e8e3e81c71faefd94a52699815f215c0.ppt
- Количество слайдов: 50
XML Security By Rami Amar January 2003

Introduction 8 XML is a growing standard 8 Security integration is essential 8 XML Security combines legacy cryptographic technologies with XML technologies to provide a secure environment for users and applications 2

On The Lecture … 8 XML Digital Signature Integrity & Authentication 8 XML Encryption Confidentiality 8 XML Key Management Public Key Registration&Validation 8 P 3 P Privacy Policies & Preferences 8 WS Security framework for Web Services 8 Digital Rights Management (Xr. ML) 8 SAML Conveying Authentication 8 XACML Access Control 3
What Else? 8 Some general XML Background 8 Some SOAP Background 8 Some Security Background 4
So What’s this XML? ? 8 e. Xtended Markup Language (like HTML, just extended) 8 Syntax and rules for structuring information 8 Anyone can create a vocabulary and use it 8 Any application can learn a vocabulary and read it 8 We tell apart from vocabularies using namespaces 5
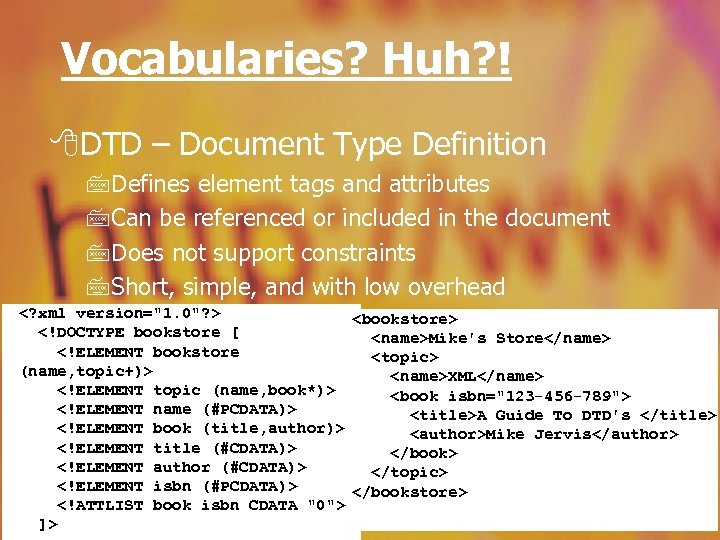
Vocabularies? Huh? ! 8 DTD – Document Type Definition 7 Defines element tags and attributes 7 Can be referenced or included in the document 7 Does not support constraints 7 Short, simple, and with low overhead <? xml version="1. 0"? > <bookstore> <!DOCTYPE bookstore [ <name>Mike's Store</name> <!ELEMENT bookstore <topic> (name, topic+)> <name>XML</name> <!ELEMENT topic (name, book*)> <book isbn="123 -456 -789"> <!ELEMENT name (#PCDATA)> <title>A Guide To DTD's </title> <!ELEMENT book (title, author)> <author>Mike Jervis</author> <!ELEMENT title (#CDATA)> </book> <!ELEMENT author (#CDATA)> </topic> <!ELEMENT isbn (#PCDATA)> </bookstore> <!ATTLIST book isbn CDATA "0"> 6 ]>
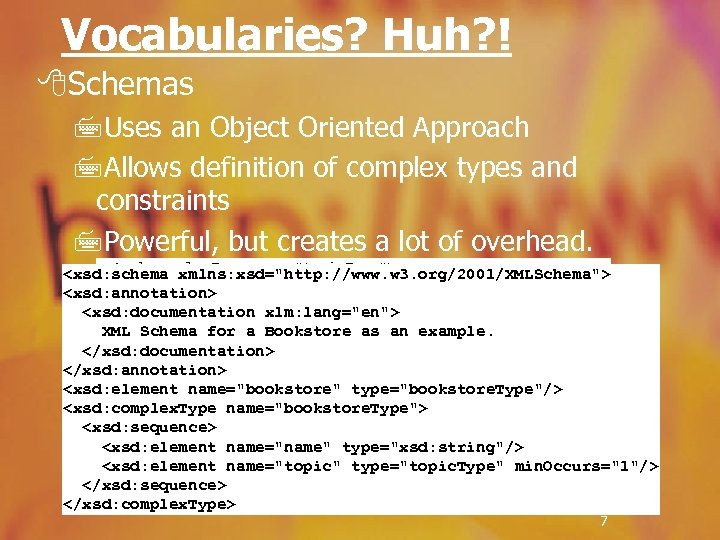
Vocabularies? Huh? ! 8 Schemas 7 Uses an Object Oriented Approach 7 Allows definition of complex types and constraints 7 Powerful, but creates a lot of overhead. <xsd: complex. Type name="topic. Type"> <xsd: schema xmlns: xsd="http: //www. w 3. org/2001/XMLSchema"> <xsd: element name="name" type="xsd: string"/> <xsd: annotation> name="book" type="book. Type" min. Occurs="0"/> <xsd: element <xsd: documentation xlm: lang="en"> </xsd: complex. Type> XML Schema for aname="book. Type"> an example. <xsd: complex. Type Bookstore as <xsd: element name="title" type="xsd: string"/> </xsd: documentation> <xsd: element </xsd: annotation> name="author" type="xsd: string"/> <xsd: attribute name="isbn" type="isbn. Type"/> <xsd: element name="bookstore" type="bookstore. Type"/> </xsd: complex. Type> <xsd: complex. Type name="bookstore. Type"> <xsd: simple. Type name="isbn. Type"> <xsd: sequence> <xsd: restriction base="xsd: string"> <xsd: element name="name" type="xsd: string"/> <xsd: pattern value="[0 -9]{3}[-][0 -9]{3}"/> <xsd: element name="topic" type="topic. Type" min. Occurs="1"/> </xsd: restriction> </xsd: simple. Type> </xsd: sequence> </xsd: complex. Type> 7
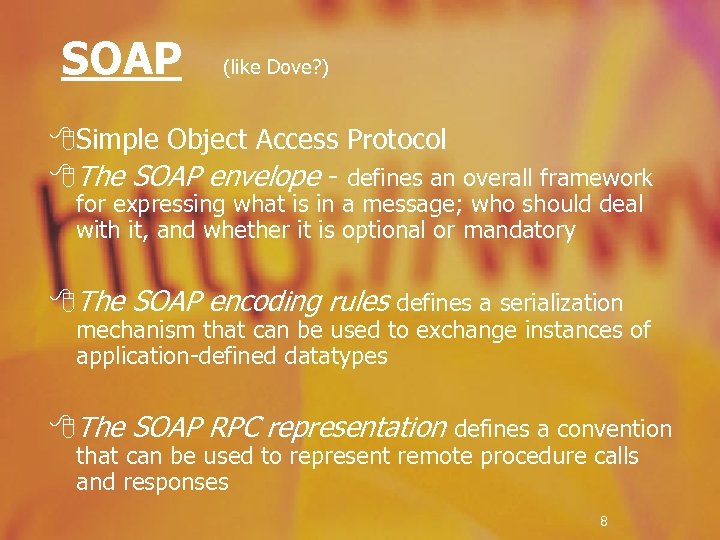
