d1f6d632ca7803e34731c2844ddf50e0.ppt
- Количество слайдов: 59
你的心跳可能成為您的密碼 Your heartbeat could be your password Ching-Kun Chen Department of Electrical Engineering National Chung Hsing University Taichung, Taiwan, R. O. C. April 30, 2013
Outline Introduction Chaos and Quantifying Chaotic Behavior Phase space reconstruction Lyapunov Exponent Chaotic Functions ECG-Based Biometric Recognition Synchronization of Two Identical Lorenz Systems System Design and Secure Information Transmission Experimental Results and Discussion Conclusions and Feature Work
Introduction Motivation As multimedia and network technologies continue to develop, digital information is increasingly applied in real-world applications. However, digitized information is easy to copy, making information security increasingly crucial in the communication process. Cryptography is one of basic methodologies for information security. Since 1990 s, many researchers have noticed that there exists a close relationship between chaos and cryptography. Recently, chaos theory gradually plays an active role in cryptography consistently.
Introduction Motivation Biometric based authentication system provides better security solutions than conventional. But some biological parameters that are used as biometric don’t provide the robustness against falsified credentials such as voice can be copied through microphone, fingerprint can be collected on silicon surface and iris can be copied on contact lenses. ECG doesn’t have these problems and it’s unique in every individual. Human heart is a supremely complex biological system. There are no model that account for all of cardiac electrical activity. Researchers in the field of chaotic dynamical system theory have used several features, including correlation dimension (D 2), Lyapunov exponents ( ), approximate entropy, etc. These key features have can explain ECG’s behavior for diagnostic purposes.
Literature Survey Chaos-related research Chaos Encryption ECG Transmission
Literature Survey - Chaotic Encryption Pareek et al. proposed an image encryption scheme which utilizes two chaotic logistic maps and an external key of 80 bits. (2006) Kwok et al. proposed a fast chaos-based image cryptosystem with the architecture of a stream cipher. (2007) Behina et al. proposed a novel algorithm for image encryption based on mixture of chaotic maps, using one dimensional chaotic map and their coupling to obtain high level security. (2008) Zhu et al. proposed a chaos-based symmetric image encryption scheme using a bit-level permutation. (2012)
Literature Survey - Chaotic ECG Signal Babloyantz et al. showed the human heart is not a simple oscillator, the heart behavior exhibits a chaotic behavior. (1988) Casaleggio et al. applied lyapunov exponents to analysis and estimation of ECG signals from MIT-BIH database. (1995, 1997) Owis et al. present a study of features based on the nonlinear dynamical ECG signals for arrhythmia detection and classification. (2002) Al-Fahoum et al. used simple reconstructed phase space approach for ECG arrhythmia classification. (2006)
Literature Survey - Chaotic Transmission The application of chaotic synchronization to secret communication was suggested by Pecora and Carroll. (1990, 1991) A successful experimental realization of signal masking and recovery was first made using electric circuits by Cuomo. (1993) Control of chaos techniques have also been used for the transmission of messages by means of chaotic signals. There are several control techniques used to synchronize chaotic systems, such as fuzzy control, delayed neural networks, impulsive control, and linear error feedback control. The chaotic signals can be used to mask information waveforms or serve as modulating waveforms.
Chaos and Quantifying Chaotic Behavior
Description of Methods Phase space reconstruction Packard et al. (1980)proposed phase space reconstruction that is a standard procedure while analyzing chaotic systems which shows the trajectory of the system in time. Phase space in d dimensions display a number of points where each point is given by of the system, where n is the moment in time of a system variable, with denoting the sampling period and T being the period between two consecutive measurement for constructing the phase plot. The trajectory in d dimensional space is a set of k consecutive points and where is the starting time of observation.
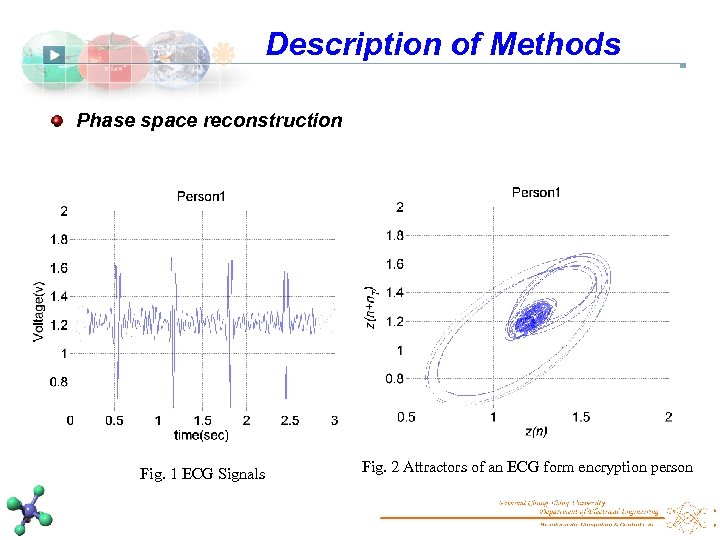
Description of Methods Phase space reconstruction Fig. 1 ECG Signals Fig. 2 Attractors of an ECG form encryption person
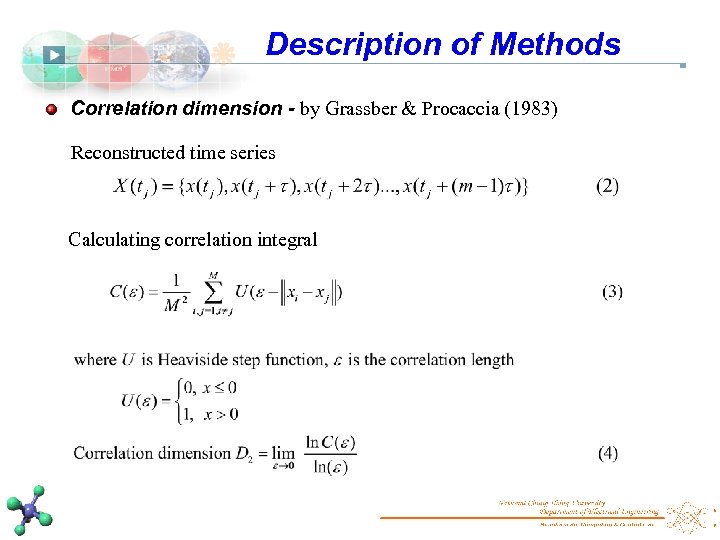
Description of Methods Correlation dimension - by Grassber & Procaccia (1983) Reconstructed time series Calculating correlation integral
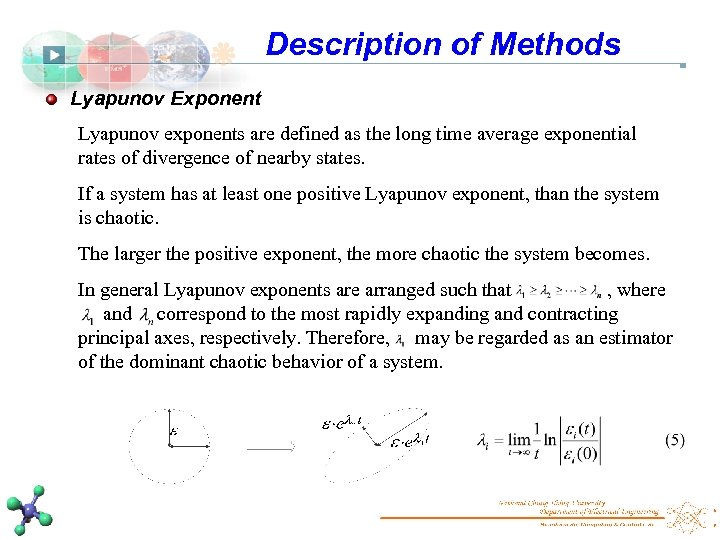
Description of Methods Lyapunov Exponent Lyapunov exponents are defined as the long time average exponential rates of divergence of nearby states. If a system has at least one positive Lyapunov exponent, than the system is chaotic. The larger the positive exponent, the more chaotic the system becomes. In general Lyapunov exponents are arranged such that , where and correspond to the most rapidly expanding and contracting principal axes, respectively. Therefore, may be regarded as an estimator of the dominant chaotic behavior of a system.
