044f2c4235807b0aa87b650f84fb06f4.ppt
- Количество слайдов: 27
“Ensuring distributed accountability for data sharing in the cloud” Smitha Sundareswaran, Anna C. Squicciarini and Dan Lin 1
Contents ● ● ● ● ● Cloud computing Introduction to CIA framework Problem statement Information accountability Automated logging mechanism End-to-end auditing mechanism Security discussion Performance study Conclusion References 2
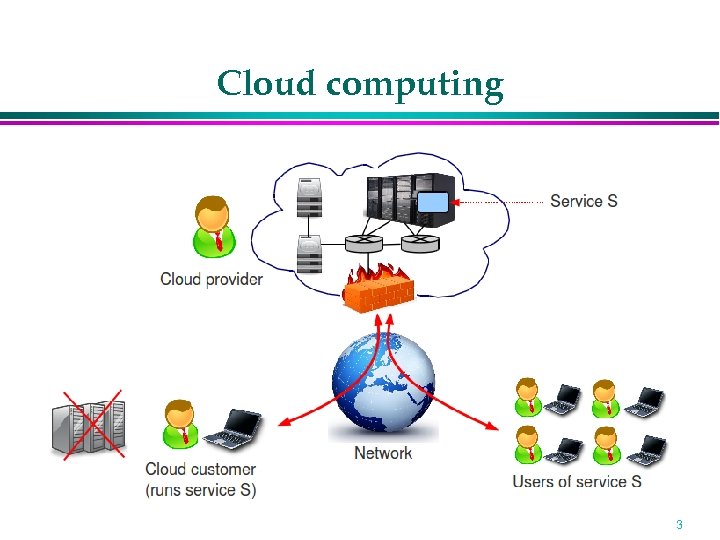
Cloud computing 3
Introduction to CIA framework Security of user data in cloud computing » Cloud computing & its services » User’s data processed in remote machine » Fear of losing data & other security concerns Cloud Information Accountability(CIA) framework » Highly decentralized » We leverage JAR programmable capabilities » Also use distributed auditing mechanisms 4
Problem statement Cloud user send his/her data & access control policies to the service provider The service provider will have granted access rights If the rights are granted using conventional access control mechanisms, data will be fully available at the service provider We use new logging and auditing techniques to track the actual usage of data 5