SOAP (like Dove? ) 8 Simple Object Access Protocol 8 The SOAP envelope - defines an overall framework for expressing what is in a message; who should deal with it, and whether it is optional or mandatory 8 The SOAP encoding rules defines a serialization mechanism that can be used to exchange instances of application-defined datatypes 8 The SOAP RPC representation defines a convention that can be used to represent remote procedure calls and responses 8
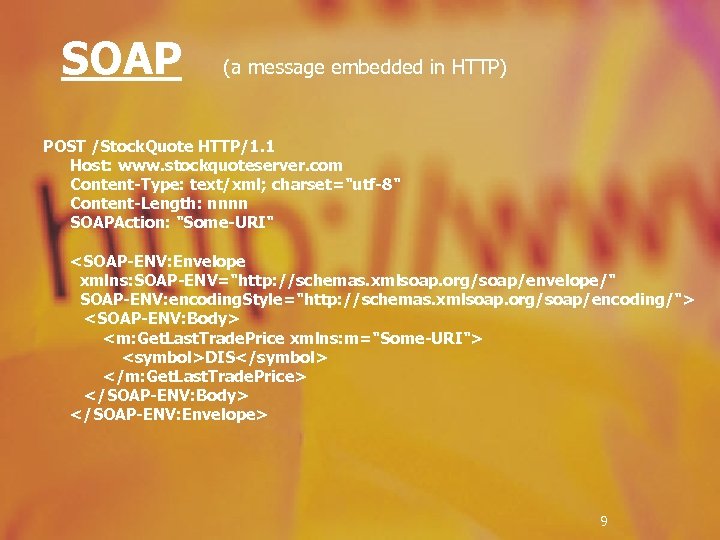
SOAP (a message embedded in HTTP) POST /Stock. Quote HTTP/1. 1 Host: www. stockquoteserver. com Content-Type: text/xml; charset="utf-8" Content-Length: nnnn SOAPAction: "Some-URI" <SOAP-ENV: Envelope xmlns: SOAP-ENV="http: //schemas. xmlsoap. org/soap/envelope/" SOAP-ENV: encoding. Style="http: //schemas. xmlsoap. org/soap/encoding/"> <SOAP-ENV: Body> <m: Get. Last. Trade. Price xmlns: m="Some-URI"> <symbol>DIS</symbol> </m: Get. Last. Trade. Price> </SOAP-ENV: Body> </SOAP-ENV: Envelope> 9
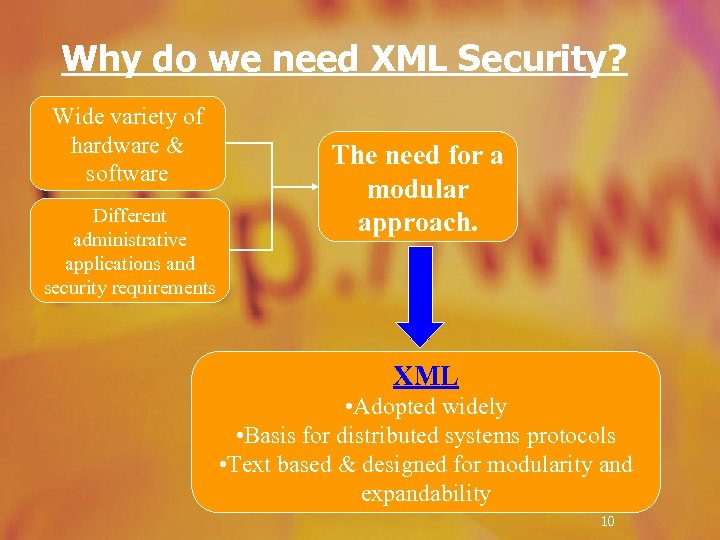
Why do we need XML Security? Wide variety of hardware & software Different administrative applications and security requirements The need for a modular approach. XML • Adopted widely • Basis for distributed systems protocols • Text based & designed for modularity and expandability 10
What’s wrong with older Enryption tools? 8 They encrypt whole documents only 8 They are not designed for the content management approach 8 They provide security only over the data connection 11
So What’s so good about XML Security? 8 It provides means for integrity, authentication, and confidentiality 8 It is integrated with XML and maintains all XML’s advantages. 8 It also provides end-to-end security Sounds Peachy, But… 8 It damages documents searchability 8 Gets complicated when it comes to signatures 8 Vulnerable to plain text attacks… 12
Security Mumbo Jumbo 8 Authentication Determine identity of a person/object 8 Authorization Determine what the person is allowed to do 8 Integrity Ensure the data was not altered on its way to you 8 Signature Validate the source of the data 8 Confidentiality Limit the people allowed to view the data 8 Privacy Make sure no one abuses your data 8 Digital Rights Management Limit users from doing whatever they want 13
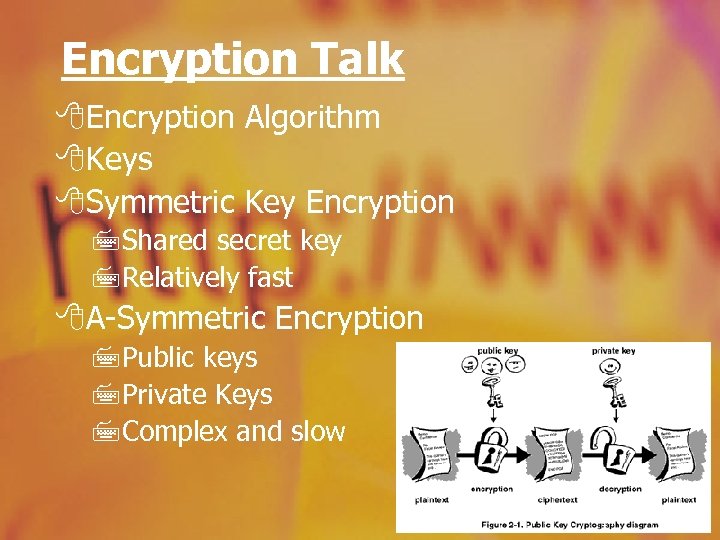
Encryption Talk 8 Encryption Algorithm 8 Keys 8 Symmetric Key Encryption 7 Shared secret key 7 Relatively fast 8 A-Symmetric Encryption 7 Public keys 7 Private Keys 7 Complex and slow 14
XML Security Standards 8 XML Vocabulary for security information is defined 8 Standards comply with other XML standards 8 Security should be applied to: 7 Whole XML Documents 7 Specific XML Elements 7 XML Element Content 8 Security is associated with content (not transport, like SSL) 8 XML Security uses existing crypto methods 15
XML Digital Signature 8 The Purpose: 7 DS creates & verifies portable electronic signatures 7 DS provides persistent content integrity Reminder: a signature can be created only by one person, A, but anyone can verify that A signed it 16