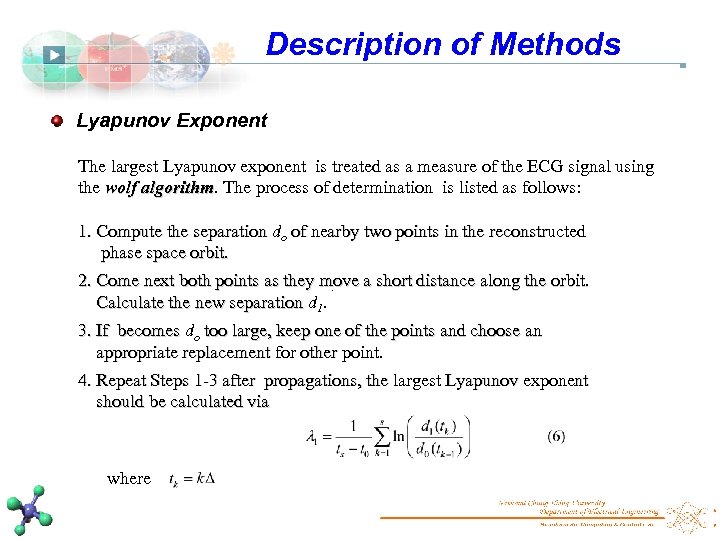
Description of Methods Lyapunov Exponent The largest Lyapunov exponent is treated as a measure of the ECG signal using the wolf algorithm. The process of determination is listed as follows: algorithm 1. Compute the separation do of nearby two points in the reconstructed phase space orbit. 2. Come next both points as they move a short distance along the orbit. . Calculate the new separation d 1. 3. If becomes do too large, keep one of the points and choose an appropriate replacement for other point. 4. Repeat Steps 1 -3 after propagations, the largest Lyapunov exponent should be calculated via where
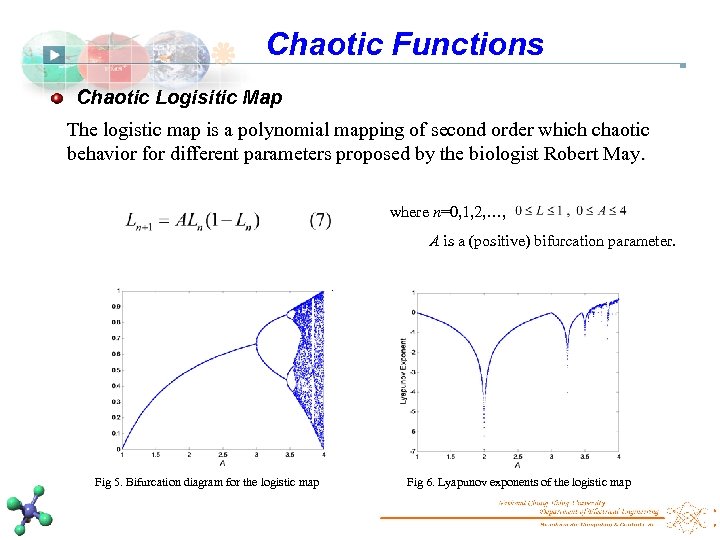
Chaotic Functions Chaotic Logisitic Map The logistic map is a polynomial mapping of second order which chaotic behavior for different parameters proposed by the biologist Robert May. where n=0, 1, 2, …, A is a (positive) bifurcation parameter. . Fig 5. Bifurcation diagram for the logistic map Fig 6. Lyapunov exponents of the logistic map
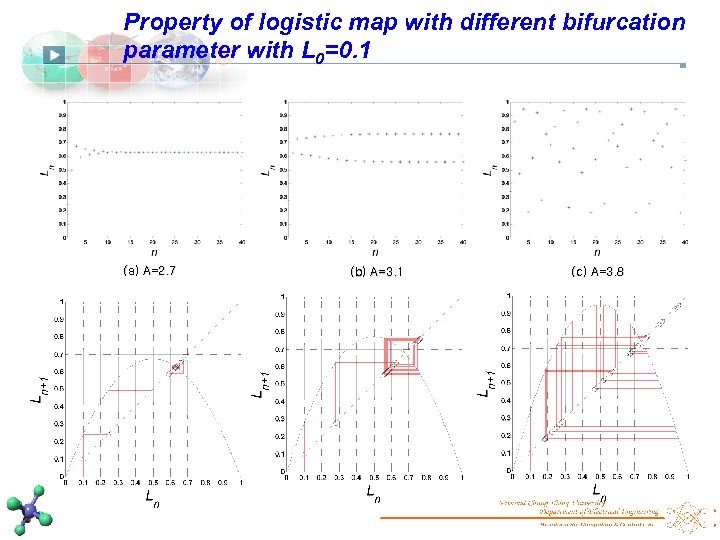
Property of logistic map with different bifurcation parameter with L 0=0. 1 (a) A=2. 7 (b) A=3. 1 (c) A=3. 8
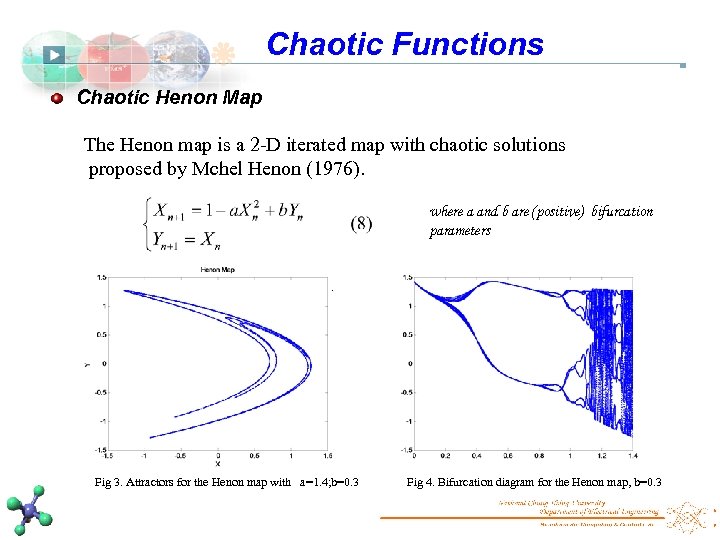
Chaotic Functions Chaotic Henon Map The Henon map is a 2 -D iterated map with chaotic solutions proposed by Mchel Henon (1976). where a and b are (positive) bifurcation parameters . Fig 3. Attractors for the Henon map with a=1. 4; b=0. 3 Fig 4. Bifurcation diagram for the Henon map, b=0. 3
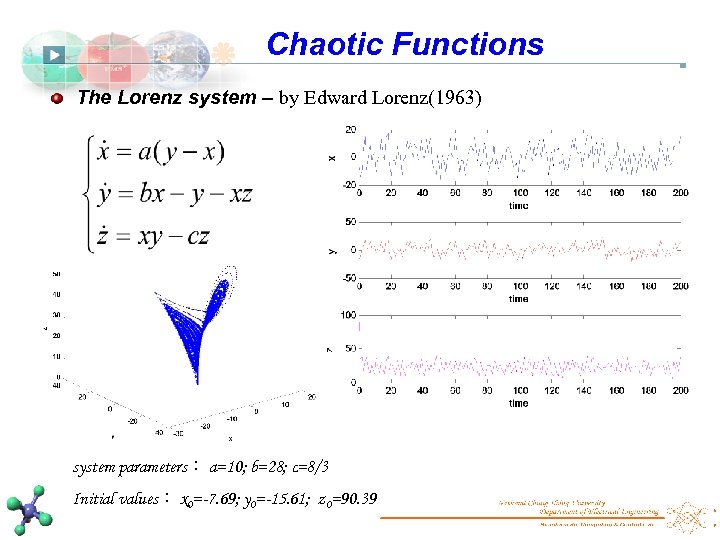
Chaotic Functions The Lorenz system – by Edward Lorenz(1963) system parameters: a=10; b=28; c=8/3 Initial values: x 0=-7. 69; y 0=-15. 61; z 0=90. 39
Characteristics of Chaotic Systems They are aperiodic. They exhibit sensitive dependence on initial conditions and unpredictable in the long term. They are governed by one or more control parameters, a small change in which can cause the chaos to appear or disappear. Their governing equations are nonlinear.