Requirements The logging technique must satisfy: » Logging should be decentralized » Every access to user’s data should be automatically logged » Log files should be reliable and tamper proof » Recovery mechanisms are also desirable » Log files should sent back to data owners periodically 6
Information accountability Accountability helps to » Trace the user’s data » Protect sensitive & confidential information » Enhance user’s trust in cloud computing A cloud is accountable if: » Faults can be reliably detected » Each fault can be linked to one party (customer or provider) 7
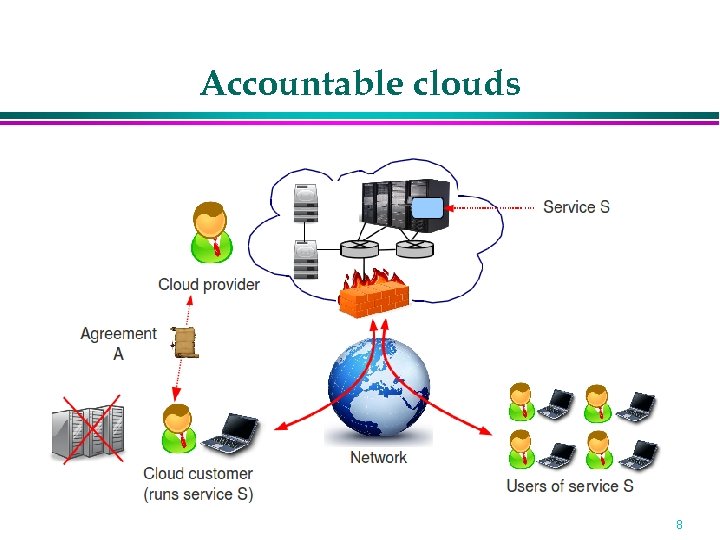
Accountable clouds 8
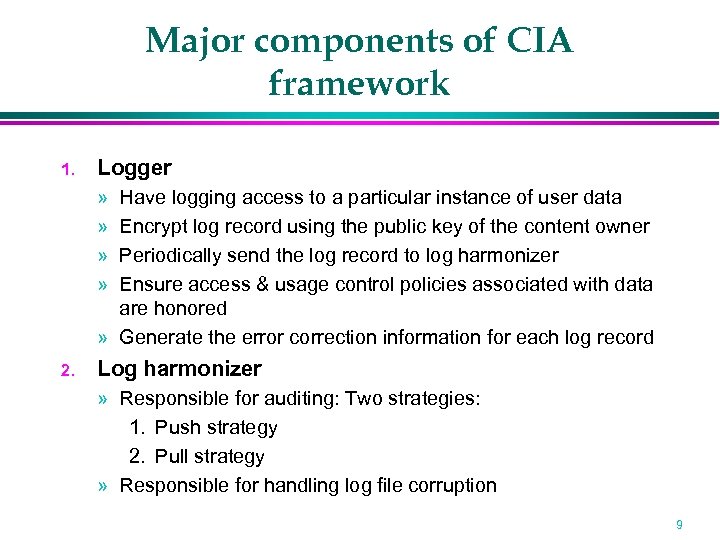
Major components of CIA framework 1. Logger » » Have logging access to a particular instance of user data Encrypt log record using the public key of the content owner Periodically send the log record to log harmonizer Ensure access & usage control policies associated with data are honored » Generate the error correction information for each log record 2. Log harmonizer » Responsible for auditing: Two strategies: 1. Push strategy 2. Pull strategy » Responsible for handling log file corruption 9