XML Digital Signature 8 Features: 7 You can sign just about anything in the document 7 You can use XML Canonicalization for robustness 7 You can separate the signature from the document 17
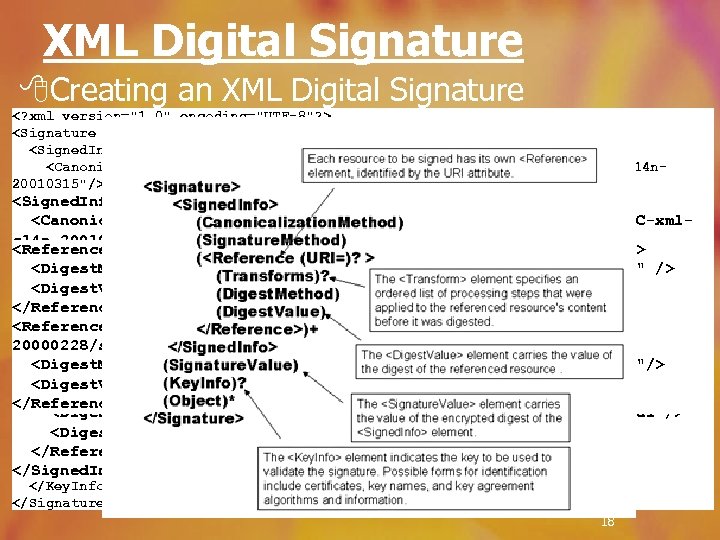
XML Digital Signature 8 Creating an XML Digital Signature <? xml version="1. 0" encoding="UTF-8"? > <Signature xmlns="http: //www. w 3. org/2000/09/xmldsig#"> <Signed. Info Id="foobar"> <Canonicalization. Method Algorithm="http: //www. w 3. org/TR/2001/REC-xml-c 14 n 20010315"/> <Signature. Method Algorithm="http: //www. w 3. org/2000/09/xmldsig#dsa-sha 1" /> <Signed. Info Id="foobar"> <Reference URI="http: //www. abccompany. com/news/2000/03_27_00. htm"> <Canonicalization. Method Algorithm="http: //www. w 3. org/TR/2001/REC-xml<Digest. Method c 14 n-20010315"/> Algorithm="http: //www. w 3. org/2000/09/xmldsig#sha 1" /> <Reference URI="http: //www. abccompany. com/news/2000/03_27_00. htm"> <Digest. Value>j 6 lwx 3 rv. EPO 0 v. Kt. Mup 4 Nbe. Vu 8 nk=</Digest. Value> <Signature. Method Algorithm="http: //www. w 3. org/2000/09/xmldsig#dsa-sha 1" </Reference> <Digest. Method Algorithm="http: //www. w 3. org/2000/09/xmldsig#sha 1" /> /> <Reference URI="http: //www. w 3. org/TR/2000/WD-xmldsig-core-20000228/signature<Digest. Value>j 6 lwx 3 rv. EPO 0 v. Kt. Mup 4 Nbe. Vu 8 nk=</Digest. Value> <Reference URI="http: //www. abccompany. com/news/2000/03_27_00. htm"> ex. xml"> </Reference> <Digest. Method Algorithm="http: //www. w 3. org/2000/09/xmldsig#sha 1"/> <Digest. Method Algorithm="http: //www. w 3. org/2000/09/xmldsig#sha 1" /> <Reference URI="http: //www. w 3. org/TR/2000/WD-xmldsig-core<Digest. Value>Ur. XLDLBIta 6 sko. V 5/A 8 Q 38 GEw 44=</Digest. Value> <Digest. Value>j 6 lwx 3 rv. EPO 0 v. Kt. Mup 4 Nbe. Vu 8 nk=</Digest. Value> 20000228/signature-ex. xml"> </Reference> <Digest. Method Algorithm="http: //www. w 3. org/2000/09/xmldsig#sha 1"/> </Signed. Info>URI="http: //www. w 3. org/TR/2000/WD-xmldsig-core<Reference <Digest. Value>Ur. XLDLBIta 6 sko. V 5/A 8 Q 38 GEw 44=</Digest. Value> <Signature. Value>MC 0 E~LE=</Signature. Value> 20000228/signature-ex. xml"> <Key. Info> </Reference> <Digest. Method Algorithm="http: //www. w 3. org/2000/09/xmldsig#sha 1"/> <X 509 Data> <Digest. Value>Ur. XLDLBIta 6 sko. V 5/A 8 Q 38 GEw 44=</Digest. Value> <X 509 Subject. Name>CN=Ed Simon, O=XMLSec Inc. , ST=OTTAWA, C=CA</X 509 Subject. Name> </Reference> <X 509 Certificate> MIID 5 j. CCA 0+g. A. . . l. VN </X 509 Certificate> </X 509 Data> </Signed. Info> </Key. Info> </Signature> 18

XML Digital Signature 8 Verifying an XML Signature: 7 Recalculate the signature of <Signed. Info> 7 If it’s correct, recalculate the signature of each reference. 19
XML Encryption 8 Purpose: 7 Allow users to encrypt and decrypt data 7 Provide confidentiality in transport and in storage 8 Features: 7 Defined vocabulary for ciphers and encryption information 7 Both XML and non-XML content can be encrypted 7 Encryption granularity – element content 7 Encrypted infromation stays in XML form. 7 Compatible with signatures 7 Supports for many encryption algorithms 20
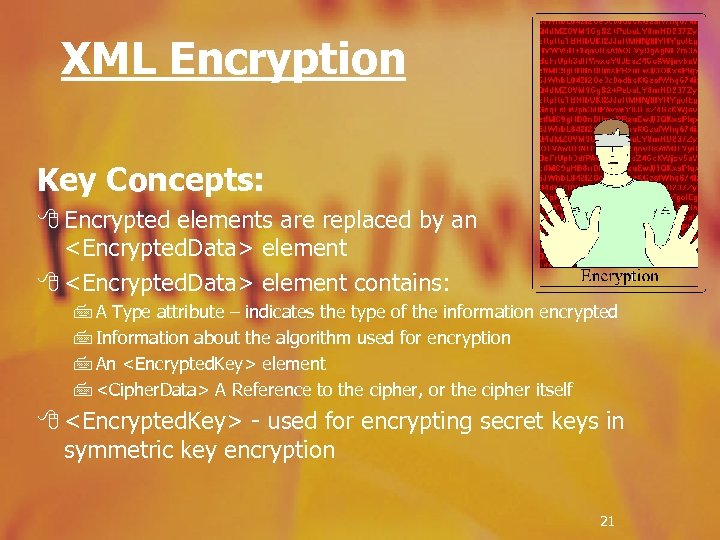