ECG-Based Biometric Recognition
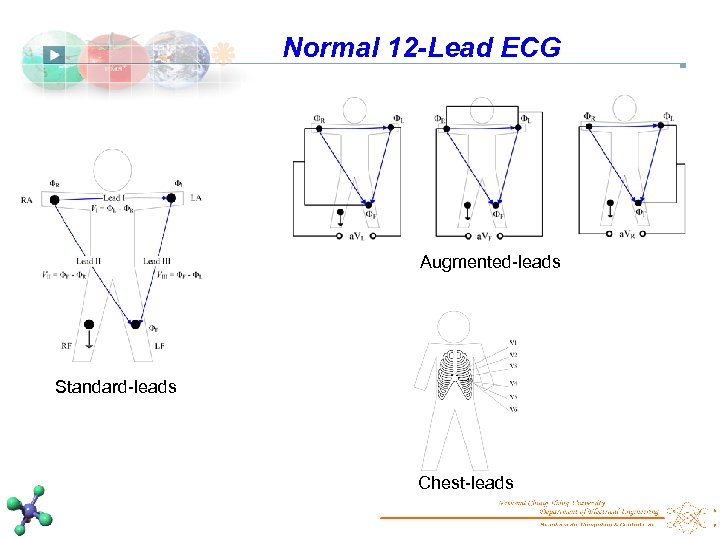
Normal 12 -Lead ECG Augmented-leads Standard-leads Chest-leads
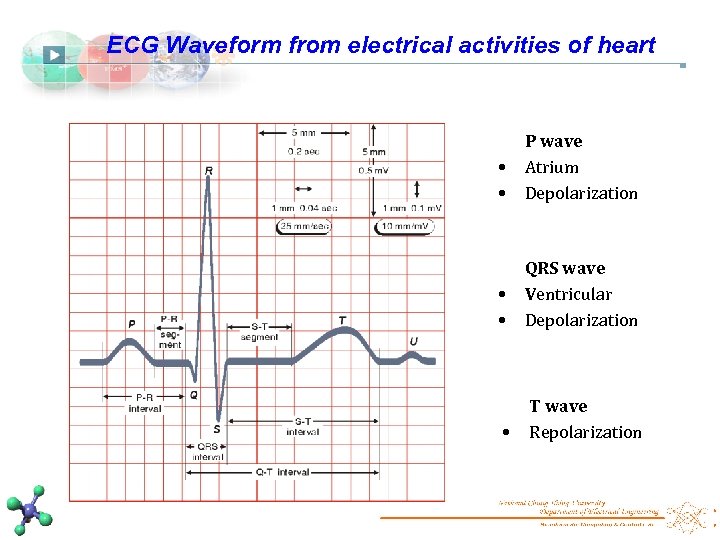
ECG Waveform from electrical activities of heart • • P wave Atrium Depolarization • • QRS wave Ventricular Depolarization • T wave Repolarization
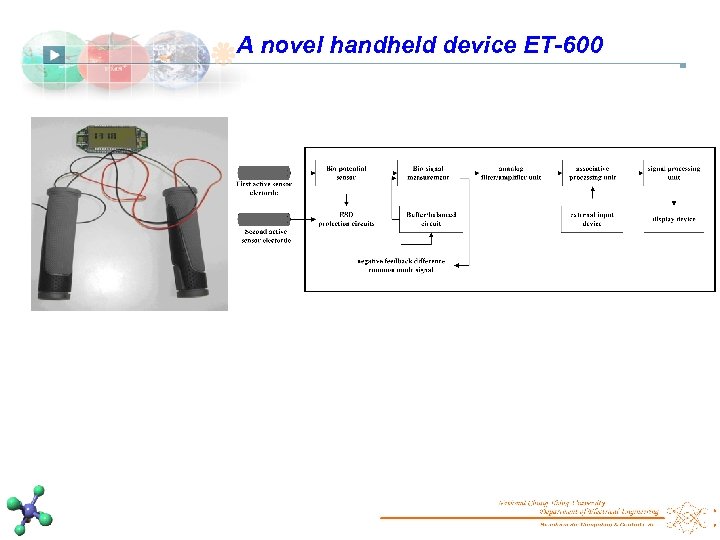
A novel handheld device ET-600
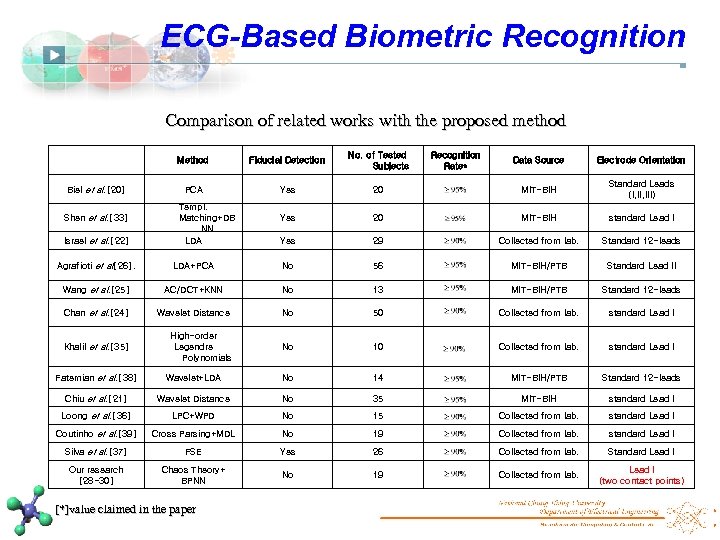
ECG-Based Biometric Recognition Comparison of related works with the proposed method Method Biel et al. [20] Shen et al. [33] Israel et al. [22] Fiducial Detection No. of Tested Subjects PCA Yes Templ. Matching+DB NN LDA Recognition Rate* Data Source Electrode Orientation 20 MIT-BIH Standard Leads (I, III) Yes 20 MIT-BIH standard Lead I Yes 29 Collected from lab. Standard 12 -leads Agrafioti et al[26]. LDA+PCA No 56 MIT-BIH/PTB Standard Lead II Wang et al. [25] AC/DCT+KNN No 13 MIT-BIH/PTB Standard 12 -leads Chan et al. [24] Wavelet Distance No 50 Collected from lab. standard Lead I Khalil et al. [35] High-order Legendre Polynomials No 10 Collected from lab. standard Lead I Fatemian et al. [38] Wavelet+LDA No 14 MIT-BIH/PTB Standard 12 -leads Chiu et al. [21] Wavelet Distance No 35 MIT-BIH standard Lead I Loong et al. [36] LPC+WPD No 15 Collected from lab. standard Lead I Coutinho et al. [39] Cross Parsing+MDL