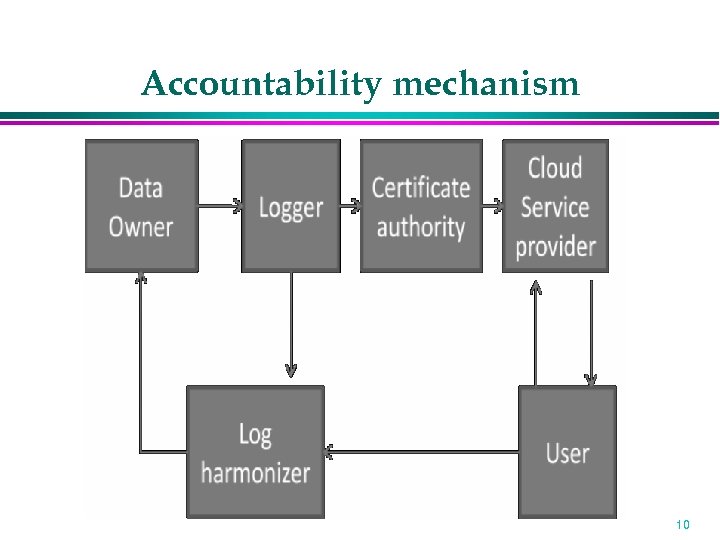
Accountability mechanism 10
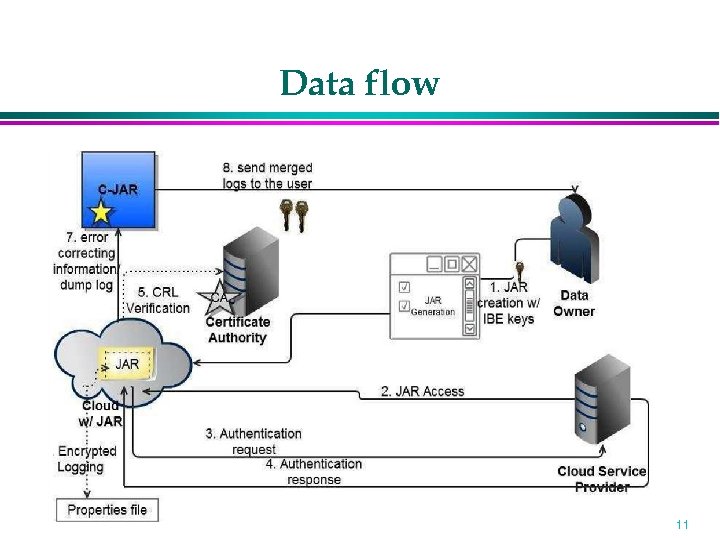
Data flow 11
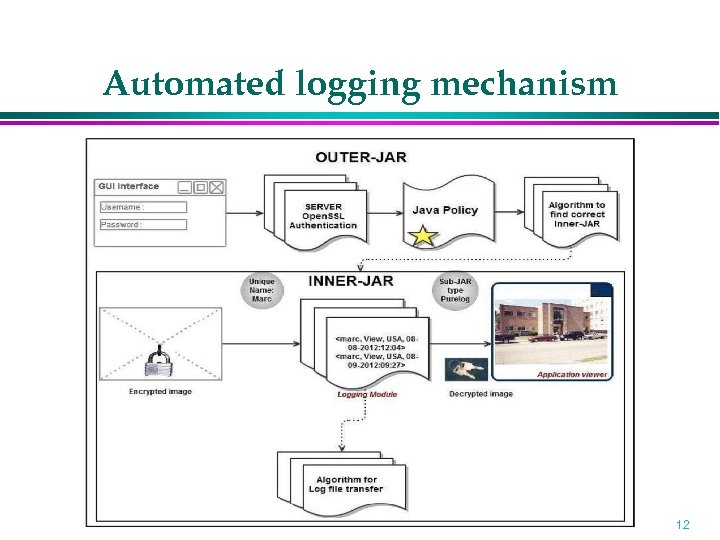
Automated logging mechanism 12
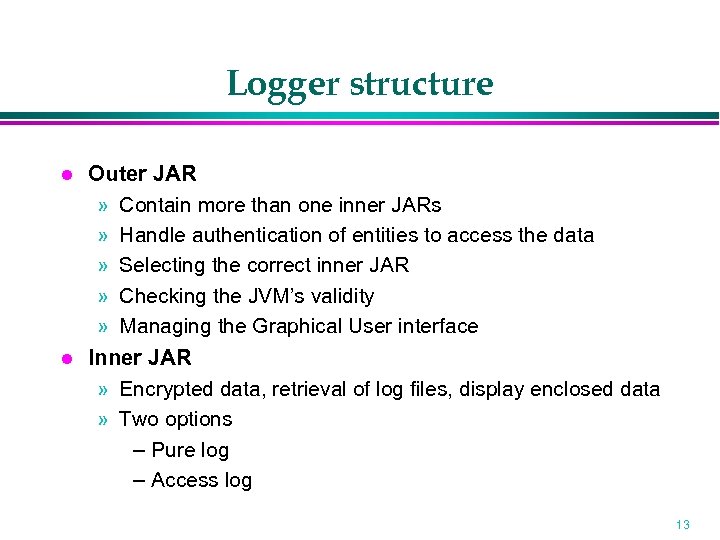
Logger structure Outer JAR » Contain more than one inner JARs » Handle authentication of entities to access the data » Selecting the correct inner JAR » Checking the JVM’s validity » Managing the Graphical User interface Inner JAR » Encrypted data, retrieval of log files, display enclosed data » Two options – Pure log – Access log 13
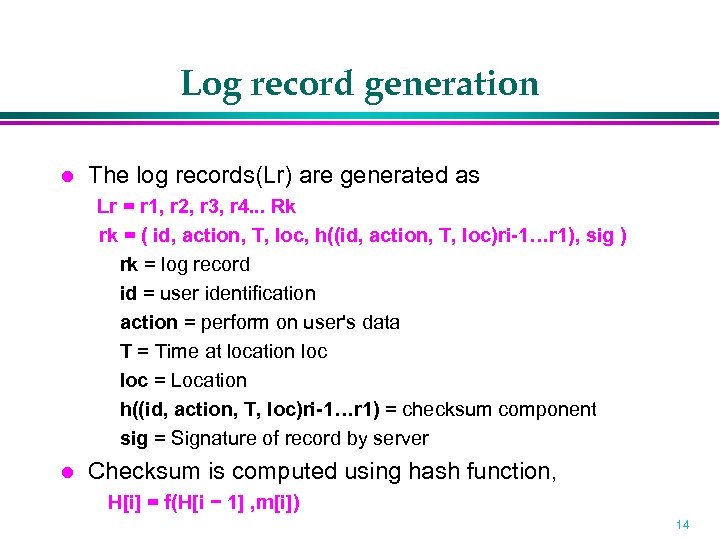
Log record generation The log records(Lr) are generated as Lr = r 1, r 2, r 3, r 4. . . Rk rk = ( id, action, T, loc, h((id, action, T, loc)ri-1…r 1), sig ) rk = log record id = user identification action = perform on user's data T = Time at location loc = Location h((id, action, T, loc)ri-1…r 1) = checksum component sig = Signature of record by server Checksum is computed using hash function, H[i] = f(H[i − 1] , m[i]) 14
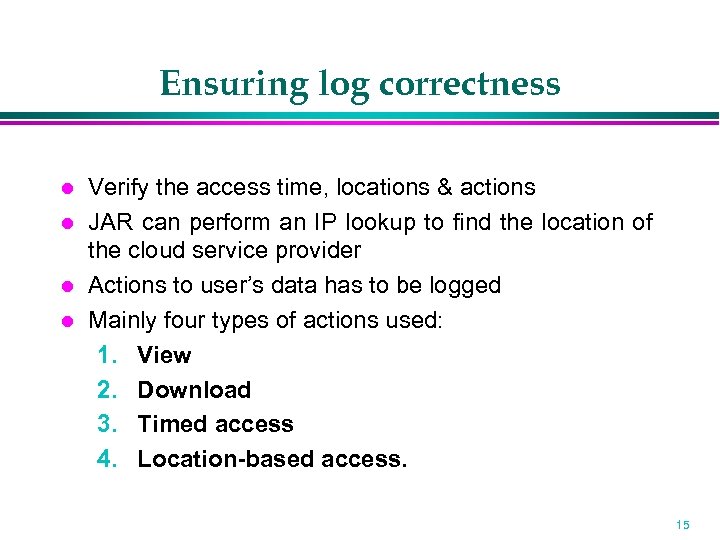