XML Encryption Key Concepts: 8 Encrypted elements are replaced by an <Encrypted. Data> element 8 <Encrypted. Data> element contains: 7 A Type attribute – indicates the type of the information encrypted 7 Information about the algorithm used for encryption 7 An <Encrypted. Key> element 7 <Cipher. Data> A Reference to the cipher, or the cipher itself 8 <Encrypted. Key> - used for encrypting secret keys in symmetric key encryption 21
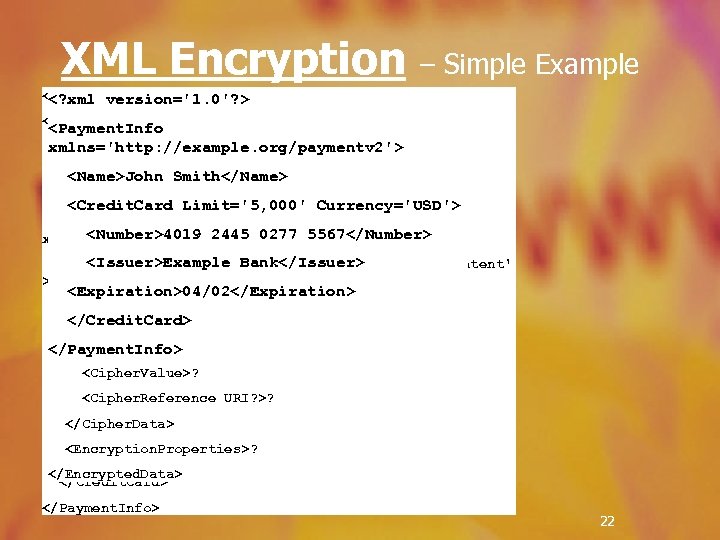
XML Encryption – Simple Example <? xml version='1. 0'? > Mime. Type? <Encrypted. Data Id? Type? Encoding? > <Payment. Info xmlns='http: //example. org/paymentv 2'> <Payment. Info <Encryption. Method/>? <Name>John Smith</Name> xmlns='http: //example. org/paymentv 2'> <ds: Key. Info> Smith</Name> <Credit. Card Limit='5, 000' Currency='USD'> <Name>John <Encrypted. Key>? <Number> <Credit. Card Limit='5, 000' Currency='USD'> <Agreement. Method>? <Encrypted. Data <Number>4019 2445 0277 5567</Number> xmlns='http: //www. w 3. org/2001/04/xmlenc#‘ <ds: Key. Name>? <Issuer>Example Bank</Issuer> Type='http: //www. w 3. org/2001/04/xmlenc#Content' <ds: Retrieval. Method>? > <Expiration>04/02</Expiration> <ds: *>? <Cipher. Data> </Credit. Card> </ds: Key. Info>? <Cipher. Value>A 23 B 45 C 56</Cipher. Value> <Cipher. Data> </Payment. Info> </Cipher. Data> <Cipher. Value>? </Encrypted. Data> <Cipher. Reference URI? >? </Number> </Cipher. Data> <Issuer>Example Bank</Issuer> <Encryption. Properties>? <Expiration>04/02</Expiration> </Encrypted. Data> </Credit. Card> </Payment. Info> 22
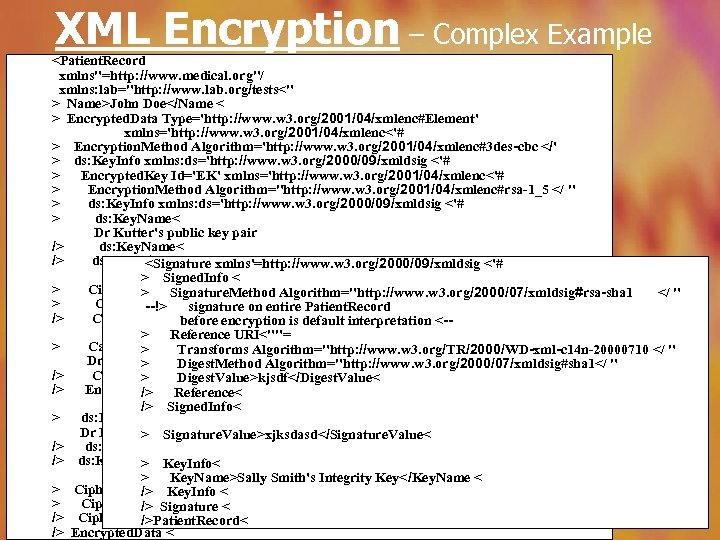
XML Encryption – Complex Example <Patient. Record xmlns"=http: //www. medical. org"/ xmlns: lab="http: //www. lab. org/tests<" > Name>John Doe</Name < > Encrypted. Data Type='http: //www. w 3. org/2001/04/xmlenc#Element' xmlns='http: //www. w 3. org/2001/04/xmlenc<'# > Encryption. Method Algorithm='http: //www. w 3. org/2001/04/xmlenc#3 des-cbc </' > ds: Key. Info xmlns: ds='http: //www. w 3. org/2000/09/xmldsig <'# > Encrypted. Key Id='EK' xmlns='http: //www. w 3. org/2001/04/xmlenc<'# > Encryption. Method Algorithm="http: //www. w 3. org/2001/04/xmlenc#rsa-1_5 </ " > ds: Key. Info xmlns: ds='http: //www. w 3. org/2000/09/xmldsig <'# > ds: Key. Name< Dr Kutter's public key pair /> ds: Key. Name< /> ds: Key. Info < <Signature xmlns'=http: //www. w 3. org/2000/09/xmldsig <'# > Signed. Info < > Cipher. Data< Signature. Method Algorithm="http: //www. w 3. org/2000/07/xmldsig#rsa-sha 1 > </ " > Cipher. Value>xyzabc</Cipher. Value< --!> signature on entire Patient. Record /> Cipher. Data < before encryption is default interpretation <-> Reference URI<""= > Carried. Key. Name< > Transforms Algorithm="http: //www. w 3. org/TR/2000/WD-xml-c 14 n-20000710 </ " Dr Kutter's symmetric key Algorithm="http: //www. w 3. org/2000/07/xmldsig#sha 1</ " > Digest. Method /> Carried. Key. Name< > Digest. Value>kjsdf</Digest. Value< /> Encrypted. Key Reference< < /> /> Signed. Info< > ds: Key. Name< Dr Kutter's symmetric key > Signature. Value>xjksdasd</Signature. Value< /> ds: Key. Name< /> ds: Key. Info < Key. Info< > > Key. Name>Sally Smith's Integrity Key</Key. Name < > Cipher. Data< Key. Info < /> > Cipher. Value>a 17 xj 2 z</Cipher. Value< /> Signature < /> Cipher. Data< />Patient. Record< 23 /> Encrypted. Data <