No 19 Collected from lab. standard Lead I Silva et al. [37] FSE Yes 26 Collected from lab. Standard Lead I Our research [28 -30] Chaos Theory+ BPNN No 19 Collected from lab. Lead I (two contact points) [*]value claimed in the paper
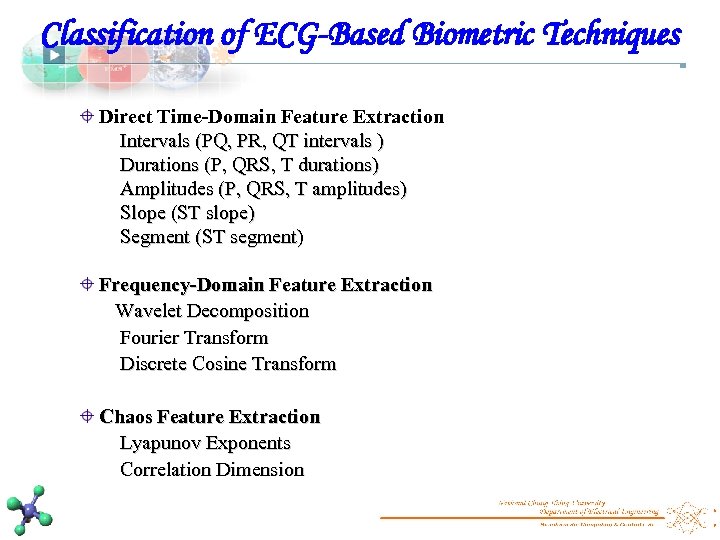
Classification of ECG-Based Biometric Techniques Direct Time-Domain Feature Extraction Intervals (PQ, PR, QT intervals ) Durations (P, QRS, T durations) Amplitudes (P, QRS, T amplitudes) Slope (ST slope) Segment (ST segment) Frequency-Domain Feature Extraction Wavelet Decomposition Fourier Transform Discrete Cosine Transform Chaos Feature Extraction Lyapunov Exponents Correlation Dimension
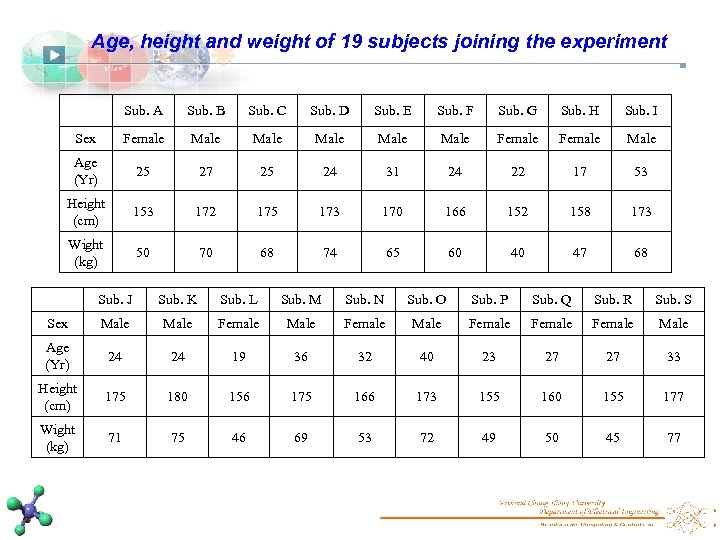
Age, height and weight of 19 subjects joining the experiment Sub. A Sub. B Sub. C Sub. D Sub. E Sub. F Sub. G Sub. H Sub. I Sex Female Male Male Female Male Age (Yr) 25 27 25 24 31 24 22 17 53 Height (cm) 153 172 175 173 170 166 152 158 173 Wight (kg) 50 70 68 74 65 60 40 47 68 Sub. J Sub. K Sub. L Sub. M Sub. N Sub. O Sub. P Sub. Q Sub. R Sub. S Sex Male Female Female Male Age (Yr) 24 24 19 36 32 40 23 27 27 33 Height (cm) 175 180 156 175 166 173 155 160 155 177 Wight (kg) 71 75 46 69 53 72 49 50 45 77
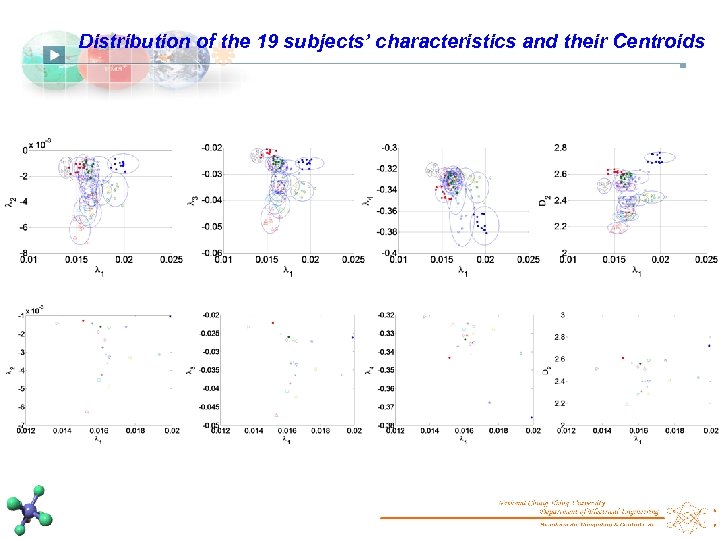
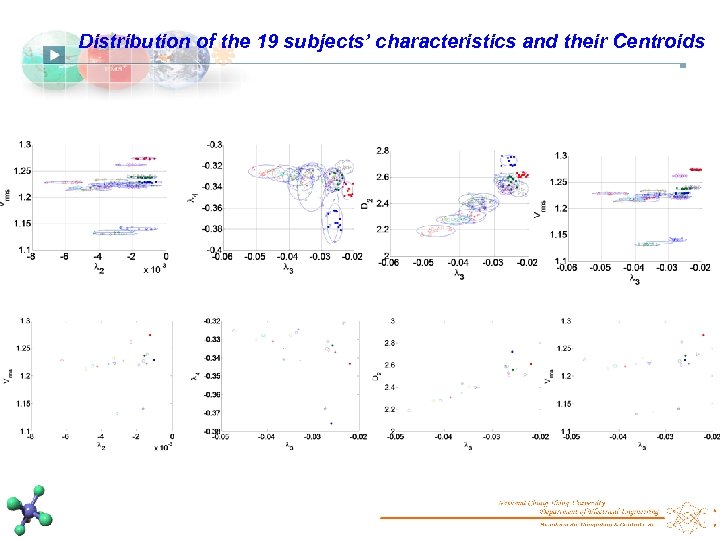
Distribution of the 19 subjects’ characteristics and their Centroids