Ensuring log correctness Verify the access time, locations & actions JAR can perform an IP lookup to find the location of the cloud service provider Actions to user’s data has to be logged Mainly four types of actions used: 1. View 2. Download 3. Timed access 4. Location-based access. 15
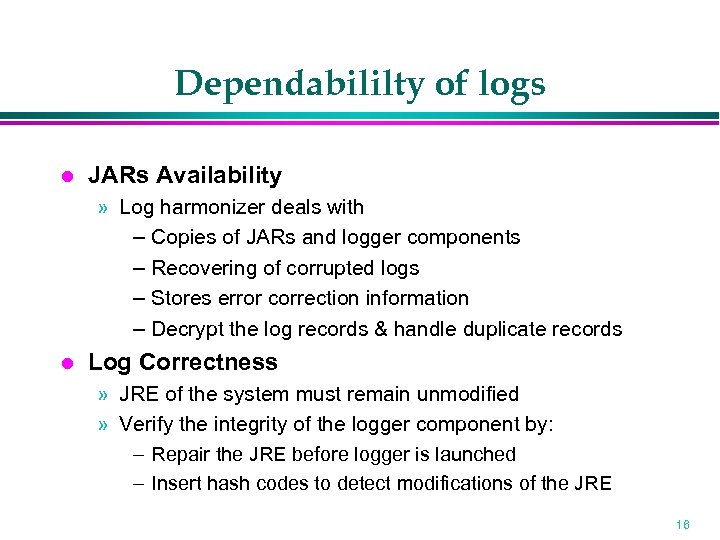
Dependabililty of logs JARs Availability » Log harmonizer deals with – Copies of JARs and logger components – Recovering of corrupted logs – Stores error correction information – Decrypt the log records & handle duplicate records Log Correctness » JRE of the system must remain unmodified » Verify the integrity of the logger component by: – Repair the JRE before logger is launched – Insert hash codes to detect modifications of the JRE 16
End-to-end auditing mechanism Push and Pull Mode » Push mode: – The logs are periodically pushed to the data owner by the harmonizer: Ensures size of the log files does not explode Enables timely detection and correction of any loss or damage to log files » Pull mode – auditors may retrieve the logs anytime – Pull message contains FTP pull command 17
End-to-end auditing mechanism Algorithms: » Pushing strategy » Pull strategy » Hybrid strategy 18