XML Key Management Specification Purpose: 8 XKMS is designed to manage the sharing of public keys. 8 Managing includes verifying signatures 8 Managing also includes encrypting messages to recipients. 8 XKMS defines XML messages for registering and finding keys 8 XKMS saves the work for applications 24
XKMS Features: 8 XKRSS – XML Key Registration Service Specification 7 Allows registering key pairs 7 Saves the key pairs as <Key. Binding> elements 7 Supports backing up & restoring keys 8 XKISS – XML Key Information Service Specification 7 Enables clients to request <Key. Binding>’s associated with <Key. Info> elements. 7 LOCATE operation – locates a requested key 7 VALIDATE operation – validates <Key. Binding>’s 8 XKMS defines SOAP binding 25
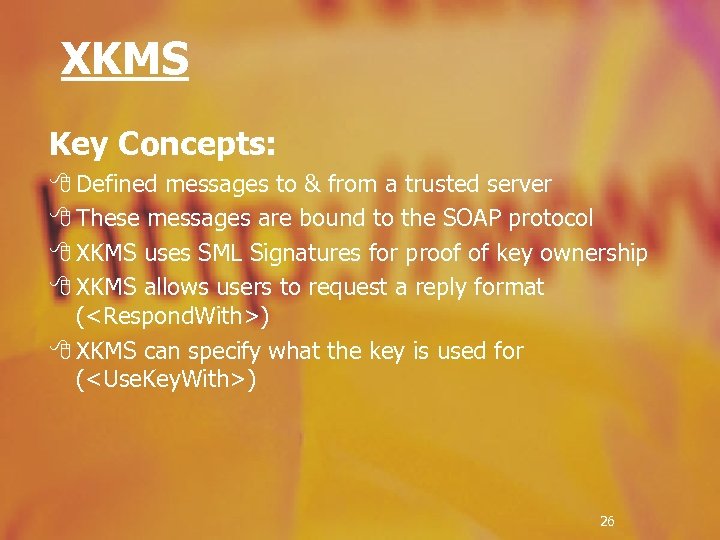
XKMS Key Concepts: 8 Defined messages to & from a trusted server 8 These messages are bound to the SOAP protocol 8 XKMS uses SML Signatures for proof of key ownership 8 XKMS allows users to request a reply format (<Respond. With>) 8 XKMS can specify what the key is used for (<Use. Key. With>) 26
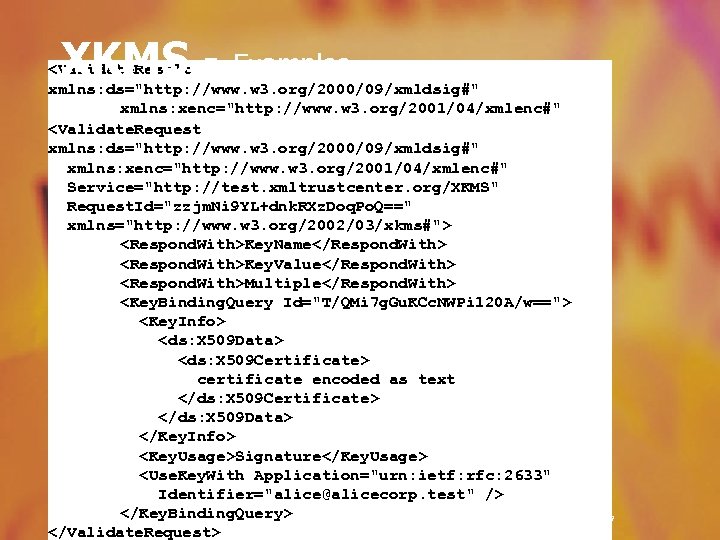
XKMS - Examples <Validate. Result xmlns: ds="http: //www. w 3. org/2000/09/xmldsig#" xmlns: xenc="http: //www. w 3. org/2001/04/xmlenc#" Service="http: //test. xmltrustcenter. org/XKMS" <Validate. Request Result. Major="Success" xmlns: ds="http: //www. w 3. org/2000/09/xmldsig#" Request. Id="zzjm. Ni 9 YL+dnk. RXz. Doq. Po. Q==" xmlns: xenc="http: //www. w 3. org/2001/04/xmlenc#" Response. Id="0 Wein. JVdby. BKru. Xhiq. Tscg==" Service="http: //test. xmltrustcenter. org/XKMS" xmlns="http: //www. w 3. org/2002/03/xkms#"> Request. Id="zzjm. Ni 9 YL+dnk. RXz. Doq. Po. Q==" <Key. Binding Id="m 0/p 5 bekjem. I 4 t. V+FPBkig=="> xmlns="http: //www. w 3. org/2002/03/xkms#"> <Key. Info> <Respond. With>Key. Name</Respond. With> <ds: Key. Value> <Respond. With>Key. Value</Respond. With> <ds: RSAKey. Value> <Respond. With>Multiple</Respond. With> <ds: Modulus>. . . </ds: Modulus> <Key. Binding. Query Id="T/QMi 7 g. Gu. KCc. NWPi 120 A/w=="> <ds: Exponent>AQAB</ds: Exponent> <Key. Info> </ds: RSAKey. Value> <ds: X 509 Data> </ds: Key. Value> <ds: X 509 Certificate> </Key. Info> certificate encoded as text <Key. Usage>Signature</Key. Usage> </ds: X 509 Certificate> <Use. Key. With Application="urn: ietf: rfc: 2633" </ds: X 509 Data> Identifier="alice@alicecorp. test" /> </Key. Info> <Reason>Issuer. Trust</Reason> <Key. Usage>Signature</Key. Usage> <Reason>Revocation. Status</Reason> <Use. Key. With Application="urn: ietf: rfc: 2633" <Reason>Validity. Interval</Reason> Identifier="alice@alicecorp. test" /> </Key. Binding. Query> </Validate. Result> </Validate. Request> 27
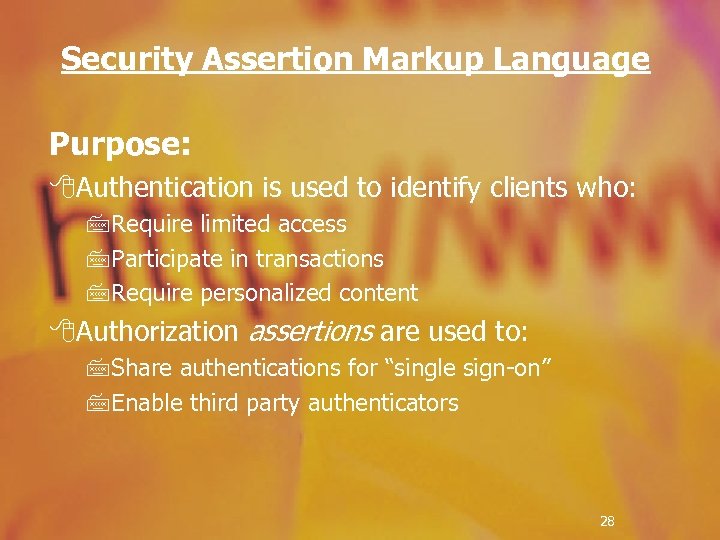