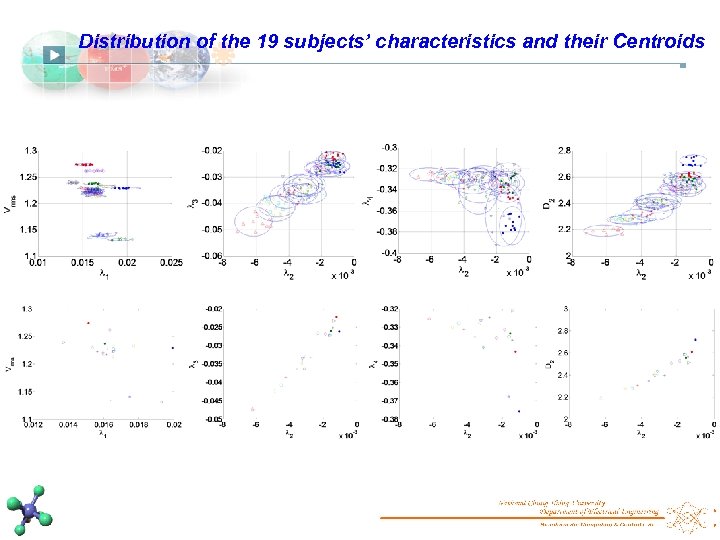
Distribution of the 19 subjects’ characteristics and their Centroids
Distribution of the 19 subjects’ characteristics and their Centroids
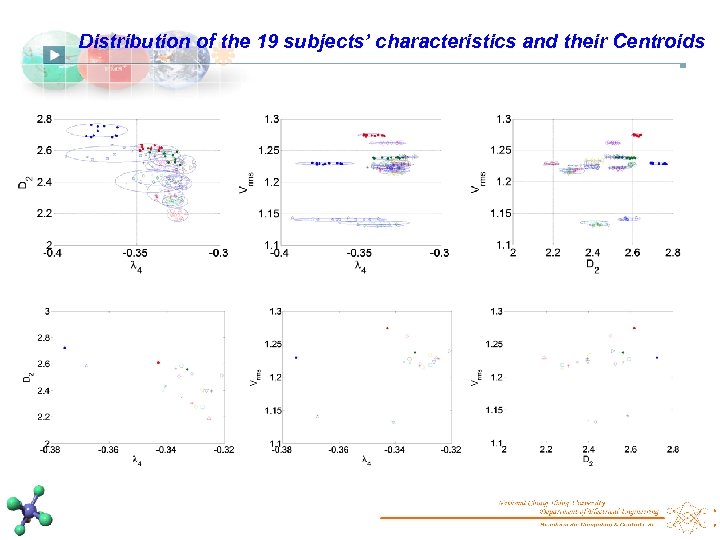
Distribution of the 19 subjects’ characteristics and their Centroids
Synchronization of two identical Lorenz systems
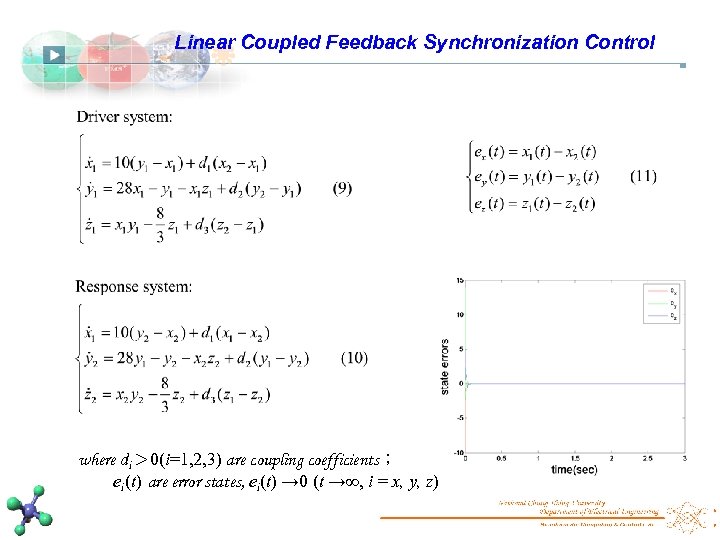
Linear Coupled Feedback Synchronization Control where di> 0(i=1, 2, 3) are coupling coefficients; ei(t) are error states, ei(t) → 0 (t →∞, i = x, y, z)
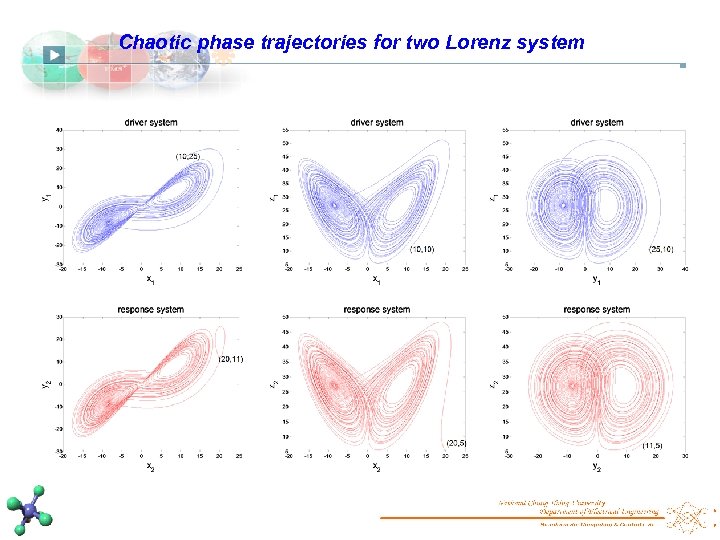
Chaotic phase trajectories for two Lorenz system
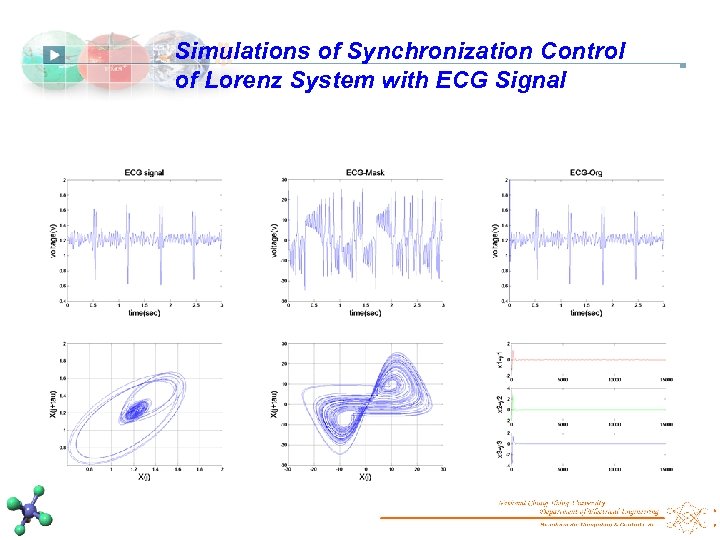
Simulations of Synchronization Control of Lorenz System with ECG Signal
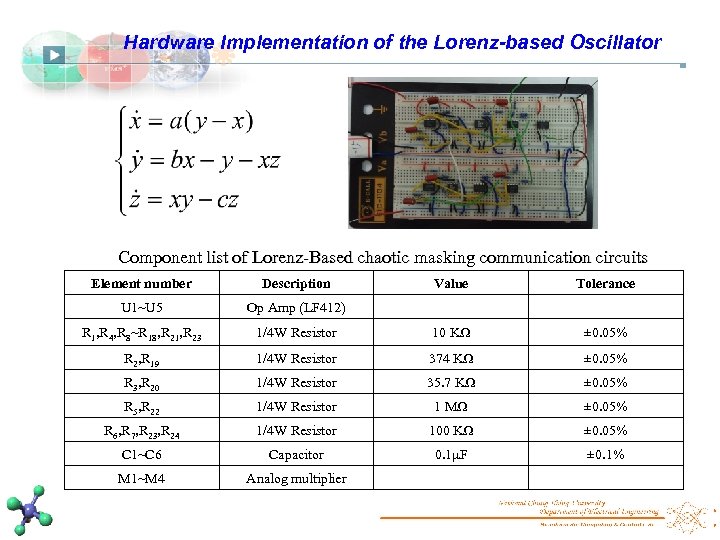
Hardware Implementation of the Lorenz-based Oscillator Component list of Lorenz-Based chaotic masking communication circuits Element number Description Value Tolerance U 1~U 5 Op Amp (LF 412) R 1, R 4, R 8~R 18, R 21, R 23 1/4 W Resistor 10 KΩ ± 0. 05% R 2, R 19 1/4 W Resistor 374 KΩ ± 0. 05% R 3, R 20 1/4 W Resistor 35. 7 KΩ ± 0. 05% R 5, R 22 1/4 W Resistor 1 MΩ ± 0. 05% R 6, R 7, R 23, R 24 1/4 W Resistor 100 KΩ ± 0. 05% C 1~C 6 Capacitor 0. 1μF ± 0. 1% M 1~M 4 Analog multiplier
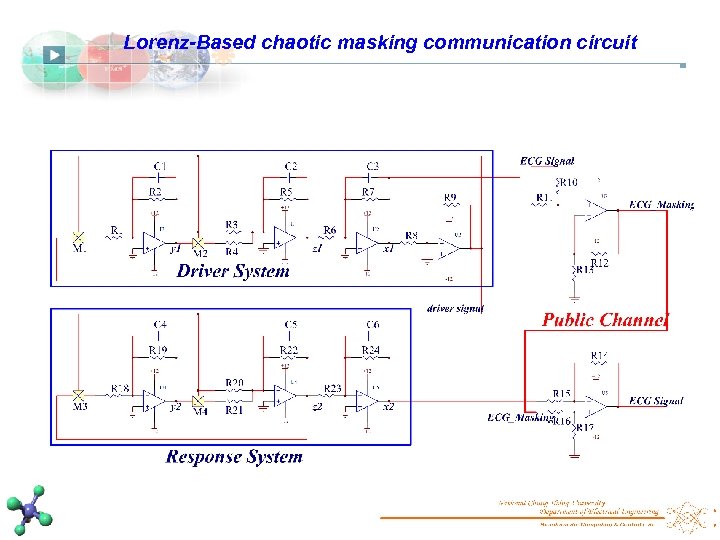
Lorenz-Based chaotic masking communication circuit
