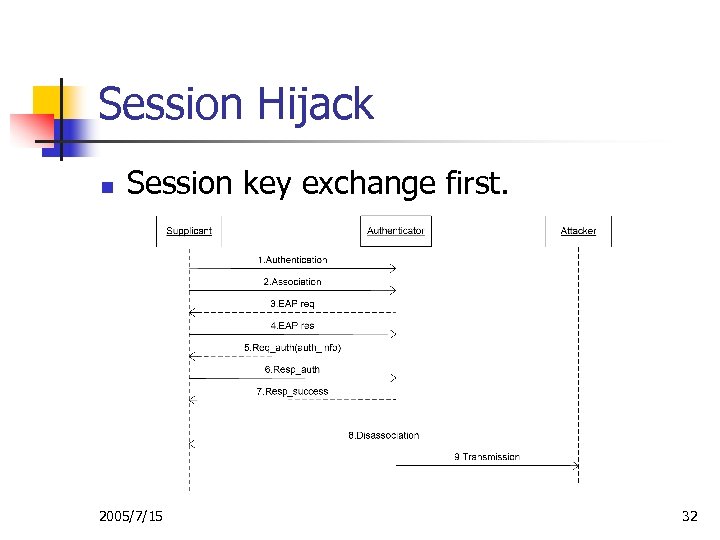
Session Hijack n Session key exchange first. 2005/7/15 32
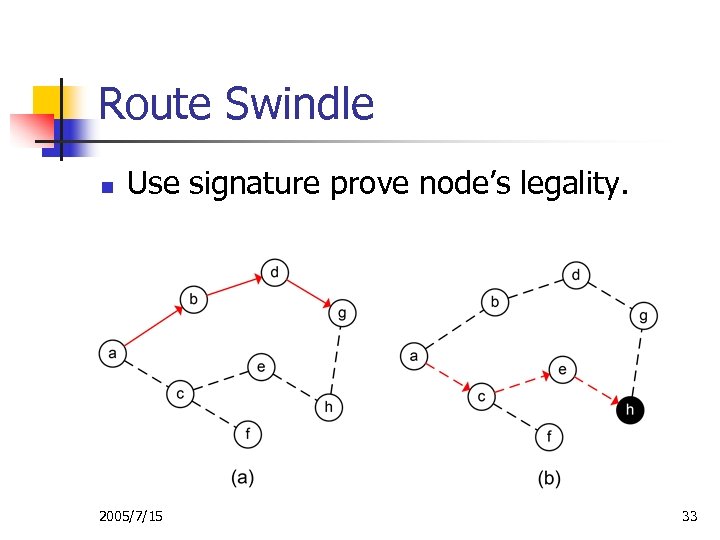
Route Swindle n Use signature prove node’s legality. 2005/7/15 33
Denial of Service n Attack: n n n Limited CPU and memory. Continually send streams of association and disassociation packets. Solutions: n n There are not any solution to solve this problem. Self-healing procedure 2005/7/15 34
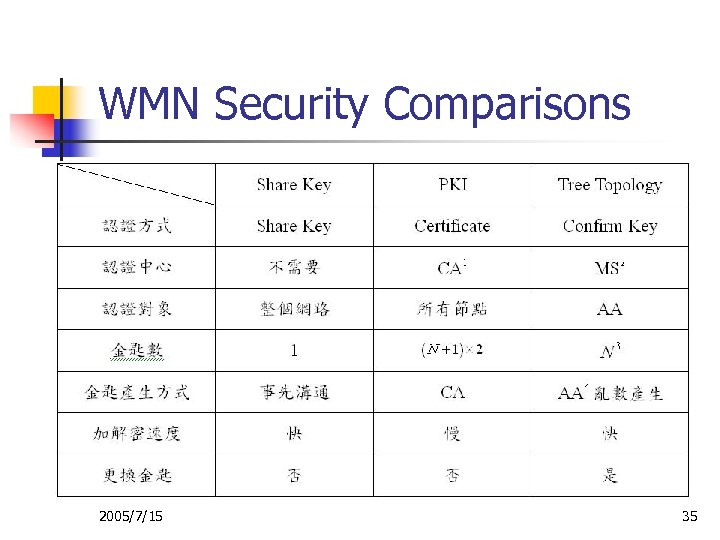
WMN Security Comparisons 2005/7/15 35
Conclusion n n Tree based secure architecture was proposed. Define WMN’s basic functions of WMN. Analysis WMN’s security problems. Compare with other security issue. 2005/7/15 36
Future Work n n n Consider more available attacks. Mobile mesh network. Other application: n n Sensor network Ad hoc network 2005/7/15 37
The End, Thank You 2005/7/15 38
777d5fabf84077ab34142afb0896d7c7.ppt