Security Assertion Markup Language Purpose: 8 Authentication is used to identify clients who: 7 Require limited access 7 Participate in transactions 7 Require personalized content 8 Authorization assertions are used to: 7 Share authentications for “single sign-on” 7 Enable third party authenticators 28
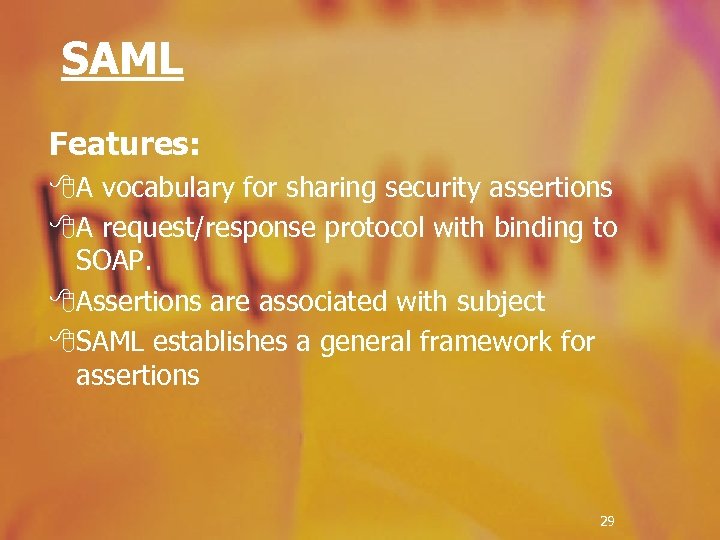
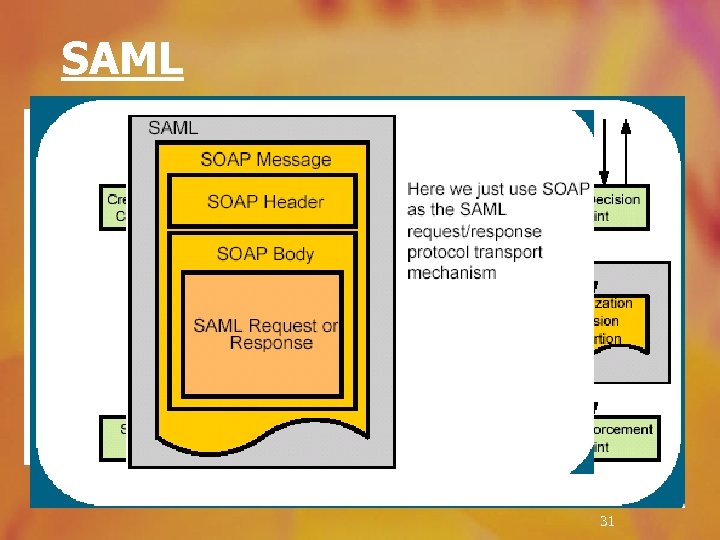
SAML Features: 8 A vocabulary for sharing security assertions 8 A request/response protocol with binding to SOAP. 8 Assertions are associated with subject 8 SAML establishes a general framework for assertions 29
SAML Key Concepts 8 Detailed authentication & authorization expressions 8 Schema for Security Assertions 7 Types: Authentication, Attribute, Authorization Decision, user defined 7 Information in each Assertion: : Assertion ID : Subject (name + security domain) : Conditions for assertion validity : Any additional info (such as ‘how the assertion was created’) 7 Examples: : Authorization decision: by subject S, for access type A, to resource R, given evidence E. 30
SAML 31

SAML Implementations 8 JSAML – A toolkit by Netegrity (http: //www. netegrity. com/) 8 JSR 155 (Java Community Process) 32
XML Access Control Markup language Purpose: 8 XACML defines a vocabulary for making the authorization rules. Features: 8 A defined vocabulary for expressing authorization rules 8 A defined vocabulary for expressing condition for rules 8 Rules combinations and evaluation 8 Policies which apply rules to subjects 33
XML Access Control Markup language Key Concepts: 8 Compatibility with SAML (same subject/action definitions) 8 Rules are defined as targets, effects and conditions 8 Target – includes resources, subjects, and actions 8 Effect - <Allow|Deny> 8 Conditions – predicates defined in XACML 8 Policy – A collection of rules, and obligations (actions performed on authorization) 34
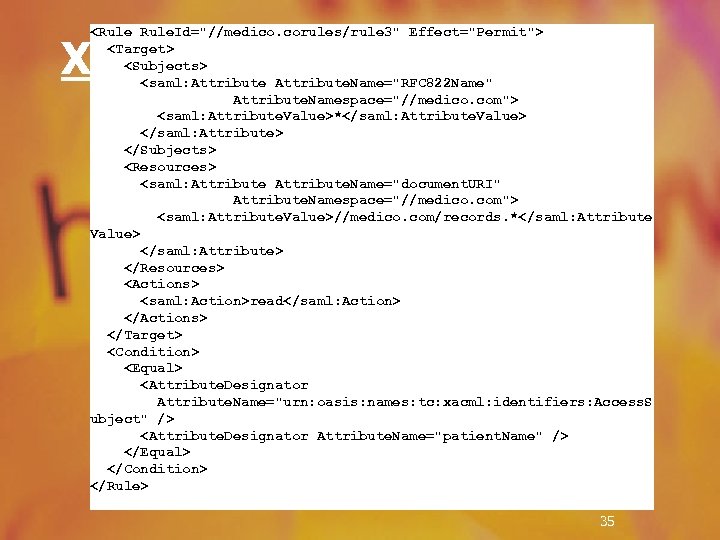
<Rule. Id="//medico. corules/rule 3" Effect="Permit"> <Target> <Subjects> <saml: Attribute. Name="RFC 822 Name" Attribute. Namespace="//medico. com"> <saml: Attribute. Value>*</saml: Attribute. Value> </saml: Attribute> </Subjects> <Resources> <saml: Attribute. Name="document. URI" Attribute. Namespace="//medico. com"> <saml: Attribute. Value>//medico. com/records. *</saml: Attribute Value> </saml: Attribute> </Resources> <Actions> <saml: Action>read</saml: Action> </Actions> </Target> <Condition> <Equal> <Attribute. Designator Attribute. Name="urn: oasis: names: tc: xacml: identifiers: Access. S ubject" /> <Attribute. Designator Attribute. Name="patient. Name" /> </Equal> </Condition> </Rule> XACML - Example 35

XML Security Applications WS Security 8 Web Services rely on XML Protocol messages to link applications across enterprises and platforms. 8 Securing those inter-connections is essential. 8 Microsoft and IBM released a Web Services Security architecture 8 The Goal: Define a uniform, flexible, and extensible security framework for Web Services. 36

WS Security Terminology 8 Web service 8 Security Token 8 Signed Security Token 8 Claims 8 Subject 8 Proof-of-Possession 8 Web Service Endpoint Policy 8 Intermediaries 8 Actor 37