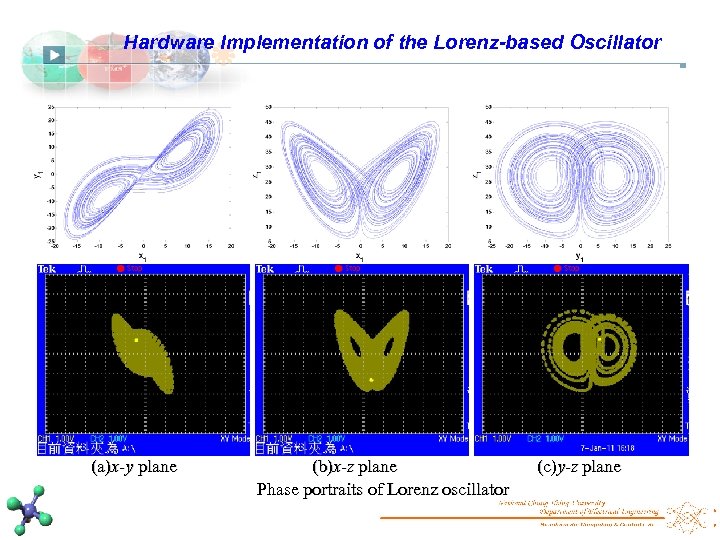
Hardware Implementation of the Lorenz-based Oscillator (a)x-y plane (b)x-z plane Phase portraits of Lorenz oscillator (c)y-z plane
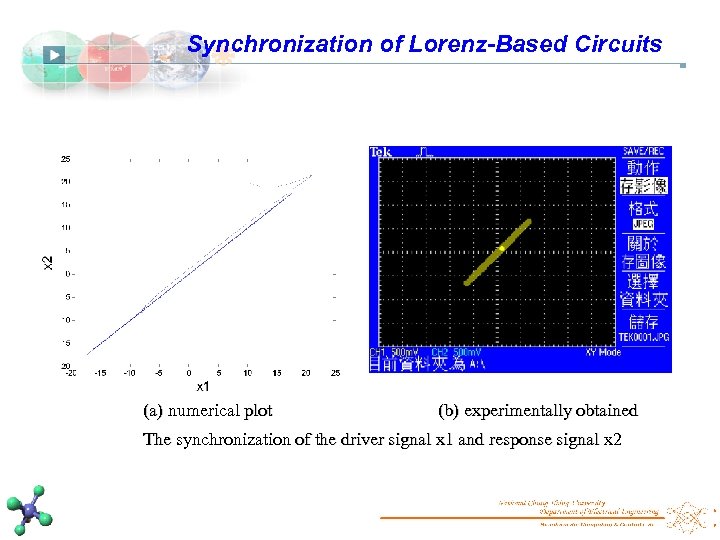
Synchronization of Lorenz-Based Circuits (a) numerical plot (b) experimentally obtained The synchronization of the driver signal x 1 and response signal x 2
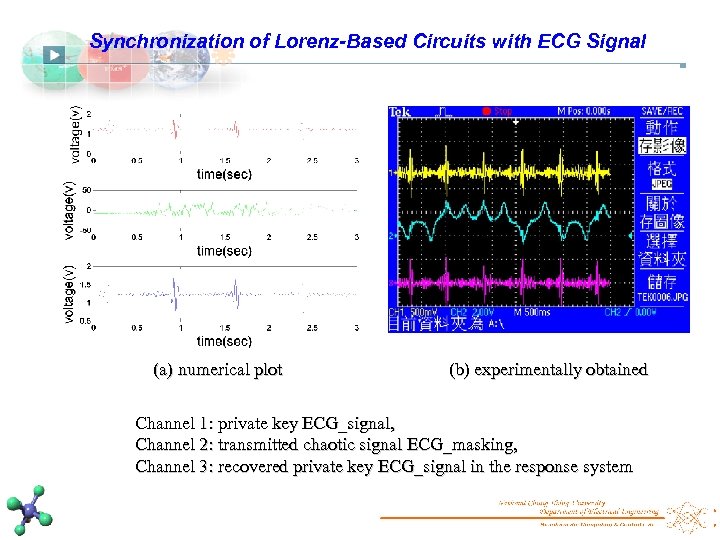
Synchronization of Lorenz-Based Circuits with ECG Signal (a) numerical plot (b) experimentally obtained Channel 1: private key ECG_signal, Channel 2: transmitted chaotic signal ECG_masking, Channel 3: recovered private key ECG_signal in the response system
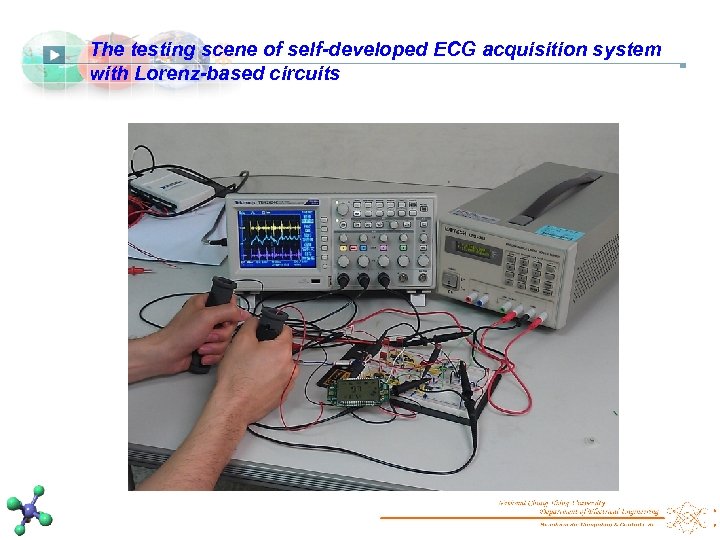
The testing scene of self-developed ECG acquisition system with Lorenz-based circuits
System Design and Secure Information Transmission
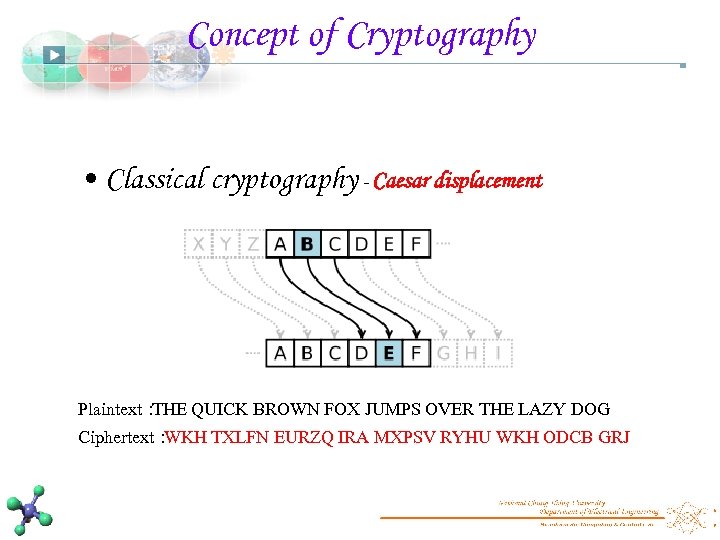
Concept of Cryptography • Classical cryptography - Caesar displacement Plaintext: THE QUICK BROWN FOX JUMPS OVER THE LAZY DOG Ciphertext: WKH TXLFN EURZQ IRA MXPSV RYHU WKH ODCB GRJ
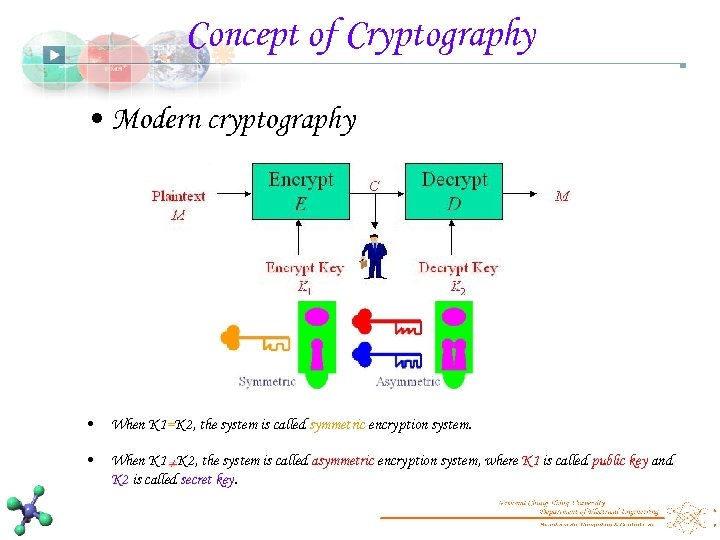
Concept of Cryptography • Modern cryptography • When K 1=K 2, the system is called symmetric encryption system. • When K 1 K 2, the system is called asymmetric encryption system, where K 1 is called public key and K 2 is called secret key.