Security discussion Copying Attack The attacker copies entire JAR files. Disassembling Attack Disassemble the JAR file & attempt to extract information useful Man-in-the-Middle Attacker intercept messages during authentication of service provider with certificate authority, and reply messages Compromised JVM Attacker try to compromise the JVM 19
Performance study Experimental Settings » » By setting up a small cloud, using the Emulab testbed On Open. SSL-enabled servers Servers are installed with Eucalyptus Used Linux-based servers running Fedora 10 OS – a 64 -bit Intel Quad Core Xeon E 5530 processor – 4 GB RAM – 500 GB Hard Drive 20
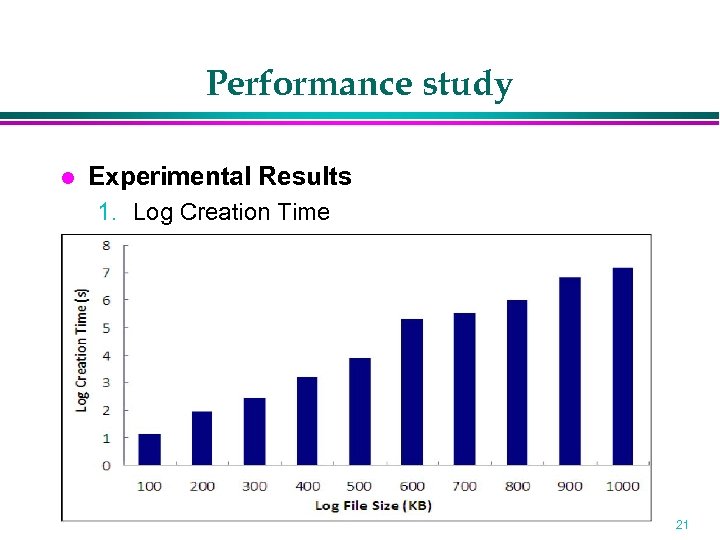
Performance study Experimental Results 1. Log Creation Time 21
Performance study 1. Authentication Time – Not too much overhead is added – Performance can be further improved by caching the certificates 2. Time Taken to Perform Logging – Time for executing the action is negligible 22
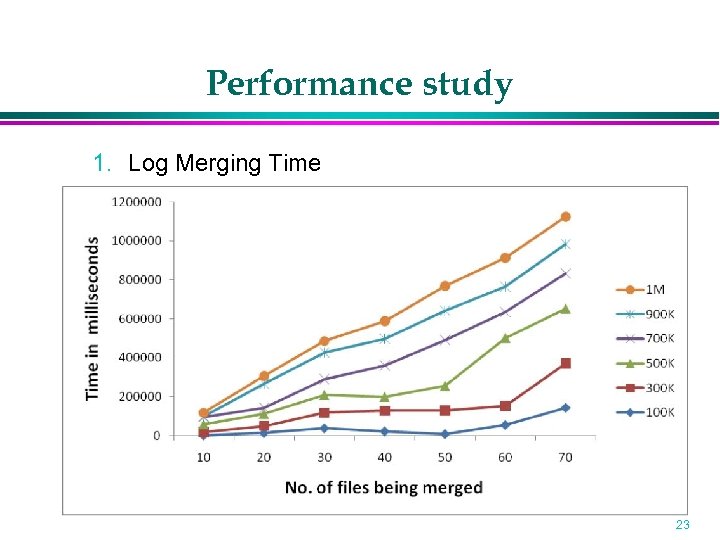
Performance study 1. Log Merging Time 23
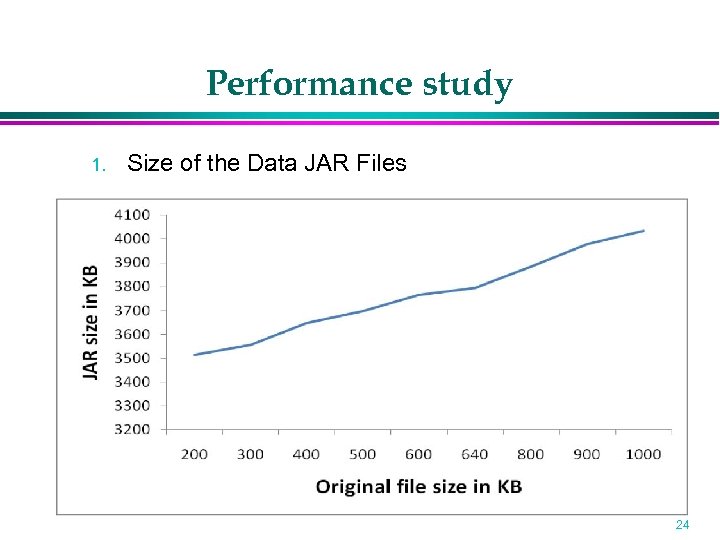
Performance study 1. Size of the Data JAR Files 24
Conclusion CIA performs automatic authentication of users Data owner can confirm that his data is safe in the cloud by using auditing mechanism Able to distribute applications to many different mobile devices Information gathering capabilities is high High portability 25
![References [1] Smitha Sundareswaran, Anna C. Squicciarini and Dan Lin, "Ensuring Distributed Accountability for References [1] Smitha Sundareswaran, Anna C. Squicciarini and Dan Lin, "Ensuring Distributed Accountability for](https://present5.com/presentation/044f2c4235807b0aa87b650f84fb06f4/image-26.jpg)
References [1] Smitha Sundareswaran, Anna C. Squicciarini and Dan Lin, "Ensuring Distributed Accountability for Data Sharing in the Cloud, ", IEEE Transaction on dependable a secure computing, VOL. 9, NO. 4, pg 556 -568, 2012. [2] S. Pearson and A. Charlesworth, "Accountability as a Way Forward for Privacy Protection in the Cloud, " Proc First Int'l conf. Cloud Computing, 2009. [3] B. Chun and A. C. Bavier , "Decentralized Trust Management and Accountability in Federated System, " Proc. Ann. Hawaii Int'l Conf. System Science (HICSS), 2004. [4] B. Crispo and G. Ruffo, “Reasoning about Accountability within Delegation, ” Proc. Third Int’l Conf. Information and Comm. Security (ICICS), pp. 251 -260, 2001 26
Thank you! 27
044f2c4235807b0aa87b650f84fb06f4.ppt