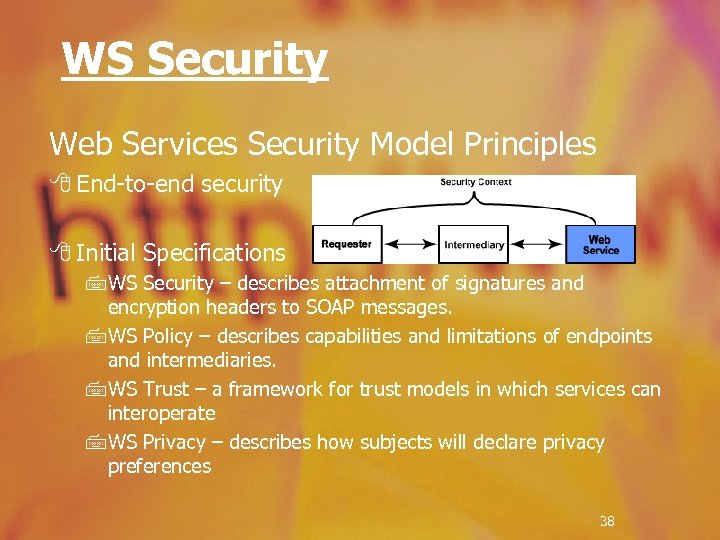
WS Security Web Services Security Model Principles 8 End-to-end security 8 Initial Specifications 7 WS Security – describes attachment of signatures and encryption headers to SOAP messages. 7 WS Policy – describes capabilities and limitations of endpoints and intermediaries. 7 WS Trust – a framework for trust models in which services can interoperate 7 WS Privacy – describes how subjects will declare privacy preferences 38
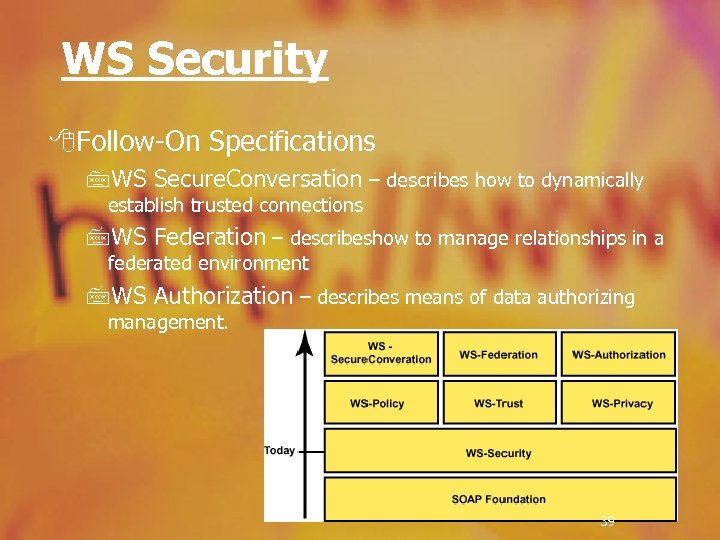
WS Security 8 Follow-On Specifications 7 WS Secure. Conversation – describes how to dynamically establish trusted connections 7 WS Federation – describeshow to manage relationships in a federated environment 7 WS Authorization – describes means of data authorizing management. 39
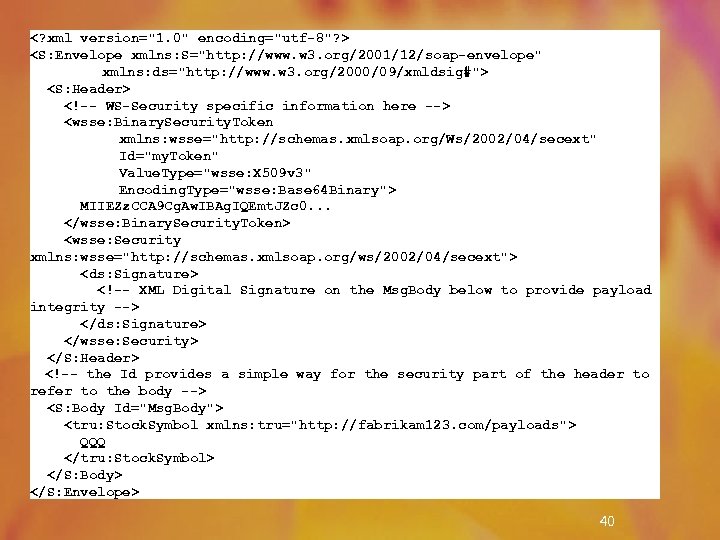
WS Security <? xml version="1. 0" encoding="utf-8"? > <S: Envelope xmlns: S="http: //www. w 3. org/2001/12/soap-envelope" xmlns: ds="http: //www. w 3. org/2000/09/xmldsig#"> <S: Header> <!-- WS-Security specific information here --> <wsse: Binary. Security. Token xmlns: wsse="http: //schemas. xmlsoap. org/Ws/2002/04/secext" Id="my. Token" Value. Type="wsse: X 509 v 3" Encoding. Type="wsse: Base 64 Binary"> MIIEZz. CCA 9 Cg. Aw. IBAg. IQEmt. JZc 0. . . </wsse: Binary. Security. Token> <wsse: Security xmlns: wsse="http: //schemas. xmlsoap. org/ws/2002/04/secext"> <ds: Signature> <!-- XML Digital Signature on the Msg. Body below to provide payload integrity --> </ds: Signature> </wsse: Security> </S: Header> <!-- the Id provides a simple way for the security part of the header to refer to the body --> <S: Body Id="Msg. Body"> <tru: Stock. Symbol xmlns: tru="http: //fabrikam 123. com/payloads"> QQQ </tru: Stock. Symbol> </S: Body> </S: Envelope> 8 Example 40
Platform For Privacy Preference Purpose: 8 Control access to personal information 8 Prevent misuse of personal information 8 Lets users control what information to distribute 8 Save the user to bother of reading the policies 41
P 3 P – Platform for Privacy Preference Features 8 An XML vocabulary for defining user’s/site’s privacy preferences 7 Defines who collects the data 7 For what purpose is the data being used 7 Who can access the data 7 Etc. 8 A tool for retrieving policies easily 8 Transparency – User does not have to look for the policies. 42

P 3 P Client Implementations 8 Idcide Privacy Companion 7 Browser plug in 7 Allows user to set a privacy level, and warns when it’s reached 7 Keeps a tracking history 8 YOUpowered Orby Privacy Plus Trust Meter 7 A tool bar on the desktop 7 Basically does the same 7 www. youpowered. com 43
P 3 P Policy Generators 8 IBM P 3 P Policy Editor 7 Allows websites to create policies in P 3 P and English 7 http: //www. alphaworks. ibm. com/tech/p 3 peditor 8 Privacy. Bot. com 7 An online interface for creating policies. 8 YOUpowered Consumer Trust Policy Manager Wizard 7 http: //www. youpowered. com/ 44