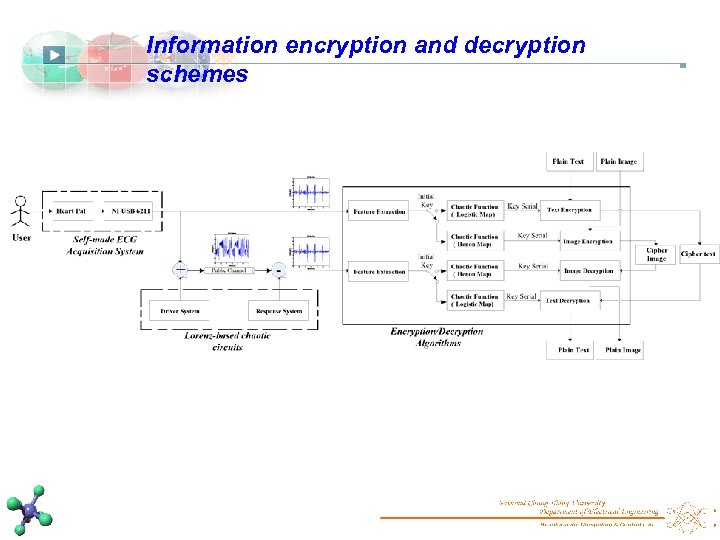
Information encryption and decryption schemes
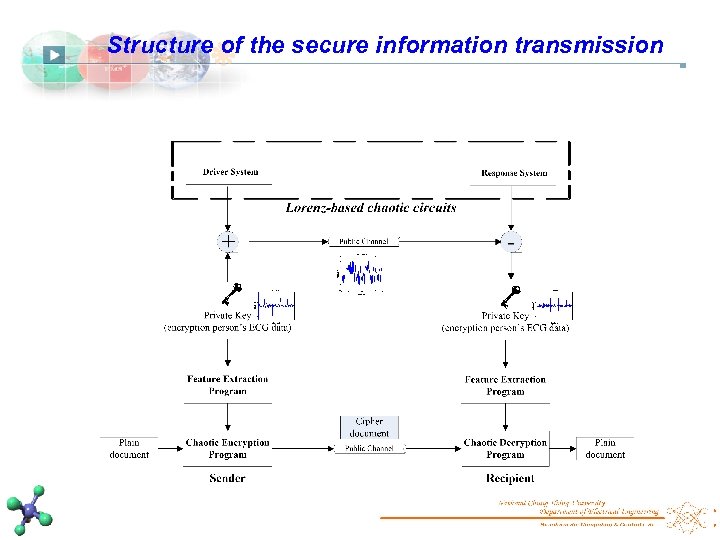
Structure of the secure information transmission
Experimental Results and Discussion
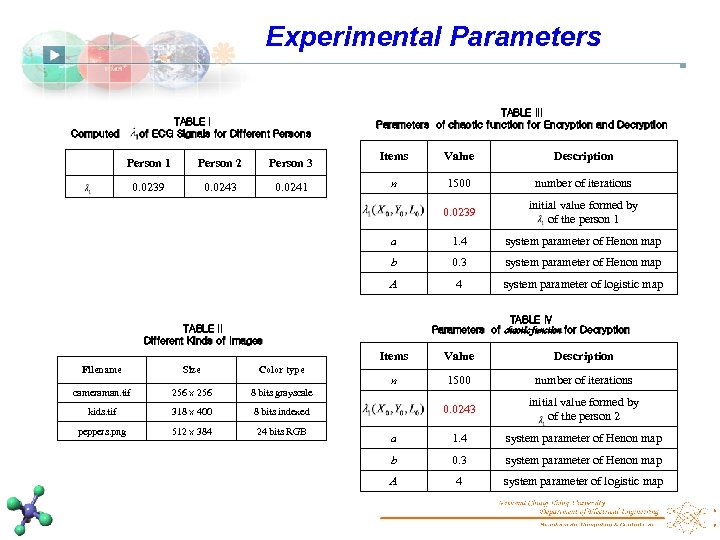
Experimental Parameters TABLE I of ECG Signals for Different Persons Computed TABLE III Parameters of chaotic function for Encryption and Decryption 0. 0243 0. 0241 n 1500 number of iterations initial value formed by of the person 1 1. 4 system parameter of Henon map 0. 3 system parameter of Henon map A 0. 0239 Description b Person 3 Value a Person 2 Items 0. 0239 Person 1 4 system parameter of logistic map TABLE IV Parameters of chaotic function for Decryption TABLE II Different Kinds of Images Items Filename Size Color type cameraman. tif 256 × 256 318 × 400 512 × 384 24 bits RGB n 1500 number of iterations 0. 0243 initial value formed by of the person 2 a 1. 4 system parameter of Henon map b 0. 3 system parameter of Henon map A 4 system parameter of logistic map 8 bits indexed peppers. png Description 8 bits grayscale kids. tif Value
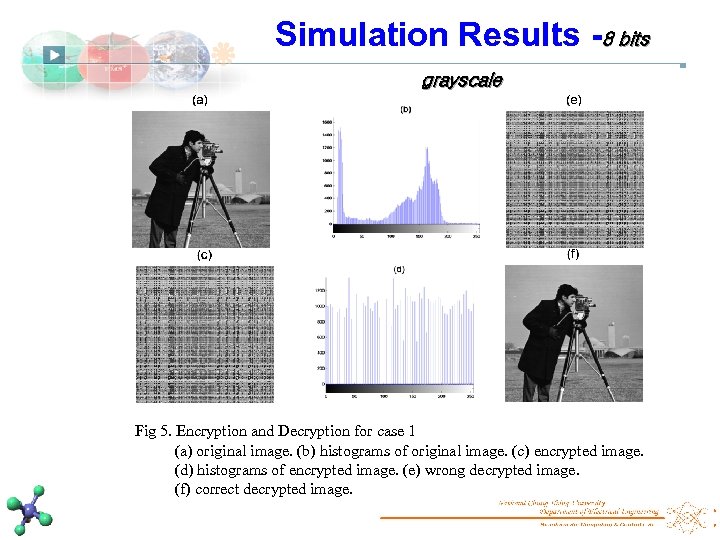
Simulation Results -8 bits grayscale Fig 5. Encryption and Decryption for case 1 (a) original image. (b) histograms of original image. (c) encrypted image. (d) histograms of encrypted image. (e) wrong decrypted image. (f) correct decrypted image.
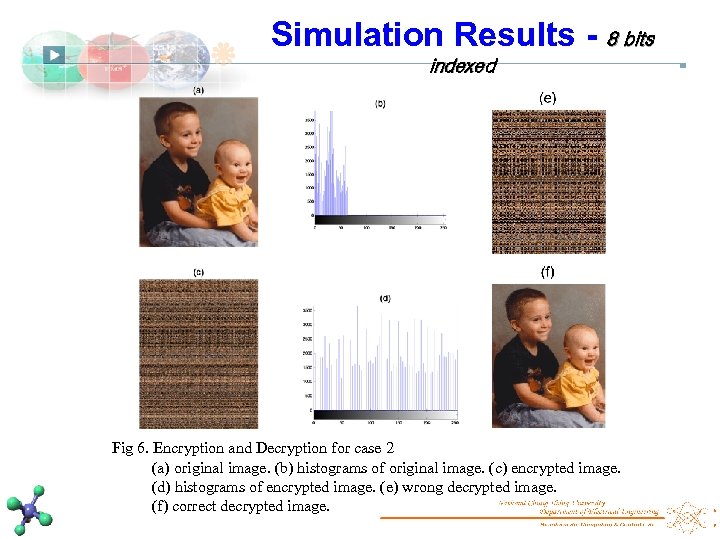
Simulation Results - 8 bits indexed Fig 6. Encryption and Decryption for case 2 (a) original image. (b) histograms of original image. (c) encrypted image. (d) histograms of encrypted image. (e) wrong decrypted image. (f) correct decrypted image.
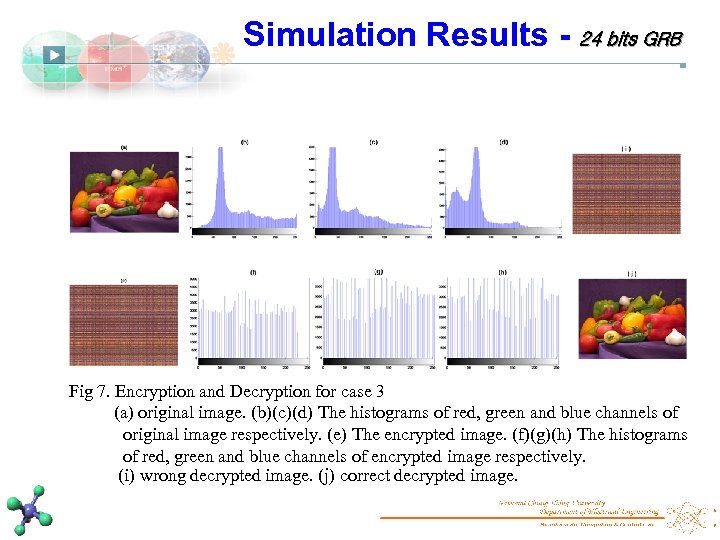
Simulation Results - 24 bits GRB Fig 7. Encryption and Decryption for case 3 (a) original image. (b)(c)(d) The histograms of red, green and blue channels of original image respectively. (e) The encrypted image. (f)(g)(h) The histograms of red, green and blue channels of encrypted image respectively. (i) wrong decrypted image. (j) correct decrypted image.