P 3 P Enabled Websites 8 www. aol. com 8 www. att. com 8 www. cdt. org 8 www. engage. com 8 www. hp. com 8 www. ibm. com 8 www. idcide. com 8 www. microsoft. com 8 www. pg. com 8 www. ttuhsc. edu 8 www. youpowered. com 8 www. vineyard. net 8 www. w 3. org 8 www. whitehouse. gov 45

Digital Rights Management Purpose: 8 Control the use of content according to a license 8 Keep this control after content is copied/moved 8 Allow interoperability among content viewers Features: 8 Xr. ML defines a framework for expressing: 7 Rights, 7 Definitions, 7 Rules 46
Xr. ML – e. Xtensible rights Markup Language Key Concepts: 8 Principal – unique, authenticated individual 8 Resource – an object (i. e. – a movie, a book) 8 Right – an action a principal can perform on a resource 8 Grant – a right of a principal to use a resource 8 Condition – terms which must be met to execute a grant 8 License – a collection of grants, along with issuer’s info 8 Xr. ML uses XML to define grants and provide extensibility 8 Xr. ML takes advantage of XML Signatures for signing licenses 47
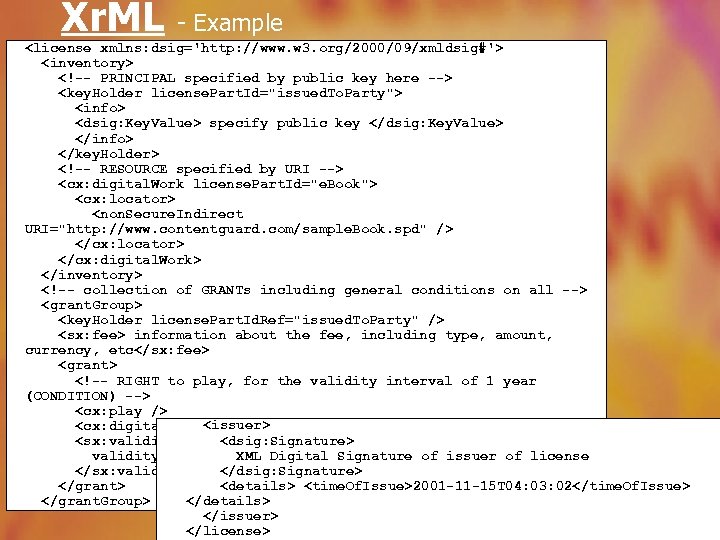
Xr. ML - Example <license xmlns: dsig='http: //www. w 3. org/2000/09/xmldsig#'> <inventory> <!-- PRINCIPAL specified by public key here --> <key. Holder license. Part. Id="issued. To. Party"> <info> <dsig: Key. Value> specify public key </dsig: Key. Value> </info> </key. Holder> <!-- RESOURCE specified by URI --> <cx: digital. Work license. Part. Id="e. Book"> <cx: locator> <non. Secure. Indirect URI="http: //www. contentguard. com/sample. Book. spd" /> </cx: locator> </cx: digital. Work> </inventory> <!-- collection of GRANTs including general conditions on all --> <grant. Group> <key. Holder license. Part. Id. Ref="issued. To. Party" /> <sx: fee> information about the fee, including type, amount, currency, etc</sx: fee> <grant> <!-- RIGHT to play, for the validity interval of 1 year (CONDITION) --> <cx: play /> <cx: digital. Work <issuer> license. Part. Id. Ref="e. Book" /> <dsig: Signature> <sx: validity. Interval. Floating> XML Digital Signature of issuer of license validity interval, possibly unique identifier </dsig: Signature> </sx: validity. Interval. Floating> <details> <time. Of. Issue>2001 -11 -15 T 04: 03: 02</time. Of. Issue> </grant> </details> </grant. Group> </issuer> 48 </license>
XML Security - Conclusion Using all of the described tools, XML Security provides a secure environment in which users and Web Services communicate and interact. The base of these tools are the XML Digital Signatures and XML Encryption. 49
Bibliography 8 XML, SOAP, XML Digital Signatures, XML Encryption, XKMS, P 3 P 7 http: //www. w 3. org/XML/ 7 http: //www. w 3. org/2000/xp/Group/ 7 http: //www. w 3. org/Signature/ 7 http: //www. w 3. org/Encryption/2001/ 7 http: //www. w 3. org/2001/XKMS/ 7 http: //www. w 3. org/P 3 P/ 8 XACML www. oasis-open. org/committees/xacml/ 8 SAML www. oasis-open. org/committees/security , www. simc -inc. org/archive 0002/February 02/ devwed 1015_rouault. pdf 8 WS Security www. alphaworks. ibm. com/developerworks/security/library/ws-secmap/ 50
e8e3e81c71faefd94a52699815f215c0.ppt