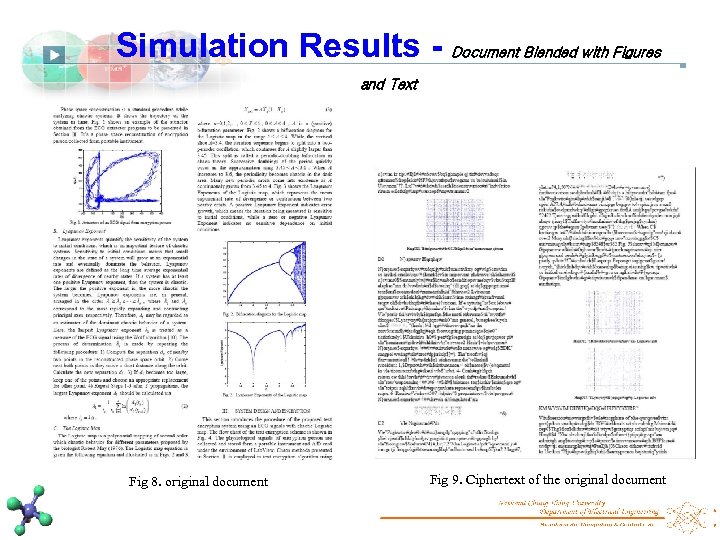
Simulation Results - Document Blended with Figures and Text Fig 8. original document Fig 9. Ciphertext of the original document
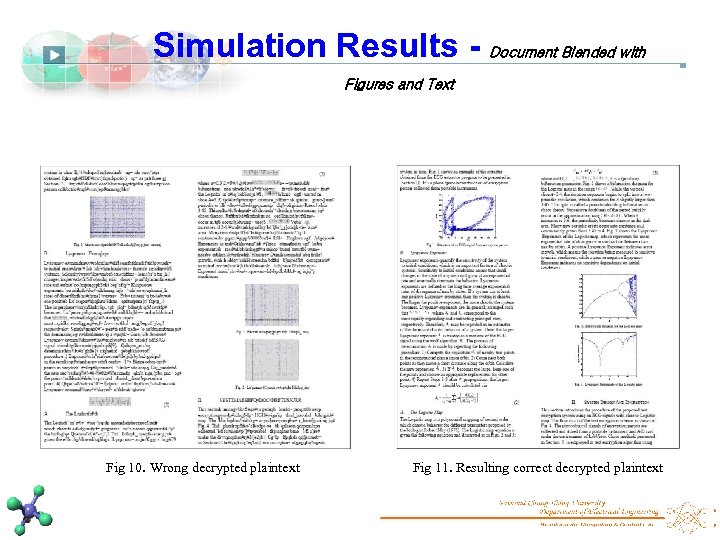
Simulation Results - Document Blended with Figures and Text Fig 10. Wrong decrypted plaintext Fig 11. Resulting correct decrypted plaintext
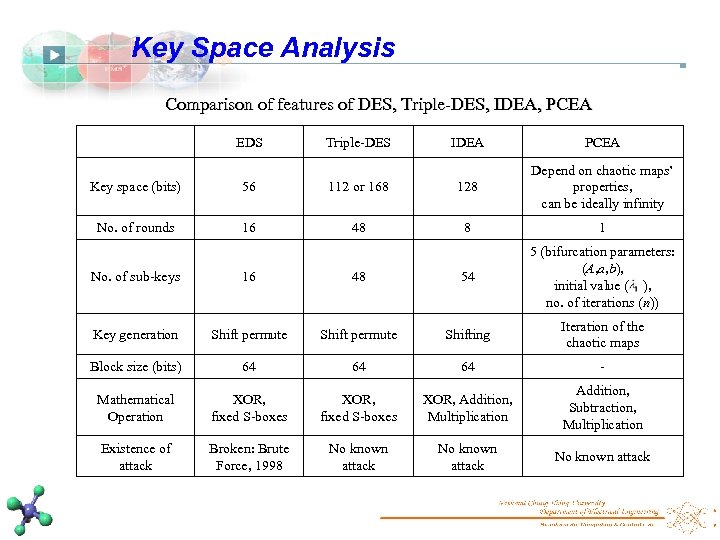
Key Space Analysis Comparison of features of DES, Triple-DES, IDEA, PCEA EDS Triple-DES IDEA PCEA Key space (bits) 56 112 or 168 128 Depend on chaotic maps’ properties, can be ideally infinity No. of rounds 16 48 8 1 No. of sub-keys 16 48 54 5 (bifurcation parameters: (A, a, b), initial value ( ), no. of iterations (n)) Key generation Shift permute Shifting Iteration of the chaotic maps Block size (bits) 64 64 64 - Mathematical Operation XOR, fixed S-boxes XOR, Addition, Multiplication Addition, Subtraction, Multiplication Existence of attack Broken: Brute Force, 1998 No known attack
Conclusions This study has presented a theoretical and experimental study on chaos synchronization and masking of data communication using electronic devices described by the Lorenz equations, and showed that the private key created by ECG signals can be recovered from a chaotic carrier using a response system whose chaotic dynamics is synchronized with a driver system. We investigate the use of ECG signal features from nonlinear dynamic modeling for information encryption, and present a personalized encryption scheme based on the individual-specific features of ECG as a personal key. Experimental results have proved its feasibility and effectiveness. Moreover, the encryption time shows its applicability in real-time applications for image encryption and data transmission. The proposed system can thus be used for personalized secure data storage and transmission.
Future Work The chaotic features of ECG that the characteristic distributions appear the proposed features would be appropriate for biometric identification. In the current stage of this research, the recognition process was conducted off-line and the effectiveness of the proposed methods was tested on the normal rest subjects. Investigation of the on-line operation to demonstrate possibility of the proposed verification systems in practical applications such as the tested subjects are under stressed or after exercise should be further studied. On the application side, our proposed biometric identification can be applied to the access control system, such as electromagnetic induction cards, locks, etc.
![List of Publication [J 1] C. K. Chen, C. L. Lin, C. T. Chiang, List of Publication [J 1] C. K. Chen, C. L. Lin, C. T. Chiang,](https://present5.com/presentation/d1f6d632ca7803e34731c2844ddf50e0/image-56.jpg)
List of Publication [J 1] C. K. Chen, C. L. Lin, C. T. Chiang, and S. L. Lin, “Information encryption using ECG signals with chaotic functions, ” Information Sciences, vol. 193, pp. 125 -140, 2012. (SCI, Impact Factor: 3. 291, Rank: 6/116) (NSC-99 - 2221 -E- 005 -066). [J 2] C. K. Chen, C. L. Lin, S. L. Lin, Y. M. Chiu, and C. T. Chiang, “A Chaotic Theoretical Approach to ECG-Based Identity Recognition , ” IEEE Computational Intelligence Magazine , 2013, (SCI) (NSC-99 -2221 -E-005 -066), revised. [J 3] C. K. Chen, C. L. Lin, C. T. Chiang, and S. L. Lin, “Personalized Information Encryption Using ECG Signals with Chaotic Functions and Secure Transmissions via Synchronized Circuits, ” IEEE Transactions on System, Man , and Cybernetics, Part B, 2013, (SCI) (NSC-99 -2221 -E-005 -066), revised. [C 1] C. K. Chen, C. L. Lin, and Y. M. Chiu, “Data Encryption Using ECG Signals with Chaotic Henon Map, ” in Proc. of International Conference on Information Science and Applications, pp. 1 -5, Seoul, Korea, 2010. [C 2] C. K. Chen and C. L. Lin, “Text Encryption Using ECG signals with Chaotic Logistic Map, ” in Proc. of IEEE International Conference on Industrial Technology, pp. 1741 -1746, Taichung, Taiwan, 2010. [C 3] C. K. Chen, C. L. Lin, and Yen-Ming Chiu, “Individual Identification Based on Chaotic Electrocardiogram Signals, ” in Proc. of IEEE International Conference on Industrial Technology, pp. 1765 -1770, Beijing, China, 2011. [C 4]Y. H. Hsu, C. L. Lin, C. K. Chen, C. T. Chiang, and W. T. Yang, “Health Care Platform Based on Acquisition of ECG for HRV analysis, ” in Proc. of International Conference on Industrial Informatics, Beijing, China, 2012.

Thanks for your attention
d1f6d632ca7803e34731c2844ddf50e0.ppt